
Data Privacy Compliance: A Practical Checklist for 2026

Data privacy compliance in 2026 is less about having a policy on a shelf and more about proving, at any time, that your organisation knows what data it holds, why it holds it, who it shares it with, and how it protects it. In Jamaica, that proof matters even more as organisations continue to operationalise obligations under the Data Protection Act, 2020 and respond to rising cyber risk, vendor dependency, and rapid adoption of AI-driven tools.
This checklist is written for Jamaican organisations that want a practical, audit-ready way to tighten privacy operations this year, without turning compliance into a never-ending project.
How to use this 2026 checklist
Use it in two passes:
Baseline pass (2 to 4 weeks): Confirm each control exists and identify gaps.
Evidence pass (4 to 8 weeks): Collect proof (documents, logs, screenshots, approvals) to demonstrate the control is working.
If you need a foundation on the Act itself, start with PLMC’s primer, Data Protection Basics: What Jamaican Firms Must Know. If you already have a programme in place, this article focuses on what to verify and refresh specifically for 2026.

The 2026 “minimum viable evidence pack” (what regulators, customers, and partners ask for)
A common failure mode is doing the work but not documenting it in a way that stands up to scrutiny. Build a simple compliance folder (digital is fine) that contains current versions of the items below, plus a change log.
Core evidence pack
Governance artefacts (privacy roles, reporting lines, meeting minutes)
Data inventory and data flow map (including cloud services)
Lawful basis or authority for key processing activities (especially marketing, HR, CCTV, biometrics, health data)
Privacy notices (customers, employees, website users) and notice change history
Rights request procedure and tracking log
Vendor list with risk ratings, contracts, and security/privacy due diligence records
Security policies and key technical evidence (access control, MFA, backups, encryption where applicable)
Incident response plan and at least one test or tabletop exercise record
Retention schedule and disposal records (or system rules enforcing deletion)
Training plan, completion records, and role-based materials
You can align this pack to established good practice frameworks like the NIST Privacy Framework (useful for structuring controls and outcomes), even if your legal compliance obligations come from local law and contracts.
Practical checklist for data privacy compliance (2026 edition)
The table below is designed to be used in a working session with your leadership team, IT, HR, and operations. Treat it as your “control register” for privacy.
Checklist area | What “good” looks like in 2026 | Evidence to collect | Cadence |
Accountability and governance | A named privacy lead (or team), defined responsibilities for controllers and processors, and management oversight | Role assignment memo, org chart, governance meeting minutes | Quarterly |
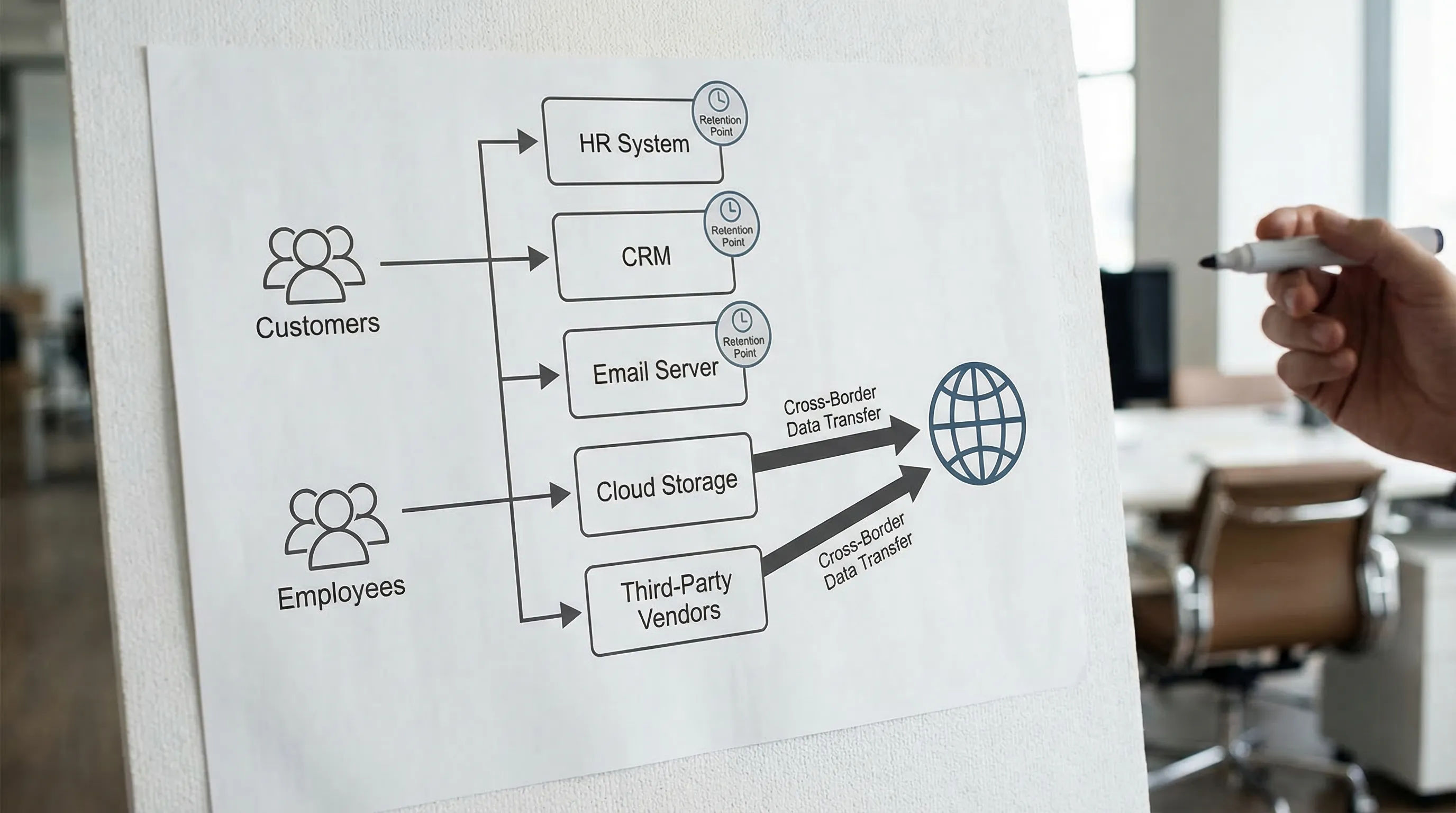
Data inventory and flows | A living record of systems, data types, purposes, locations, recipients, and retention, including shadow IT | Data inventory spreadsheet, system list, flow diagram, change log | Monthly updates, quarterly review |
Lawful basis and purpose control | Each key processing activity has a documented purpose and authority, and purpose creep is prevented | Processing register fields, approvals for new uses, DPIA triggers | Per change |
Transparency (notices) | Notices are accurate, easy to find, and match reality (including third-party tools on your website) | Published notices, version history, cookie/analytics list, screenshots | Semi-annually, and per change |
Rights handling | A defined intake channel, identity verification rules, and tracked timelines and outcomes | SOP, request log, templates, training record | Ongoing, monthly review |
Security controls supporting privacy | Access is role-based, MFA is standard, sensitive data is protected, logging exists, backups are tested | MFA report, access review evidence, backup test record, security policies | Monthly key checks, quarterly review |
Vendor and cloud management | Vendors are risk-rated, contracts include privacy and security clauses, and due diligence is evidenced | Vendor register, DPAs/contract clauses, assessment forms, SOC/ISO attestations where available | Onboarding, annual refresh |
Cross-border data sharing | You know where data is stored and accessed, and you assess transfer risks for offshore vendors | Data residency notes, transfer assessments, vendor documentation | Onboarding, per change |
Retention and disposal | Retention is defined by category, enforced operationally, and disposal is verifiable | Retention schedule, disposal certificates, system deletion rules | Annual review, ongoing execution |
Incident readiness | Incidents are triaged fast, roles are clear, evidence is preserved, communications are rehearsed | IR plan, tabletop exercise record, incident log template | Semi-annually exercises |
Training and awareness | Staff get practical training relevant to their role (HR, customer service, IT, marketing) | Training plan, attendance/completion logs, role-based decks | Onboarding, annual refresh |
Monitoring and assurance | Internal spot checks, metrics, and corrective actions are tracked to closure | Audit checklists, KPI dashboard (simple), remediation log | Quarterly |
1) Governance: make privacy a business process (not a side task)
In many organisations, compliance breaks down because privacy is treated as a legal document exercise instead of an operational system. In 2026, regulators and business partners expect clearer accountability, particularly where data is processed across multiple vendors and cloud environments.
Confirm you have:
A designated privacy lead with authority to coordinate across departments
Clear ownership for HR data, customer data, marketing data, and IT/security controls
A routine management forum to review risk, incidents, and programme progress
If you are still building your overall programme plan for the year, PLMC’s Data Protection Jamaica: Compliance Roadmap for 2026 is a useful companion for sequencing deliverables.
2) Data inventory: the fastest way to reduce risk is to know what you hold
A data inventory is not just a list of systems. For compliance, it should help you answer:
What personal data do we hold, and where is it stored?
Why do we process it, and who can access it?
Who do we share it with (including service providers and group companies)?
How long do we keep it, and how do we dispose of it?
In 2026, update your inventory approach to reflect how work is actually done:
Include collaboration platforms and messaging tools used for business
Capture data processed by “embedded” tools (CRM plugins, website chat, analytics, payment tools)
Track where AI features are enabled (for example, call summarisation, email drafting, CV screening)
3) Lawful processing: document your “why” and stop purpose creep
One of the easiest ways to drift out of compliance is to collect data for one reason and reuse it for another without proper authority or notice. The fix is operational: require a lightweight approval step any time a team wants to use personal data in a new way.
A practical 2026 control is a simple “new processing” intake form that captures:
Purpose and expected benefit
Data categories (especially sensitive categories)
Source (direct from individuals, third parties, public sources)
Recipients (including vendors)
Retention and security needs
Whether a privacy impact assessment is required
When to trigger a privacy impact assessment in 2026
Not every change needs a full assessment, but high-risk activities should be flagged early.
High-risk trigger | Common examples in Jamaican organisations |
Sensitive or special category data | Health data, biometric identifiers, disciplinary records |
Systematic monitoring | CCTV expansions, vehicle tracking, employee productivity monitoring |
Large-scale processing | Customer databases, telecoms-style datasets, loyalty programmes |
Automated decision-making | Automated screening, profiling for marketing, risk scoring |
New data sharing pattern | Integrations with offshore vendors, new analytics platforms |
4) Transparency: your notices must match reality (especially online)
Privacy notices become risky when they are copied from templates and never updated after the business changes tools. In 2026, pay special attention to:
Website tracking technologies (analytics, pixels, embedded content)
Outsourced customer support tools (ticketing, call recording, chat)
Recruitment platforms and background check providers
A practical step is to run a quarterly “notice-to-reality check” where marketing and IT confirm what is actually deployed on the website and customer platforms, and privacy updates the notice accordingly.
For a broader foundation on privacy principles and rights under Jamaican law, see Data Privacy in Jamaica: Key Principles and Rights.
5) Rights requests: design the workflow before the volume arrives
Rights handling is a credibility test. Even if request volume is low today, one employee matter, customer complaint, or media issue can change that instantly.
Your rights workflow should be clear on:
Where requests can be submitted (email, form, physical location)
How identity is verified (with a safe, minimal-data approach)
Who triages (privacy lead) and who fulfils (HR, IT, customer service)
What gets logged (date, request type, outcome, exemptions relied on where applicable)
A 2026 best practice is to track average completion time and top request themes, then use that data to reduce friction (for example, improving data accuracy at source reduces rectification requests).
6) Vendor and cloud management: your compliance depends on theirs
Most organisations rely on vendors for payroll, HRIS, cloud hosting, accounting, customer communications, and cybersecurity services. That makes vendor governance one of the most important privacy controls in 2026.
At minimum, ensure:
You have a complete vendor register (including “free” tools used by teams)
Vendors are risk-rated based on data sensitivity and access
Contracts include privacy and security expectations, breach notification, and clear processing instructions
You retain due diligence evidence (questionnaires, security attestations, policy summaries)
If you need to understand controller vs processor roles, and why that distinction changes your contract posture, PLMC’s Jamaica Data Protection Act Explained for Businesses provides a practical overview.
7) Security measures that regulators actually expect to see evidence for
Security is broad, but privacy compliance often turns on whether you can prove a few critical controls are consistently applied.
Focus your 2026 evidence collection on:
Multi-factor authentication coverage for email, admin accounts, and remote access
Joiner-mover-leaver access controls (how access is granted, changed, removed)
Encryption where appropriate (particularly for portable devices and backups)
Logging and monitoring for key systems holding personal data
Backup testing and restoration drills (not just “we have backups”)
Where possible, align your operational security controls to recognised standards such as ISO/IEC 27001 (information security management) and extend to privacy governance with ISO/IEC 27701 (privacy information management), particularly if you operate in regulated sectors.
8) Retention and disposal: reduce your exposure by deleting safely
Keeping data “just in case” increases breach impact, increases rights request complexity, and makes it harder to defend your compliance posture. In 2026, retention needs to be more than a spreadsheet.
Strengthen retention by:
Defining retention periods by data category (HR, customer, vendor, marketing)
Implementing deletion rules in systems where possible
Controlling copies (exports, spreadsheets, personal inboxes)
Recording disposal actions for high-risk datasets
A practical approach is to start with your top 10 datasets by risk (for example, employee records, customer ID documents, health information, credit-related files) and operationalise retention there first.
9) Incident response: privacy compliance depends on your first 24 hours
Under modern data protection regimes, the first hours of an incident matter, both for limiting harm and for meeting legal and contractual obligations. Even if you have not had a reportable breach, you should be able to demonstrate readiness.
In 2026, a strong privacy-aligned incident capability includes:
A clear definition of what counts as a personal data incident
Escalation paths that include privacy, IT/security, legal, and communications
Steps to preserve evidence (logs, affected systems, vendor notifications)
A tested tabletop exercise that includes a realistic scenario (ransomware, misdirected email, vendor compromise)
For local guidance and updates, monitor the Office of the Information Commissioner (Jamaica) and ensure your internal procedures reflect current expectations.
10) Training: focus on role-based behaviours, not generic slide decks
Annual training is rarely enough, and generic training rarely changes day-to-day habits. In 2026, training works best when it is specific to what people actually do.
Examples of role-based topics that reduce risk quickly:
HR: handling medical information, disciplinary files, reference checks, and payroll vendors
Customer service: identity verification, secure communication channels, preventing oversharing
Marketing: consent, mailing lists, third-party tracking, customer segmentation and profiling
IT and admins: access reviews, secure configuration, data exports, retention controls
PLMC provides training sessions and educational resources, and can tailor sessions to your organisation’s risk profile and industry.
11) The 2026 add-on checks: AI, shadow IT, and “invisible” sharing
Many privacy programmes were designed for traditional databases and predictable workflows. In 2026, three realities regularly create compliance gaps:
AI features inside everyday tools
Even when you do not “buy an AI product,” AI features may be enabled by default in email, document platforms, or customer service tools. Treat AI enablement as a processing change that needs review: what data is used, where it goes, how long it is retained, and whether it is used to train models.
For a structured approach to AI risk governance, the NIST AI Risk Management Framework is a helpful reference for policies and controls.
Shadow IT and unsanctioned tools
Teams adopt tools to move faster. Your compliance posture depends on how quickly you can detect and govern them. A practical control is a monthly review of:
New SaaS subscriptions and expense claims
New website tags and plugins
Data exports from core platforms
Third-party sharing in web and mobile environments
Many organisations underestimate how much personal data is shared through analytics, advertising tags, and embedded services. In 2026, ensure marketing and IT can answer, in plain language, what data is collected, who receives it, and how users are informed.
Turning the checklist into a 30-day action plan
If you want momentum without overwhelming your team, run this as a one-month compliance sprint:
Week 1: Confirm governance, assign owners, and build your evidence folder structure.
Week 2: Update data inventory, vendor register, and cross-border notes.
Week 3: Refresh notices, rights workflow, and retention schedule for top-risk datasets.
Week 4: Validate security evidence, run an incident tabletop, and publish a short management report with next-quarter priorities.
This is often enough to move from “we think we comply” to “we can demonstrate compliance.”
When to get help
If your organisation is short on internal capacity, or if you are dealing with high-risk processing (sensitive data, large-scale customer datasets, significant vendor exposure), external support can be the fastest path to a defensible posture.
Privacy & Legal Management Consultants Ltd. (PLMC) supports Jamaican organisations with data protection implementation, GRC integration, cyber security services, training, and risk assessment tools. If you want to pressure-test your current programme against this 2026 checklist, you can start with a free consultation and map out a realistic execution plan.
