
Privacy and Legal Policies: Aligning Rules Across the Business

Policy sprawl is one of the fastest ways to create compliance risk. A company can have a solid privacy notice, a decent employee handbook, and an incident response plan, yet still fail basic questions during an audit or investigation because the documents do not agree with each other. When privacy and legal policies conflict across departments, teams make inconsistent decisions about retention, access, monitoring, disclosures, and vendor use. That inconsistency is what turns everyday operations into regulatory exposure.
In Jamaica, the Data Protection Act (DPA) raises the bar for how organisations document and apply their rules, especially when personal data flows through HR, marketing, customer service, finance, IT, security, and third parties. Aligning policies is not just “paperwork”, it is how you make compliance operational.
What “privacy and legal policies” means in a real business
Most organisations have more policy documents than they realise. Some are formal and approved by the Board, others live as “process notes” in a shared drive, and a few exist only as institutional memory.
For alignment purposes, think of privacy and legal policies as a single ecosystem that covers:
External commitments: privacy notices, cookie notices, customer terms, vendor terms, marketing consent language.
Internal governance rules: data protection policy, information security policy, acceptable use, records management and retention, HR policies, CCTV and monitoring rules, whistleblowing, AML/CTF policies (where relevant), and third-party risk standards.
Operational playbooks: breach response, access request handling, onboarding and offboarding, vendor onboarding, secure disposal.
The problem is rarely that one policy is “wrong”. The problem is that each policy was written for a specific purpose, by a specific owner, at a specific time. Over the years, the documents drift.
Where misalignment creates the biggest risk (with practical examples)
Policy misalignment becomes visible when a staff member asks, “Which rule do I follow?” These are common friction points:
Retention: “Keep it forever” vs “keep it only as long as needed”
A records practice that defaults to long-term storage can clash with storage limitation expectations under data protection principles. If HR keeps applicant CVs indefinitely, or customer support keeps chat logs for years without a defined purpose, you can struggle to justify retention.
Security: IT controls exist, but legal documents do not match
IT may enforce strong access controls and logging, while contracts, privacy notices, or internal policies fail to describe how access is limited, how vendors are vetted, or what happens during an incident.
Monitoring and CCTV: security objectives without privacy guardrails
Security teams may deploy CCTV, access control systems, or device monitoring to protect people and property. Without aligned rules on signage, access to footage, retention, and disclosure, you risk inappropriate use or over-collection.
Marketing and consent: “We have opt-in” but the workflows do not support it
Marketing might publish consent language, but the CRM fields, unsubscribe process, and vendor mailing tools may not reliably record and respect a person’s choices.
Third parties: procurement moves faster than governance
Vendor onboarding often happens under time pressure. If procurement templates, IT security standards, and the privacy programme do not align, you may end up with contracts that do not reflect how data is actually processed.
If your organisation already has a general DPA compliance plan, a dedicated checklist can help you validate fundamentals. See: Privacy and Data Protection: A Practical Checklist.
Build a policy architecture that makes alignment easier
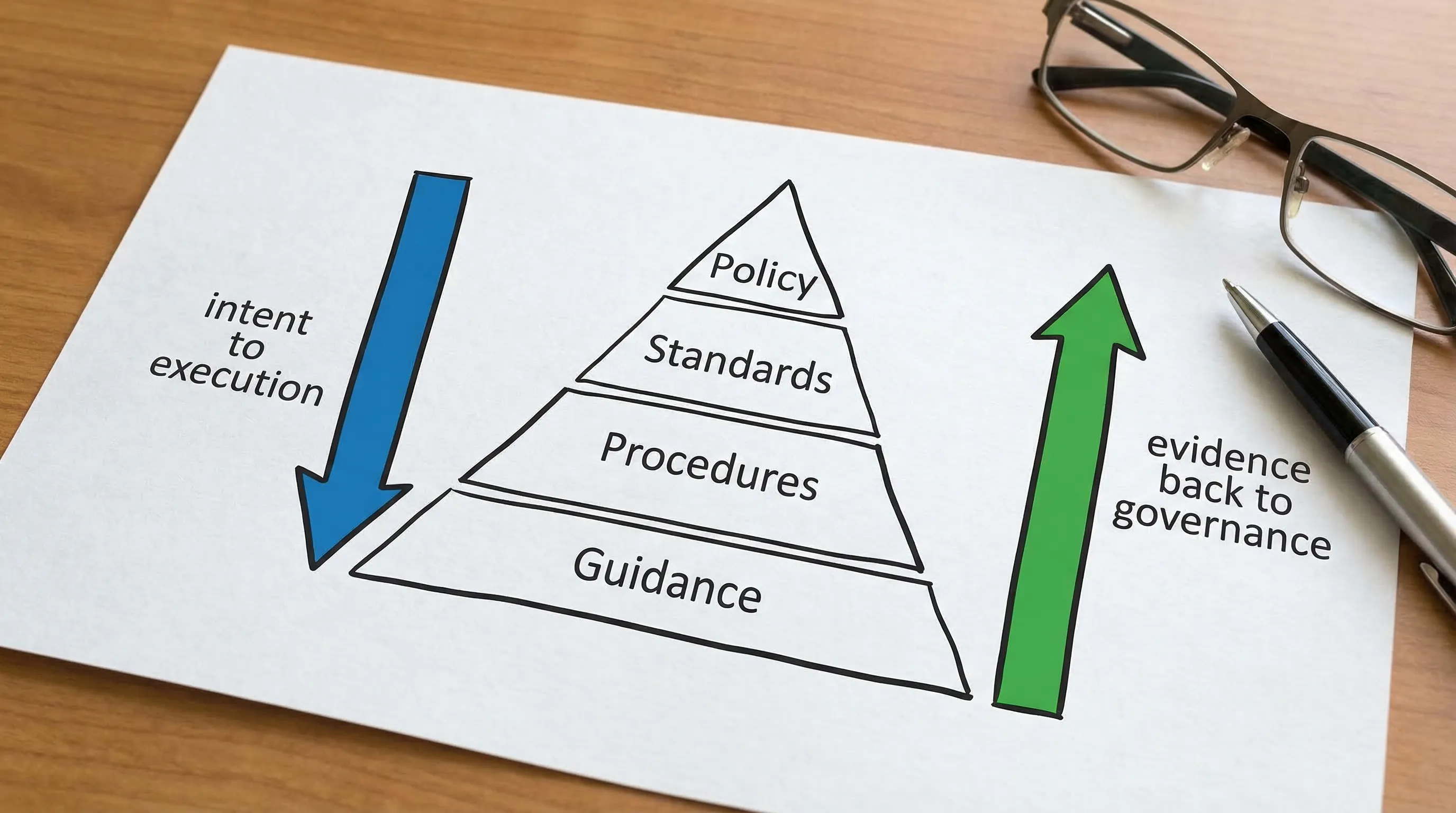
Alignment is much easier when your documents have a clear hierarchy. Otherwise, teams argue over which document “wins”. A simple, audit-friendly structure is:
Layer | Purpose | Example outputs | Who approves (typical) |
Policy | Sets the rule and intent (what and why) | Data Protection Policy, Information Security Policy, Records Retention Policy | Executive leadership, Board (depending on governance) |
Standard | Defines minimum requirements (how good is “good enough”) | Password standard, encryption standard, vendor due diligence standard | Senior management, risk/compliance |
Procedure | Step-by-step actions (how to execute) | DSAR procedure, breach reporting procedure, offboarding procedure | Process owners |
Guidance | Tips and examples (how to do it well) | “How to share data securely”, “Emailing personal data guidance” | Privacy/security leads |
This structure reduces contradictions because each layer has a job. Your privacy notice and external terms should then be aligned to the policy layer, not written in isolation.
A practical method to align rules across the business
Below is a method PLMC often recommends because it creates a clear line from legal obligations to day-to-day decisions, without rewriting everything from scratch.
1) Create a single inventory of policy documents (yes, all of them)
Start with a lightweight inventory that captures the document name, owner, last update date, scope, where it is stored, and whether staff can find it.
Do not limit this to “privacy documents”. Include HR, IT, physical security, customer service, procurement, AML/CTF, and corporate governance artefacts. A privacy programme fails in practice when one team’s rules sit outside the governance perimeter.
2) Standardise definitions so departments stop speaking different languages
Misalignment often comes down to words. “Personal data”, “confidential information”, “sensitive data”, “incident”, “breach”, “record”, “consent”, and “vendor” get defined differently across documents.
Create a shared glossary and require policies to reference it. This is a simple control with outsized impact, especially when you need consistent incident classification and reporting.
If your teams need a refresher on data protection concepts and roles (controller, processor, etc.), this guide can help: Data Protection Basics: What Jamaican Firms Must Know.
3) Map obligations to policies (one view that shows coverage and gaps)
Take key obligations relevant to your organisation (DPA requirements, sector rules, contractual duties, governance expectations) and map them to where they are addressed.
The output is not a long memo. It is a simple coverage map that answers:
Where is this requirement stated?
Where is it executed (procedure)?
What evidence proves it is followed?
This step prevents “policy theatre”, where rules exist only on paper.
4) Harmonise the high-risk “cross-cutting” topics
Some topics cut across every department. Align these first because they remove the biggest contradictions:
Retention and disposal: one retention schedule, applied through records management, HR, and IT systems.
Access control and least privilege: consistent access principles for HR files, customer databases, shared drives, and cloud tools.
Incident and breach handling: one definition of reportable events, one escalation path, one communications process.
Third-party management: one onboarding standard and contract baseline for vendors handling personal data.
Transparency: external notices, internal scripts, and customer service responses should agree.
If you want to align policies to the core rights and principles under Jamaica’s DPA, this companion article is useful: Data Privacy in Jamaica: Key Principles and Rights.
5) Assign ownership and approvals so alignment survives organisational change
Policies drift when nobody “owns” them. Every document should have:
A named business owner (accountable for content)
A privacy/legal reviewer (ensures compliance)
An information security reviewer (ensures controls match reality)
A review cycle (at least annually, and after major changes)
This is where corporate governance practices matter. If approvals are unclear, teams create side documents and the sprawl restarts.
6) Embed policies into workflows so staff do not have to “remember” them
Alignment succeeds when the right action is the easiest action. Convert policy requirements into operational hooks such as:
Vendor onboarding checklists and contract gates
HR onboarding training and confidentiality acknowledgements
CRM fields that capture consent and preferences
Ticketing categories for privacy incidents and requests
A policy that is not connected to a workflow is usually not being followed consistently.
What alignment looks like in practice (owners, checks, and evidence)
Use the table below as a starting point for cross-functional alignment. The goal is not to create bureaucracy. The goal is to ensure each area has an owner, consistent rules, and proof.
Policy area | Primary owner (typical) | Alignment checks | Evidence to keep |
Privacy notice and transparency | Legal/Privacy | Matches actual processing, retention statements, rights process, vendor disclosures where needed | Published notices, change log, internal “processing notes” |
Records retention and disposal | Records Management/Operations | Retention periods match legal needs and data minimisation, disposal is verifiable | Retention schedule, disposal logs, system retention settings |
Information security | IT/Security | Controls align with commitments in contracts and notices, access rules are consistent | Access reviews, security policies, logs, training completion |
HR data handling | HR | Recruitment, personnel files, monitoring, and disclosures follow defined rules | HR procedures, onboarding acknowledgements, role-based access |
Vendor and outsourcing | Procurement/Risk | Data processing terms, security requirements, subprocessor controls, exit/return or deletion | Due diligence records, signed contracts, vendor reviews |
Incident response | Security/Risk | One definition of incident, one escalation route, privacy input included early | Incident register, tabletop exercises, post-incident reviews |
Fast wins that reduce risk without a full rewrite
If you need immediate progress, focus on the mismatches that create real-world harm:
Fix contradictions on retention: ensure your privacy notice, retention schedule, and system settings do not tell three different stories.
Unify incident language: make “incident” and “breach” definitions consistent across security, HR, and privacy documents.
Standardise vendor clauses: adopt a baseline addendum for vendors processing personal data and require it through procurement.
These moves create alignment that auditors and regulators can see, and staff can follow.
How to measure whether policy alignment is actually working
Policy alignment should show up as fewer exceptions, quicker response times, and clearer decision-making. Practical indicators include:
Reduced time to answer “Which policy applies?” questions from staff
More consistent retention and deletion outcomes across systems
Faster incident triage because severity criteria are shared
Fewer contract exceptions for data protection and security clauses
Better quality responses to access or correction requests because procedures match the notice
For organisations building a year-round plan, you can also use a roadmap approach to structure governance and evidence over time. See: Data Protection Jamaica: Compliance Roadmap for 2026.

Frequently Asked Questions
Do we need separate privacy policies for each department? Not usually. You typically need one organisational privacy policy, supported by role-based procedures (HR procedure, marketing procedure, incident procedure) that apply the same principles consistently.
Who should own privacy and legal policy alignment? Treat it as a governance task. Assign a business owner for each policy, then ensure privacy/legal and information security have formal review roles. Alignment fails when it is left to one department without cross-functional authority.
How often should we review privacy and legal policies? At minimum annually, and any time you change systems, vendors, products, workplace monitoring, or how you collect and use personal data. Reviews should also follow incidents and audit findings.
What is the biggest policy conflict you see in practice? Retention is a frequent one. Many organisations publish broad retention statements while operational teams keep data indefinitely because systems lack deletion routines or nobody owns the schedule.
Do our contracts need to match our privacy notice? Yes. If your notice says you limit sharing, but your vendor contracts allow broad reuse or weak security, you have a gap between commitments and reality. Alignment requires both documents to reflect the same rules.
Is policy alignment only a “privacy” issue? No. It strengthens Governance, Risk, and Compliance overall, including cyber security readiness, corporate governance consistency, and third-party risk management.
Need help aligning privacy and legal policies across your organisation?
Privacy & Legal Management Consultants Ltd. (PLMC) supports organisations in Jamaica with data protection implementation, GRC integration, cyber security services, training sessions, and practical tools to assess risk and readiness.
If you want a clear, workable set of rules that departments can follow consistently, you can request a free consultation via Privacy & Legal Management Consultants Ltd. to discuss a policy alignment review, documentation clean-up, and an implementation plan tailored to your operations.
