
Purpose of Data Protection Policy: What It Should Achieve

A data protection policy is one of those documents many organisations say they have, but far fewer can confidently use. When it is written well and actually used, it becomes your internal rulebook for handling personal data. When it is copied from the internet and left in a folder, it becomes a risk.
For Jamaican organisations working to meet the expectations of the Data Protection Act, 2020, the purpose of a data protection policy is practical: it should help your people make consistent decisions about personal data, reduce privacy and security incidents, and prove you are managing privacy in an accountable way.
What a data protection policy is (and what it is not)
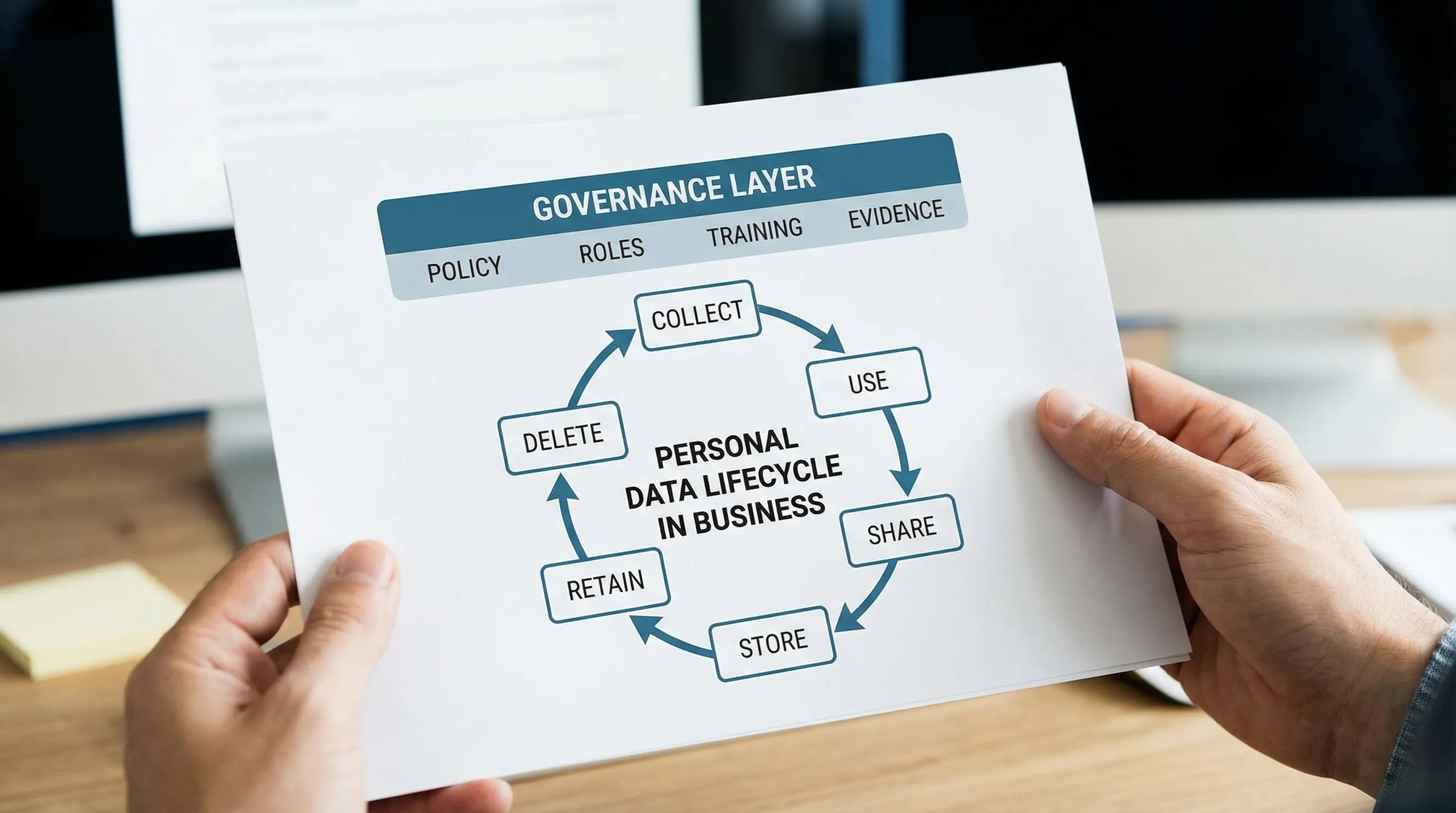
A data protection policy is an internal governance document that sets out how your organisation will process personal data across the data lifecycle (collection, use, sharing, storage, retention, disposal). It translates legal obligations and good practice into clear, repeatable rules for staff and contractors.
It is not the same thing as:
A privacy notice (a customer-facing explanation of what you do with someone’s data and why).
A cyber security policy (controls for protecting systems, networks, and information security more broadly).
A cookie policy (web tracking disclosures).
Your privacy notice and your data protection policy should align, but they serve different audiences and purposes.
The purpose of a data protection policy (in plain language)
The purpose of a data protection policy is to make privacy operational. In practice, it should achieve five big outcomes:
Clarity: staff know what “good” looks like when handling personal data.
Consistency: teams do the same thing in the same situation (HR, IT, Marketing, Customer Service, Operations).
Control: the organisation can prevent, detect, and respond to privacy risks.
Compliance: the organisation can demonstrate alignment with legal requirements and recognised principles.
Confidence: customers, employees, regulators, and partners can trust the organisation’s handling of data.
If your policy does not change day-to-day behaviour, it is not achieving its purpose.
What it should achieve in a Jamaican organisation
Below are the core objectives a data protection policy should achieve. These align with the practical realities of Jamaican businesses and the types of data commonly processed (employee records, customer databases, KYC files, health information, student records, CCTV footage, and marketing lists).
1) Establish accountability (who is responsible for what)
A policy should remove ambiguity about ownership. That means defining:
Who approves the policy (typically senior leadership).
Who administers it day to day (privacy lead, compliance, or a designated function).
Who owns specific processes (HR for employee files, IT for access controls, Procurement for vendors, Marketing for campaigns).
Accountability is also about escalation: when something goes wrong, people must know who to tell, what to record, and what happens next.
2) Set the standard for lawful, fair, and transparent processing
Your policy should define what “lawful and fair” means in your environment, for example:
Collect only what you need for a legitimate business purpose.
Use personal data only for clearly defined purposes.
Be transparent through appropriate notices and internal communication.
This is where many organisations stumble: they have data everywhere, but no agreed standard for what data should be collected, who can access it, and how long it should be kept.
If you want a broader grounding in core concepts, see: Data Protection Basics: What Jamaican Firms Must Know.
3) Control the full data lifecycle (from collection to disposal)
A strong policy should make the data lifecycle manageable by setting rules for:
Collection channels (forms, phone calls, WhatsApp, websites, CCTV, email).
Storage locations (cloud apps, shared drives, paper files).
Access (role-based access, least privilege, joiners and leavers).
Retention and disposal (what to keep, for how long, and how to securely delete).
This is not just “good governance”. It is also one of the fastest ways to reduce operational risk because uncontrolled data tends to cause uncontrolled incidents.
4) Enable individuals’ rights handling (without panic)
Rights requests (for access, correction, deletion, objection, and related requests) can overwhelm teams that have no process. Your policy should:
Define where requests are received and how they are identified.
Assign a process owner.
Require logging, response tracking, and quality checks.
Set expectations for identity verification and secure delivery of responses.
Even if requests are currently rare, the policy’s job is to make your response predictable and defensible.
For deeper context on rights and principles in local terms, refer to: Data Privacy in Jamaica: Key Principles and Rights.
5) Set minimum security and confidentiality expectations
A data protection policy should state minimum security expectations and how they are enforced, including:
Access controls (unique accounts, strong authentication where possible).
Secure sharing (approved tools, encryption where appropriate).
Physical security for paper records.
Clean desk and screen practices.
Rules for using personal devices and removable media.
It should also connect to your incident response requirements so staff understand what qualifies as a privacy incident and what to do immediately.
6) Reduce third-party and vendor risk
Most organisations share personal data with third parties: payroll providers, cloud services, customer messaging tools, security providers, auditors, or outsourced call centres.
Your policy should require:
Vendor due diligence proportional to risk.
Written agreements where personal data is processed.
Rules for onboarding new tools (especially those that store data overseas).
Periodic review and offboarding standards.
If you are building a complete privacy governance system, this is often the point where privacy and procurement need to work together more closely.
7) Create a privacy-aware culture (training and discipline)
Policies do not implement themselves. One key purpose is to drive training and accountability:
Mandatory induction training for new staff.
Refresher training (at least annually, and when the policy changes).
Targeted training (HR, Marketing, Customer Service, IT, and senior leaders have different risks).
Consequences for non-compliance (fair, consistent, documented).
Culture is often the difference between an organisation that “has a policy” and one that is genuinely compliant.
8) Produce evidence you can show (clients, partners, regulators, auditors)
In 2026, many organisations are being asked to demonstrate privacy controls to win business, pass vendor onboarding, or satisfy governance requirements. A policy should make it easier to produce evidence such as:
A record of approvals and versions.
Training attendance logs.
Risk assessments and action plans.
Incident logs and lessons learned.
Vendor registers and contract clauses.
If your policy does not connect to evidence, it will not support accountability.
For an action-oriented view of implementation evidence, see: Data Protection Jamaica: Compliance Roadmap for 2026.
What good looks like: policy goals mapped to outputs and evidence
A practical way to judge whether your policy is doing its job is to map each purpose to outputs (processes and rules) and evidence (proof).
What the policy should achieve | What that looks like in practice | Evidence you can keep |
Accountability | Named policy owner, clear escalation path, leadership sign-off | Approved policy, RACI or responsibility assignments, governance minutes |
Consistent collection and use | Standard rules for forms, marketing lists, HR data, CCTV | Approved templates, documented purposes, data inventory entries |
Controlled access | Role-based access, joiner-leaver process, secure sharing rules | Access reviews, account termination logs, sharing procedure |
Manageable retention and disposal | Retention rules by record type, secure disposal steps | Retention schedule, destruction certificates, deletion logs |
Rights readiness | Intake process, verification steps, response workflow | Rights request log, response templates, delivery records |
Incident readiness | Clear reporting path, triage, containment steps | Incident register, investigation notes, corrective actions |
Vendor control | Due diligence and contracting requirements | Vendor register, due diligence records, DP clauses in contracts |
Staff awareness | Role-based training, periodic refreshers | Training materials, attendance lists, assessment results |
If you cannot point to evidence for at least half of these, your policy is likely not embedded.
A practical outline: what to include in a data protection policy
While every organisation is different, most effective policies cover the following areas clearly (without legal jargon):
Scope (who and what it applies to, including contractors and temporary staff)
Definitions (personal data, sensitive data, processing, third party)
Principles and standards (fairness, purpose limitation, minimisation, accuracy, storage limitation, security, accountability)
Roles and responsibilities (including escalation contacts)
Lawful basis and approved purposes (at a policy level, not a full legal memo)
Data handling rules (collection, sharing, remote work, paper records, messaging apps)
Security expectations (minimum controls and prohibited behaviours)
Retention and disposal rules (and where schedules live)
Rights request handling (how to recognise and route requests)
Incident reporting requirements (what counts as an incident, who to notify internally)
Vendor and cross-border processing rules
Training and enforcement
Review cycle and version control
If you also maintain a detailed procedures pack, the policy should point to those procedures and templates rather than duplicating them.
To benchmark your documentation set, you can compare against: Privacy and Data Protection: A Practical Checklist.
Common mistakes that stop a policy from achieving its purpose
Writing it as a legal document instead of an operational tool
If the only people who can understand it are lawyers or compliance officers, it will not change staff behaviour.
Treating the policy as a one-time deliverable
A policy is a living control. If you do not review it after incidents, new systems, reorganisations, or regulatory updates, it becomes outdated fast.
Making rules you cannot enforce
For example, banning all use of personal devices when the organisation depends on them, or requiring approvals that no one has time to provide. Unrealistic rules lead to silent non-compliance.
Ignoring the “shadow systems”
In many organisations, personal data sits in email inboxes, WhatsApp threads, spreadsheets, paper files, and personal USB drives. Your policy must address real workflows, not ideal ones.
How to make your data protection policy actually work
A policy achieves its purpose only when it is adopted and reinforced.
Start with these practical steps:
Align stakeholders early: HR, IT, Operations, Customer Service, Marketing, Procurement.
Map your most important data flows (customer onboarding, HR lifecycle, incident reporting, vendor onboarding).
Draft in plain language and test it with real scenarios.
Approve it formally and communicate it in multiple ways (email alone is not enough).
Embed it into onboarding, procurement checklists, and system change processes.
Review it on a set schedule and after major changes.
If you are building a broader governance structure, integrate the policy into your GRC programme so privacy risk is assessed and tracked like any other risk.

Frequently Asked Questions
What is the purpose of a data protection policy? The purpose of a data protection policy is to set clear internal rules for handling personal data so staff act consistently, risks are reduced, and the organisation can demonstrate accountability and compliance.
Is a data protection policy the same as a privacy policy on a website? No. A website privacy notice is written for the public and explains what you do with data. A data protection policy is an internal governance document that tells staff how to process personal data safely and lawfully.
Who should own a data protection policy in a company? Ownership should sit with a named role or function that can coordinate across departments, supported by senior leadership. Day-to-day responsibility often involves compliance, risk, legal, or a privacy lead, but HR, IT, and business units must have defined responsibilities.
How often should we review a data protection policy? At minimum, review annually. Also review after significant changes such as new systems, new vendors, restructures, incidents, or changes in regulatory expectations.
Do small businesses in Jamaica need a data protection policy? If a small business processes personal data (customers, employees, CCTV, marketing lists), a policy is a practical control to reduce mistakes and demonstrate responsible handling. It can be shorter, but it should still be clear and usable.
What should we show as proof that our policy is working? Keep evidence such as signed approvals and version history, training records, incident logs, rights request logs, vendor due diligence records, and retention schedules or disposal records.
Need a policy that stands up in real operations?
Privacy & Legal Management Consultants Ltd. (PLMC) helps Jamaican organisations design and implement practical data protection policies that align with real workflows and the Data Protection Act. If you want a policy that staff can follow and leadership can rely on, explore PLMC’s data protection implementation support or request a free consultation to discuss your current documentation and priority risks.
