
Data Protection Articles: What to Read to Stay Compliant

Staying compliant with data protection law is not a one-time project. Even if your policies are solid today, guidance evolves, threat patterns change, vendors introduce new risks, and your own organisation launches new products, campaigns, and systems that reshape how personal data is used.
That is why the right data protection articles are a practical compliance tool. They help you interpret obligations, spot emerging risk, and keep your programme current without waiting for a crisis.
This guide explains what to read, how to judge whether an article is actually reliable for compliance, and how to turn what you read into actions and evidence, with a focus on organisations operating in Jamaica under the Data Protection Act.
Start with “primary sources” before opinions
If your goal is compliance (not just general awareness), prioritise sources in this order:
1) The law itself and any official supporting instruments
For Jamaica, that means reading the Data Protection Act and tracking any official updates that affect obligations, timelines, enforcement, or definitions.
A useful habit is to keep a short internal “legal highlights” note for your team that records:
The specific section(s) you relied on
What business process it affects (HR onboarding, marketing email, CCTV, customer support calls, etc.)
What control you implemented as a result (policy, procedure, technical safeguard)
2) Regulator guidance, statements, and enforcement signals
In many jurisdictions, regulator publications clarify what “reasonable” looks like in practice. Even when guidance is not law, it is often what investigators and auditors treat as the expected baseline.
If you cannot find Jamaica-specific guidance on a point, it is still useful to consult mature regulators for practical interpretations, then adapt to the Jamaican legal context. The UK Information Commissioner’s Office (ICO) is a strong example of detailed, operational guidance that many Commonwealth organisations use as a reference point: see the ICO Guide to data protection.
3) Court decisions and reported enforcement cases
Articles that summarise enforcement actions can be valuable, but only if they cite primary documents (decision, order, judgment) and clearly distinguish facts from commentary. These pieces help you answer: “What actually triggered regulatory attention?” and “What controls were expected but missing?”
The compliance topics that are worth reading about year-round
Many teams read privacy articles reactively, usually after a breach or complaint. A better approach is to maintain a small set of topics you revisit regularly, because they are where most compliance programmes weaken over time.
Privacy governance and accountability (board-ready topics)
Look for articles that explain how to operationalise accountability, not just define it. The best governance articles typically include examples of:
RACI-style responsibility assignment for controller and processor activities
Reporting lines and escalation criteria
What to measure (requests, incidents, training completion, vendor risk ratings)
What evidence to retain to demonstrate compliance
If you want a Jamaica-focused baseline you can compare your programme against, PLMC’s practical resources can help you set the frame before you dive into niche topics, for example:
Privacy notices and transparency (marketing, HR, customer journeys)
Transparency obligations tend to drift when websites change, new forms are introduced, or business units copy old templates. Articles worth reading here are the ones that show:
How to write layered notices that match real touchpoints
How to document lawful purpose and data categories in plain language
Common pitfalls (over-collection, unclear retention, vague sharing statements)
A strong reading signal is when the author includes sample notice wording and explains why each element matters.
Data subject rights handling (requests become operational fast)
Rights requests fail less often because people “do not know the law,” and more often because workflow breaks: identity verification is unclear, systems cannot locate records, deadlines are missed, or teams do not know what to redact.
Prioritise articles that include:
A practical intake to closure workflow
Guidance on identity verification and secure delivery
Search strategy across systems (email, CRM, shared drives, ticketing tools)
A records approach for logging and reporting
For a Jamaica-specific overview of principles and rights, see: Data Privacy in Jamaica: Key Principles and Rights
Vendor and outsourcing risk (processors, SaaS, payroll, call centres)
If your organisation relies on third parties, vendor management is one of the highest leverage reading areas.
Look for articles that go beyond “sign a DPA” and address:
What to ask vendors about access controls, sub-processors, and incident notification
How to assess cross-border transfer exposure
How to map vendors to data types and business criticality
Contract clauses that drive real operational behaviour (not just legal boilerplate)
Breach readiness and incident response (privacy meets cyber)
Data protection compliance fails quickly during incidents if roles, decision criteria, and communications are not pre-defined.
The most useful breach-readiness articles include:
Clear triage criteria (what counts as a personal data breach in practice)
Decision trees for containment, investigation, notification, and documentation
Templates for internal reports and lessons-learned actions
For general security baseline reading that supports privacy outcomes, the CIS Critical Security Controls are a widely used reference.
Add “privacy engineering” articles to your reading list
Legal compliance and technical reality must match. Even excellent policies fail if systems are not designed to support minimisation, access control, logging, retention, and secure deletion.
Two credible, practical sources to read periodically:
The NIST Privacy Framework for a structured approach to privacy risk management that complements security frameworks.
The OWASP Top 10 to stay grounded on common application security risks that often lead to personal data exposure.
Even if your role is not technical, reading these helps you ask better questions during risk assessments and project reviews.
Use sector-specific articles to cover your “high-risk processing” areas
General privacy content is a start, but compliance issues often emerge in specific operational contexts. Consider adding a small amount of sector reading based on what your organisation does, for example:
HR and recruitment (background checks, references, employee monitoring)
Healthcare and occupational health (sensitive data handling, access restrictions)
Financial services (KYC data minimisation, AML alignment, retention)
Education (student data, parental consent dynamics)
Hospitality and retail (CCTV, loyalty programmes, marketing consent)
A good sector article will state the data types involved, the typical system flows, and the safeguards expected, rather than simply repeating principles.
How to tell if a data protection article is “compliance-grade”
Not every privacy article is written to help you comply. Some are marketing pieces, some are jurisdiction-blind, and some are out of date.
Use these filters before you rely on an article to make decisions:
Check jurisdiction fit
Ask:
Is this written for Jamaica, or for GDPR, the UK, Canada, the US, or another regime?
If it is not Jamaica-specific, does it clearly separate universal good practice (minimisation, security, accountability) from jurisdiction-specific requirements (definitions, timelines, exemptions)?
Cross-reading is still useful, but your internal guidance should always map back to Jamaican obligations.
Check recency and versioning
Prefer articles that show:
Publication date and meaningful updates
References to current guidance and modern technology realities (cloud, SaaS, remote work)
No stale examples that ignore today’s threats (credential theft, misconfigured storage, over-permissioned SaaS)
Check whether the author cites sources
Compliance-grade articles normally cite:
The relevant legal provisions
Regulator guidance
Recognised frameworks or standards (for example NIST)
If it is all opinion and no references, treat it as a conversation starter, not a basis for policy.
Check whether it leads to an auditable output
The best articles end with something you can implement or document, such as:
A template clause set for vendor contracting
A checklist you can incorporate into project reviews
A workflow you can operationalise and test
Evidence you can retain (logs, reports, training records)
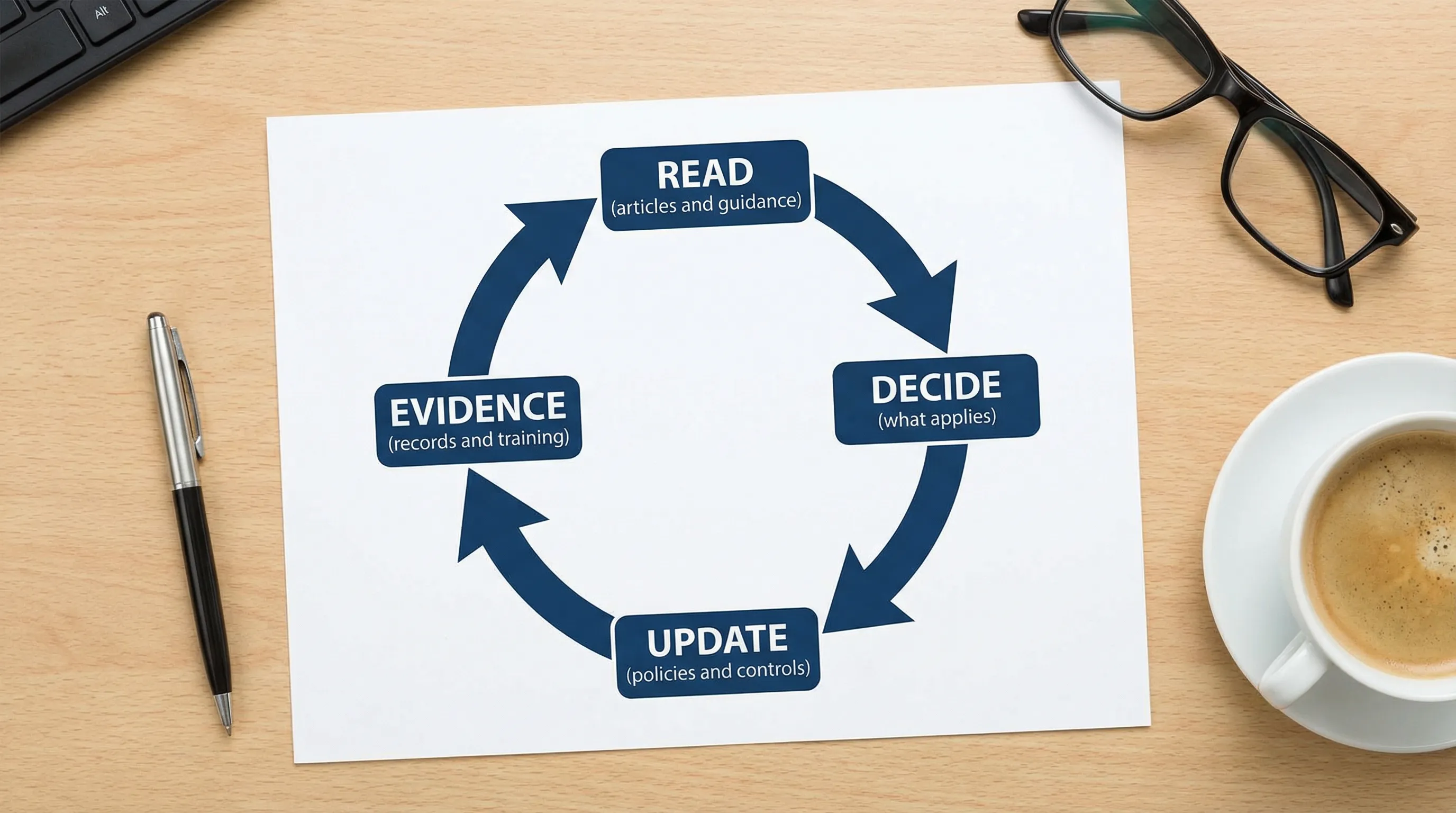
Build a simple monthly reading routine that actually changes behaviour
Many organisations “read a lot” but do not become more compliant. The difference is whether reading is connected to decisions.
A practical routine that works well for small and mid-sized teams is:
One monthly 30 minute scan for regulator updates and high-quality guidance
One monthly 30 minute deep read on a single operational topic (rights requests, retention, vendor controls, breach response)
A short internal summary that lists what changed, what action is required, and who owns it
If you want that routine to produce audit-friendly evidence, store the summary in the same place you store policies and risk decisions, and link it to a change ticket or action log.
Turn what you read into a “living” compliance evidence pack
Articles are only valuable if they lead to improved controls and traceable accountability. Consider maintaining a lightweight evidence pack that includes:
Reading topic | What you update internally | Evidence to keep | Who typically owns it |
Transparency and notices | Website notices, scripts, form disclosures | Version history, approvals, screenshots | Legal/Compliance, Marketing |
Rights requests | Intake process, identity checks, response templates | Request log, response records, redaction notes | Compliance, Customer Service, HR |
Vendor management | Due diligence questions, contract clauses, review cadence | Vendor register, risk ratings, signed agreements | Procurement, Compliance, IT |
Retention and disposal | Retention schedule, deletion process | Retention policy, deletion logs, exceptions | Records, IT, Business owners |
Incident response | Breach triage, notification workflow, tabletop testing | Incident reports, lessons learned, test outputs | IT Security, Compliance |
This approach helps you show not only that you “know” the requirements, but that you operate them.
A curated reading path (without information overload)
If you are building or refreshing your compliance programme, this sequence keeps reading focused and prevents rabbit holes:
Step 1: Ground your team in Jamaica-specific obligations
Start with an overview that can be shared across the business, then align terminology and responsibilities.
PLMC resources that provide this foundation:
Step 2: Add one operational deep dive per month
Choose based on risk and pain points. If you are seeing increased customer complaints, read and improve transparency and rights handling. If you are scaling tools quickly, focus on vendor and cross-border risk.
Step 3: Maintain a security and privacy risk baseline
Use reputable frameworks to keep conversations with IT and vendors concrete. Two strong references are the NIST Privacy Framework and the CIS Critical Security Controls.
When to get expert help instead of reading another article
Articles are excellent for awareness and continuous improvement, but there are moments when you should move from reading to structured assessment, for example when:
You cannot confidently map personal data flows across departments and systems
You are responding to a breach, complaint, or high-risk incident
You are outsourcing core functions to vendors handling significant personal data
You are launching a new data-heavy product, integrating AI, or expanding cross-border processing
If you want a second set of eyes on your privacy programme, PLMC provides data protection implementation support, training, and GRC-focused risk assessment services in Jamaica. You can start with a consultation via the contact options on Privacy & Legal Management Consultants Ltd..
