
Legal and Privacy: Who Owns Compliance Internally?

When a privacy issue hits, the first question is rarely “What does the law say?” It is “Who owns this internally?” If your answer is “Legal,” “IT,” or “the Data Protection Officer,” you are already at risk, because effective compliance is not a single department’s job. It is an operating model.
In Jamaica, the Data Protection Act places accountability on the organisation (as controller) for how personal data is collected, used, secured, shared, and retained. That accountability can be delegated in tasks, but not in responsibility. The practical challenge is designing clear ownership so decisions are fast, evidence is consistent, and nothing falls between teams.
“Legal compliance” vs “privacy compliance”: why the confusion happens
Many organisations treat privacy as a legal checkbox: update the privacy notice, add consent language, sign vendor clauses, done. In reality, privacy compliance is both:
Legal and regulatory (meeting obligations under the Data Protection Act and related rules)
Operational and technical (how data actually flows through systems, people, vendors, and processes)
Legal typically owns interpretation, risk appetite, and defensible documentation. Privacy, however, lives inside day to day operations: onboarding staff, running HR systems, managing customer databases, deploying cybersecurity controls, marketing campaigns, customer support scripts, records retention, and breach response.
That is why the right question is not “Who owns compliance?” but:
Who is accountable for the privacy programme?
Who owns data risk in each business process?
Who has decision rights for high impact calls (vendors, breaches, new products, cross border transfers)?
The accountability principle: what “ownership” must achieve
A workable internal model should deliver four outcomes:
Single point accountability for the privacy programme (governance, reporting, assurance).
Distributed execution across departments that actually process personal data.
Reliable evidence (policies, logs, approvals, training records, vendor due diligence) that proves compliance.
Fast escalation when risk spikes (incidents, complaints, regulator engagement, media exposure).
In practice, most Jamaican organisations succeed when they treat privacy as part of Governance, Risk, and Compliance (GRC), not as a standalone legal project.
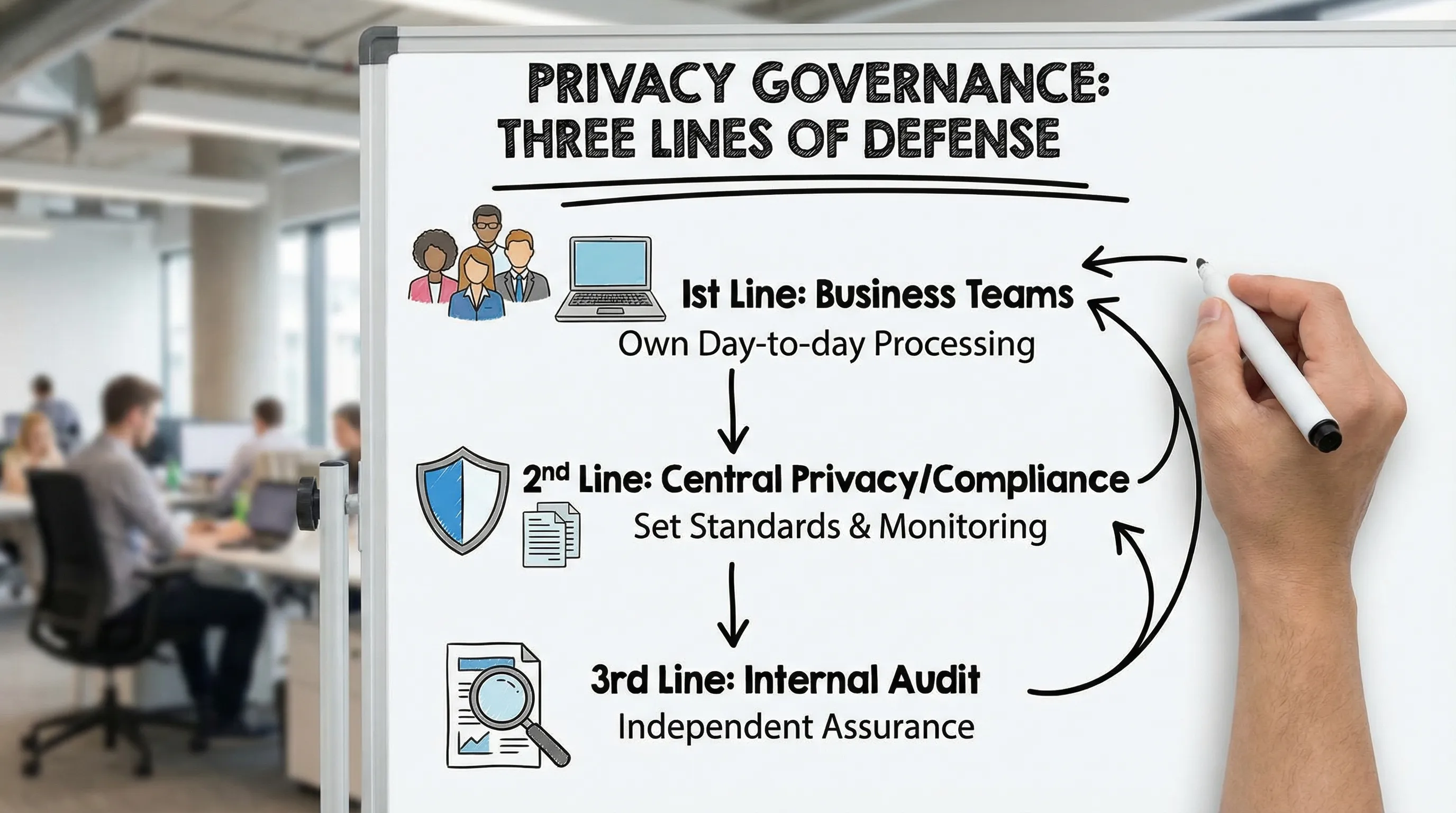
Common internal models (and when each works)
Centralised model (privacy sits mostly with one team)
A central privacy function (often Legal/Compliance) drafts policies, approves initiatives, handles rights requests, and runs training.
This can work for smaller organisations, but it tends to bottleneck decisions, and it fails when operational teams make changes without involving the centre.
Federated model (privacy champions embedded in departments)
Business units keep ownership of their processing activities, supported by trained privacy champions. A central function sets standards, tools, and assurance.
This is strong for larger or fast moving organisations (finance, telecoms, retail, BPOs), especially where data processing is spread across multiple systems and vendors.
Hybrid model (recommended for most organisations)
A central privacy lead owns governance and the programme, while departments own execution, with clear escalation paths.
This is usually the most resilient approach: it reduces single points of failure while still keeping accountability clear.
Who should be accountable: Board, CEO, or DPO?
“Accountable” does not mean “does all the work.” It means the role that must answer, in governance terms, for whether the organisation can demonstrate compliance.
Board and executive leadership
Board: sets risk appetite, requires reporting, ensures resources.
CEO/Managing Director: accountable for implementation across the enterprise.
If leadership treats privacy as optional, every other ownership conversation becomes theoretical.
Privacy lead (often called a DPO)
Many organisations appoint a Data Protection Officer or privacy lead (title varies). Whether or not your organisation is legally required to appoint a specific officer in every scenario, having a named privacy programme owner is one of the fastest ways to reduce ambiguity.
The privacy lead typically:
Runs the privacy governance calendar
Maintains the compliance framework (policies, templates, registers)
Advises on risks and controls
Coordinates responses (rights requests, incidents, regulator queries)
Legal and Compliance
Legal should own:
Legal interpretation, contract standards, and regulatory engagement strategy
High risk decision support (for example, whether a proposed use fits a lawful basis)
But Legal rarely owns the full operational truth of where data sits and who touches it. That is why Legal alone cannot “own privacy compliance.”
A practical RACI: who does what across the privacy lifecycle
A RACI matrix helps stop the most common failure mode: “Everyone thought someone else was doing it.” Below is a starting point you can adapt.
Key: R = Responsible (does the work), A = Accountable (signs off), C = Consulted, I = Informed
Privacy activity | Business process owner | Privacy lead / DPO | Legal | IT / Cybersecurity | HR | Procurement / Vendor mgmt | Internal Audit | Executive sponsor |
Maintain data inventory and data flows | R | A | C | C | C | C | I | I |
Approve privacy notices and key disclosures | C | R | A | I | C | I | I | I |
Handle data subject rights requests | C | A/R | C | C | C | I | I | I |
Conduct risk assessments / DPIA style reviews | R | A/R | C | C | C | C | I | I |
Security controls for personal data (access, logging, backup) | C | C | I | A/R | I | I | I | I |
Vendor due diligence and contracting for processors | C | C | C | C | I | A/R | I | I |
Incident response and breach management | C | A/R | C | A/R | C | I | I | I |
Training and awareness | C | A/R | C | C | A/R | I | I | I |
Privacy compliance monitoring and reporting | I | A/R | C | C | C | C | C | I |
Independent assurance / audits | I | C | I | I | I | I | A/R | I |
Two notes that matter in real organisations:
Business process owners cannot be “informed only.” They must be responsible for their processing activities because they control the workflows.
IT cannot be accountable for privacy. IT can be accountable for security controls, but privacy includes purpose, fairness, retention, and disclosure decisions that sit with the business.
Decision rights: the five calls you must assign explicitly
Even with a RACI, compliance breaks down when teams do not know who makes final decisions. Assign decision rights, in writing, for at least these:
1) Launching a new product, campaign, or data use
Who can say “yes,” “yes with controls,” or “no”? Require a lightweight review trigger for anything that changes:
the purpose of processing
categories of data collected
who data is shared with
how long data is kept
2) Vendor onboarding and cross border processing
Procurement can run the process, but privacy and security must define minimum requirements.
This becomes especially important in travel and cross border services, where personal data moves quickly across systems and jurisdictions. If you integrate an external visa or border administration platform, your contracts, due diligence, and customer disclosures must align with your obligations. For example, travel businesses that work with partners like SimpleVisa’s eVisa solutions should treat that relationship as a structured vendor risk scenario, confirm roles (controller/processor), security expectations, and how data is handled end to end.
3) Responding to data subject requests
Rights requests are time sensitive and evidence driven. Decide:
who receives requests (front line vs central inbox)
who verifies identity
who searches systems and signs off on the response
4) Managing incidents and potential breaches
Incident response fails when teams debate authority mid crisis. Define in advance:
who declares an incident
who leads communications internally
who approves regulator and customer communications
5) Retention and deletion
Retention is one of the most overlooked gaps because it is uncomfortable: deletion requires changing habits and systems.
Assign who can approve retention schedules and who can enforce deletion in systems, including backups where feasible and appropriate.
What “good” looks like: an operating rhythm, not a policy binder
Ownership becomes real when it shows up on calendars, dashboards, and meeting agendas. A simple operating rhythm for many organisations includes:
Monthly privacy working session (privacy lead + champions): open actions, vendor reviews, upcoming initiatives.
Quarterly governance review (executive sponsor): metrics, incidents, training completion, high risk projects.
Annual assurance cycle (internal audit or independent reviewer): evidence sampling, control testing, remediation plan.
To keep reporting meaningful, use a small set of indicators you can actually measure:
Metric | What it tells you | Why leadership cares |
% systems/processes mapped in data inventory | Visibility of risk | Unknown processing is unmanageable risk |
Time to close rights requests | Operational readiness | Delays drive complaints and regulator scrutiny |
Vendor risk reviews completed vs planned | Third party exposure | Vendors are a common failure point |
Training completion by role | Culture and awareness | Human error drives incidents |
Incidents logged and time to contain | Resilience | Faster containment reduces harm and cost |
The most common ownership mistakes (and how to fix them)
Mistake 1: “Privacy lives with Legal”
Fix: keep Legal as a key decision partner, but assign operational ownership to process owners, supported by a privacy lead.
Mistake 2: “IT owns privacy because it owns the systems”
Fix: make IT accountable for security controls and incident response execution, but keep purpose and disclosure decisions with the business.
Mistake 3: “We appointed a DPO, so we are covered”
Fix: a privacy lead without authority, budget, or departmental champions becomes a single point of failure.
Mistake 4: “No one owns retention”
Fix: align retention to legal requirements, business needs, and risk, then assign enforcement owners for each system.
A fast start: how to assign ownership in the next 30 days
If you need momentum without boiling the ocean:
Name an executive sponsor and a privacy programme owner (privacy lead).
Create a cross functional privacy working group (Legal, IT/security, HR, Procurement, Operations, Customer Service).
Define the RACI for three workflows first: rights requests, vendor onboarding, incident response.
Pick a single evidence repository (even a controlled folder structure) for policies, logs, and approvals.
If you want a deeper “what to implement” view alongside governance, PLMC has practical guides that complement this ownership discussion, including:

Frequently Asked Questions
Is privacy compliance owned by Legal or IT? Neither should own it alone. Legal typically owns legal interpretation and contracting standards, IT owns security controls, but the organisation must assign a privacy programme owner and make business process owners responsible for their processing.
Do we need a Data Protection Officer to be compliant in Jamaica? Many organisations appoint a DPO or privacy lead to create clear accountability and coordination. Whether a formal DPO is required in your exact situation depends on your context, but a named privacy programme owner is a strong governance practice.
Who should handle data subject access requests internally? A central privacy function should coordinate and sign off responses, while system and process owners (HR, customer service, operations, IT) are responsible for searching records and providing evidence within agreed timelines.
Where should vendor compliance sit, Procurement or Privacy? Procurement should run the workflow, but privacy and security must set minimum standards, due diligence checks, and contract requirements. Accountability often sits with Procurement for execution, with Privacy consulted and Legal supporting contract terms.
What is the biggest risk if ownership is unclear? Delays and inconsistent decisions. That shows up as missed rights request timelines, unmanaged vendor exposure, and slow incident response, all of which increase legal, reputational, and operational risk.
Need help defining internal ownership for legal and privacy compliance?
Privacy & Legal Management Consultants Ltd. (PLMC) supports Jamaican organisations with practical, defensible compliance programmes, including governance design, role based training, risk assessments, and implementation support aligned to the Data Protection Act.
If you are unsure whether your current structure is workable, start with a quick ownership review: map your key workflows (rights requests, vendors, incidents), assign a RACI, and identify gaps in authority and evidence. You can also contact PLMC for a free consultation to pressure test your model and prioritise what to fix first.
