
Data Protection Governance: Roles, RACI, and Reporting

A privacy programme can have strong policies and still fail if no one owns the decisions, the work, and the evidence. That is why data protection governance matters. It turns the Jamaica Data Protection Act obligations into a practical operating model: clear roles, a RACI for recurring activities, and reporting that lets management and the board see risk and progress.
This guide shows how to set up roles, build a workable RACI, and design reporting that stands up to audits, incidents, vendor due diligence, and board scrutiny.
What “data protection governance” means in practice
Data protection governance is the structure that answers four operational questions:
Who is accountable for compliance decisions and risk acceptance?
Who does the work (privacy notices, vendor reviews, rights requests, breach response, training)?
Who must be consulted before changes go live (new systems, new campaigns, new vendors)?
How do we prove it with reporting and evidence, not just statements?
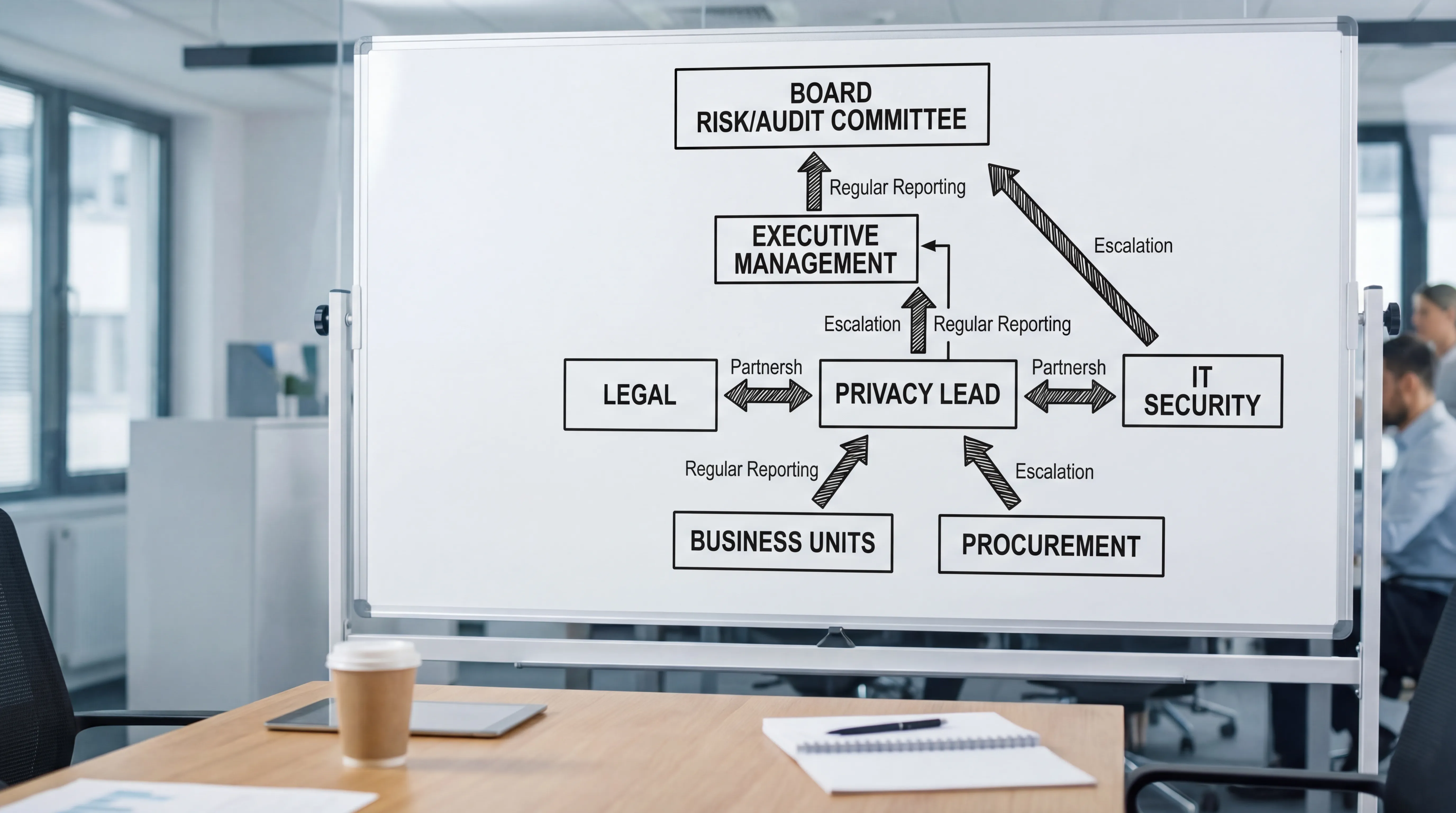
In Jamaican organisations, governance is also the bridge between privacy, cyber security, legal, HR, procurement, and enterprise risk. If you are already working through implementation steps like data mapping, privacy notices, vendor contracts, and incident readiness, governance is what keeps those elements coordinated and sustainable. (See PLMC’s practical background guides: Jamaica Data Protection Act Explained for Businesses and Data Protection Jamaica: Compliance Roadmap for 2026.)
The core roles (and what “good” looks like)
A common mistake is to treat privacy as a single person’s job title. Effective governance spreads responsibilities across the lines where data is collected, used, shared, and stored.
Board and executive leadership (accountability and tone)
Senior leadership should be able to answer, at any time:
What are our highest privacy risks and why?
What controls are in place for those risks?
Where are we behind plan, and what resources are required?
In practice, the board or a board committee (often audit, risk, or governance) should receive regular reporting and approve key risk decisions such as accepting residual risk for high impact processing, resourcing remediation, and setting the organisation’s risk appetite.
Privacy Lead / DPO function (programme ownership)
Whether you call this role a Data Protection Officer, Privacy Officer, or Privacy Lead, the function typically:
Maintains the privacy management framework (policies, standards, templates)
Advises on lawful processing, transparency, and rights handling
Coordinates DPIAs or privacy impact assessments for high risk processing
Oversees breach readiness and privacy by design
Provides training guidance and awareness support
Keeps the evidence trail (records, decisions, approvals)
The key is not the title. It is the authority to stop or escalate risky processing, and the access to leadership to raise issues early.
Legal / Compliance (interpretation and defensibility)
Legal and compliance teams help keep your decisions defensible by:
Reviewing privacy notices and contract terms
Advising on cross border processing clauses and vendor risk positions
Aligning privacy governance with wider compliance (for example AML and sector rules)
They should not be the bottleneck for routine operational work. Your RACI should prevent everything becoming “send to legal.”
IT and Cyber Security (technical and operational controls)
Security enables privacy obligations such as confidentiality, integrity, availability, access control, logging, and secure disposal. Cyber teams often own:
Identity and access management
Endpoint, network, and cloud security
Vulnerability management and patching
Incident detection and response
Privacy governance should define how security evidence (for example access reviews, pen test summaries, incident logs) feeds into privacy reporting.
HR (employee data and culture)
HR commonly handles sensitive employee information and should be a key stakeholder for:
Staff privacy notices and internal transparency
Background checks and third party HR platforms
Offboarding, access termination, and records retention
Training completion and conduct expectations
Procurement / Vendor Management (processor oversight)
Vendor relationships are a frequent compliance weak point. Procurement should not only negotiate price and service levels, but also coordinate:
Due diligence and security questionnaires
Data processing clauses and audit rights
Subprocessor visibility
Exit and deletion requirements
Business unit owners (where the processing happens)
Marketing, customer service, operations, and product teams are usually the source of new data use cases. Governance must treat these teams as owners of processing activities, not passive recipients of “privacy rules.”
A useful principle: the team that benefits from the processing should be accountable for using it lawfully and safely, with support from privacy, legal, and security.
Risk management and internal audit (second and third line)
Where your organisation has an ERM function or internal audit, use it:
Risk can help formalise privacy risk registers and risk acceptance
Audit can test whether controls and evidence match what policies claim
For good practice framing, many organisations align accountability expectations to recognised approaches like the UK ICO’s accountability guidance (see the Information Commissioner’s Office resources) and security frameworks such as ISO/IEC 27001.
Turning roles into action: a practical RACI
A RACI matrix is useful when it is short, readable, and used in real workflows. If it becomes a 40 row spreadsheet that no one opens, it fails.
RACI rules that prevent confusion
One “A” per activity (one accountable owner). Multiple “A”s create delays and finger pointing.
Keep “C” tight. “Consult everyone” equals “consult no one.”
Use “I” for predictable stakeholders who need awareness but should not slow delivery.
Align RACI to existing meetings and approvals so it matches how work actually moves.
Sample RACI for common data protection activities
Adjust this for your size and sector, but keep the logic.
Activity | Board / Exec | Privacy Lead | Legal / Compliance | IT / Security | HR | Procurement | Business Unit Owner | Risk / Internal Audit |
Maintain privacy policies and standards | I | A/R | C | C | C | I | I | C |
Maintain record of processing (data inventory) | I | A | C | C | C | C | R | C |
Approve new high risk processing (privacy by design gate) | A | R | C | C | C | I | R | C |
Privacy notices (customer and employee) | I | R | A | C | R | I | C | I |
DPIA / privacy impact assessment (when required) | I | A/R | C | C | C | C | R | C |
Rights requests (access, correction, deletion) | I | A | C | C | C | I | R | I |
Vendor due diligence and data processing clauses | I | C | C | C | I | A/R | R | I |
Cross border data transfer assessment | I | A/R | C | C | I | C | R | I |
Retention schedule and disposal | I | A | C | C | R | I | R | C |
Data breach response coordination | I | A/R | C | R | C | I | C | I |
Training and awareness (role based) | I | A | C | C | R | I | C | I |
Periodic compliance testing and assurance | I | C | C | C | C | C | C | A/R |
Notes on the table:
Many organisations place vendor due diligence as Procurement “A,” because procurement controls the vendor onboarding gate. Privacy and security remain key “C” stakeholders.
Rights requests often work best when the business unit is “R” for locating data and applying corrections, while Privacy remains “A” for process integrity and deadlines.
If you want a complementary implementation checklist to ensure your RACI covers all obligations, use Privacy and Data Protection: A Practical Checklist.
Reporting that management and boards actually use
Governance fails when reporting is either too technical (no decisions) or too vague (no evidence). Effective reporting is decision oriented.
Three reporting levels (with different audiences)
Operational reporting (weekly to monthly): For Privacy Lead, IT Security, HR, procurement, and process owners. Focus on workload, deadlines, and exceptions.
Management reporting (monthly to quarterly): For executive leadership. Focus on risk, delivery against plan, and resourcing.
Board reporting (quarterly, plus incident escalation): Focus on top risks, significant incidents, regulatory exposure, and whether the programme is effective.
KPIs and KRIs: what to measure
Use a blend:
KPIs (performance) show whether the programme is being executed.
KRIs (risk indicators) show where exposure is increasing.
Here is a reporting starter set that works well for Jamaica based organisations.
Metric | Type | Why it matters | Typical owner | Frequency |
Rights requests received, closed within target timeframe, overdue | KPI/KRI | Demonstrates operational compliance and customer impact | Privacy Lead | Monthly |
Breach incidents by severity, time to contain, lessons learned status | KRI/KPI | Shows resilience and readiness | IT/Security with Privacy | Monthly, escalate immediately for major incidents |
High risk processing count, DPIAs completed vs pending | KRI/KPI | Shows whether privacy by design is real | Privacy Lead with Business Units | Quarterly |
Vendor onboarding: % with completed due diligence and signed data clauses | KPI/KRI | Vendor risk is a common gap | Procurement | Monthly/Quarterly |
Training completion rates by role (frontline, HR, IT, leadership) | KPI | Measures privacy culture and coverage | HR | Quarterly |
Data inventory coverage (systems mapped vs known systems) | KPI | Accountability evidence and operational clarity | Privacy Lead | Quarterly |
Retention and disposal exceptions (aged records, unresolved holds) | KRI | Reduces exposure and storage risk | Business Units / HR | Quarterly |
Top 5 privacy risks and remediation status (on track, delayed, blocked) | KRI | Keeps leadership focused on what matters | Risk/Privacy Lead | Quarterly |
A simple board pack structure
A board pack does not need to be long. A practical format is:
Executive summary: what changed since last period, key decisions required
Top risks: 5 to 10 risks, trend direction, remediation status
Incidents: summary, actions taken, lessons learned
Programme delivery: roadmap milestones and blockers
Assurance: audit findings, testing results, third party concerns
Where possible, tie your reporting to your 2026 plan so the board can see progress against a defined roadmap (see Data Protection Jamaica: Compliance Roadmap for 2026).
Evidence: what to retain so you can prove compliance
A mature governance programme keeps an “evidence pack” that supports audits, customer assurance requests, and internal investigations.
Common evidence items include:
Record of processing activities and data flow maps
Approved policies, standards, and review dates
DPIAs and approvals for higher risk processing
Privacy notices, version history, and sign offs
Rights request logs and response templates
Vendor due diligence records and executed contract clauses
Training attendance, completion, and role based content
Incident response records and post incident reviews
Retention schedules and disposal logs (where feasible)
This is also where governance intersects with broader GRC. If your organisation already uses risk registers, control libraries, or audit tracking, privacy evidence should live within those systems rather than in personal folders.
Common governance pitfalls (and how to fix them)
“Privacy is owned by one person”
Fix: Assign business unit accountability in the RACI and require privacy sign off for new processing through a lightweight change gate.
“We have a policy, but no operational process”
Fix: Create simple workflows for rights requests, vendor onboarding, breach escalation, and DPIAs. Governance should define who can approve what.
“Reporting is activity based, not risk based”
Fix: Add KRIs (overdue rights requests, repeated incidents, unassessed high risk processing, vendor gaps) and require decisions, not just updates.
“Procurement signs vendors before privacy sees them”
Fix: Put privacy and security checks into procurement intake so vendors cannot go live without minimum due diligence and contract clauses.
“Security and privacy operate separately”
Fix: Create a joint incident response process, shared reporting metrics, and a regular meeting cadence between the Privacy Lead and IT Security.
Frequently Asked Questions
Do we need a Data Protection Officer to build data protection governance? Not always. What you need is a clearly mandated privacy leadership function, independence to escalate issues, and defined responsibilities across the business.
What is the difference between a RACI and a policy? A policy states the rules and expectations. A RACI assigns who is Responsible, Accountable, Consulted, and Informed so the work happens consistently and can be evidenced.
How often should we report data protection to the board? Quarterly is common, with immediate escalation for major incidents or significant new high risk processing. The right frequency depends on risk profile and change volume.
Which teams should be involved in vendor governance for privacy? Procurement typically owns onboarding, but privacy, legal, and IT security should be consulted on due diligence, contract clauses, and any high risk processing.
What should we do first if we have no governance structure today? Start with role definitions, a short RACI for core processes (rights requests, vendors, incidents, DPIAs), then implement a monthly management report and quarterly board report.
Build a governance model you can defend (and operate)
If you want help turning the Data Protection Act requirements into a working governance model, PLMC supports Jamaican organisations with data protection implementation, GRC integration, training sessions, risk assessments, and practical templates.
You can start with a free consultation to review your current structure, clarify roles, and draft a fit for purpose RACI and reporting pack. Visit Privacy & Legal Management Consultants Ltd. or explore the supporting guides: Data Protection Basics: What Jamaican Firms Must Know and Data Privacy in Jamaica: Key Principles and Rights.
