
Policies and Procedures for Data Protection: Audit-Ready Guide

A data protection programme is only as strong as the documents that make it repeatable and provable. When a regulator, customer, bank, or internal auditor asks “Show me how you handle personal data”, verbal assurances do not help. Policies and procedures for data protection are what turn good intentions into consistent practice, and they are the backbone of audit readiness.
This guide explains what an “audit-ready” policy framework looks like for Jamaican organisations, what documents you actually need (and which ones are often unnecessary), and how to build an evidence pack that demonstrates compliance with the Data Protection Act.
What “audit-ready” means for data protection
In most Jamaican organisations, a privacy audit (formal or informal) tests three things:
Design: Do you have documented rules and controls that align with the law and your risks?
Operation: Do staff actually follow them in day-to-day work?
Evidence: Can you prove it with records, logs, approvals, and training results?
A common gap is having a privacy policy document, but no supporting procedures, no ownership, and no evidence trail. An audit-ready programme is less about having “more documents” and more about having the right documents, with clear accountability and consistent records.
Policy vs procedure vs standard: the hierarchy auditors expect
Many organisations mix these terms. Clarifying the hierarchy helps you avoid bloated documentation and makes testing easier.
Document type | What it does | Typical audience | Audit question it answers |
Policy | States the rule and management intent (what must be true) | All staff, management | “What is your organisation’s position and governance?” |
Procedure | Step-by-step process (how to do it) | Teams who execute the task | “How do you consistently perform the control?” |
Standard | Minimum requirements or baselines (for example password length) | IT, security, operations | “What minimum level is enforced?” |
Record (evidence) | Proof that the process happened | Auditors, regulators, management | “Show me it was done, for this time period.” |
If you are short on time, prioritise policies + procedures + evidence. Standards can be embedded as “minimum requirements” inside procedures.
The core set of data protection policies most organisations need
You do not need a separate policy for every department. Start with a manageable set that maps to the Data Protection Act principles and common risk areas.
Below is a practical “core set” used across many industries in Jamaica (financial services, education, healthcare, retail, and professional services).
Core policy | What it should cover (in plain language) | Typical owner | Evidence an auditor will ask for |
Data Protection (Privacy) Policy | Principles, lawful handling expectations, accountability, governance | DPO/Compliance/Legal | Approved policy, review history, staff acknowledgement |
Data Classification and Handling Policy | What is personal vs sensitive data, how to label, store, share | InfoSec/IT + Privacy | Labels, handling rules, examples, spot-check results |
Access Control Policy | Who gets access, least privilege, joiner-mover-leaver rules | IT/Security | Access reviews, provisioning tickets, role matrices |
Records Retention and Secure Disposal Policy | How long to keep data, deletion and disposal methods | Legal/Records + IT | Retention schedule, disposal logs, deletion evidence |
Incident and Data Breach Response Policy | What counts as an incident, escalation, roles, reporting, lessons learned | Security/Privacy | Incident register, tabletop tests, post-incident reports |
Individual Rights Handling Policy | Access/correction/erasure requests process and timelines | Privacy/Customer Ops/HR | Request log, response templates, outcomes |
Vendor and Third-Party Data Processing Policy | Due diligence, contracts, monitoring of processors | Procurement/Compliance | DPIA/vendor assessments, DPAs, review notes |
Remote Work and Acceptable Use Policy | Working from home, devices, email, cloud tools, confidentiality | HR + IT | Training records, device register, exceptions |
Depending on your operations, you may also need topic-specific policies such as CCTV/physical security, HR/employee privacy, marketing communications, or cross-border data transfers. The goal is not volume, it is coverage of your highest-risk processing.

The procedures that make your policies real (and testable)
Audits often fail at the procedure level. The policy says “we respect individuals’ rights”, but nobody can show a repeatable workflow, service mailbox, templates, or tracking.
Strong procedures are:
Role-specific (who does what, and when)
Time-bound (internal deadlines, not just legal ones)
Tool-aware (email address, ticketing system, spreadsheet register, or GRC tool)
Evidence-producing by design (it generates a log, approval, or record)
High-value procedures to document first
These are frequently tested because they are both legally important and operationally sensitive:
Data subject request procedure: intake, identity verification, scoping, search instructions, exemptions, response, closure, retention of request records.
Breach and incident response procedure: detection, triage, containment, assessment of impact, decision-making on notification, communications, post-incident review.
Joiner-mover-leaver procedure: access provisioning, access removal on exit, shared accounts control, periodic access recertification.
Retention and disposal procedure: triggers for deletion, legal holds, backup considerations, disposal methods (paper and electronic), approvals.
Vendor onboarding procedure: risk tiering, due diligence questions, contract requirements, security assurance, review cadence.
A useful test is this: if your DPO, IT lead, and HR manager are out for a week, can the organisation still execute the process correctly based on the procedure? If not, the procedure is not yet operational.
Aligning your documentation to Jamaica’s Data Protection Act
Your policies and procedures should clearly demonstrate the law’s core expectations in operational terms.
A simple way to structure this is to map each policy to:
A principle or obligation (fairness, purpose limitation, minimisation, accuracy, storage limitation, security, accountability, transfer controls)
A business activity (onboarding customers, payroll, marketing, CCTV, vendor services)
A set of controls (notices, access control, encryption, retention schedule, training)
If you need a refresher on definitions and core obligations, PLMC’s explainer is a helpful starting point: Jamaica Data Protection Act explained for businesses.
Clarify controller vs processor responsibilities
Where organisations get caught is assuming vendors “handle compliance”. Policies should explicitly state:
When your organisation is acting as controller (deciding purpose and means)
When you are acting as processor for someone else
What your minimum contract requirements are (confidentiality, security measures, sub-processing, incident notification, deletion/return)
This is also where your GRC and third-party risk approach should connect to privacy.
How to write policies that hold up in an audit
A good data protection policy is clear, enforceable, and easy to test. Avoid legal copy-paste that staff will not follow.
Include these elements in every policy
Purpose and scope: which entities, systems, and data types.
Definitions: keep them short, align with the Act where relevant.
Roles and responsibilities: Board/senior management oversight, DPO or privacy lead, IT/security, HR, business owners.
Policy statements (the “must” rules): keep each statement testable.
Exceptions process: how to request, who approves, how long exceptions last.
Monitoring and enforcement: audits, reviews, consequences.
Review cycle and version control: who reviews, how often, what triggers ad hoc updates.
Make procedures measurable
A procedure becomes audit-ready when you can attach internal service levels and evidence points. For example:
Rights requests: “Acknowledge within 2 business days, complete data search within 10 business days, draft response within 15 business days.”
Incidents: “Triage within 4 hours, contain within 24 hours, complete initial impact assessment within 72 hours.”
Even if your organisation uses simple tools (shared mailbox + spreadsheet), the key is consistency and traceability.
Build an “audit evidence pack” (what to keep, and why)
Most audit stress comes from scrambling for evidence at the last minute. An evidence pack is a structured folder or repository that you maintain continuously.
The minimum evidence set to maintain
Keep these items current and easy to export:
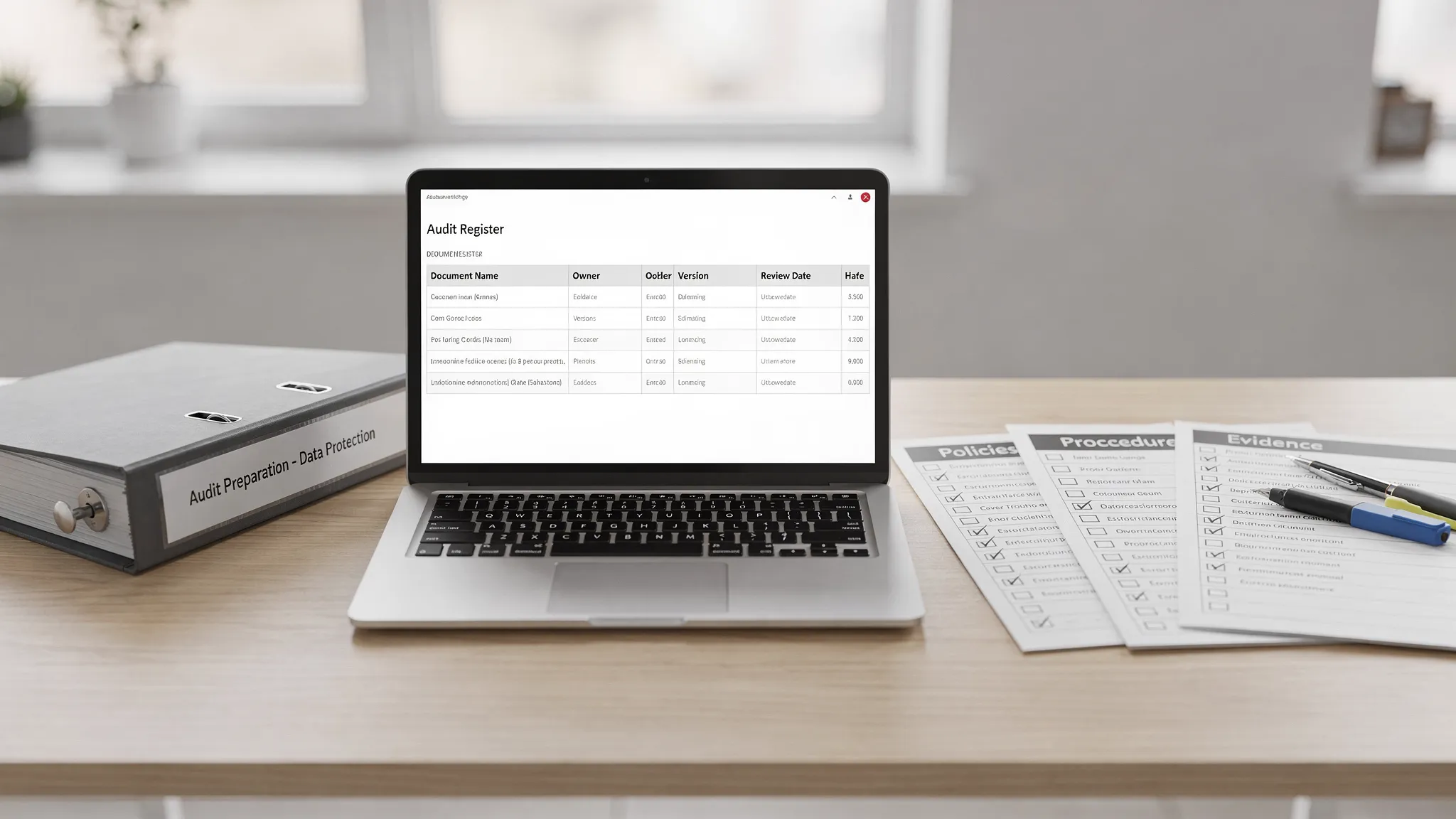
Policy register with owners, approval dates, and next review dates
Version-controlled policies and procedures, showing changes over time
Training plan and attendance records, including induction and annual refreshers
Data inventory / records of processing (even a phased approach is better than none)
Risk assessments and DPIAs (where relevant)
Vendor due diligence and contracts (especially data processing terms)
Incident register, including near misses and lessons learned
Access reviews and key security control evidence
If you are building this from scratch, PLMC’s practical checklist can help you identify the gaps without over-documenting: Privacy and data protection practical checklist.
Evidence-to-control mapping table (simple and effective)
This kind of mapping is useful for internal audits and for answering regulator questions efficiently.
Control area | Policy/procedure to point to | Evidence to produce | Suggested frequency |
Transparency | Privacy notices, communications procedure | Current notices, change log, proof of publication | Annual and when processing changes |
Security | Access control policy, incident response | Access review reports, incident register | Quarterly access reviews, ongoing incidents |
Retention | Retention policy, disposal procedure | Retention schedule, disposal logs | Annual review, ongoing disposal |
Vendor governance | Vendor policy, onboarding procedure | Due diligence results, signed contracts | At onboarding and renewal |
Rights handling | Rights policy, DSAR procedure | Request log, responses, ID verification records | Ongoing, monthly monitoring |
Common policy and procedure gaps (and how to fix them quickly)
Policies exist, but nobody owns them
Fix: assign an owner per policy (not “the company”), set a review date, and require documented approval. Ownership is one of the easiest audit wins.
Policies are generic templates that do not match operations
Fix: add one page of “how this works here”, for example what systems hold customer data, where requests are received, who approves marketing lists, and how retention is applied.
No evidence of training and awareness
Fix: define a training cadence (induction plus annual refresh), keep attendance logs, and include short assessments. If you run short sessions, document the agenda and objectives.
Rights requests are handled ad hoc
Fix: centralise intake (one email address or form), maintain a register, and standardise identity verification and response templates.
Vendors are not governed consistently
Fix: create a vendor risk tiering approach, require data processing terms in contracts, and keep a renewal review log.
A practical 60-day approach to become audit-ready
If you are behind, aim for credible progress, not perfection. An audit-ready programme can be built in phases.
Weeks 1 to 2: establish governance and scope
Confirm who is accountable (senior management sponsor), who leads day to day (DPO or privacy lead), and which business units and systems are in scope. Build a policy register and identify what already exists.
If you are planning your 2026 work programme, the quarter-by-quarter structure in PLMC’s roadmap may help you sequence deliverables realistically: Data protection Jamaica compliance roadmap for 2026.
Weeks 3 to 5: write or refresh the core policies, then publish
Focus on the core set first (privacy, access, retention, incidents, rights, vendors, remote work). Ensure:
Each policy has an owner, version, and review date.
Procedures are attached where execution is complex (rights, incidents, vendors, joiner-mover-leaver).
Staff can find the documents (intranet, shared drive, handbook).
Weeks 6 to 8: generate evidence and test one workflow
Pick one workflow that produces strong evidence, often rights handling or incident response. Run a test exercise and capture:
The log (request or incident record)
Decisions and approvals
Response templates and communications
Lessons learned and improvements made
Auditors value tested processes because they demonstrate operational maturity.
When professional support is worth it
Many organisations can draft basic policies internally, but support becomes valuable when:
You process sensitive personal data at scale (health, biometrics, financial)
You have complex vendor ecosystems (outsourced payroll, cloud services, call centres)
You have had an incident, complaint, or near miss
You need a programme that integrates privacy with wider GRC (risk, AML, cybersecurity)
PLMC supports Jamaican organisations with data protection implementation, training, and integrated compliance approaches. If you want an objective view of your current policies, procedures, and audit evidence, start with a free consultation via Privacy & Legal Management Consultants Ltd..
