
Data Security and Privacy: Building Controls and Proof

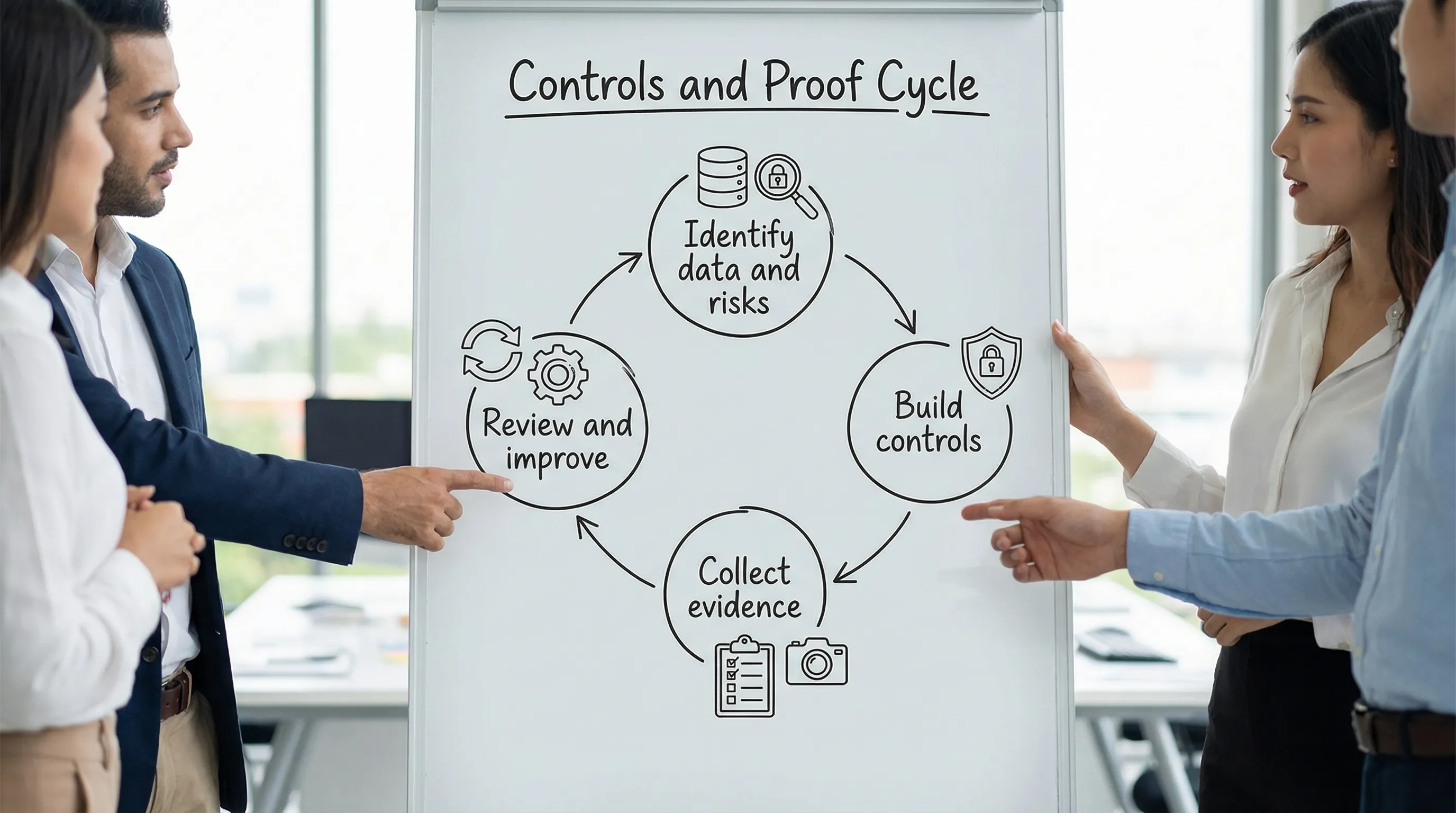
If your organisation is serious about data security and privacy, you need two things working together:
Controls (the practical safeguards that reduce risk)
Proof (the evidence that those safeguards are working)
In Jamaica, the Data Protection Act makes accountability a practical requirement, not just a “nice to have.” Stakeholders also expect it: customers, employees, vendors, boards, and increasingly, overseas partners who want assurance before sharing data.
This guide explains how to build a control set that fits your risk, then create “audit-ready” proof without turning your team into full-time document producers.
Controls vs proof: the difference that trips up many organisations
A control is a safeguard that prevents, detects, or corrects a privacy or security problem. Examples include multi-factor authentication (MFA), a retention schedule, vendor due diligence, incident response playbooks, and role-based access reviews.
Proof is the verifiable trail that shows the control exists and is operating. Examples include MFA enforcement screenshots or reports, signed approvals, training attendance logs, ticketing records, system logs, and evidence of periodic reviews.
A common failure pattern is “policy-only compliance.” The organisation can produce documents, but cannot demonstrate consistent execution.
Start where privacy and security overlap: your data and your risk
Before selecting controls, confirm what you are protecting and why it matters.
Build a usable data inventory (not a one-time spreadsheet)
At minimum, you want to know:
What personal data you hold (including sensitive data)
Where it lives (systems, files, cloud platforms, paper)
Who can access it
Why you collect it (purpose and lawful basis)
Who you share it with (processors, partners)
How long you keep it (retention)
If you already have the basics covered, the next step is to make the inventory operational: connect it to access reviews, vendor risk, retention, and incident response.
PLMC has practical guidance on operationalising compliance in Jamaica in this roadmap: Data Protection Jamaica: Compliance Roadmap for 2026.
Use a simple risk lens to prioritise controls
You do not need an enterprise-sized framework to be effective. A strong starting lens is:
Impact if data is exposed, altered, or unavailable
Likelihood based on your threat environment and current gaps
Exposure based on who has access and how widely data is shared
For recognised structure, many organisations map to established frameworks such as NIST Cybersecurity Framework 2.0 or the CIS Critical Security Controls. You can adopt the logic without adopting the full bureaucracy.
A practical control set for data security and privacy
The most defensible programmes combine governance, people, process, and technology. Below are control areas that typically produce the biggest reduction in risk and the strongest compliance posture.
1) Governance controls (who is accountable, and how decisions are made)
Governance is what prevents privacy and security from becoming “everybody’s job” (which often becomes nobody’s job).
Strong governance controls include:
Defined roles for controller and processor responsibilities, including escalation paths
Policies that are connected to operating procedures (not just PDFs)
Risk assessment routines for new systems, new data uses, and high-risk processing (often via DPIAs)
A clear board or leadership reporting cadence (metrics, incidents, top risks, remediation progress)
If your organisation needs a structured checklist to validate core privacy programme elements, see: Privacy and Data Protection: A Practical Checklist.
2) Identity and access controls (who can see data, and why)
Access control is one of the fastest ways to reduce exposure.
Focus on:
MFA for email, remote access, and administrator accounts
Least privilege (role-based access, no broad shared folders by default)
Joiner, mover, leaver process (accounts created, changed, and removed quickly)
Periodic access reviews for systems that hold personal or sensitive data
Logging and monitoring for key systems (especially where sensitive data is processed)
Proof here is usually straightforward if you capture it consistently (reports, screenshots, review sign-offs).
3) Data handling controls (minimisation, retention, encryption, disposal)
Privacy and security meet most clearly in day-to-day data handling.
High-value controls include:
Data minimisation rules (collect what you need, not what might be useful later)
Retention schedules that are implemented (including deletion and disposal procedures)
Encryption for data at rest and in transit where feasible and proportionate
Secure backup and recovery routines, tested periodically
Controls for exporting data (limits on USB, email forwarding rules, approved transfer methods)
A frequent Jamaican SME reality is “data sprawl” across email inboxes, WhatsApp, personal devices, and shared drives. Minimisation and retention controls reduce sprawl and reduce breach impact.
4) Incident readiness (your ability to respond, decide, and evidence)
Incidents are not only technical. Lost devices, misdirected emails, unauthorised access, and vendor issues are common triggers.
Essential controls include:
Incident response plan with named roles (legal, IT, HR, communications)
A triage method for whether an event is a notifiable breach
Tabletop exercises (even 60 minutes quarterly can raise capability sharply)
A breach register (what happened, impact, decisions, lessons learned, remediation)
When regulators or business partners ask questions, your incident evidence often matters as much as your prevention controls.
5) Vendor and cloud controls (your risk does not stop at your boundary)
If a payroll provider, marketing platform, call centre, or cloud host processes personal data, you need controls that address shared risk.
Practical measures include:
Documented vendor inventory (who, what data, where hosted)
Due diligence before onboarding (security and privacy questionnaire, relevant certifications, incident history)
Contracts that define processor obligations, breach notification, and sub-processing rules
Periodic reviews for higher-risk vendors
This area also supports cross-border transfer governance, which is frequently raised when using overseas SaaS platforms.
Build a proof system: make evidence a normal by-product of work
The goal is not “collect documents for audits.” The goal is to make evidence collection natural and repeatable.
Step 1: Create an evidence map
For each key control, define:
What evidence will prove it is working
Where that evidence will come from (system report, ticket, HR record)
Who owns it
How often it must be produced
Step 2: Standardise where evidence lives
Choose a controlled location (secured SharePoint folder, GRC tool, or structured drive with permissions). The key is consistency and access control.
If evidence is scattered across personal inboxes, you will struggle to prove accountability.
Step 3: Use “operational records” as proof
The strongest proof is created during normal operations:
Helpdesk tickets for access requests and removals
Training enrolment and completion records
Change management approvals
Vendor onboarding checklists
Logs and monitoring alerts
Meeting minutes for risk decisions
You can often prove more with a well-run ticketing workflow than with a 40-page policy.
A control-to-proof example table
Use a table like the one below as a starting template for your organisation’s “proof pack.”
Control area | Key control | Example proof (evidence) | Cadence | Typical owner |
Access management | MFA enforced for email and admin accounts | Admin console report or enforcement screenshot, exception list with approvals | Monthly | IT / Security |
Identity lifecycle | Joiner, mover, leaver process | HR request + ticket closure, deprovisioning timestamp, access revocation report | Ongoing + quarterly review | HR + IT |
Training | Privacy and security awareness training | Training roster, completion report, refresher schedule | Quarterly or biannual | HR / Compliance |
Incident readiness | Incident response plan tested | Tabletop exercise agenda, attendee list, outcomes and actions | Quarterly | Security + Legal |
Vendor management | High-risk vendor due diligence | Completed questionnaire, contract clauses, risk rating, approval record | Onboarding + annual review | Procurement / Compliance |
Retention | Retention and disposal implemented | Retention schedule, deletion logs, disposal certificates for paper/media | Quarterly | Records Mgmt + IT |
What “good proof” looks like in real life
If a regulator, customer, or partner asked, “Show us how you protect personal data,” a credible response is usually a small set of well-organised artefacts, not hundreds of pages.
A practical proof pack often includes:
Data inventory summary and key data flows
Privacy notice set and update history
Rights request process and log (access, correction, deletion, objection)
High-risk processing assessments (where relevant)
Vendor list with risk tiering and key contracts
Security control evidence (MFA, backups, access reviews)
Incident and breach register with lessons learned
Training records and role-based training plan
A risk register snapshot and remediation tracking
If you need a strong foundation on rights and principles, this article complements the proof approach: Data Privacy in Jamaica: Key Principles and Rights.
A “proof-first” 60 to 90 day approach (without boiling the ocean)
If you have limited time and capacity, prioritise controls that produce immediate risk reduction and easy evidence.
Weeks 1 to 2: Pick your scope and stabilise access
Align leadership on your highest-risk data sets and systems (for many organisations: HR, customer databases, finance, student or patient data). Then stabilise identity controls (MFA, admin accounts, shared accounts, leavers).
Weeks 3 to 6: Put repeatable workflows in place
Implement a ticketed process for access requests and removals, centralise training records, and begin a vendor inventory. These create evidence naturally.
Weeks 7 to 12: Package evidence and test readiness
Create your proof pack folder structure, collect your first monthly evidence set, and run one tabletop incident exercise. Identify gaps, assign actions, and track them.
This approach builds confidence quickly because you can demonstrate progress with proof, not promises.
Common gaps that weaken data security and privacy programmes
Many organisations are closer to compliance than they think, but a few recurring gaps can undermine trust:
Policies exist, but procedures are not followed or not measurable
Access is granted once and never reviewed
Exports of personal data happen via email with no tracking or approval
Vendor relationships have contracts, but no due diligence or ongoing oversight
Retention schedules exist, but deletion and disposal are not implemented
Incident response exists “on paper,” but the team has never practiced
Fixing these is less about buying tools and more about disciplined operations and documentation.
Frequently Asked Questions
What is the difference between data security and privacy? Data security focuses on protecting data against unauthorised access, loss, or misuse (confidentiality, integrity, availability). Privacy focuses on lawful, fair, and transparent use of personal data, including rights, purpose limitation, and minimisation. Strong programmes treat them as connected.
How do we “prove” our controls without creating too much paperwork? Design controls so evidence is created during normal work, for example ticketing for access changes, automated MFA reports, training completion records, and vendor onboarding checklists. Keep evidence centralised and review it on a set cadence.
What controls should we prioritise first? Start with identity and access (MFA, least privilege, leavers), incident readiness (plan plus tabletop), and vendor oversight. These reduce risk quickly and are easier to evidence than complex projects.
Do SMEs in Jamaica need the same level of controls as large enterprises? The principles are the same, but the implementation should be proportionate to risk. SMEs can be highly effective with a smaller, well-run control set and consistent proof.
How does the Jamaica Data Protection Act relate to security controls? The Act expects organisations to protect personal data appropriately and to be accountable. Security controls (technical and organisational) support compliance, and evidence demonstrates that protections are operating.
Need help building controls and proof in your organisation?
PLMC supports Jamaican organisations with practical data protection implementation, risk assessments, governance integration, and training that translates legal requirements into day-to-day controls and evidence.
If you want a clear view of what to fix first, and what proof you should retain, request a free consultation or explore PLMC’s resources starting with the Jamaica Data Protection Act explained for businesses.
