
Difference Between Data Protection and Data Privacy Explained

Confusing “data privacy” with “data protection” is one of the fastest ways for an organisation to mis-scope a compliance project. In Jamaica, where the Data Protection Act (DPA) is driving new expectations around accountability, transparency, and security, that confusion can lead to gaps like strong cybersecurity but weak privacy notices, or clear notices but poor access controls.
This guide breaks down the difference between data protection and data privacy, explains how they overlap, and shows what the distinction means in day-to-day operations.
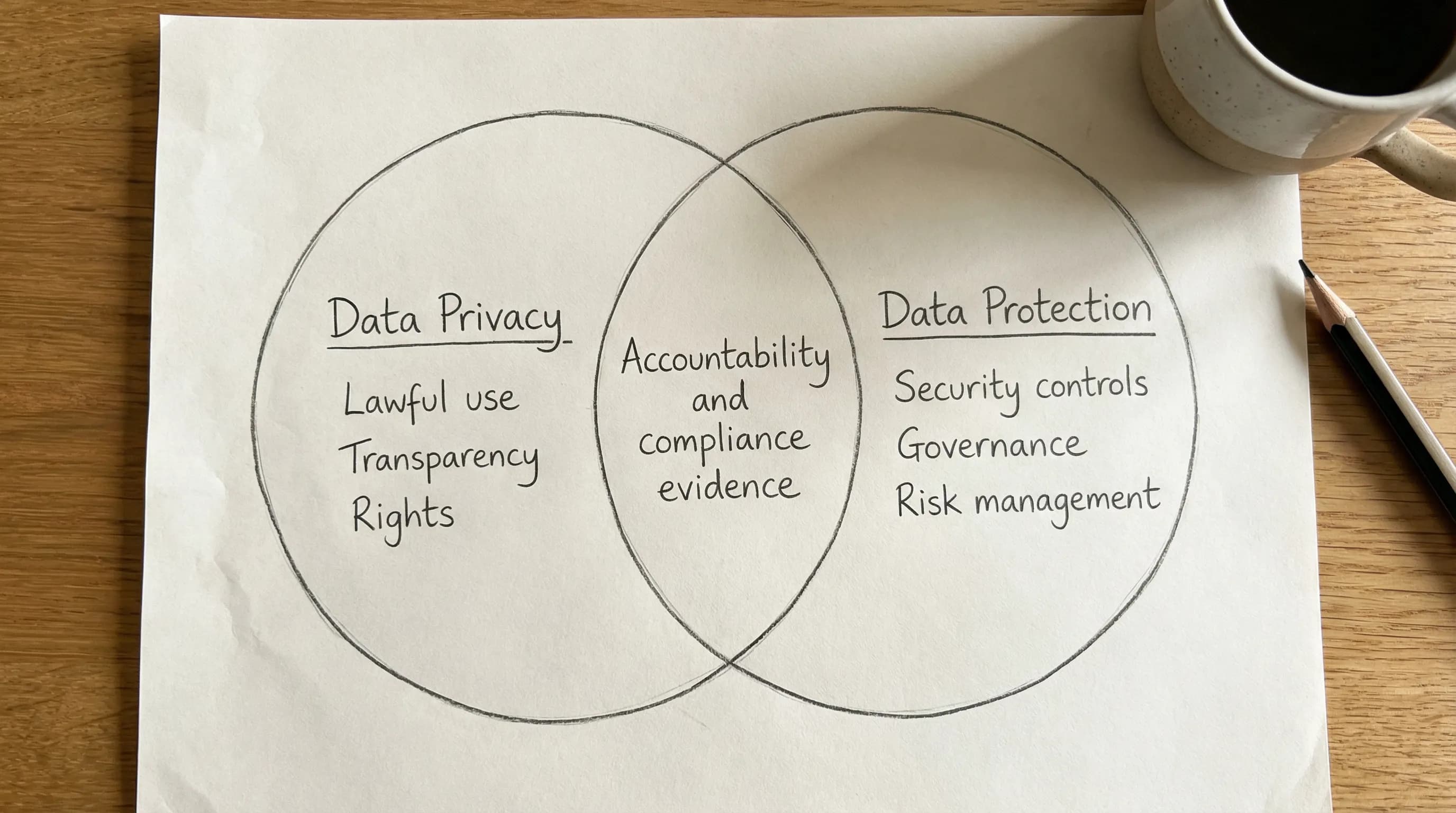
The simple difference (in plain language)
Data privacy is about people and permissions: what personal data you collect, why you collect it, whether you are allowed to use it that way, and what rights individuals have.
Data protection is about controls and accountability: the policies, security measures, governance, and processes you use to keep personal data safe, accurate, available when needed, and used in line with the law.
A practical way to remember it:
Privacy asks: “Should we do this with personal data?”
Protection asks: “How do we do it safely, consistently, and provably?”
Data privacy explained
Data privacy focuses on appropriate, lawful, and transparent handling of personal data. It is closely tied to individual expectations and rights.
In a typical organisation, privacy shows up in decisions like:
What information you request on a form (and what you do not need).
Whether you can reuse customer data for marketing.
How you explain your processing in a privacy notice.
How you respond when someone asks for access to their personal data.
Privacy is also about preventing “purpose creep”, where data collected for one reason (for example, onboarding an employee) gradually gets reused for unrelated purposes.
Privacy is not just “consent”
Many teams assume privacy equals consent. In reality, privacy compliance is broader. You may rely on different lawful grounds depending on the context (employment, contractual performance, legal obligations, and so on). The key is that your chosen approach must be defensible, communicated, and consistent with what you actually do.
For Jamaican organisations aligning to the DPA, privacy usually requires clarity on:
Purpose: why the data is collected and used.
Transparency: what you tell people, when, and in what language.
Rights: how individuals can exercise their rights, and how you handle requests.
Data minimisation: collecting only what is needed.
If you want a practical Jamaica-specific foundation, PLMC’s guide on principles and rights is a helpful companion: Data Privacy in Jamaica: Key Principles and Rights.
Data protection explained
Data protection is the operational side of responsible data handling. It includes the governance and security measures that protect personal data across its lifecycle, from collection to disposal.
Protection typically covers:
Governance and accountability (roles, responsibilities, reporting lines).
Policies and procedures (retention, incident response, access management).
Security controls (technical and organisational measures).
Vendor and third-party management (contracts, due diligence, oversight).
Risk management (risk assessments, privacy impact assessments where applicable).
Importantly, data protection is not limited to IT. A strong data protection programme includes HR, Operations, Finance, Legal, Procurement, and customer-facing teams, because personal data lives everywhere.
Data protection is not the same as cybersecurity
Cybersecurity is a major component of data protection, but it is not the whole thing.
You can have excellent cybersecurity tools and still fail data protection obligations if, for example, you keep personal data for too long, cannot locate records for an access request, or share data with vendors without proper terms.
You can also have written policies and still fail if the controls are not implemented, tested, and followed.
For a broader, Jamaica-focused compliance view, see: Jamaica Data Protection Act Explained for Businesses.
Data privacy vs data protection (side-by-side)
The easiest way to see the distinction is to compare focus, goals, and evidence.
Category | Data privacy | Data protection |
Primary focus | Appropriate and lawful use of personal data | Safeguarding personal data with controls and accountability |
Main question | “Are we allowed to do this, and did we explain it?” | “How do we secure it, manage it, and prove compliance?” |
Typical drivers | Individual rights, transparency, fairness, purpose limitation | Risk management, security, governance, operational resilience |
Common artefacts | Privacy notices, consent language (where used), rights-request communications | Policies, access controls, retention schedules, incident response plans, vendor contracts |
Common failures | Vague notices, over-collection, using data for new purposes without justification | Weak access management, no retention discipline, poor vendor oversight, untested breach response |
Who is involved | Legal/Compliance, Marketing, HR, Product/Operations | IT/Security, Compliance, Risk, Procurement, Operations, HR |
How they work together in real life
Privacy and protection should not be separate workstreams that never meet. They reinforce each other.
Example: a customer sign-up form
Privacy decides what you collect and why (for example, you may not need date of birth for a basic newsletter).
Protection ensures the data is secured, access is limited, and the data is deleted when no longer needed.
If privacy is strong but protection is weak, you might collect the right data for the right reason, but still expose it through poor controls.
If protection is strong but privacy is weak, you might store data securely, but use it in ways that are unfair, unexpected, or not properly explained.
Example: CCTV in the workplace
Privacy addresses transparency (signage, notices, purpose), proportionality, and access rules.
Protection covers secure storage, restricted viewing rights, retention periods, and audit logs.
Practical examples for Jamaican organisations
The difference becomes clearer when you map it to common local workflows.
HR and payroll
Privacy concerns: what employee data is collected, what is disclosed in internal directories, how background checks are handled, and how privacy information is provided to staff.
Protection concerns: role-based access to HR systems, secure transmission to payroll providers, retention rules for personnel files, and offboarding access removal.
Customer service and call recordings
Privacy concerns: notifying customers that calls are recorded, stating the purpose (quality, training, dispute resolution), and handling requests for access.
Protection concerns: encryption, limiting who can retrieve recordings, retention configuration, and preventing unauthorised copying.
Marketing databases
Privacy concerns: lawful basis for marketing, opt-out handling, clarity of notices, and avoiding unexpected reuse of data.
Protection concerns: segmentation access controls, vendor contracts with email/SMS platforms, and monitoring for misdirected campaigns.
Vendor and cloud services
Privacy concerns: ensuring individuals are informed about the use of third parties and cross-border considerations.
Protection concerns: due diligence, data processing terms, security requirements, incident notification clauses, and periodic review.
PLMC’s checklist-style guide can help you see these pieces in one place without losing the distinction: Privacy and Data Protection: A Practical Checklist.
Common misconceptions that create compliance gaps
“If we have a privacy policy, we are covered”
A website privacy policy is only one element of transparency. You still need operational alignment, including accurate internal practices, staff training, and the ability to honour rights requests.
“If we buy security software, we are compliant”
Security tooling helps, but compliance also needs governance, retention, vendor management, and documented decision-making.
“Privacy is Legal’s job, protection is IT’s job”
This split often causes failure. Privacy decisions affect system design and operations, and protection controls must reflect the actual purposes and data flows.
“We will address it when there is an incident”
Reactive programmes are expensive. Under most privacy frameworks, your organisation is expected to implement reasonable measures before something goes wrong, and to be able to demonstrate them.
A quick self-check: are you treating privacy and protection as one programme?
If you are unsure where your organisation stands, use these prompts.
Privacy prompts
Can you explain, in plain language, why you collect each category of personal data?
Do your privacy notices match real operational practice (not just what you intended)?
Can you reliably receive and process rights requests within a defined workflow?
Protection prompts
Do you know where personal data is stored, including email inboxes and shared drives?
Are access rights reviewed periodically (especially for HR, Finance, and customer databases)?
Do you have a tested incident response process that includes privacy considerations?
If your answers are mixed, that is normal. Many organisations build maturity over time. A structured plan helps, such as the quarterly approach in: Data Protection Jamaica: Compliance Roadmap for 2026.
What “good” looks like: evidence you can produce
A regulator, auditor, board member, or key customer will typically want evidence that privacy and protection are both working.
Evidence type | Privacy value | Protection value |
Data inventory and data flow maps | Shows purpose and categories of data | Shows where data sits and where it moves |
Privacy notices and internal privacy statements | Demonstrates transparency | Reduces operational confusion and inconsistency |
Rights request procedure and logs | Shows rights are respected | Shows repeatable process and controls |
Retention schedule and disposal records | Supports storage limitation | Reduces breach impact and data sprawl |
Vendor contracts and due diligence | Confirms appropriate third-party disclosures | Enforces security and incident obligations |
Incident response plan and test results | Ensures individuals’ interests are considered | Demonstrates readiness and containment capability |
Frequently Asked Questions
What is the main difference between data protection and data privacy? Data privacy is about lawful, fair, and transparent use of personal data and respecting individual rights. Data protection is about the governance and controls (including security) that keep personal data safe and managed throughout its lifecycle.
Is data protection the same as cybersecurity? No. Cybersecurity is part of data protection, but data protection also includes retention, vendor governance, access management, training, documentation, and accountability.
Do we need both privacy and data protection to comply with Jamaica’s Data Protection Act? In practice, yes. The DPA expects organisations to process personal data fairly and transparently (privacy) and to implement appropriate measures to safeguard data and demonstrate accountability (protection).
If we outsource payroll, are we still responsible for privacy and protection? Outsourcing does not remove responsibility. You still need appropriate vendor terms, oversight, and a clear understanding of how employee data is used, stored, and protected.
Where should an organisation start if resources are limited? Start by identifying where personal data is held and why (a basic inventory), then align your notices and lawful grounds, tighten access controls, set retention rules, and train staff on the highest-risk workflows.
Need help turning the definitions into an operational programme?
Knowing the difference between data privacy and data protection is useful. Turning that knowledge into policies, workflows, and evidence is what reduces risk.
Privacy & Legal Management Consultants Ltd. (PLMC) supports organisations in Jamaica with data protection implementation, training sessions, risk assessment tools, and free consultations to help you align to the Data Protection Act and embed privacy awareness across teams.
Explore PLMC resources or get started here:
