
Difference Between Privacy and Data Protection: Real Examples

People often use “privacy” and “data protection” as if they mean the same thing. In practice, they are related but not identical, and confusing them can lead to gaps in compliance, customer trust issues, and avoidable incidents.
In Jamaica, that difference matters even more now that organisations are actively operationalising the Data Protection Act, 2020 across HR, customer service, marketing, security, and vendor management. This guide breaks down the difference between privacy and data protection using real-world examples, so you can spot what’s missing in your programme.
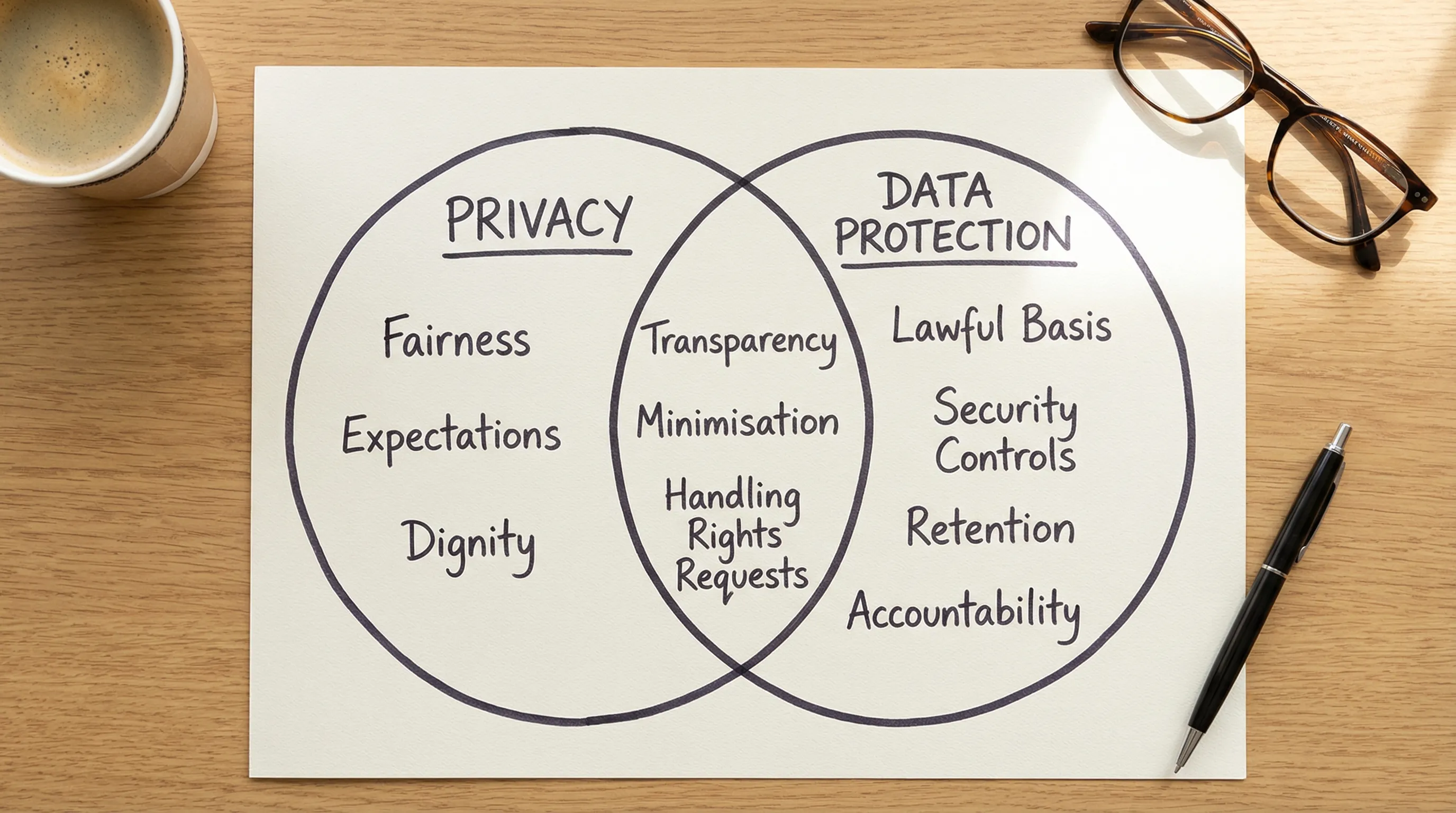
Privacy vs data protection (plain-English definitions)
Privacy is about people’s expectations and rights around how their personal lives and information are treated. It answers: Should we collect or use this information in the first place, and is it fair to the person?
Data protection is about the rules, controls, and accountability for processing personal data. It answers: If we process personal data, are we doing it lawfully, securely, transparently, and with appropriate governance?
They overlap heavily, but they are not interchangeable.
A simple way to remember the difference
Privacy focuses on people (dignity, autonomy, reasonable expectations, and impact).
Data protection focuses on processing (lawful basis, purpose limitation, minimisation, retention, security, rights handling, vendors, and evidence).
Topic | Privacy is mainly about… | Data protection is mainly about… | What “good” looks like in practice |
Core question | “Is this intrusive or unfair?” | “Is this lawful, controlled, and documented?” | Your business can justify the processing, and the individual is not surprised or harmed. |
Typical focus | Proportionality, expectations, transparency, choice | Policies, procedures, technical and organisational measures, records | Clear notices, limited collection, access controls, retention rules, vendor contracts, audit trail. |
Common mistake | Assuming “we told them” makes it acceptable | Assuming cybersecurity controls alone equal compliance | You manage both: fairness and legality, plus safeguards and accountability. |
Real examples: what changes when you look through a privacy lens vs a data protection lens
Below are scenarios Jamaican organisations deal with every day. For each one, notice how the privacy question and the data protection requirements differ.
1) CCTV in a lobby or on a compound
Privacy issue: Are you monitoring more than you need to? For example, cameras pointed into staff break areas, a neighbouring property, or a clinic waiting room can feel excessive and intrusive.
Data protection issue: CCTV footage can be personal data. You need controls such as:
Clear signage and a notice that explains who operates the system and why
Strict access (who can view, export, or share footage)
A defined retention period (not “keep it forever”)
Secure storage and a process for responding to access requests or incidents
Practical example: A business may have excellent camera encryption (data protection control) but still create a privacy problem if the placement is disproportionate.
2) Collecting TRN, ID, and “just in case” details at sign-up
Privacy issue: People reasonably expect to provide only what’s needed. Collecting TRN or a copy of ID for a low-risk service can be seen as overreach.
Data protection issue: If you collect it, you must be able to justify it, secure it, restrict access, and delete it when no longer necessary. You also need to communicate clearly, in plain language, what you collect and why.
Practical example: A front desk form that asks for date of birth, TRN, and address when an email and phone number would do is both a privacy red flag (unnecessary intrusion) and a data protection risk (more sensitive data to safeguard).
3) HR managing sick leave, medical notes, or wellness information
Privacy issue: Even within an organisation, staff expect sensitive information to be handled discreetly. Sharing details broadly (for example, in a group chat or an open email thread) can be humiliating and harmful.
Data protection issue: Health-related information is highly sensitive. You need tighter governance, including strict role-based access, secure storage, controlled sharing, retention rules, and training for supervisors on what should never be circulated.
Practical example: A manager may mean well by telling a team “she is out with X condition” (privacy harm), while HR may also be storing medical notes in an unsecured shared drive (data protection failure).
4) Marketing: WhatsApp broadcasts, email campaigns, and “we already have your number”
Privacy issue: People don’t want surprise marketing. If they gave a number for delivery updates, they typically do not expect weekly promotions.
Data protection issue: Marketing requires a clear lawful basis and good governance: consent where needed, opt-out mechanisms, suppression lists, records of what people agreed to, and controls over who can export customer lists.
Practical example: A business can provide an opt-out link (data protection mechanism) but still get privacy wrong if it sends promotions to customers who never reasonably expected marketing from that interaction.
5) Customer service calls and call recording
Privacy issue: Recording can feel invasive unless customers are told clearly and early, and the purpose makes sense (quality assurance, dispute resolution).
Data protection issue: Recordings need retention limits, restricted access, secure storage, and a process to locate recordings for access requests or complaint handling.
Practical example: Recording may be legitimate, but keeping recordings indefinitely “because storage is cheap” is a data protection weakness and increases breach impact.
6) Sharing data with vendors (payroll, cloud storage, IT support, marketing agencies)
Privacy issue: People often do not expect their information to be shared widely with third parties, especially across borders, unless this is explained.
Data protection issue: You need governance over processors and third parties: due diligence, contract terms, security expectations, clear instructions, and ongoing oversight. If data leaves Jamaica, you also need to manage cross-border transfer risk.
Practical example: A vendor may offer strong security certifications, but privacy can still be harmed if customers were never told their data would be processed by that third party for that purpose.

Why organisations get stuck: common “privacy vs data protection” mix-ups
Most compliance gaps come from treating one as a substitute for the other.
“We have cybersecurity, so we’re compliant”
Strong cybersecurity is essential, but data protection is broader than security. You still need purpose limitation, minimisation, transparency, retention, vendor oversight, and rights-handling processes.
“We posted a privacy notice, so it’s handled”
A notice supports transparency, but privacy also requires fairness and proportionality. Data protection requires operational controls and evidence, not just a statement on a website.
“Consent solves everything”
Consent is not a magic wand. If your collection is excessive or your use is unexpected, you can still create privacy harm. Also, consent needs to be meaningful and manageable (including withdrawal), which requires governance.
“Only the legal team needs to care”
Privacy and data protection live in daily operations: HR, IT, customer service, sales, procurement, and security. If those teams are not trained and accountable, compliance becomes theoretical.
How to build a programme that covers both (without overcomplicating it)
A practical approach is to treat privacy and data protection as two outputs of the same operating system: you design processing to be fair to people, and you control it like a regulated business process.
1) Start with purpose and proportionality (privacy-first design)
Before forms, tools, or policies, define:
The purpose (what problem are you solving?)
The minimum data required
Who truly needs access
What would surprise or upset a reasonable person
If you cannot justify the collection or the use, don’t “secure it better”, reduce it.
2) Turn that into data protection controls you can evidence
Once you decide the processing is justified, implement controls you can prove:
Clear notices and scripts (front desk, call centres, online forms)
Access controls and logging for sensitive datasets
Retention schedules and secure disposal
Vendor contracts and due diligence
Rights request workflows (so you can respond accurately and on time)
Incident response and breach readiness
If you need a Jamaican-focused implementation path, PLMC’s resources on the Act and operational steps can help you connect requirements to real deliverables, including:
3) Train teams on “moments that matter”
Annual training is rarely enough. Focus on high-risk moments:
HR onboarding and employee relations
Customer complaints and verification calls
Marketing list building and message sending
Sharing information with contractors
Handling medical or financial information
Practical training reduces privacy harm (what people experience) and strengthens data protection performance (what the organisation can defend).
Quick self-check: are you managing privacy, data protection, or both?
Use these prompts to identify gaps quickly. If you answer “no” to several, you likely have both privacy and data protection exposure.
Can we explain, in plain language, why we collect each field on our main forms?
Do we have a defined retention period for key datasets (CCTV, HR files, customer records, call recordings)?
Do staff know what they must never share on WhatsApp or in informal channels?
Can we locate and respond to an access request without scrambling across inboxes and shared drives?
Do we know which vendors handle personal data, and do we have contracts and oversight in place?
Are we collecting data that would surprise a reasonable customer or employee?
Do we have a simple approval step for new projects that involve personal data (new app, new camera, new CRM, new marketing tool)?
For a more operational checklist (evidence, documents, and controls), see: Privacy and data protection: a practical checklist
When to get specialist support
Some situations are high-impact and benefit from an outside review because the risk is not only legal, it’s reputational and operational.
Consider support if you are:
Rolling out CCTV, biometrics, new access control, or monitoring tools
Migrating to a new HRIS, CRM, or cloud platform
Expanding marketing activity (especially new channels like WhatsApp broadcasts)
Sharing data with a new vendor, especially outside Jamaica
Responding to a suspected breach or repeated internal mishandling
If you want a structured 2026 plan that boards and leadership teams can track, the Data Protection Jamaica compliance roadmap for 2026 lays out measurable quarterly deliverables.
Bringing it together
Privacy and data protection work best when they reinforce each other:
Privacy helps you decide what is fair and proportionate.
Data protection ensures that whatever you do is lawful, controlled, secure, and accountable.
If you’re unsure where your organisation stands, PLMC provides data protection implementation support in Jamaica, training sessions, and privacy awareness guidance. You can learn more about PLMC’s services at Privacy & Legal Management Consultants Ltd. and reach out for a consultation when you are ready to turn policy into day-to-day practice.
