
International Data Protection Standards: A Plain-English Guide

When a Jamaican organisation stores employee records in a US HR platform, uses an EU-based marketing tool, or processes bookings for overseas guests, one question shows up fast: what “good” data protection looks like beyond our borders.
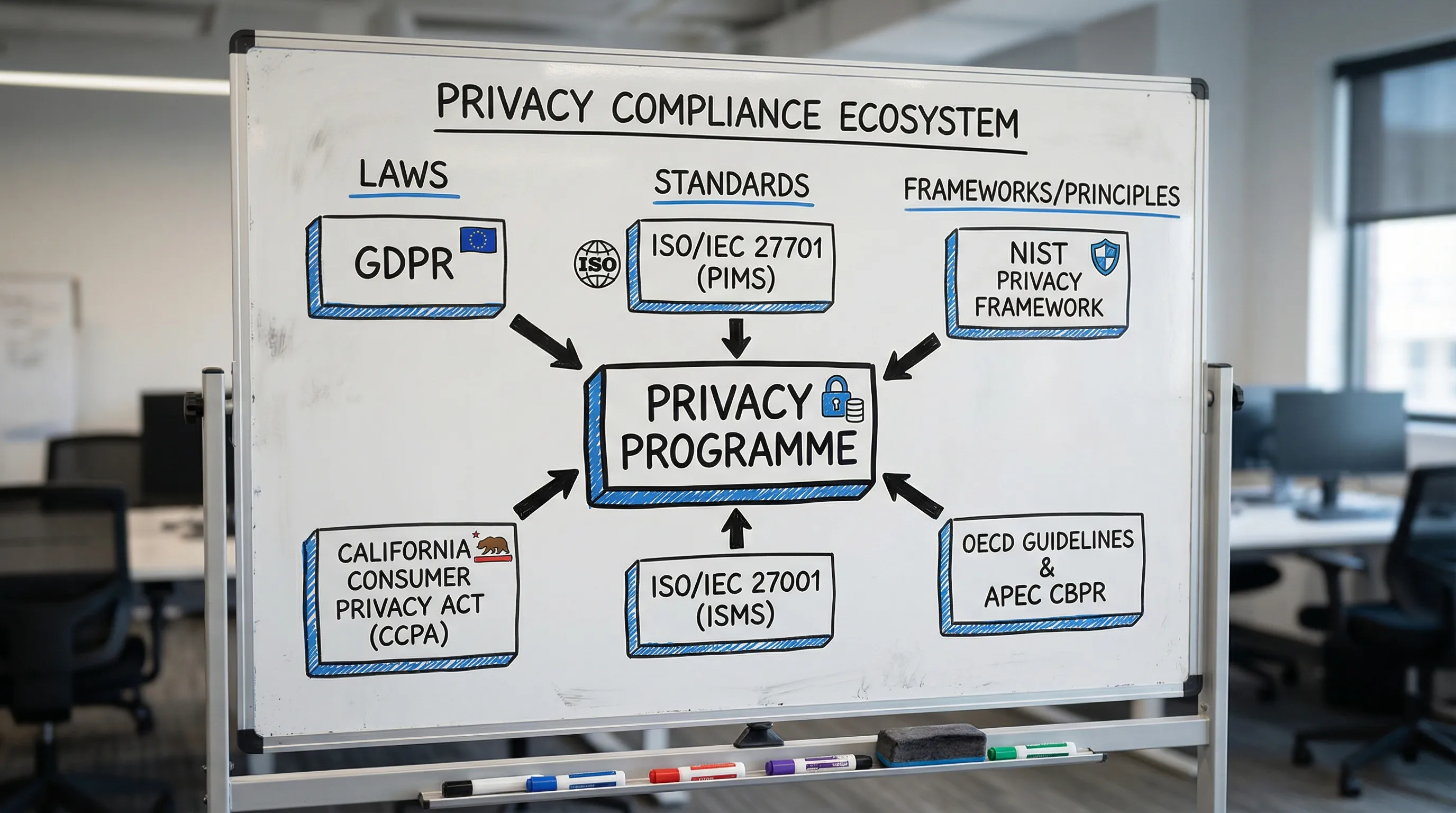
That is where international data protection standards come in. Some are laws (like the EU’s GDPR). Others are frameworks and standards (like ISO/IEC 27701 or the NIST Privacy Framework). In plain English, they are widely accepted rulebooks that help organisations protect personal information in a consistent, auditable way, even when data moves across countries and vendors.
This guide breaks down the main international standards, what they mean for Jamaican organisations in 2026, and how to choose a practical path to alignment.
What are “international data protection standards” (and what are they not)?
People often use the phrase international data protection standards to describe several different things:
Laws with extraterritorial reach: Rules that may apply to you even if your business is not physically located in that country (GDPR is the most well-known example).
International conventions and principles: High-level commitments adopted by multiple countries (for example, Council of Europe Convention 108+ and the OECD Privacy Guidelines).
Operational standards and frameworks: Practical playbooks for building and proving a privacy programme (for example, ISO/IEC 27701 and the NIST Privacy Framework).
Cross-border transfer schemes: Mechanisms intended to support data flows between economies (for example, APEC’s Cross-Border Privacy Rules).
They are not a substitute for Jamaica’s Data Protection Act requirements. Think of them as a way to organise, operationalise, and demonstrate that your privacy and security practices meet expectations that clients, regulators, and international partners recognise.
The major international standards, explained in plain English
Below are the most commonly referenced standards and frameworks Jamaican organisations encounter, especially in outsourcing, financial services, tourism, healthcare, education, and any business using global cloud providers.
GDPR (EU General Data Protection Regulation)
The GDPR is a law, not just a best-practice guide. Organisations outside the EU can still be affected if they offer goods or services to individuals in the EU or monitor their behaviour.
Why it matters: GDPR has shaped privacy expectations worldwide and influences contracts, vendor questionnaires, and procurement requirements.
Authoritative source: the official GDPR text on EUR-Lex.
ISO/IEC 27701 (Privacy Information Management System)
ISO/IEC 27701 is a privacy extension to ISO/IEC 27001 (information security management). In plain terms, it helps you build a privacy management system with documented controls, roles, risk management, and auditability.
Why it matters: it is widely recognised in corporate procurement and is useful when you need to show a structured programme rather than a collection of policies.
Authoritative source: ISO’s overview of ISO/IEC 27701.
ISO/IEC 27001 (Information Security Management)
ISO/IEC 27001 is primarily security-focused, but it often sits at the core of privacy compliance because privacy requires appropriate security measures.
Why it matters: many clients accept ISO/IEC 27001 certification (or alignment) as evidence of disciplined security governance.
Authoritative source: ISO’s overview of ISO/IEC 27001.
NIST Privacy Framework (and related NIST guidance)
The NIST Privacy Framework is a risk-based approach that helps organisations identify privacy risks, apply controls, and communicate maturity. It is especially common in US-linked supply chains.
Why it matters: it provides a practical structure for measuring progress and integrating privacy with enterprise risk management.
Authoritative source: NIST Privacy Framework.
OECD Privacy Guidelines
The OECD Guidelines are not a law, but they are foundational. They outline core privacy principles that influenced many modern laws.
Why it matters: they provide a globally understood “baseline logic” for fair and responsible personal data use.
Authoritative source: OECD Privacy Guidelines.
Council of Europe Convention 108+ (modernised Convention 108)
Convention 108+ is an international treaty focused on data protection. It is influential in shaping national laws and cross-border cooperation.
Why it matters: it reinforces global norms around rights, safeguards, and oversight.
Authoritative source: Council of Europe page on Convention 108+.
APEC Cross-Border Privacy Rules (CBPR)
APEC CBPR is designed to support trusted cross-border data flows between participating economies.
Why it matters: you may encounter it in Asia-Pacific procurement and vendor assurance discussions.
Authoritative source: APEC overview of Cross-Border Privacy Rules.
Quick comparison: which standard helps with what?
Different standards solve different problems. This table gives a practical way to think about them.
Standard or framework | Type | What it helps you do | Where you’ll see it most | Best for |
GDPR | Law | Meet strict requirements for lawful processing, transparency, rights, and transfers | EU business, EU vendors, global contracts | Organisations touching EU personal data, or selling into the EU |
ISO/IEC 27701 | Standard | Build a privacy management system (policies, roles, risk, auditability) | Enterprise procurement, regulated industries, mature GRC programmes | Organisations that need a certifiable or auditable privacy structure |
ISO/IEC 27001 | Standard | Build an information security management system | Enterprises, MSPs, BPOs, critical services | Organisations needing demonstrable security governance |
NIST Privacy Framework | Framework | Manage privacy risk and maturity in a structured way | US-linked supply chains, risk-based programmes | Organisations that want a measurable privacy roadmap |
OECD Guidelines | Principles | Anchor your programme in globally recognised privacy principles | Policy discussions, baseline expectations | Organisations looking for a clear “why” behind privacy rules |
APEC CBPR | Transfer scheme | Support trusted cross-border transfers within participating economies | Asia-Pacific procurement | Organisations moving data in APEC ecosystems |
The common “privacy basics” that show up almost everywhere
Even though the documents differ, most international data protection standards converge on a shared set of expectations:
Be clear with people about what you collect, why you collect it, and who you share it with.
Collect only what you need and keep it only as long as necessary.
Secure personal data with reasonable organisational and technical safeguards.
Respect individual rights (for example, access and correction) and have a process to respond.
Be accountable: document decisions, assign ownership, and be able to prove what you do.
Control third parties and cross-border sharing through due diligence and contracts.
If your organisation already has a working compliance programme under Jamaica’s Data Protection Act, these concepts will feel familiar. The difference internationally is usually the depth of evidence expected and the formalisation of your processes.
How international standards relate to Jamaica’s Data Protection Act
For Jamaican organisations, international standards usually matter for three reasons:
1) Client and partner requirements
International customers often ask for evidence such as:
a recognised framework (for example, “Do you align to ISO/IEC 27701 or NIST?”)
structured risk assessments and DPIAs
vendor oversight and documented security controls
breach management readiness
Even if the client is not asking for certification, they often want proof of a repeatable programme.
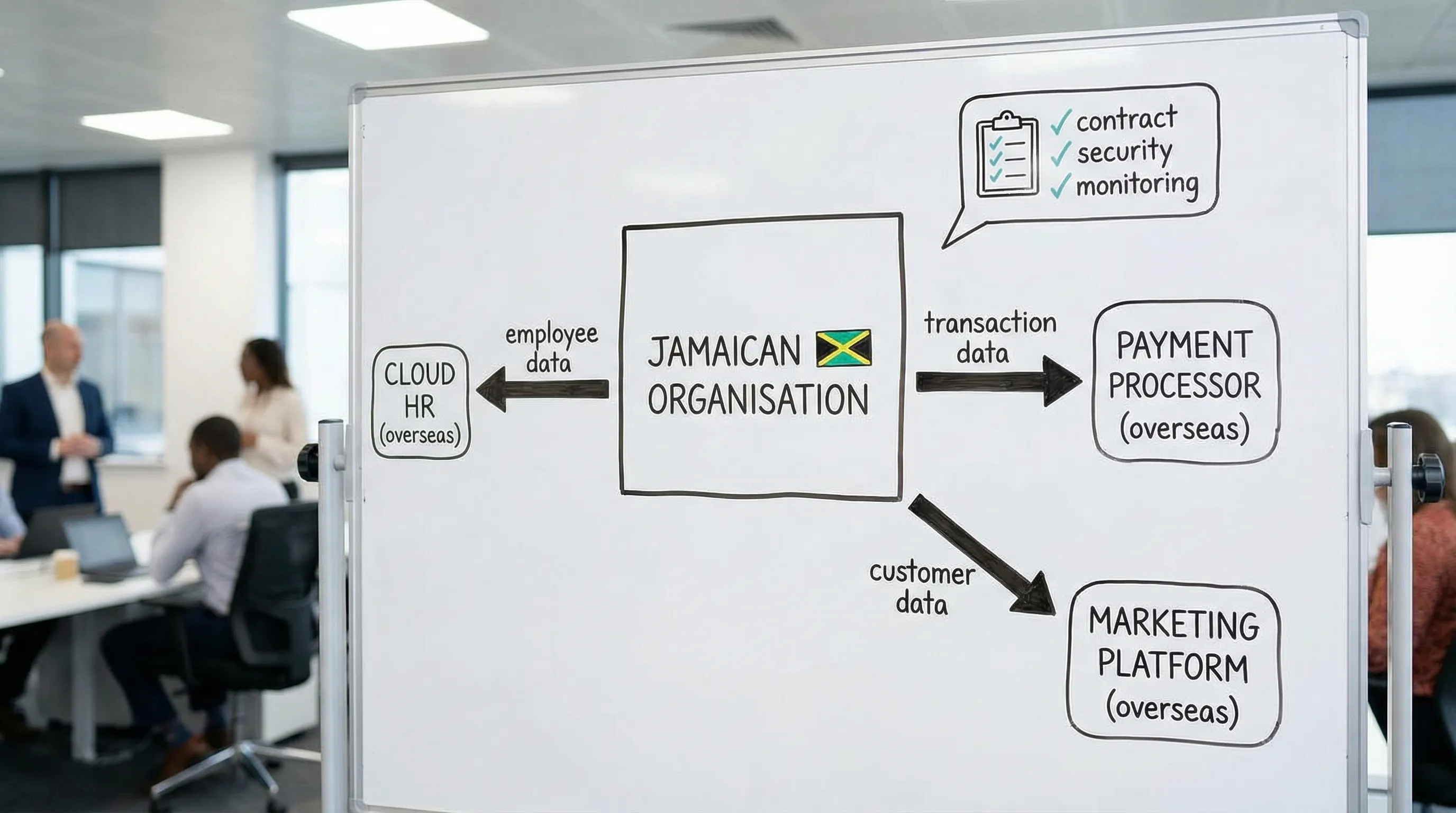
2) Cross-border operations and cloud services
Most organisations use overseas vendors for email, HR, payroll, CRM, analytics, and hosting. International standards provide a shared language for assessing those vendors and documenting transfer safeguards.
3) Audit readiness and defensibility
When something goes wrong (a breach, a complaint, a vendor incident), standards help you show that your organisation followed a recognised, risk-based approach.
If you want Jamaica-specific operational guidance, see:
Cross-border data transfers: what “adequate protection” looks like in practice
Cross-border transfer rules are often the hardest part for teams because the data flows are real and messy: cloud hosting, outsourced support, remote access, and shared tools.
A plain-English approach is to focus on three questions:
Where does the data go (and who can access it)?
You need a defensible view of:
which vendors process personal data
which countries are involved (hosting, support, sub-processors)
which categories of personal data are affected (employee, customer, health, financial)
This is why data mapping and vendor inventories are a priority in most standards.
What safeguards exist?
Internationally, safeguards usually combine:
contract controls (privacy clauses, confidentiality, security requirements, breach notification, audit rights)
technical controls (access control, MFA, encryption, logging)
governance controls (risk assessments, approvals, monitoring)
Can you prove it?
A recurring theme in ISO and NIST-aligned programmes is evidence. Examples include signed vendor agreements, due diligence questionnaires, DPIAs, security policies, training records, and incident response test results.
A practical alignment plan (without boiling the ocean)
If you are trying to align to international data protection standards, the goal is not to “implement GDPR” or “become ISO-certified overnight.” The goal is to build a programme that is coherent, risk-based, and provable.
Here is a pragmatic sequence that works for most Jamaican organisations.
Step 1: Choose your target outcome
Pick one primary driver:
Contract readiness (to satisfy customer/vendor questionnaires)
Audit readiness (to demonstrate governance and controls)
Risk reduction (to reduce breaches, complaints, and operational surprises)
Your target outcome determines whether ISO/IEC 27701, NIST, or another approach will be the best fit.
Step 2: Establish your “minimum viable privacy programme”
Most international frameworks expect, at minimum:
defined roles and accountability (who owns privacy and security decisions)
a current data inventory (what you collect, where it lives, why you use it)
privacy notices and internal policies that match real practice
vendor governance and contract controls
an incident response plan and a way to test it
a process for rights requests (and staff who know what to do)
Step 3: Add the evidence layer
This is where many organisations fall short: they do the work, but do not document it.
A useful mindset is: if a regulator or key customer asked for proof next week, what would you show?
Step 4: Measure and improve
International standards assume continuous improvement. That can be lightweight, for example quarterly reviews of:
new vendors and system changes
incidents and near-misses
training completion
privacy risk assessments for new projects
A mapping table: activities, evidence, and the standards they support
Use this as a starting point when building your internal implementation plan.
What you implement | What “good evidence” looks like | Supports alignment to |
Data inventory and data flow mapping | Data map, system list, records of processing (even a simplified register) | GDPR, ISO/IEC 27701, NIST |
Vendor and cross-border transfer governance | Vendor register, due diligence records, signed DPAs, security requirements, sub-processor awareness | GDPR, ISO/IEC 27701, OECD principles |
Rights request workflow | SOP for access/correction/deletion requests, request log, response templates | GDPR, ISO/IEC 27701 |
Privacy risk assessment for projects | DPIA/PIA template, completed assessments, approval trail | GDPR, ISO/IEC 27701, NIST |
Security controls for personal data | Access controls, MFA, encryption approach, logging, incident response plan, testing records | ISO/IEC 27001, ISO/IEC 27701, NIST |
Training and awareness | Training content, attendance records, role-based modules, refresh schedule | GDPR, ISO/IEC 27701, NIST |
Governance and oversight | Assigned owners, reporting cadence, management sign-off, internal audits or reviews | ISO/IEC 27701, ISO/IEC 27001, NIST |
How to choose the right standard for your organisation
There is no single “best” international standard. The right choice depends on your risk profile, customers, and operational maturity.
If you are a growing SME using standard cloud tools
Start with a strong baseline privacy programme and a clear checklist, then add vendor governance and incident readiness. If customers begin asking for formal alignment, you can layer in a NIST-style maturity approach without committing to certification.
If you are in financial services, BPO, or handle large volumes of sensitive data
ISO/IEC 27001 plus ISO/IEC 27701 alignment is often a practical pairing because it combines security governance and privacy governance. Even without certification, using the standards as a structure can help you build defensible controls.
If you actively serve EU residents or have EU clients
You should treat GDPR-driven requirements as a likely contractual and legal priority. Even if your main legal obligations are domestic, GDPR-aligned practices often become necessary to win and keep EU-linked business.
Common mistakes organisations make with international standards
Treating privacy as “policies only”
Policies matter, but international standards look for operational reality: workflows, approvals, logs, tests, and training.
Copying templates without matching real processes
A “perfect” privacy notice does not help if the business actually uses data differently in practice. Misalignment increases regulatory and reputational risk.
Forgetting vendors (and sub-vendors)
Most data incidents involve third parties in some way. International standards expect you to know who your processors are and what they do.
Over-scoping too early
Trying to implement every control at once burns out teams. A staged plan with measurable milestones is more credible than a massive document drop.
Frequently Asked Questions
Are international data protection standards legally required in Jamaica? Not necessarily. Jamaica’s Data Protection Act sets legal requirements, while international standards are usually adopted to meet customer expectations, manage risk, and demonstrate best practice.
What is the difference between GDPR and ISO/IEC 27701? GDPR is a law with specific obligations and enforcement. ISO/IEC 27701 is a management system standard that helps you organise policies, roles, risk, and evidence to run a privacy programme.
Do we need ISO certification to benefit from ISO/IEC 27701 or ISO/IEC 27001? No. Many organisations align to the standards without certification to structure controls and improve audit readiness. Certification is a separate decision based on cost, customer demands, and maturity.
Which standard should we start with if we are overwhelmed? Start with a practical baseline: data mapping, vendor controls, incident readiness, and a rights-request workflow. From there, choose a framework (often NIST) to measure maturity, or ISO/IEC 27701 if you need a formal management system.
How do international standards affect cross-border cloud services? They push you to document where data is hosted, who can access it, and what contractual and technical safeguards protect it. This is often the difference between “we use the cloud” and “we can defend our cloud risk decisions.”
Build an internationally credible privacy programme in Jamaica
If your organisation needs to align with international data protection standards while meeting Jamaica’s Data Protection Act obligations, PLMC can help you translate requirements into a working programme with the right governance, evidence, and training.
Explore PLMC at Privacy & Legal Management Consultants Ltd. or request a free consultation to discuss your current state, vendor landscape, and the most practical alignment path for 2026.
