
Legal Data Handling: Retention, Access, and Disclosure

Retention, access, and disclosure are where “privacy on paper” most often breaks down in real operations. Files sit in shared drives for years “just in case”, someone forwards a spreadsheet to the wrong external address, a manager shares CCTV clips in a WhatsApp group, or a team delays a data access request because they are not sure who owns the process.
For Jamaican organisations working toward compliance with the Data Protection Act, 2020, these three activities also tend to create the clearest evidence trail (or the clearest gaps). Done well, they show accountability, disciplined governance, and respect for individual rights. Done poorly, they can quickly become regulatory, contractual, and reputational risk.
This guide focuses on practical, defensible ways to handle:
Retention (how long you keep personal data, and how you dispose of it)
Access (how you respond to individuals who ask for their personal data)
Disclosure (how and when you share personal data internally and externally)
(As always, this is practical information, not legal advice. Your retention and disclosure decisions should reflect your sector, contracts, and any other laws that apply.)
What “legal data handling” means in practice
Under Jamaica’s Data Protection Act, 2020, good data handling is not just about having a privacy notice. It is about running a consistent operational system that aligns with core data protection ideas you will also recognise from GDPR-style programmes, including:
Purpose limitation: collect and use personal data for specific, legitimate reasons.
Storage limitation: do not keep personal data longer than necessary.
Security and confidentiality: protect data against unauthorised access, loss, or disclosure.
Transparency and individual rights: be clear about what you do, and enable access rights.
Accountability: document decisions and be able to demonstrate compliance.
A useful way to frame the topic is to view personal data as moving through a lifecycle: collect, use, store, share, archive, dispose. Retention, access, and disclosure each sit at points in that lifecycle where mistakes are common and consequences are high.

If you are still building your broader privacy programme, PLMC’s practical starting points can help you connect these operational areas to your overall compliance roadmap:
Data retention: keep what you need, delete what you do not
Retention is easy to get wrong because it is rarely owned by one team. HR keeps files “forever”, IT keeps backups “just because”, and business units keep data exports locally for convenience.
A compliant retention approach has two parts:
Rules: documented retention periods and triggers.
Execution: consistent deletion, anonymisation, or secure destruction, plus evidence.
Step 1: Build a retention schedule that matches how the business operates
A retention schedule is not only a spreadsheet. It is a governance tool that connects your personal data to:
The purpose(s) for processing
Any legal or regulatory retention requirements you must meet
Operational needs (for example, customer support history)
Risk (for example, sensitive data needing stricter controls)
Instead of starting with “how long should we keep everything?”, start with “what data sets do we hold?” and “what is each used for?”. Data mapping and inventory work makes retention decisions easier to defend.
A retention schedule is typically easiest to manage when it is grouped by data category and system owner.
Data category (examples) | Typical retention trigger | Key risk if kept too long | What “good” looks like |
HR and recruitment records | End of employment, end of recruitment process | Unnecessary exposure of sensitive or outdated info | Clear HR retention rules, restricted access, timely disposal |
Customer account records | Account closure, contract end | Identity and fraud risks, unnecessary exposure | Defined retention by customer type, documented deletion workflow |
CCTV / security footage | Recording date | High sensitivity, misuse risk | Short, defined retention, controlled access, disclosure log |
Marketing contacts | Withdrawal of consent, inactivity threshold | Complaints, enforcement risk, poor trust | Clean suppression lists, prompt updates across tools |
Incident and investigation files | Case closure, legal hold lifted | “Secondary use” creep, internal gossip | Need-to-know controls, strict retention and access |
Note: The right retention period depends on your sector and obligations. The key is that it is defined, justified, and implemented.
Step 2: Define retention “triggers”, not just time periods
Retention often fails because teams only define a number of months or years, but not the event that starts the clock.
Examples of practical triggers include:
Date the customer relationship ends
Date a matter is closed (complaint, case, investigation)
Last activity date for an account
Date a consent is withdrawn
When you define the trigger, you also make it easier to automate retention in systems.
Step 3: Design disposal that is secure and auditable
A defensible retention programme includes disposal methods that match the format of the data:
Paper records: secure shredding, controlled bins, vendor certificates (where used).
Digital records: deletion from systems plus controls for archives and shared drives.
Backups: ensure backups are governed (retention, access, restore procedures) so you are not “keeping everything forever” by accident.
For many organisations, a good first milestone is creating a disposal procedure with clear responsibilities across HR, IT, Legal/Compliance, and each business owner.
Step 4: Use “legal holds” properly
Sometimes you must keep data longer than normal because of litigation, investigations, or regulatory inquiries. That is not a retention failure, it is a controlled exception.
A simple legal hold approach should:
Identify who can approve a hold
Specify what data is in scope
Prevent deletion while the hold applies
Specify the release process when the hold ends
This prevents ad hoc over-retention where teams keep everything “just in case” for years.
Access: handle requests consistently, securely, and on time
Under modern data protection regimes, individuals may request access to their personal data. Organisations often call this a data subject access request (DSAR) or simply an access request.
The main risk points are not only legal deadlines, they are operational:
You disclose the wrong person’s data due to weak identity verification.
You miss data in key systems because searches are inconsistent.
You release sensitive information without appropriate review and redaction.
You respond inconsistently, creating complaints and distrust.
A practical access request workflow
Your goal is to make access requests routine, not urgent.
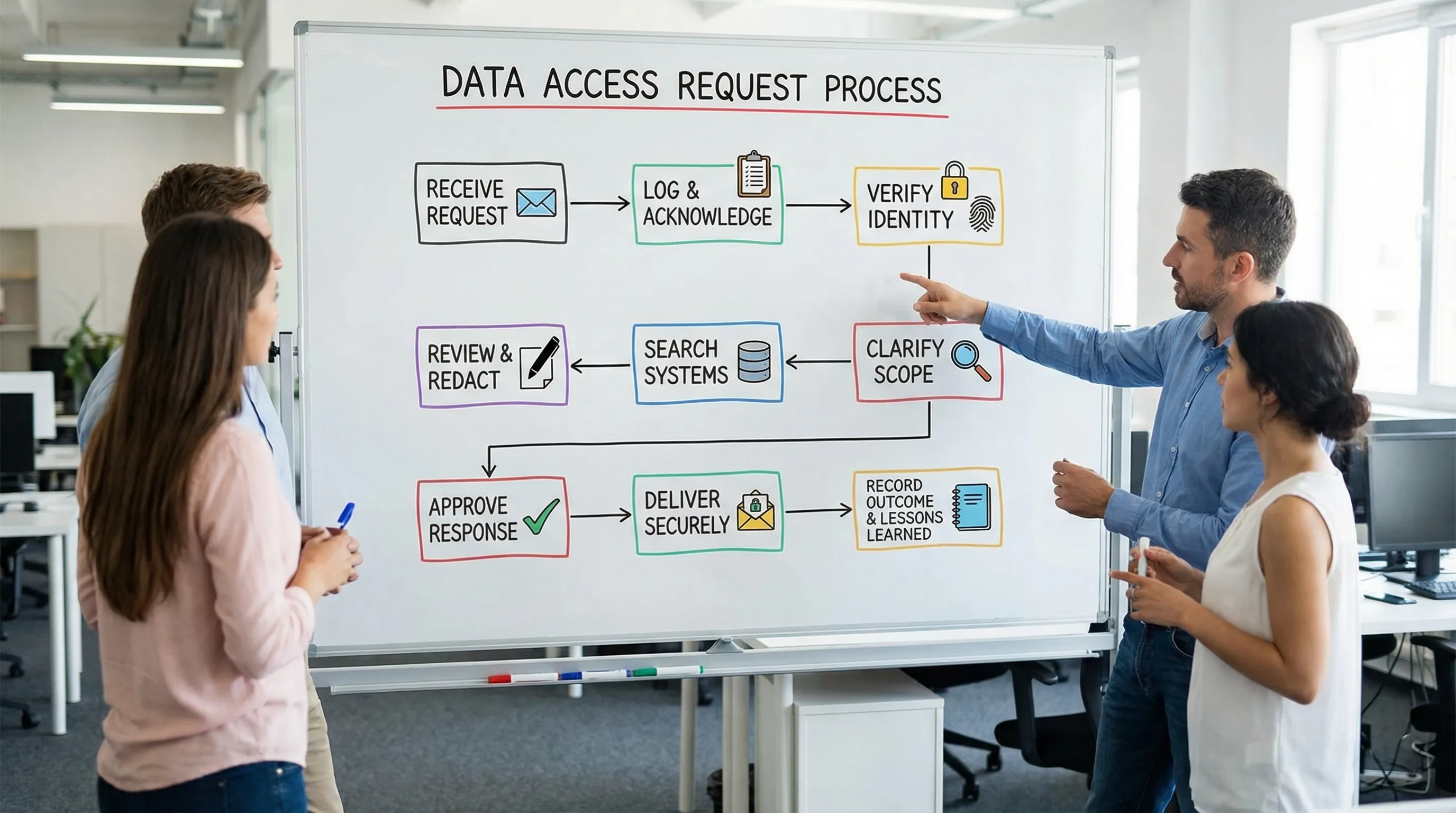
A simple, defensible workflow includes:
Intake and logging: one channel (email address or form), one log, one owner.
Identity verification: proportional to risk. If the data is sensitive, verification should be stronger.
Scoping: clarify what the person is asking for (time period, systems, specific records).
Search and collection: documented system list and search steps.
Review: check for third-party information and sensitive internal commentary.
Secure delivery: avoid sending large personal data bundles through unsecured channels.
Closure: log what was provided, when, and why any information was withheld.
If you need a reference point for how regulators tend to interpret “reasonable” access handling, the UK Information Commissioner’s Office has practical guidance on subject access requests that many Caribbean organisations use as a benchmark while local enforcement expectations mature: ICO guidance on the right of access.
Common access request pitfalls (and how to prevent them)
Mistake: Treating requests as informal customer service emails. Fix it by training staff to recognise access requests and route them to a central process.
Mistake: Responding without identity verification. Fix it with a short verification checklist aligned to the sensitivity of the data and the channel used.
Mistake: Exporting entire databases “to be safe”. Fix it by applying data minimisation. Provide what is relevant to the request, not everything the organisation has ever stored.
Mistake: Missing data in shared drives and email. Fix it by defining a repeatable search plan (systems plus custodians) and documenting it.
Disclosure: share personal data lawfully and with controls
“Disclosure” covers any sharing of personal data outside the original team that collected it, including:
Sharing with service providers (processors) such as payroll, cloud systems, or call centres
Sharing with partners (other controllers) such as financial institutions, insurers, or affiliates
Sharing with authorities (law enforcement or regulators) based on a lawful request
Sharing internally where there is no legitimate need-to-know
The safest approach is to treat disclosure as a decision that must be justified, limited, and recorded.
A disclosure decision checklist (what to validate before sharing)
Before you disclose personal data, confirm:
Authority: Do we have a lawful basis or legal obligation to share?
Necessity: Is the disclosure necessary for the stated purpose, or could we share less?
Scope: What is the minimum data required?
Security: How will data be transmitted and stored by the recipient?
Transparency: Have we told individuals in our privacy notice that this disclosure may occur (where appropriate)?
Documentation: Do we have a record of what was shared, to whom, when, and why?
Common disclosure scenarios and recommended controls
Scenario | Main risk | Recommended controls |
Vendor receives employee data for payroll | Excess access, onward sharing | Written contract, access limitation, security requirements, deletion obligations |
Customer data sent to a courier or delivery partner | Over-sharing (sending more than needed) | Share only delivery fields, restrict re-use, confirm retention and security |
CCTV footage request (individual, police, insurer) | Misuse, third-party exposure | Validate request authority, redact where feasible, log disclosures |
Internal “need help” email with attachment of customer info | Accidental wide distribution | Role-based access, secure file sharing, training on safe collaboration |
Sending data to overseas service providers | Cross-border risks | Due diligence, contractual safeguards, clear transfer governance |
For organisations that also align with GDPR-style expectations (common where you serve EU residents or work with EU partners), keep an eye on cross-border and processor management standards. The European Data Protection Board publishes guidance that many global companies use as a reference point: EDPB guidelines and recommendations.
Do not forget internal disclosure
Many incidents start internally, not with hackers. Practical internal disclosure controls include:
Access based on role and job function
Avoiding shared generic accounts
Approval steps for sensitive disclosures (HR, medical, investigations)
Clear rules for using messaging apps and personal email
The evidence you should be able to produce (and why it matters)
Compliance is not only the policy, it is the proof. For retention, access, and disclosure, an organisation should be able to show evidence such as:
Area | “Good evidence” examples | Why it matters |
Retention | Retention schedule, disposal procedure, deletion logs, legal hold register | Shows you are not keeping data indefinitely and can prove disposal |
Access | Request log, identity verification steps, response templates, redaction approach | Shows consistent rights handling and reduces disclosure errors |
Disclosure | Data sharing agreements, vendor due diligence, disclosure register, secure transfer records | Shows controlled sharing and accountability |
Training | Attendance records, role-based training content, refresh cycles | Proves staff are equipped to follow the process |
If you want a structured way to assess readiness, PLMC’s resources on operationalising compliance (not just documenting it) can help: Data Protection Jamaica: Compliance Roadmap for 2026.
Common “silent failures” to watch for
These issues often sit unnoticed until an incident or complaint occurs:
No retention enforcement: a schedule exists but systems and teams do not follow it.
Uncontrolled exports: staff download customer or employee lists to desktops and USB drives.
Access requests handled informally: inconsistent responses across departments.
Disclosure without documentation: data is shared “because we always do” with no record.
Backups treated as exempt: backups become a long-term store of personal data with unclear access and retention.
A quick self-check for your organisation
If you can answer “yes” to most of these, you are in a strong position:
We can explain, per system, what personal data we hold and why.
We have a retention schedule with triggers and owners, not only suggested time periods.
We can delete or anonymise data in practice (including in archives and shared drives).
We have one access request workflow, with identity verification and a request log.
We can describe when and how we disclose data, and we can show contracts and records.
If several are “no” or “not sure”, the fix is usually not complicated, it just needs ownership and governance.
Frequently Asked Questions
What is the difference between retention and archiving? Retention is the overall rule for how long you keep personal data for a defined purpose. Archiving is a storage state, not a justification. Archived personal data still needs a lawful purpose, limited access, and an end date (or clear disposal trigger).
Do we have to delete personal data from backups to comply with retention rules? Backups are part of your retention reality. Many organisations manage this by setting backup retention limits, restricting access to backups, and ensuring deleted data is not routinely restored into active systems except for genuine recovery needs.
How do we respond to an access request without exposing another person’s data? Use a review and redaction step before release, especially for emails, CCTV, complaints, and investigation files. Where records include third-party data, you may need to redact or withhold parts, depending on the context and lawful limitations.
When can we disclose personal data to law enforcement? Treat this as a controlled disclosure. Validate the authority and scope of the request, share only what is necessary, use secure transmission, and record what was disclosed and why. Where appropriate, involve your legal/compliance lead.
Do we need a disclosure register? It is one of the most effective accountability tools. Even a simple register that captures date, recipient, data type, purpose, legal basis, and approver can dramatically reduce repeat mistakes.
Need help operationalising retention, access, and disclosure in Jamaica?
If your organisation has policies but is still struggling with execution, PLMC can help you translate requirements into day-to-day controls. That includes building retention schedules, setting up access request workflows, training staff, and strengthening disclosure governance within a broader GRC approach.
Explore PLMC’s data protection resources, or request a free consultation via Privacy & Legal Management Consultants Ltd..
