
Data Privacy Standards: ISO, NIST, and What Fits Jamaica

In Jamaica, the Data Protection Act sets the legal expectation for how personal data should be handled, but it does not hand you a ready-made operating system for your organisation. That is where data privacy standards and frameworks come in. They translate broad legal duties (like “appropriate security” and “accountability”) into repeatable governance, risk management, and control practices you can implement, evidence, and improve.
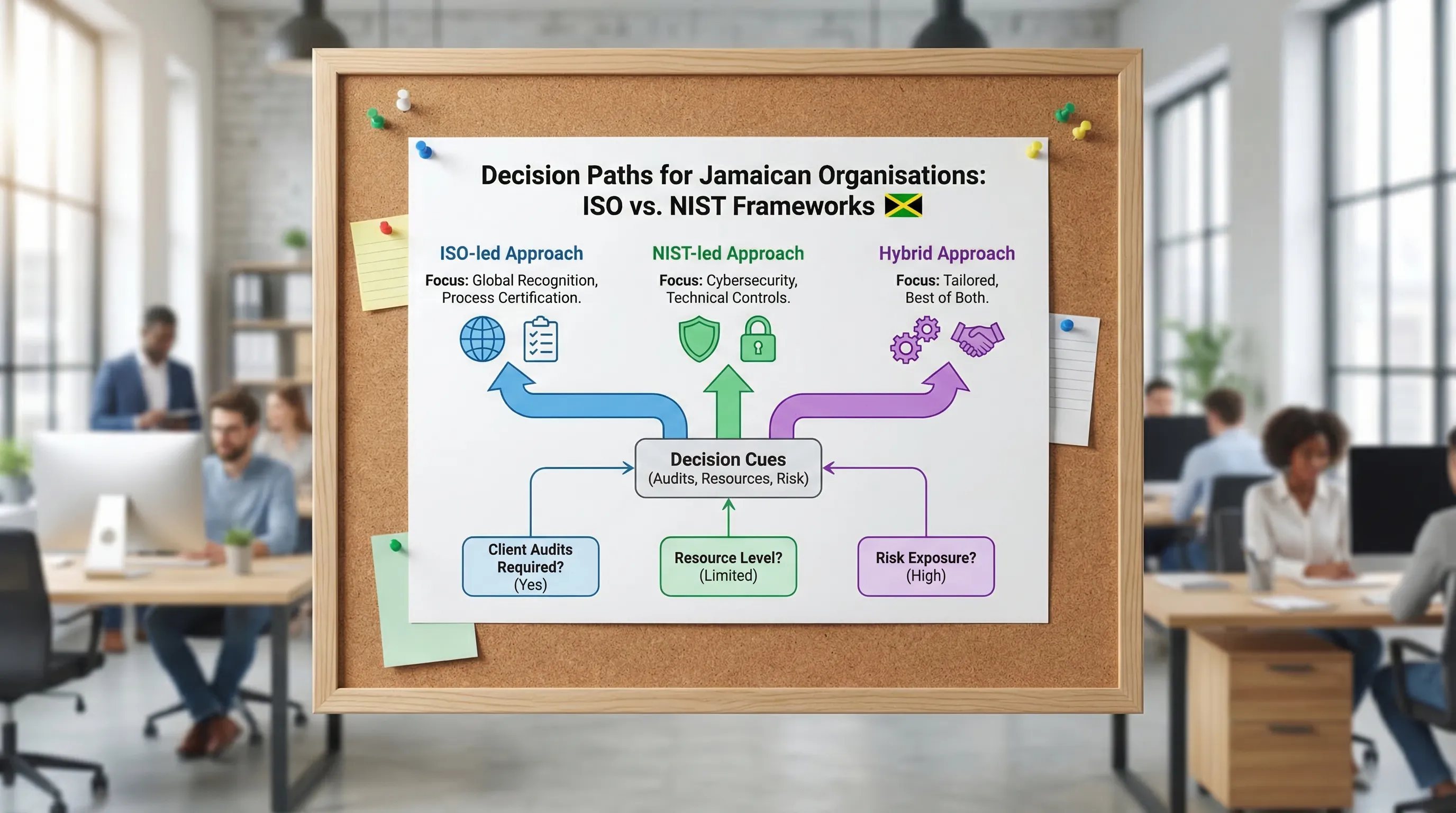
If you are deciding between ISO and NIST, the best choice is rarely “either/or”. The practical question is: which standard (or combination) best fits your industry, risk profile, client expectations, and budget in Jamaica?
Standards vs laws: what Jamaican organisations should understand first
A law tells you what you must do and what regulators can enforce. A standard or framework tells you how to structure your programme so you can demonstrate control, consistency, and continuous improvement.
For Jamaica, that distinction matters because many compliance gaps are operational, not theoretical. Organisations often know the principles, but struggle to prove:
Who owns privacy decisions and risk acceptance
Where personal data lives and who can access it
Whether vendors and cloud tools are being governed
Whether incident response and breach reporting are tested
Whether training actually changes day-to-day behaviour
A recognised standard helps you build evidence and discipline, especially when you are dealing with customers, overseas partners, audits, or insurance questionnaires.
If you need a Jamaica-first overview of core obligations before selecting a framework, PLMC’s guides on the Jamaica Data Protection Act explained for businesses and data protection basics are useful starting points.
The ISO approach (ISO/IEC 27001, 27002, 27701): best for “management systems” and auditability
When people say “ISO for privacy”, they often mean a family of standards that work together:
ISO/IEC 27001: requirements for an Information Security Management System (ISMS). It is designed for governance, risk treatment, internal audit, and continual improvement. It is also the standard most commonly used when organisations want a certifiable, externally auditable security management system.
ISO/IEC 27002: guidance and a catalogue of information security controls that support 27001.
ISO/IEC 27701: a privacy extension that helps organisations build a Privacy Information Management System (PIMS) on top of 27001, including privacy-specific controls for controllers and processors.
In practical terms, ISO is strong when you need a formal structure that management can sponsor and auditors can test. It also fits well when procurement teams ask for “ISO-aligned” security and privacy governance.
Authoritative references:
The NIST approach (Privacy Framework, CSF, and control catalogues): best for flexibility and risk outcomes
NIST is widely adopted internationally, especially in the United States and by organisations serving US clients. It is less about a single certifiable management system and more about risk outcomes, control maturity, and practical implementation pathways.
Key pieces to know:
NIST Privacy Framework: helps you identify and manage privacy risk (including risks that arise even when you have “security” controls). It supports governance, data processing awareness, and communication.
NIST Cybersecurity Framework (CSF) 2.0: a high-level model for cybersecurity outcomes (Govern, Identify, Protect, Detect, Respond, Recover). It is commonly used to organise a security programme and measure maturity.
NIST SP 800-53 (and related publications): a deep control catalogue used to implement and assess security and privacy controls in a structured way.
Authoritative references:
ISO vs NIST: what is the real difference for a Jamaican organisation?
The simplest way to think about it is:
ISO is a management system standard that is very strong for governance, audit trails, and “run it like a programme”.
NIST is a framework ecosystem that is very strong for mapping outcomes, prioritising by risk, and building a practical control roadmap without the overhead of formal certification.
Many Jamaican organisations benefit from both: use ISO to formalise governance and evidence, and NIST to accelerate security and privacy control maturity.
A quick comparison table
Topic | ISO (27001/27002/27701) | NIST (Privacy Framework / CSF / 800-53) |
Primary strength | Formal management system, auditability, consistency | Flexible risk-based implementation, outcome maturity |
Typical use case | Demonstrating structured governance to clients/auditors | Rapidly organising and prioritising controls by risk |
Certification | 27001 is commonly certified (external audit model exists) | Frameworks are typically not “certified” (implementation can be assessed) |
Documentation intensity | Higher, by design | Adjustable, based on your needs |
Privacy coverage | Strong when paired with 27701 | Strong privacy-risk framing and integration with security |
Best fit when | Client contracts demand ISO-style assurance | You need a practical roadmap and control prioritisation |
“What fits Jamaica?” A selection lens that actually works
Choosing a standard is less about geography and more about your operating context in Jamaica:
Regulatory pressure and reputational risk: If a breach would trigger major consequences (loss of customers, disruption, public scrutiny), you want a framework that drives repeatability and strong governance.
Client and partner demands: Many Jamaican firms provide services to overseas entities (BPO, tourism platforms, online services). Client security questionnaires may lean ISO-aligned or NIST-aligned depending on market.
Organisational size and maturity: SMEs often need a framework that prioritises essential controls without creating a documentation burden they cannot sustain.
Data types: Handling sensitive personal data (health, financial, children’s data) raises the bar. Even where the law is principle-based, your programme should be more rigorous.
Third-party dependence: Cloud services and outsourced processing are common. Your framework needs strong vendor governance and evidence.
Recommended “recipes” for common Jamaican scenarios
Below are practical combinations that tend to work well. They are not legal advice, but they reflect how privacy and cybersecurity programmes are typically built in a risk-based way.
If you are a Jamaican SME that needs quick wins and credible structure
A lightweight approach can still be disciplined:
Use NIST CSF to structure your cybersecurity outcomes (so you can prioritise what matters).
Use the NIST Privacy Framework to ensure privacy risk is addressed (not just security).
Build a small set of repeatable privacy operations: data inventory, rights handling workflow, vendor checks, retention rules, incident handling.
This approach is often faster to start and easier to maintain, especially when you do not need external certification immediately.
If you are a BPO, IT services firm, or you sell services to overseas clients
Client trust is frequently the commercial driver. In that environment:
ISO/IEC 27001 is a strong anchor because it signals management oversight, governance, and internal audit discipline.
ISO/IEC 27701 helps you cover privacy controls and clarify controller vs processor responsibilities.
Add NIST CSF as a practical overlay for operational security maturity, especially for detection and response.
If you are in a high-risk sector (financial services, health-adjacent services, large customer databases)
Where risk exposure is high, the priority is demonstrable control and tested readiness:
Use ISO 27001 for governance, risk treatment, and audit.
Use a deeper control set (often NIST SP 800-53-style depth, or a comparable detailed catalogue) to ensure security and privacy controls are implemented consistently across systems.
Ensure your privacy programme can evidence accountability: training, role-based access, vendor controls, and incident exercises.
How standards support Jamaica Data Protection Act compliance (without duplicating the law)
Most principle-based privacy laws create the same operational needs. Standards help you build those needs into your normal way of working.
Here are common programme components Jamaican organisations are expected to operationalise, and how ISO and NIST help:
Programme need (practical) | Why it matters | How ISO helps | How NIST helps |
Data inventory and processing awareness | You cannot protect what you cannot locate | Documented scope, assets, risk context | Identify functions and risk mapping across processes |
Governance and accountability | Clear ownership and reporting | ISMS roles, internal audit, management review | Governance outcomes and maturity measurement |
Vendor and cloud oversight | Third parties are a major risk source | Supplier control requirements and evidence | Control selection and continuous monitoring focus |
Incident readiness | Breaches are operational events | Required procedures, testing, evidence | Respond/Recover structure, operational playbooks |
Training and awareness | People drive many privacy failures | Competence and awareness requirements | Behavioural outcomes, role-based adoption |
If you want a tactical evidence checklist (policies, registers, logs) tailored to Jamaica, PLMC’s privacy and data protection practical checklist complements the standards conversation well.
A practical adoption plan (that avoids “framework theatre”)
Framework adoption fails when it becomes a documentation project instead of a risk and operations project. The goal is to implement controls that reduce real risk and produce evidence that stands up to scrutiny.
1) Set scope based on services and data flows
Define what is in scope (business units, systems, locations, third parties). In Jamaica, scope often expands quickly because personal data sits in:
HR and payroll processes
Customer service inboxes and call recordings
Marketing tools and CRM platforms
Cloud storage and shared drives
A tight scope is not a shortcut, it is a way to be honest about what you can govern well.
2) Choose your “spine” and your “control library”
A clean way to decide:
Pick a spine for governance and reporting (ISO 27001 or NIST CSF are common spines).
Pick a control library for detailed implementation (ISO 27002, NIST 800-53, or another recognised catalogue).
Add a privacy layer (ISO 27701 and/or NIST Privacy Framework) so privacy risk is not treated as only an IT problem.
3) Run a gap assessment that produces a realistic roadmap
A useful gap assessment does not just say “compliant/non-compliant”. It should produce:
A risk-ranked backlog (what to fix first)
Owners and timelines
Evidence required (policies, logs, technical configurations)
Dependencies (vendor changes, tooling, training)
This is where many organisations benefit from a structured assessment, especially if they need to show progress to boards, investors, or overseas partners.
4) Implement “minimum viable controls” before chasing maturity
Most Jamaican organisations get immediate risk reduction from a short list of controls executed well: strong access control, patching discipline, secure configuration, backups, incident response, vendor governance, and a working rights-request process.
Perfection is not required at the start. Repeatability is.
5) Build an evidence pack that matches your stakeholder needs
Whether you are responding to a customer questionnaire or preparing for an internal audit, you will be asked for proof. Your evidence pack typically includes:
Evidence item | What it proves | Who usually owns it |
Data inventory / records of processing | You understand where personal data is | Privacy lead, operations, IT |
Risk assessment and treatment plan | Decisions are risk-based and approved | Risk/GRC, management |
Policies and procedures (privacy, incident, retention) | You have defined rules people must follow | GRC, legal, HR |
Vendor due diligence and contracts | Third-party risk is controlled | Procurement, legal, IT |
Training records and role-based materials | Staff competence is managed | HR, privacy lead |
Incident logs and tabletop exercise notes | You can respond under pressure | IT security, operations |
6) Establish continuous improvement, not a one-time project
ISO formalises this with internal audits and management reviews. NIST formalises it through maturity tracking and iterative improvement. Either way, the standard should become part of “how you operate”, not a binder on a shelf.
For a structured year view of implementation activities, you can cross-reference your framework roadmap with PLMC’s Data Protection Jamaica compliance roadmap for 2026.
The decision shortcut: when to prefer ISO, when to prefer NIST, and when to go hybrid
If you want a simple but reliable way to decide, use this table as a first filter:
Your reality | Best starting point | Why |
You need formal assurance for procurement and contracts | ISO/IEC 27001 (add 27701 for privacy) | Clear management system, strong audit story |
You need a pragmatic control roadmap fast | NIST CSF + NIST Privacy Framework | Strong prioritisation and maturity approach |
You already have security basics but privacy feels scattered | Add NIST Privacy Framework or ISO 27701 | Brings privacy risk and governance into focus |
You have multiple third parties and cloud dependencies | ISO + NIST hybrid | ISO for governance, NIST for operational depth |
Where PLMC can help (without locking you into a single framework)
Framework selection is a governance decision as much as it is a technical one. PLMC supports organisations in Jamaica with data protection implementation, GRC integration, cyber security services, training sessions, and risk assessment tools, helping teams translate requirements into operating practices and evidence.
If you are weighing ISO vs NIST, a good first step is a scoping discussion and a gap assessment that clarifies:
Your in-scope data and systems
Your highest-risk processing and vendors
The framework combination that fits your client demands
A phased plan your team can actually deliver
You can explore PLMC’s resources on transitioning with the Data Protection Act or start with a consultation via the site at Privacy & Legal Management Consultants Ltd..
