
Security and Privacy Policies: What Every Jamaica Org Needs

Security and privacy policies are easy to dismiss as “documents for the file”, until a customer complaint, a staff mistake, or a vendor incident puts your organisation on the back foot. In Jamaica, the Data Protection Act makes accountability practical, you are expected to show that you have appropriate controls, not just good intentions.
A well-built set of security and privacy policies does two things at once:
It tells people what to do (so practices are consistent).
It creates evidence (so you can demonstrate compliance and good governance).
Below is a practical guide to the policy set most Jamaican organisations need, how to structure it, and how to turn policies into day-to-day behaviour.
Why policies matter (beyond “compliance”)
Most policy projects fail because they are written for auditors instead of for teams. The point is not a perfect document, it is predictable decision-making.
Security and privacy policies help you:
Meet Data Protection Act expectations around security safeguards, transparency, retention, and accountability.
Reduce operational risk by setting clear rules for access, sharing, storage, and incident handling.
Pass customer and vendor due diligence (questionnaires often ask for written policies and proof of training).
Speed up incident response because roles, escalation paths, and steps are already agreed.
Avoid “shadow IT” by giving staff safe, approved ways to do their jobs.
If your organisation uses cloud tools, outsourced payroll, marketing platforms, CCTV, biometrics, or remote work, your policy set is no longer optional. It is your control system.
Security policies vs privacy policies (and why you need both)
These are related but not interchangeable.
Security policies focus on protecting systems and information from unauthorised access, loss, alteration, or disruption.
Privacy policies focus on lawful, fair, transparent handling of personal data, including how it is collected, used, shared, retained, and how people can exercise their rights.
A simple way to remember it is: privacy is about appropriate use of personal data, security is about appropriate protection of data and systems.
Topic | Security policy focus | Privacy policy focus |
Primary goal | Confidentiality, integrity, availability | Lawful and fair processing, transparency, rights |
Typical owner | IT, InfoSec, risk, operations | Legal, compliance, privacy lead, HR |
Core artefacts | Access rules, encryption, backups, logging, incident response | Privacy notice, retention rules, vendor clauses, rights workflows |
Common failure | Controls exist but staff bypass them | Notice exists but actual processing differs |
In practice, you want these to align. For example, a privacy policy might require deletion after a retention period, but security must ensure backups and archives follow that rule too.
The minimum policy set most Jamaican organisations should have
Many organisations start with a single “Data Protection Policy” and stop there. That usually creates gaps because different teams need different rules.
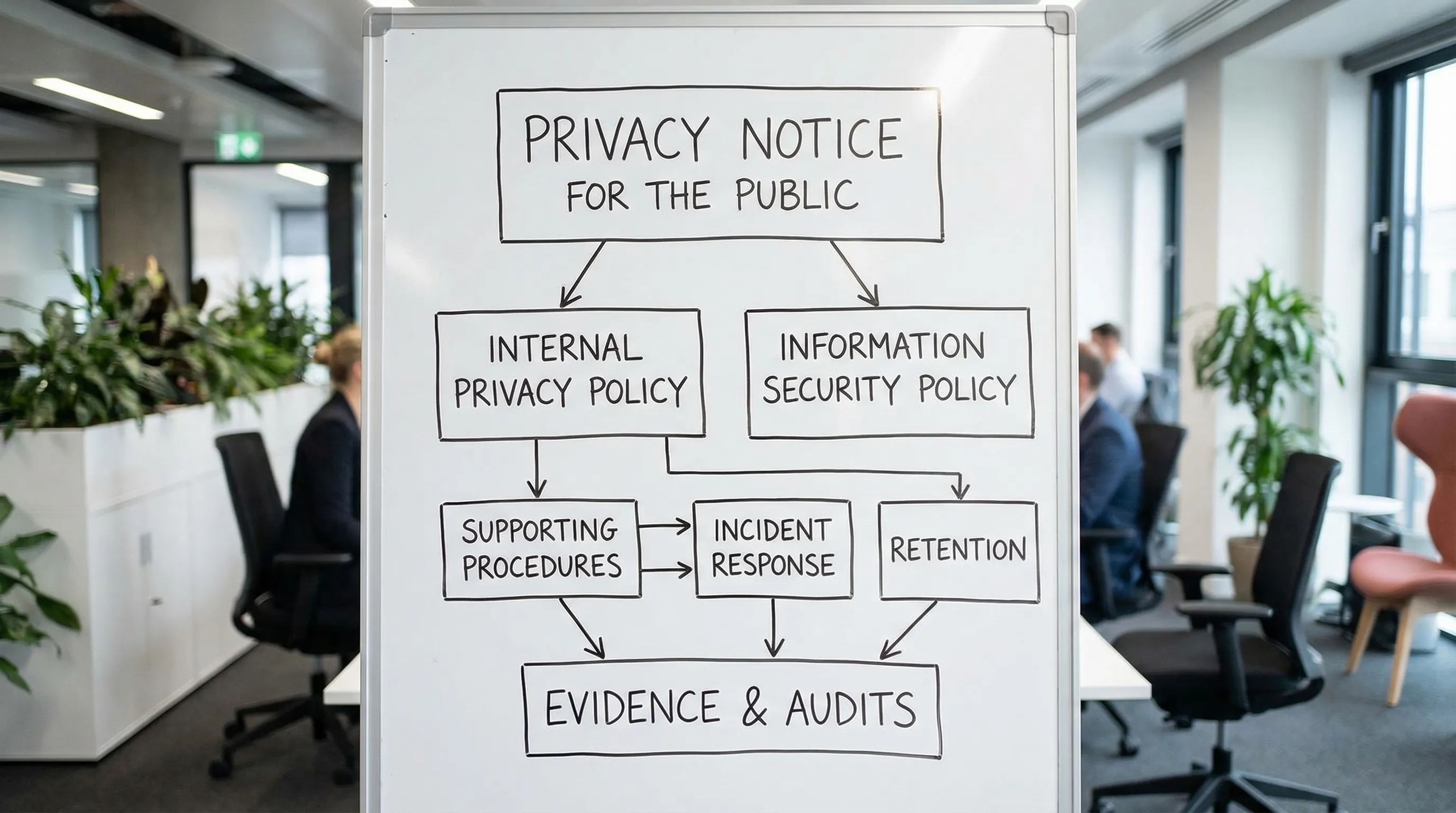
A lean, effective policy set typically includes:
Privacy governance policy (internal): Defines your privacy programme, roles, reporting, and how you approve new uses of personal data.
Privacy notice (external facing): Explains to individuals what you do with their personal data (customers, website visitors, employees as applicable).
Information security policy: Sets the baseline security controls and responsibilities.
Acceptable use policy: Rules for email, internet, passwords, removable media, and workplace tech.
Access control policy: How access is granted, reviewed, removed, and how privileged access is handled.
Data classification and handling policy: What “confidential” means in your environment, and how each category must be stored, shared, and disposed of.
Retention and disposal policy: How long you keep records and how you dispose of them securely.
Incident response and breach management policy: What counts as an incident, how to escalate, who decides, what to document.
Vendor and outsourcing policy: How you select, contract, and monitor processors and service providers.
Remote work and BYOD policy (if applicable): Requirements for personal devices, home Wi-Fi, MFA, screen locks, and approved apps.
You can merge some items for smaller organisations, but do not merge them so much that the rules become vague.
What a strong privacy policy should cover (internal governance)
A privacy policy for internal operations should read like a playbook, not marketing copy. It should clearly answer:
1) Scope and definitions
What the policy applies to (employees, contractors, systems, locations).
Definitions your staff will actually use (personal data, sensitive data, processing, controller vs processor).
If you need a refresher on local concepts and obligations, PLMC has a practical explainer here: Jamaica Data Protection Act Explained for Businesses.
2) Lawful processing and purpose control
Even without turning your policy into a legal textbook, you should set operational rules such as:
No collection “just in case”, collect what is needed for a defined purpose.
New purposes require review and approval (especially marketing, analytics, or new sharing).
Sensitive data requires higher scrutiny and stronger safeguards.
3) Transparency and notices (including internal notices)
Separate the concept of an internal policy from a privacy notice.
Your privacy notice is what individuals see.
Your policy is what your staff follow.
Your policy should include minimum notice requirements for common contexts (website forms, job applications, CCTV signage, employee onboarding).
4) Individual rights handling (workflow, not theory)
Your policy should define:
Where requests are submitted (email, form, physical location).
Who verifies identity and how.
Who searches systems, who approves responses, who sends the response.
What to log (date received, type of request, outcome, actions taken).
5) Data sharing and vendor management
A policy should make it difficult to “just send the spreadsheet”. Include rules for:
When sharing is allowed.
Minimum contract clauses expected of service providers.
Due diligence triggers (for example, cloud hosting, outsourced customer support, payroll).
6) Retention and disposal
Privacy compliance is not only about collection, it is also about not keeping data forever.
A good policy references:
Your retention schedule (even if it starts simple).
Secure disposal methods (paper, devices, drives, cloud records).
Handling for legal holds and disputes.
PLMC’s Privacy and Data Protection: A Practical Checklist is a useful companion when you want to confirm you have the right building blocks.
What a strong information security policy should cover
Security policies often become too technical, then staff ignore them. The best ones set clear minimums and point to procedures for detail.
Consider structuring your information security policy around widely-used frameworks such as ISO/IEC 27001 and the NIST Cybersecurity Framework. You do not need certification to use the concepts.
Key sections to include:
Security roles and accountability
Define who is responsible for:
Approving access.
Managing assets and software.
Monitoring, patching, and backups.
Incident response leadership and communications.
Access control and authentication
Set minimum requirements such as:
Unique user accounts (no shared logins, except controlled service accounts).
Multi-factor authentication where feasible, especially for email and admin tools.
Periodic access reviews.
Joiner, mover, leaver processes (new hires, role changes, departures).
Data protection controls
This is where security and privacy meet. Include:
Encryption expectations (in transit, at rest where appropriate).
Approved storage locations (no personal email for work files).
Rules for external sharing (links, permissions, expiry, password protection).
Backup, recovery, and resilience
A policy should mandate backup and testing, not just “we back up”. Include:
Backup frequency expectations.
Restore testing schedule.
Ransomware considerations (immutable backups, separation).
Incident and breach handling
Define what staff must do in the first hour:
Stop the spread (disconnect device if instructed).
Preserve evidence (do not delete logs or emails).
Report immediately through a defined channel.
For application and web security awareness, it also helps to align your development and vendor expectations to reputable guidance like the OWASP Top 10.
Map policies to evidence (what you should be able to show)
A regulator, customer, or board will usually ask two questions:
Do you have policies?
Can you prove you follow them?
Use the table below as a quick “evidence map” you can build over time.
Policy or control area | What “good” looks like in practice | Evidence to keep |
Privacy governance | Named owner, reporting line, review cycle | Approved policy, meeting minutes, programme plan |
Privacy notices | Notices match actual processing | Current notices, change logs, screenshots of forms |
Access control | Access is approved and reviewed | Access request records, review logs, offboarding checklist |
Vendor management | Vendors assessed and contracted appropriately | Due diligence notes, contracts, DP clauses, SLA summaries |
Retention and disposal | Data is deleted or archived on schedule | Retention schedule, disposal certificates, deletion logs |
Incident response | Incidents handled consistently | Incident register, investigation notes, lessons learned |
Training and awareness | Staff understand their role | Training attendance, materials, quiz results where used |
This is where many organisations gain real leverage. When you can produce evidence quickly, you reduce disruption and uncertainty.
A practical rollout plan (without turning it into a 6-month project)
You can build a defensible baseline in weeks if you focus on the highest-risk processes first.
Start with your “real life” data flows
Before writing or updating policies, confirm:
What personal data you collect (customers, employees, members, patients, students).
Where it lives (email, shared drives, HR systems, WhatsApp messages, paper files).
Who you share it with (banks, insurers, payroll providers, marketing tools).
If your organisation wants a structured way to plan across 2026 deliverables, see: Data Protection Jamaica: Compliance Roadmap for 2026.
Use “policy plus procedure” instead of one massive document
A workable structure is:
Policy: the rule and minimum requirements.
Procedure: the steps and templates.
Records: the proof.
For example, your incident response policy can be short, but supported by a one-page incident checklist and an incident report template.
Socialise policies with the people who will use them
Policies fail when they are written in isolation. Build quick feedback loops with:
HR (employee data, onboarding, discipline).
IT (identity, devices, security tooling).
Operations (customer handling, records).
Finance and procurement (vendors, payments, outsourcing).
Train by role, not just once per year
A single annual lecture rarely changes behaviour. Instead, tailor short sessions:
Front desk and customer service (identity verification, disclosure rules).
HR and payroll teams (employee privacy, sharing, retention).
IT administrators (privileged access, logging, incident response).
Marketing (consent, mailing lists, tracking tools).
PLMC provides training sessions and implementation support, and you can start with a free consultation to prioritise what matters most for your environment.
Common gaps Jamaican organisations should watch for
These are issues that frequently create risk even when an organisation “has policies”:
Copy-paste templates that do not match operations (especially around marketing, CCTV, and HR practices).
Unmanaged informal channels like personal email, WhatsApp, or unapproved shared drives.
Vendor sprawl with no clear list of service providers handling personal data.
No retention discipline, meaning old spreadsheets and reports remain accessible indefinitely.
Weak offboarding, where access remains active after someone leaves or changes roles.
Policies that are not approved or reviewed, with no version control or ownership.
If you fix only one thing first, fix the gap between “what the policy says” and “what staff actually do”. That gap is where most incidents start.
Turning policies into trust
Security and privacy policies are part of governance, but they also signal maturity to customers, partners, and staff. The organisations that do this well keep their policies simple, connect them to real workflows, and maintain an evidence pack that proves follow-through.
If you want support building or refreshing your security and privacy policies so they align with the Data Protection Act and your day-to-day operations, PLMC can help with implementation, risk assessment tools, and targeted training. You can reach out via the contact page to discuss your current state and the quickest path to a defensible baseline.
