
Data Secrecy vs Data Privacy: What’s the Difference?

Many organisations treat “privacy” as a matter of keeping information secret. Lock it down, limit who can see it, and you are done.
That approach is understandable, especially in regulated environments like financial services, healthcare, and HR. But it is also incomplete. Data secrecy and data privacy overlap, but they are not the same thing, and confusing the two can create avoidable compliance risk under Jamaica’s Data Protection Act, 2020.
This guide clarifies the difference in plain language, then shows what it means in real Jamaican workplace scenarios (employee records, CCTV, medical results, AML/KYC files, vendor sharing, and breaches).
Quick definitions (and why the distinction matters)
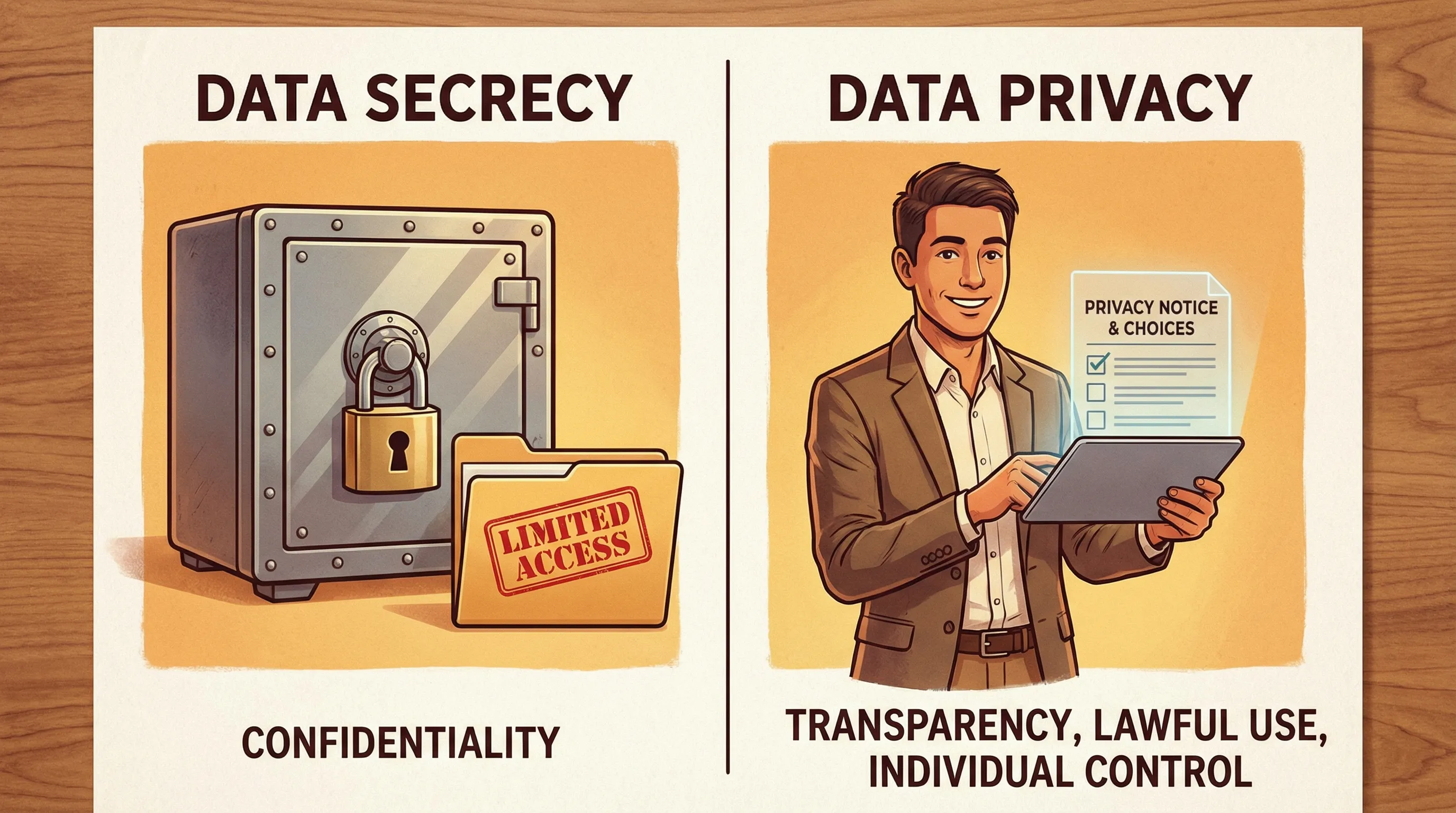
At a high level:
Data secrecy is about preventing disclosure. It focuses on confidentiality and restricting access.
Data privacy is about legitimate, fair, and transparent use of personal data. It focuses on how data is collected, used, shared, retained, and how people can exercise their rights.
A useful way to think about it is:
You can have privacy without secrecy (for example, a transparent, lawful public register with clear purpose limits).
You can have secrecy without privacy (for example, secretly collecting more personal data than you need, and storing it securely).
Data secrecy vs data privacy at a glance
Concept | Core question | Primary goal | Common controls | Typical failure mode |
Data secrecy | “Who can see it?” | Prevent unauthorised disclosure | Access control, need-to-know, encryption, NDAs | “We secured it, so we can collect/use anything.” |
Data privacy | “Should we collect/use/share it, and how?” | Fair, lawful, transparent processing and respect for rights | Privacy notices, lawful basis, minimisation, retention limits, rights handling, vendor governance | “We have a notice, but no real controls or accountability.” |
Why “keep it confidential” is not the same as “be privacy compliant”
Secrecy is typically a security mindset. It is essential, but it answers only one part of the compliance question.
Privacy, especially under modern privacy laws and frameworks (including GDPR-style approaches), expects organisations to show that personal data processing is:
Purpose-limited (collected for specific reasons and not reused incompatibly)
Minimised (only what is needed)
Accurate (kept up to date)
Not kept forever (retention limits)
Handled transparently (people understand what is happening)
Protected (security and confidentiality)
Accountable (governance and evidence)
An organisation can keep information extremely secret and still fall short on privacy if it:
Collects data without a clear purpose or lawful basis
Uses data in ways people do not reasonably expect
Shares data with vendors without appropriate contracts and oversight
Retains personal data “just in case”
Cannot respond properly to access, correction, or deletion requests
If you want a broader implementation view, PLMC’s practical resources can help you connect principles to operational steps, for example:
Where secrecy fits inside privacy (confidentiality is a privacy control)
Secrecy is not “wrong”. In fact, it is often a required safeguard.
In privacy programmes, secrecy typically shows up as:
Confidentiality commitments (internal policies, contracts, NDAs)
Access controls (role-based access, least privilege)
Secure storage and transfer (encryption, secure portals, controlled email practices)
Data loss prevention practices (technical and procedural)
Privacy compliance, however, expects you to go beyond secrecy and answer additional questions:
Why are we collecting this personal data?
What is the lawful basis and the justification?
How will we explain it clearly to individuals?
How long will we keep it, and why?
Who do we share it with, and what controls exist?
What rights might apply, and can we fulfil them consistently?
Jamaican context: what the Data Protection Act, 2020 pushes organisations to do
Jamaica’s Data Protection Act, 2020 requires organisations to treat personal data in a way that aligns with core privacy principles and individual rights. While security and confidentiality matter, privacy compliance is broader than “locking data away.”
From a Governance, Risk, and Compliance (GRC) perspective, a mature privacy programme generally includes:
Governance and accountability (assigned ownership, policies, decision logs)
Data mapping (knowing what you have, where it is, and who touches it)
Rules for collection and use (purpose, minimisation, lawful basis)
Clear notices and internal guidance (staff know what to say and do)
Vendor and cross-border controls (contracting, due diligence, oversight)
Retention and disposal (a defensible schedule)
Incident and breach readiness (detect, respond, document)
Ongoing training and monitoring
PLMC’s checklist-style article is a practical companion to the concepts in this post: Privacy and Data Protection: A Practical Checklist
Real-world scenarios: secrecy vs privacy in practice
The easiest way to see the difference is to look at common operations and ask, “What would a secrecy-only approach do, and what would a privacy-compliant approach do?”
Scenario | Secrecy-only approach | Privacy-compliant approach (secrecy included) | What can go wrong if you stop at secrecy |
Employee files (HR) | Lock filing cabinets, restrict HR folder access | Collect only what is needed, define retention, provide clear employee privacy info, restrict access, handle rights requests, control sharing with insurers and payroll vendors | Over-collection, indefinite retention, informal sharing, inability to respond to access/correction requests |
CCTV in the workplace | Store footage on a locked DVR, only security can view | Provide clear signage and notice, document purpose (safety, security), restrict access, set retention period, manage disclosure requests, secure footage | “Secret surveillance” perception, excessive monitoring, footage kept too long, uncontrolled sharing |
Customer onboarding and KYC (AML) | Keep KYC files confidential, restrict access | Explain why you need each item, request only what’s required, set retention aligned to legal obligations, govern vendor tools, protect special categories, enable rights handling where applicable | Collecting unnecessary documents, storing scans indefinitely, unclear sharing with third parties |
Health information (medical results, sick leave documentation) | Keep results in a confidential envelope or secure folder | Limit who needs to know, minimise detail, store securely, explain use, control retention, share only with justified parties | Oversharing with managers, collecting too much detail, retention beyond necessity |
Vendor sharing (payroll, cloud storage, marketing tools) | “We trust the vendor, data is password protected” | Due diligence, contract terms, documented instructions, access controls, breach notification expectations, periodic review | Unclear roles, weak contractual protections, loss of visibility and accountability |
Data breach response | Keep the breach secret to avoid reputational harm | Investigate, contain, document decisions, assess risk to individuals, follow legal obligations, improve controls and training | Delayed response, poor evidence, repeated incidents, loss of trust |
A note on medical results and confidentiality
A good example of secrecy supporting privacy is health data handling. PLMC has previously discussed this in a specific context, noting that sensitive results constitute personal data and should be handled accordingly: COVID-19 results are protected by the Data Protection Act
The privacy point is not only “keep results confidential,” it is also “limit collection, explain use, restrict sharing, retain appropriately, and respect rights.”
The “privacy mindset” leaders should adopt (especially in regulated environments)
If you lead compliance, legal, HR, IT, security, or risk, here is a practical mindset shift:
Secrecy asks: “How do we stop people from seeing this data?”
Privacy asks: “Should we have this data at all, and if yes, how do we use it responsibly, transparently, and lawfully?”
This is where privacy intersects with corporate governance and enterprise risk.
A simple way to embed that mindset is to require documented answers to four questions whenever a team proposes collecting new personal data (a new form, a new app, a new vendor, a new monitoring tool):
What is the specific purpose?
What is the minimum data needed?
How will we inform individuals (and what choices exist)?
What is the retention and disposal plan?
Those questions turn privacy into a repeatable decision process, not a one-time policy document.
Practical steps to move from “secrecy” to “privacy compliance”
If your organisation already has confidentiality rules, you have a strong starting point. The next steps are usually about governance and operational consistency.
1) Map your personal data and data flows
You cannot manage what you cannot see. Data mapping typically identifies:
What personal data you hold
Where it is stored (paper, email, shared drives, HR systems, CRMs)
Who accesses it
Which vendors touch it
Where it moves (including cross-border processing)
2) Tighten collection and forms (minimisation)
Review onboarding forms, HR forms, and customer intake scripts for “just in case” fields. Minimisation reduces risk immediately because fewer data elements means fewer things to protect, explain, and retain.
3) Make transparency operational (not just legal)
Privacy notices are not only for websites. Organisations often need layered communication:
External privacy notices (customers, website users)
Employee-facing privacy information
Scripts and FAQs for frontline staff
A strong notice should match reality. If practice and notice differ, privacy risk increases even if secrecy controls are strong.
For a structured implementation approach, see: Data Protection Jamaica: Compliance Roadmap for 2026
4) Build a consistent rights-request workflow
A common compliance gap is not knowing what to do when someone asks:
“What information do you have about me?”
“Please correct this.”
“Please delete this.”
Even when legal exceptions apply in certain cases, you still need a documented, repeatable process to triage, verify identity, respond, and log decisions.
5) Formalise retention and secure disposal
Secrecy often focuses on storage security, but privacy requires retention discipline. If personal data is kept indefinitely, the organisation carries unnecessary risk.
Retention schedules should connect to business needs, legal requirements, and practical disposal steps.
6) Train staff on privacy decisions, not just confidentiality
Most breaches are operational, not technical. Training works best when it is role-based and scenario-driven, for example:
HR handling medical notes
Customer service responding to access requests
Marketing teams using contact lists
Managers requesting employee data
PLMC provides training sessions and privacy awareness support for Jamaican organisations, including implementation guidance aligned to the Data Protection Act.
Data secrecy, privacy, and trust (what customers and employees notice)
People often judge privacy by what they experience:
Were they told what would happen with their data?
Was the request reasonable, or intrusive?
Did the organisation share data unnecessarily?
Could they get answers when they asked?
Did staff handle their data discreetly and professionally?
Secrecy contributes to trust, but privacy is what sustains it. Privacy is the combination of respect, transparency, control, and safeguards.
Frequently Asked Questions
Is data privacy just another word for confidentiality? No. Confidentiality (secrecy) is one privacy safeguard, but privacy also covers lawful purpose, transparency, minimisation, retention, rights, and accountability.
Can data be private if it is not secret? Yes. Some personal data may be processed openly (for a clear, lawful purpose) with transparency and strict limits. Privacy is not always about hiding, it is about responsible processing.
Does the Jamaica Data Protection Act, 2020 require security controls? Yes, appropriate security safeguards are a core expectation, but compliance also includes governance, fair processing, transparency, rights handling, and retention controls.
If we encrypt everything, are we compliant? Encryption is excellent for security, but it does not address whether you collected too much data, used it for the wrong purpose, failed to inform individuals, or retained it for too long.
How does AML/KYC affect privacy? AML/KYC often requires collecting and retaining personal data for regulatory reasons. Privacy compliance still applies, especially minimisation, secure handling, defined retention, controlled access, vendor oversight, and clear communication.
What is the biggest sign we are treating privacy as secrecy? When the organisation can say “only a few people can access it,” but cannot clearly explain why the data is collected, how long it is kept, or how to handle an access or deletion request.
Get help turning privacy concepts into an operational programme
If your organisation is trying to move beyond confidentiality policies and build a demonstrable privacy programme aligned to Jamaica’s Data Protection Act, 2020, PLMC can help with implementation support, training, and risk assessment tools.
Explore resources on Privacy & Legal Management Consultants Ltd. and use the free consultation option to discuss your current state, gaps, and a practical path to compliance.
This article is for general information and does not constitute legal advice.
