
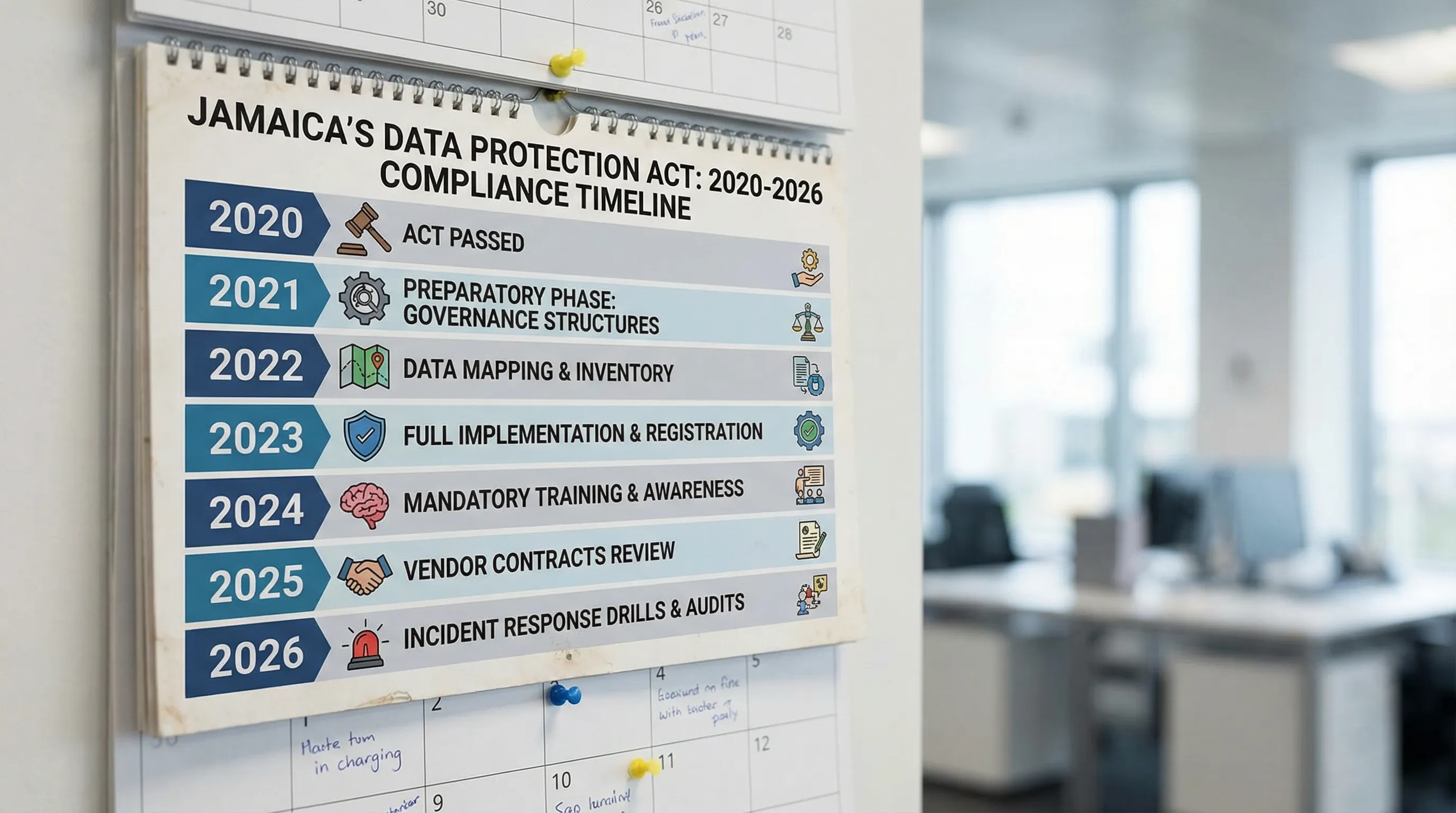
Jamaica Data Protection Act 2020: Compliance Timeline

Many organisations in Jamaica know the Data Protection Act, 2020 exists, but still feel uncertain about one practical question: when exactly does each compliance expectation apply, and what should we have done by now? The confusion is understandable because the Act was passed in 2020, but (like many modern regulatory regimes) its real-world impact depends on commencement and transition arrangements.
This guide breaks the Jamaica Data Protection Act 2020 compliance timeline into clear milestones, explains what each phase means for your business or public body, and offers a pragmatic “catch-up” plan for 2026 if you are still closing gaps.
Where we are now (2026)
For most organisations, 2026 should be treated as the period where data protection compliance is no longer a project or a “transition item”, but an operational requirement that needs evidence.
If your organisation relied on the transition window to delay implementation, the risk now is not only legal exposure, but operational disruption when:
a customer, patient, student, employee, or member submits a rights request
a vendor or overseas partner asks for assurance documentation
a security incident triggers internal and external reporting obligations
your board or senior leadership asks for a defensible risk position
Because commencement dates and any extensions are set via formal instruments, you should verify the current position using authoritative Jamaican sources (for example, the Office of the Information Commissioner and official Government of Jamaica communications). If you want an implementation view of what “good” looks like in practice, PLMC’s resources like the Privacy and Data Protection: A Practical Checklist and the Data Protection Jamaica: Compliance Roadmap for 2026 complement this timeline.
Jamaica Data Protection Act 2020: the core compliance timeline
The most useful way to understand the timeline is to separate:
the law’s passage (2020)
the appointed day (commencement)
the transition period (where applicable)
the enforcement-focused period (post-transition)
Even if your organisation is unsure of the exact dates that apply to you, the operational message remains consistent: you should be able to show that you understand your personal data footprint, have governance and controls in place, and can respond to individuals and incidents.
Timeline at a glance
Timeline milestone | What it means in plain English | What organisations should do in this phase |
2020 (Act passed) | Jamaica establishes a modern data protection framework aligned to global privacy expectations. | Start gap assessment, brief leadership, budget for compliance, and begin mapping high-risk data (HR, customer, health, financial, children’s data). |
Appointed day (commencement) | The Act becomes legally “live” based on commencement arrangements. | Activate your privacy programme, publish or update notices, formalise responsibilities, and prioritise evidence, not just policies. |
Transition period (where applicable) | Time allowed to bring legacy processing and systems up to standard. | Complete core controls, train staff, contract with processors, establish rights handling and incident readiness, and fix high-risk processing first. |
Post-transition period (ongoing compliance) | Regulators, customers, and partners expect demonstrable compliance. | Maintain governance, test controls, run audits, keep records, refresh training, and embed privacy into projects and procurement. |
What “transition” should have produced (the minimum defensible position)
Transition periods do not exist to make compliance optional, they exist to make compliance achievable for organisations with legacy systems. By the end of transition (or, if you are past it, by now), an organisation should be able to demonstrate a working privacy management system.
Below is the minimum set of outcomes that tends to matter most in audits, investigations, and serious incidents.
Governance and accountability that works in real life
A regulator, board, or client will look for clear answers to basic questions:
Who owns data protection risk, and who is accountable for decisions?
Who approves privacy notices, retention rules, and vendor arrangements?
Who signs off privacy risk in projects (new apps, new databases, new outsourcing)?
This is where many programmes fail. Policies exist, but roles, escalation paths, and decision logs do not.
A usable data inventory (not a one-time spreadsheet)
A data inventory is not about documenting everything perfectly, it is about knowing what you have well enough to control it. If you cannot identify:
what personal data you collect
why you collect it
where it is stored
who you share it with
how long you keep it
then nearly every other obligation becomes difficult.
Privacy notices and transparency that match reality
Notices should reflect your actual processing activities, including the “less visible” ones such as:
CCTV and access control systems
background checks and references
cloud hosting and customer support tools
outsourced payroll, benefits, and HR platforms
If the public-facing notice says one thing and the operational reality is different, the notice becomes a risk.
Rights request handling (because it is guaranteed to happen)
In 2026, rights requests are increasingly normal, especially in sectors like financial services, telecoms, education, healthcare, and e-commerce.
A workable process typically includes:
intake channels (email, web form, in person)
identity verification standards
internal search and retrieval procedures
response templates and legal review
timelines and escalation rules
If you want a principles-and-rights refresher tailored to Jamaica, see Data Privacy in Jamaica: Key Principles and Rights.
Vendor and outsourcing controls (your fastest path to real risk reduction)
In Jamaican organisations, a significant portion of personal data handling happens through third parties: IT providers, HR vendors, payment processors, call centres, cloud services, marketing agencies, and security firms.
A defensible vendor posture usually includes:
a vendor register that flags which vendors process personal data
contract clauses and security requirements for those vendors
a lightweight due diligence process (risk-based)
offboarding controls (revoking access, confirming deletion/return)
Incident and breach readiness
You do not need a breach to prove readiness. You can demonstrate readiness through:
an incident response plan that includes privacy decision-making
a breach log (even if it is “no reportable breaches to date”)
evidence of at least one tabletop exercise or simulation
clear internal reporting channels (staff know who to call)
PLMC has also highlighted how sensitive categories of data can elevate risk and expectations, for example in COVID-19 results are protected by the Data Protection Act.
If you are behind in 2026: a practical 30 to 90 day catch-up timeline
If your programme is late, the goal is not to “do everything”, it is to reach a defensible baseline quickly, then deepen controls over time.
Days 0 to 30: stabilise and reduce obvious exposure
Focus on actions that reduce risk fast and create management visibility.
Confirm your lead person and escalation path for privacy issues
Stand up a simple data inventory for your top 10 systems and highest-risk processes
Patch the biggest transparency gap (update or publish your privacy notice where needed)
Identify your top 10 data-processing vendors and locate contracts
Ensure basic security hygiene is in place (access control, MFA where possible, backup discipline)
Days 31 to 60: build repeatable processes
At this stage you are building capability, not just documents.
Implement a rights request workflow and test it end-to-end
Create a breach triage checklist and decision log format
Build a retention and disposal approach for the top 5 data sets (HR, customer, finance, CCTV, marketing lists)
Align vendor contracts with data protection expectations and start due diligence
Days 61 to 90: make it auditable
Now you focus on evidence, governance cadence, and embedding.
Run a tabletop incident simulation and document lessons learned
Put a quarterly privacy reporting pack in place (metrics, incidents, requests, vendor status)
Add privacy checkpoints to procurement and project initiation
Deliver role-based training (frontline intake, HR, IT, marketing, management)
This approach is compatible with PLMC’s longer-form implementation guidance in Jamaica Data Protection Act Explained for Businesses and the 2026 deliverables approach in the Compliance Roadmap for 2026.
What evidence should exist by now (the “show me” test)
A common weakness in privacy programmes is that organisations can describe what they intend to do, but cannot prove what they have done. In 2026, you should assume any serious question will become a “show me” exercise.
Here is the type of evidence that stands up well in reviews.
Area | Practical evidence examples | Why it matters |
Governance | assigned responsibility, meeting minutes, decision logs, reporting cadence | Proves accountability is real, not aspirational. |
Data inventory | system list, processing purposes, data categories, sharing, retention, owners | Enables every downstream control (rights, security, retention, vendors). |
Transparency | current privacy notice(s), internal scripts for frontline staff, cookie disclosures where relevant | Reduces complaints and builds trust. |
Rights handling | procedure, templates, request log, sample case files with redactions | Demonstrates you can comply under time pressure. |
Vendor management | vendor register, due diligence records, contract clauses, access reviews | Shows control over outsourced processing. |
Security and incidents | incident plan, tabletop results, breach log, access control records | Proves readiness and reduces impact when incidents occur. |
Training | attendance records, role-based materials, onboarding inclusion | Shows organisational awareness and reduces human error. |
Common timeline mistakes Jamaican organisations should avoid
Treating data protection as “a policy upload”
Uploading a privacy policy is not compliance. Compliance is operational, cross-functional, and evidence-based. If IT, HR, customer service, procurement, and marketing are not aligned, the programme will break under pressure.
Waiting for perfect information before starting
Many teams delay because they want a complete data map or a finalised toolset first. Instead, start with the highest-risk processing and the systems with the largest volumes.
Ignoring cross-border and cloud reality
Even SMEs commonly use overseas-hosted services for email, CRM, HR, analytics, and payments. Your timeline should include transfer governance and vendor assurance early, not as a “Phase 3” item.
Underestimating people risk
In incident investigations, the root cause is often operational: shared accounts, weak access controls, poor offboarding, phishing, misdirected emails, or lack of training.

When to get external help (and why it saves time)
If any of the following are true, it is usually more cost-effective to get advisory or implementation support rather than trying to build everything from scratch:
you process sensitive data at scale (health, financial, children’s data)
you have multiple branches, affiliates, or shared systems
you have had a recent incident, complaint, or serious vendor issue
you are implementing a new platform (CRM, HRIS, core banking, customer app)
PLMC supports Jamaican organisations with data protection implementation, training, and integrated GRC support. To explore resources or request guidance, visit Privacy & Legal Management Consultants Ltd. and review the blog and tools available.
