Privacy Protection Services: What You Should Expect in Jamaica

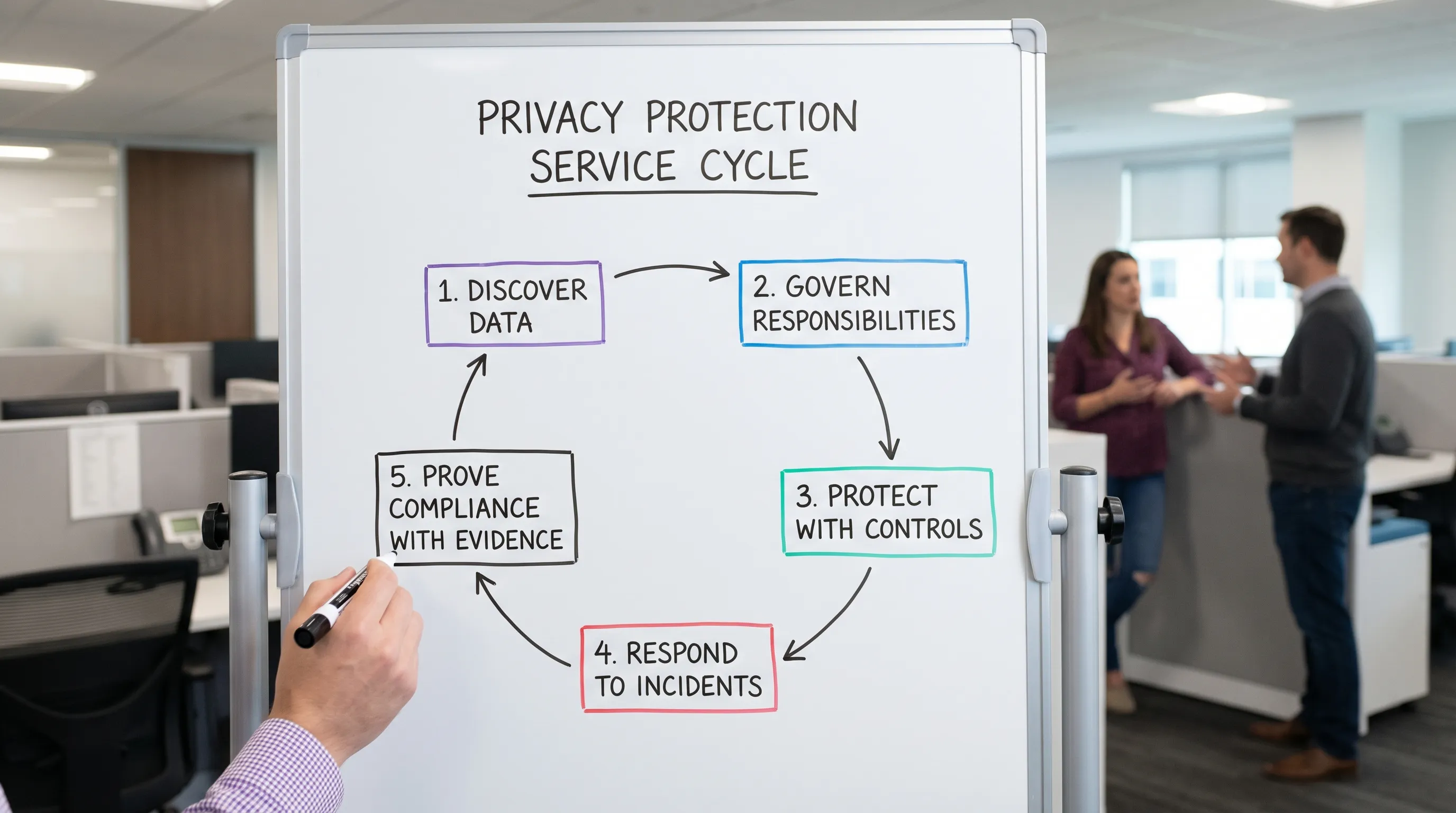
Choosing a provider for privacy protection services is no longer just about “getting a policy drafted”. In Jamaica, organisations are increasingly expected to demonstrate real control over how personal data is collected, used, stored, shared, and secured, in line with the Data Protection Act. That means the right support should feel practical, cross functional, and measurable, not theoretical.
This guide explains what you should reasonably expect when you engage privacy protection services in Jamaica, the typical deliverables, how engagements usually run, and how to spot value (and avoid expensive box ticking).
What “privacy protection services” should mean in Jamaica
A serious privacy protection engagement should help your organisation do three things at once:
Comply with the Data Protection Act requirements in day to day operations, not just on paper.
Reduce real risk, including unauthorised access, preventable breaches, vendor failures, and staff mishandling.
Prove what you’re doing, with evidence you can show to leadership, customers, and regulators if needed.
In practice, that requires both governance and implementation. Privacy is legal and operational, but it also touches IT security, HR, procurement, marketing, customer service, and any team handling sensitive or high volume data.
For official guidance and updates in Jamaica, it’s worth keeping an eye on the Office of the Information Commissioner (OIC), which has the regulatory oversight role connected to access to information and data protection.
The core deliverables you should expect from a credible provider
Different firms package services differently, but strong privacy protection services usually include the components below, tailored to your industry and risk.
1) A scoping phase that reflects your real data footprint
Before anyone writes policies, you should expect your provider to understand:
What personal data you collect (customers, staff, minors, patients, members, students)
Where it sits (paper, spreadsheets, cloud apps, email, line of business systems)
Who you share it with (banks, insurers, payroll, marketing platforms, overseas processors)
Which processes create the biggest exposure (onboarding, complaints, CCTV, call recording, background checks, payments)
If the scope is vague, the solution will be vague too.
2) A governance model that assigns accountability
Privacy protection services should help you establish clear ownership, for example:
Who is responsible for privacy decisions (management and process owners)
Who runs the programme day to day (a named role, internal or supported externally)
How issues escalate (incidents, complaints, vendor risks)
What gets reported to leadership and how often
This is where privacy becomes manageable instead of chaotic.
3) Practical documentation that matches your operations
You should expect documentation, but it should be usable and aligned to how you actually work. Depending on your organisation, that typically includes items like privacy notices, internal handling rules, retention guidance, and incident procedures.
Good documentation is not generic. It uses your systems, your forms, your departments, and your customer journeys.
4) Data handling processes people can follow
Privacy protection services should translate legal obligations into workflows, such as:
How staff identify and handle personal data safely
How access is approved and removed (especially for leavers and contractors)
How data is shared securely (including with third parties)
How records are retained and disposed of
If your provider only hands you templates, you will still be stuck when a real situation arises.
5) Vendor and third party controls (especially for cloud and overseas services)
Most Jamaican organisations rely on third parties for payroll, HR platforms, marketing tools, payment processing, or hosting. Your provider should address:
Due diligence, what you need to ask vendors before onboarding
Contract clauses and accountability expectations
Ongoing monitoring, proportionate to risk
Cross border transfer considerations where applicable
Third party risk is one of the most common gaps in otherwise “good” compliance programmes.
6) Security alignment with cyber security and operations
Privacy protection services should not replace cyber security, but they must connect to it. Expect collaboration around:
Access controls and least privilege
Logging and monitoring (where appropriate)
Encryption and secure transfer methods
Secure disposal (paper and digital)
Incident detection and response readiness
If privacy is treated as separate from security, you may end up with policies that cannot be enforced.
7) Breach readiness and response support
You should expect a clear plan for:
How staff recognise an incident and escalate quickly
What to do in the first hours (containment, evidence preservation)
Internal decision making and communications
Post incident improvements (so the same issue does not recur)
Even if you never have a major breach, being prepared reduces downtime and reputational damage.
8) Training that changes behaviour
Training is one of the best returns on effort, but only if it is role based. Effective privacy protection services usually include training that reflects how different teams interact with personal data, for example front desk, HR, IT, marketing, customer service, finance, and senior leadership.
What “good” looks like: evidence you should receive
Privacy work should produce proof, not just activity. Here is a practical way to evaluate deliverables.
Area | What you should expect | Evidence you can keep on file |
Scope and discovery | A clear view of where personal data is and how it moves | Data inventory summary, data flow notes, system list |
Governance | Clear responsibilities and escalation paths | Programme roles, reporting cadence, issue tracking approach |
Transparency | Plain language notices that reflect your processing | Updated privacy notice(s), supporting rationale |
Internal handling rules | Staff know what to do in common situations | SOPs or guidance for HR, customer queries, marketing, CCTV, etc. |
Third party management | Vendor privacy and security expectations are defined | Due diligence checklist, contract addenda or clauses |
Security alignment | Privacy requirements connect to technical controls | Control mapping notes, action plan tied to systems |
Incident readiness | A playbook that fits your environment | Incident response steps, contact list, decision workflow |
Training | Staff capability improves over time | Training plan, attendance records, tailored materials |
If a provider cannot explain what evidence you will be able to show after the engagement, clarify that before you sign.
How a privacy services engagement usually runs (and why it matters)
Privacy programmes fail when organisations expect a “one time fix”. The best providers set expectations early: you are building a capability.
A typical engagement often follows this structure.
Phase | What happens | Your organisation’s role |
Discovery and prioritisation | Understand processes, systems, and risks, agree scope | Provide access to process owners, existing policies, system context |
Design | Translate obligations into decisions, controls, and documents | Approve risk based choices, confirm how you actually operate |
Implementation | Roll out procedures, notices, contract updates, controls | Assign owners, make operational changes, communicate internally |
Training and embedding | Train teams, test workflows, refine what’s unclear | Ensure attendance, reinforce behaviours, update onboarding |
Assurance and improvement | Check what’s working, close gaps, build reporting | Review metrics, support audits, plan the next quarter |
Timelines vary depending on your size and complexity. What you should expect is clarity on what will be delivered first (highest risk), and what will be phased.
Choosing the right type of provider in Jamaica
Privacy protection services can come from different types of providers. Understanding the difference helps you buy the right thing.
Provider type | Often strong in | Watch outs | Best fit when |
Privacy and GRC consultants | End to end programme design and practical implementation | Quality varies, ask for delivery approach and sample outputs | You want a functioning programme, not only documentation |
Law firms | Legal interpretation, contracts, regulatory positioning | Implementation may be lighter unless they have an ops team | You have complex legal exposure or high stakes disputes |
IT or cyber security firms | Technical controls, monitoring, hardening, incident response | Privacy governance and notices may be shallow | Your main gap is security controls and operational security |
Internal led with external support | Strong organisational knowledge and adoption | Can stall without specialist guidance | You have an internal owner, but need structure and acceleration |
In many Jamaican organisations, the best outcome comes from privacy, legal, operations, and security working together, with one accountable programme owner.
Questions you should ask before you sign
A good provider will welcome these questions and answer them clearly.
What will you deliver in the first 30 to 60 days that reduces risk?
How will you learn our data flows and systems? (If the answer is “send us a list”, probe deeper.)
What evidence will we have at the end of the engagement?
How do you handle vendor and cross border data issues in practice?
What training will different teams receive, and how is it tailored?
What do you need from us to succeed? (Expect them to ask for leadership backing and access to process owners.)
Red flags that usually lead to “paper compliance”
Some warning signs are subtle, but costly.
No discovery work: jumping straight to templates without understanding your processes.
No ownership model: “We will do it for you” without building internal responsibility.
No linkage to security: privacy written as a policy only, with no control alignment.
No plan for rights requests and complaints: staff do not know what to do when someone asks for access or correction.
One size fits all training: a single slide deck for everyone, once.
A privacy programme should make daily work easier, not add confusion.
Industry realities in Jamaica (what services should account for)
Privacy protection services in Jamaica should reflect how local sectors operate.
Financial services and regulated entities: expect heavier emphasis on governance, monitoring, vendor oversight, and incident readiness.
Healthcare and wellness providers: sensitive data handling, confidentiality workflows, and strict access management.
Schools and youth programmes: handling minors’ data, consent expectations, photo and media controls, secure communication with parents.
Tourism and hospitality: high volume guest data, bookings, CCTV, Wi-Fi portals, and third party booking platforms.
BPOs and call centres: call recordings, scripts, QA processes, overseas clients, and strong operational controls.
Even within one industry, your risk profile depends on how much data you process, how sensitive it is, and how widely it is shared.

What to expect when working with PLMC
Privacy & Legal Management Consultants Ltd. (PLMC) supports organisations in Jamaica with data privacy, protection, and compliance programmes that connect governance requirements to real operations.
Depending on your needs, support may include data protection implementation, training sessions, risk assessment tools, cyber security services, and broader governance, risk, and compliance integration. If your organisation also has overlapping obligations, PLMC can support areas such as corporate governance and anti money laundering compliance.
If you want background reading before you engage support, these resources can help you frame the conversation internally:
To discuss what privacy protection services would look like for your organisation’s size, sector, and risk level, start with a conversation via Privacy & Legal Management Consultants Ltd..