
Data Privacy and Data Protection: How They Work Together

Most organisations say they “take privacy seriously”, but far fewer can show how privacy decisions translate into day-to-day controls. That gap is where complaints, regulator scrutiny, and breaches tend to happen.
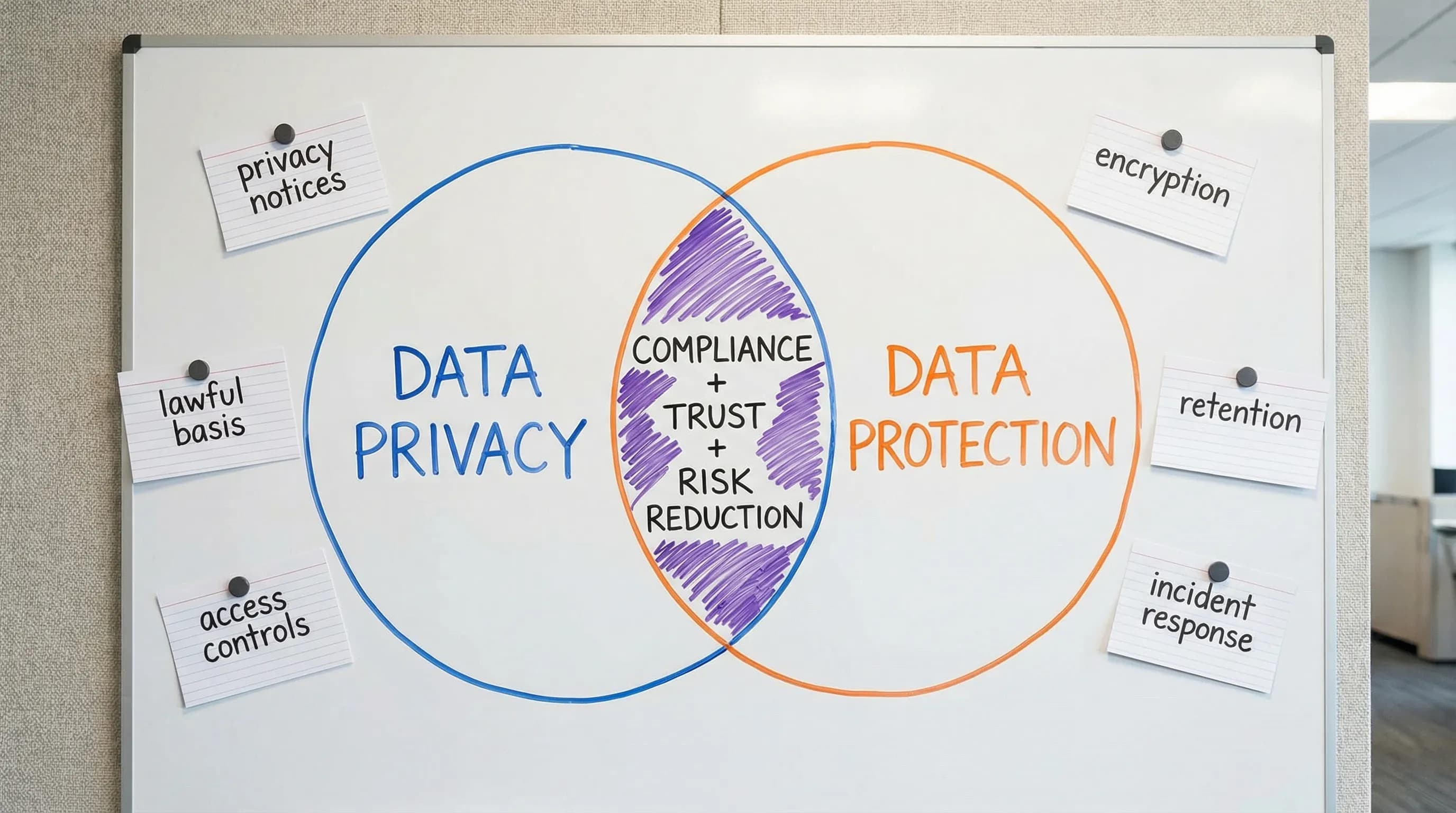
To close it, it helps to separate two terms people often treat as interchangeable: data privacy and data protection. They are different, but they are designed to work together. Privacy sets the rules and expectations for how personal data should be used. Data protection delivers the safeguards and operating discipline that make those rules real.
Data privacy vs data protection (the simplest way to think about it)
Data privacy is about appropriate use of personal data. It asks questions like:
Are we collecting more than we need?
Did we clearly tell people what we will do with their information?
Do we have a lawful basis for processing?
Can individuals access, correct, or delete their data when required?
Data protection is about keeping personal data secure, accurate, available when needed, and properly managed throughout its lifecycle. It includes:
Security controls (access management, encryption, backups)
Organisational controls (policies, training, audits)
Technical and operational resilience (patching, monitoring, incident response)
Data management controls (retention, disposal, quality checks)
A useful shortcut is:
Privacy = “Should we?” (rules, rights, transparency, fairness)
Protection = “How do we do it safely and consistently?” (controls, evidence, operations)
In Jamaica, the concepts come together under the Data Protection Act, 2020, where meeting principles and respecting individual rights requires both privacy decisions and protection controls. If you want the legal framing in plain language, see PLMC’s guide: Jamaica Data Protection Act explained for businesses.
Why privacy programmes fail when protection is treated as “just IT”
A privacy notice, consent checkbox, or policy document does not protect anyone by itself. Privacy can fail even when intentions are good, if the organisation cannot execute consistently.
Common failure patterns include:
Privacy promises with no operational backing: You tell customers you only use data for “account purposes”, but marketing exports the same dataset into a new tool without review.
Security controls that ignore privacy: You implement strong cybersecurity, but still collect excessive data, keep it too long, or share it too widely.
No end-to-end accountability: Teams do not know who owns vendor risk, retention, rights requests, or breach reporting.
Strong outcomes require both disciplines to be designed together: privacy defines the constraints and expectations, protection ensures those constraints are enforced and provable.
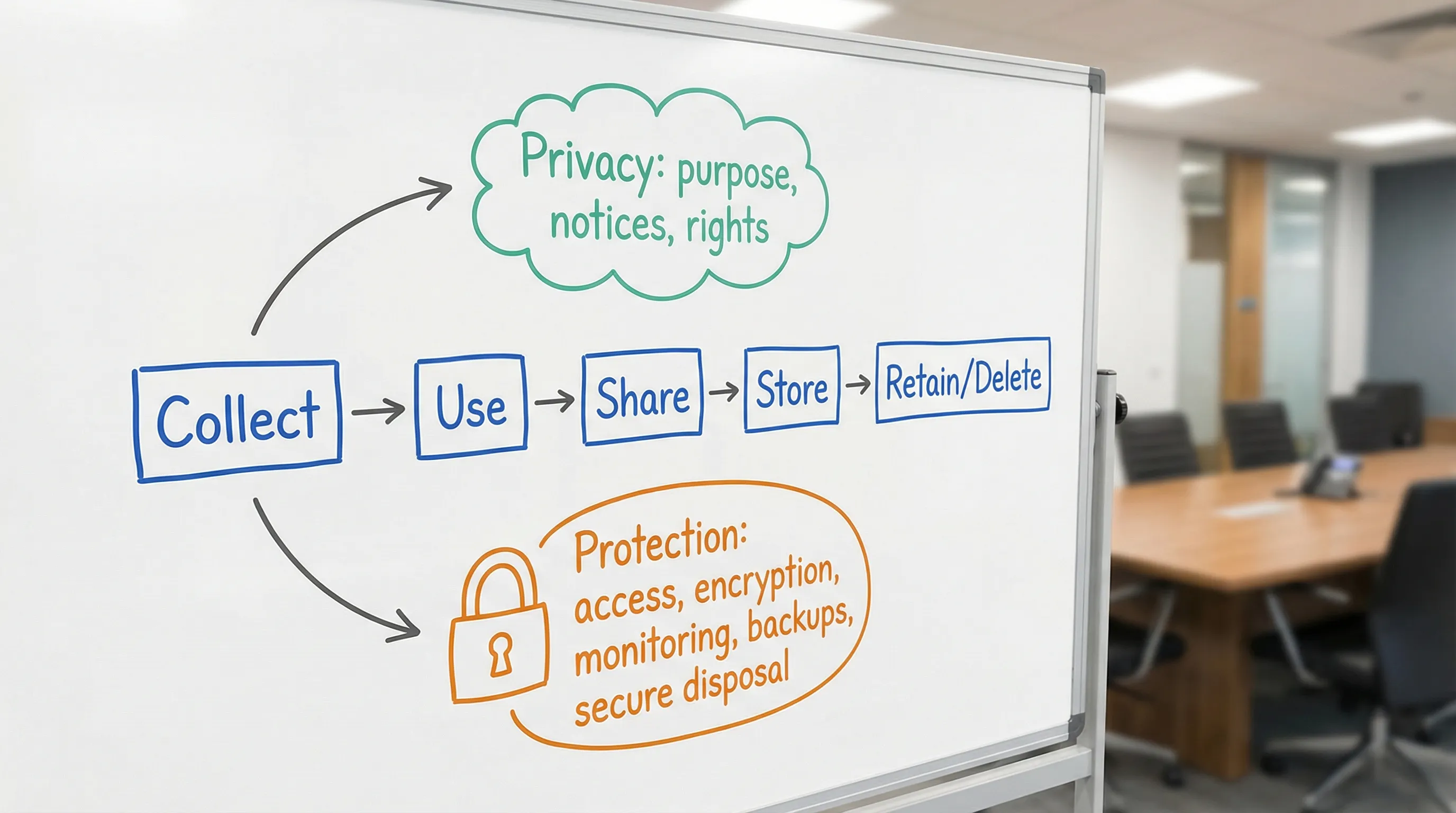
How data privacy and data protection work together across the data lifecycle
Personal data moves through a lifecycle, from collection to disposal. Privacy and protection show up at every stage, but in different ways.
1) Collection (forms, onboarding, KYC, HR)
Privacy focuses on purpose and proportionality: what you collect, why you collect it, and how you explain it.
Protection focuses on secure capture and access control: preventing unauthorised collection, leakage, or internal overreach.
Example: If you ask for government ID, the privacy question is “Is it necessary for this purpose?” The protection question is “Who can view it, how is it stored, and when is it deleted?”
2) Use (operations, analytics, customer service)
Privacy focuses on use limitation and fairness: using the data in line with what was communicated, and avoiding unexpected secondary uses.
Protection focuses on role-based access and monitoring: ensuring only appropriate staff and systems can access the data, and that access can be audited.
3) Sharing (vendors, affiliates, cross-border transfers)
Privacy focuses on transparency, lawful basis, and contractual boundaries.
Protection focuses on vendor security and transfer controls: due diligence, security clauses, and technical safeguards where appropriate.
If your operations use overseas cloud services, this is where privacy and protection must meet. Privacy defines the conditions under which transfers are acceptable. Protection validates the vendor’s controls and the organisation’s own configuration, access management, and monitoring.
4) Storage and retention
Privacy focuses on storage limitation: not keeping personal data longer than necessary.
Protection focuses on secure storage and controlled deletion: encryption, backups, retention schedules, and defensible disposal.
5) Rights handling and complaints
Privacy focuses on the right itself and response obligations (access, correction, deletion, objection, and other rights under the Act).
Protection focuses on workflows and evidence: identity verification, audit trails, secure extraction, and consistent timelines.
For a detailed overview of principles and rights in the local context, see: Data privacy in Jamaica: key principles and rights.
A practical mapping: privacy objectives and the protection controls that support them
Use this table as a quick way to sanity-check whether your privacy commitments are actually enforceable.
Privacy objective (what you promise) | Data protection controls (what makes it real) | What “evidence” can look like |
Collect only what you need (data minimisation) | Form and system field reviews, approval process for new data fields | Change logs, data inventory, documented purpose per field |
Use data only for stated purposes (purpose limitation) | Access controls by role, data sharing approvals, tagging datasets | Access reviews, workflow records, data catalog entries |
Be transparent (privacy notices) | Version control, distribution processes, training for frontline staff | Notice versions, website archive, staff scripts and training records |
Keep data accurate | Validation rules, periodic reconciliation, correction workflows | Error rates, correction tickets, QA checks |
Keep data only as long as needed (retention) | Retention schedule enforcement, secure deletion, backup lifecycle management | Retention policy, deletion reports, backup retention settings |
Keep it secure (confidentiality, integrity, availability) | Security baseline aligned to a standard, monitoring, incident response | Security policies, logs, incident tabletop reports |
Respect individual rights | Verified request workflow, secure data extraction, audit trails | Request register, identity verification procedure, response templates |
Security standards can help structure the “protection” side. Many organisations use frameworks like ISO/IEC 27001 and the NIST Cybersecurity Framework to define baseline controls and to demonstrate governance.
Real-world examples (Jamaica): where privacy and protection collide
HR and payroll records
HR teams handle highly sensitive information, including identifiers, bank details, medical details, and performance records.
Privacy questions: Who should see what, for what purpose, and for how long? What notices do staff receive?
Protection questions: Are files segmented by role? Are laptops encrypted? Are HR folders auditable? How do you handle departures and access removal?
Customer onboarding and AML/KYC
Financial institutions and regulated entities may collect extensive customer information.
Privacy questions: Are you collecting what is required, and can you clearly explain the reasons (legal obligation, contract, legitimate interests, etc.)?
Protection questions: Can you restrict access to KYC images and documents? Are scans protected from reuse in unrelated processes?
CCTV and visitor logs
CCTV and physical security data is common, and often overlooked.
Privacy questions: Is signage clear? Are retention periods defined? Is footage used for unrelated monitoring?
Protection questions: Who can export footage? Are exports logged? Is remote access secured?
Marketing databases and WhatsApp-style outreach
Marketing can move fast, which increases privacy and protection risk.
Privacy questions: Did people understand they would receive marketing? Can they opt out easily? Are you respecting their preferences?
Protection questions: Is the list stored in approved systems, or in personal devices? Is access restricted? Is there a process to remove contacts promptly?
Health information (including workplace health data)
Health data is generally high-risk, and mishandling can cause significant harm. PLMC’s article on health-related information is a helpful reminder: COVID-19 results are protected by the Data Protection Act.
Building an integrated programme (without drowning in paperwork)
If you want privacy and protection to function as one system, aim for shared governance and a small set of repeatable operating routines.
Start with a shared inventory of personal data and processing
A privacy programme cannot work without knowing what data you have, where it lives, who touches it, and why. This is not only a compliance activity, it is also a security prerequisite.
Define ownership that matches how work actually happens
Privacy is cross-functional. Typical ownership spans legal/compliance, HR, IT/security, operations, marketing, and procurement.
What matters is that:
Someone owns the privacy rules (notices, lawful bases, rights, retention)
Someone owns the protection baseline (security controls, monitoring, incident response)
Someone ensures projects and vendors go through review before launch
Embed “privacy by design” into projects and change management
New tools, new forms, and new vendor relationships are where risk multiplies. A lightweight review step can prevent long-term problems.
A practical approach is to require a short review whenever a change involves:
New categories of personal data
New purposes (especially analytics and marketing)
New vendors or cross-border processing
New surveillance or monitoring
Align security controls to the sensitivity of the data
Not all personal data needs the same level of protection, but high-risk data should trigger stronger controls. For example, you might apply stricter access rules to:
Government-issued IDs
Financial account information
Health-related data
Children’s data
Make incident response privacy-aware
A security incident is not only a technical event. It can become a privacy breach depending on what data was affected, how it was exposed, and the harm that could result.
Tabletop exercises should include privacy decision points, for example:
What data types were involved?
What is the likely impact to individuals?
Who decides if notifications are required?
What will you tell customers, regulators, and staff?
Train by role (not one-size-fits-all)
Privacy training is most effective when it matches daily tasks. A frontline customer service representative needs practical scripts and escalation steps. A developer needs secure design practices and data minimisation patterns. Procurement needs vendor due diligence triggers.
If you want a structured, hands-on way to assess coverage, PLMC’s Privacy and data protection: a practical checklist can help teams identify what is missing and what “good evidence” looks like.
What “good” looks like: outcomes you can measure
You do not need perfect maturity to reduce risk quickly. You do need measurable outcomes. Examples include:
Reduced data collection (fewer optional fields, fewer copies of IDs)
Faster rights request handling (clear intake, consistent timelines, fewer escalations)
Stronger vendor discipline (documented due diligence for new processors)
Lower incident impact (better segmentation, better logging, faster containment)
Better retention hygiene (routine deletion and fewer “forever” datasets)
If your organisation is planning major changes in 2026, such as new customer platforms, digitisation of records, or increased outsourcing, it is worth aligning initiatives to a phased plan. PLMC’s Data Protection Jamaica: compliance roadmap for 2026 provides an operational way to think about sequencing.
When it makes sense to get support
Many organisations can draft a policy. The harder part is implementing a programme that stands up in real operations, across departments and vendors.
You may benefit from specialist support if you are:
Unsure what personal data you hold, or where it flows
Rolling out a new system or outsourcing processing
Seeing repeated incidents, complaints, or near-misses
Struggling to align legal requirements, cybersecurity, and business operations
Privacy & Legal Management Consultants Ltd. (PLMC) supports Jamaican organisations with data protection implementation, GRC integration, cyber security services, training sessions, and risk assessment tools, with an option to start with a free consultation. To explore what an integrated approach could look like for your organisation, visit Privacy & Legal Management Consultants Ltd. and review their educational resources and services.
