
Difference Between Data Privacy and Data Protection: Examples

People often use “data privacy” and “data protection” as if they mean the same thing. In practice, they point to two different (but tightly connected) responsibilities. Getting the distinction right helps Jamaican organisations design policies, training, controls, and evidence that actually stand up under the Data Protection Act and, just as importantly, earn trust from customers, staff, and the public.
In this guide, we break down the difference between data privacy and data protection in plain language, then ground it with real workplace examples you can recognise.
Data privacy vs data protection (plain-language definitions)
What data privacy is
Data privacy is about appropriate use of personal information. It focuses on questions like:
Do we have a valid reason to collect this personal data?
Did we clearly tell people what we are doing with it?
Are we using it only for the purpose we stated?
Are we respecting the rights people have over their information?
You can think of privacy as the “rules of the road” for personal data: fairness, transparency, purpose limitation, and respecting individuals.
What data protection is
Data protection is about the controls and safeguards that keep personal data secure and properly managed across its lifecycle. It focuses on questions like:
Is the data stored securely and accessed only by authorised persons?
Do we have retention rules and deletion processes?
Are vendors and systems governed with proper contracts and oversight?
Can we detect, respond to, and recover from breaches?
You can think of data protection as “the seatbelts, brakes, and airbags”: security and operational controls that prevent harm and reduce risk.
Privacy sets expectations and boundaries for use. Protection enforces those boundaries with process, governance, and security.
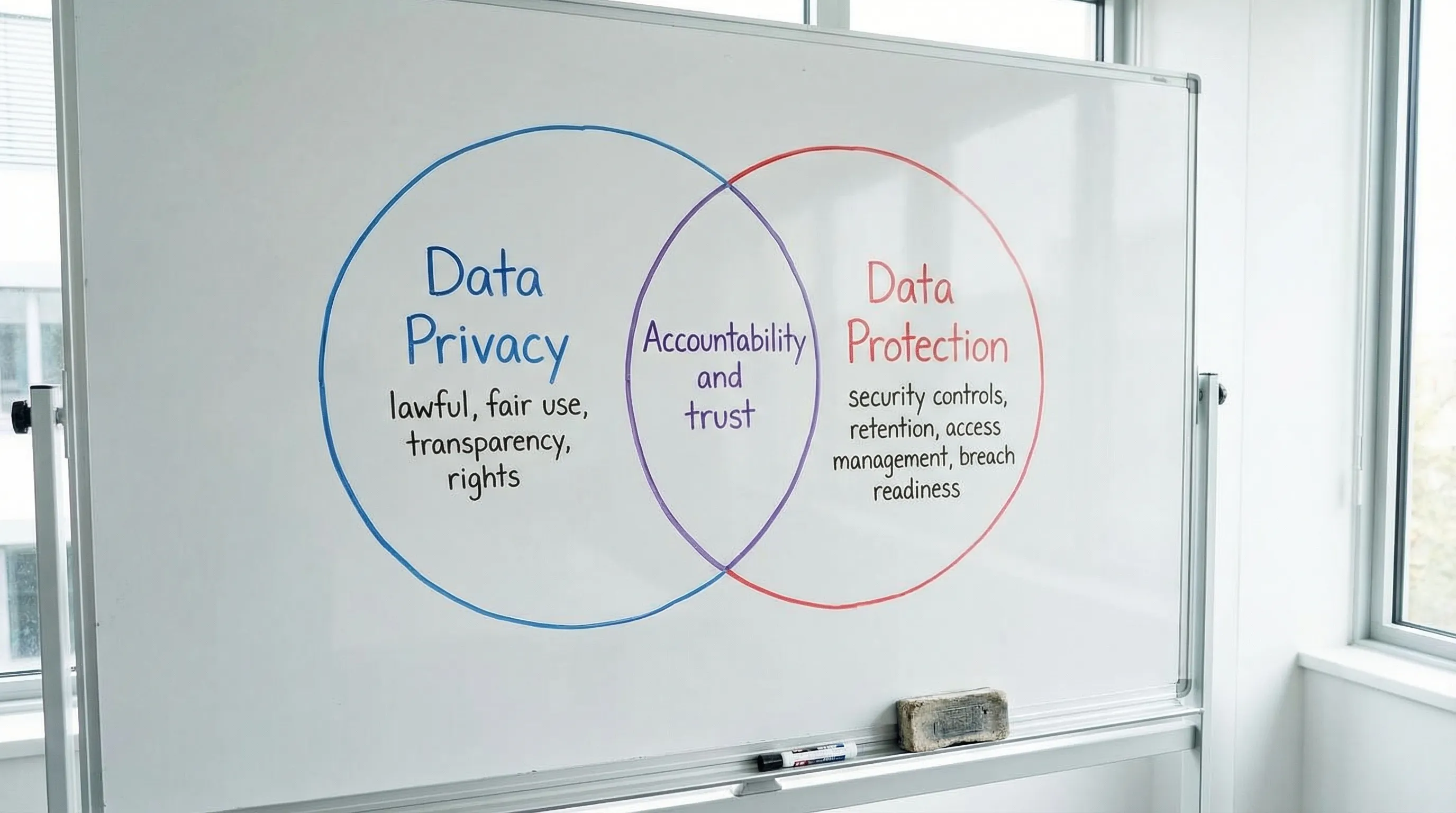
The core difference, summarised
A helpful way to separate the two is to ask:
Privacy: “Should we do this with the data?”
Protection: “How do we stop the data from being misused, lost, or exposed?”
Here is the distinction in a quick reference table.
Topic | Data privacy | Data protection |
Main focus | Appropriate, lawful, fair use of personal data | Safeguarding data with controls across its lifecycle |
Primary question | “Are we allowed to collect and use this, and have we been transparent?” | “Is it secured, governed, and handled safely end to end?” |
Typical artefacts | Privacy notices, consent wording (when relevant), lawful basis records, rights-handling procedures | Access controls, encryption, backups, retention schedules, incident response, vendor security requirements |
Main risk if weak | People are surprised, treated unfairly, or their rights are ignored | Data is leaked, altered, lost, ransomed, or accessed improperly |
Who often owns it | Legal, compliance, HR, marketing, product | IT, security, operations, risk, compliance |
In a well-run organisation, neither side operates alone. Privacy without protection becomes “good intentions with weak execution”. Protection without privacy becomes “secure processing that is still inappropriate or unlawful”.
Examples: data privacy vs data protection in real business scenarios
Below are practical examples to show where privacy ends and protection begins. In most cases, you need both.
Example 1: Collecting employee emergency contacts
Privacy issue (use): You should be able to explain why you need the information, limit it to what is necessary, and tell employees how it will be used (emergency contact only, not for marketing or unrelated HR decisions).
Protection issue (safeguard): Emergency contact details should be restricted to authorised HR personnel, stored securely, and removed when no longer needed.
Example 2: Sending a marketing email to a customer list
Privacy issue (use): The key question is whether you have a proper basis to send the message, whether the person was clearly informed, and whether you honour opt-outs and preferences.
Protection issue (safeguard): The mailing list must be protected from unauthorised export, sharing, or misuse. Access rights, audit logs, and vendor controls matter, especially when using third-party email tools.
Example 3: CCTV at an office or retail location
Privacy issue (use): Are you using CCTV for a defined purpose (for example, security and safety) and informing people with clear signage and a notice? Are you avoiding excessive monitoring where it is not justified?
Protection issue (safeguard): CCTV footage must be stored securely, with restricted access and retention limits. Footage should not be casually shared over messaging apps.
Example 4: Processing health information (including test results)
Privacy issue (use): Health data is highly sensitive. Privacy considerations include strict purpose limitation, controlled sharing, and ensuring disclosures are justified and transparent.
Protection issue (safeguard): Strong controls are required, including access restrictions and careful handling to prevent exposure.
If you want a Jamaica-specific example of sensitive information and legal obligations, PLMC also discusses health-related information in COVID-19 results are protected by the Data Protection Act.
Example 5: Sharing a customer list with a partner organisation
Privacy issue (use): Was the sharing disclosed to the individual? Is it compatible with the purpose the data was collected for? Do individuals have the ability to object or opt out where applicable?
Protection issue (safeguard): Do you have a written agreement that limits use, requires security controls, addresses breaches, and sets retention/deletion expectations? Do you do any vendor or partner due diligence?
A “spot the difference” table
Scenario | Privacy question to ask | Protection question to ask |
New online form collects TRN, DOB, address | Do we truly need all fields for this service, and did we explain why? | Are inputs encrypted in transit, stored securely, and access-controlled? |
HR uploads staff files to a shared drive | Who should have access, and have staff been informed of processing? | Are permissions locked down, monitored, and backed up? |
Customer service records calls | Did we notify callers and state the purpose? | Are recordings stored securely with retention limits? |
Incident happens (lost laptop) | Do we need to notify impacted people and regulators based on harm and obligations? | Was the device encrypted, and can we remotely wipe and investigate? |
Common misconceptions that create compliance gaps
“We are secure, so we are compliant”
A company can have strong cybersecurity and still fail privacy requirements if it:
collects excessive data “just in case”
uses information for new purposes without transparency
ignores access or deletion requests
Security reduces breach risk, but it does not automatically make processing fair or lawful.
“We have a privacy policy, so we are covered”
A policy on a website is not the same as an operational privacy programme. Regulators and customers care about what you actually do day to day: how staff handle requests, how vendors are governed, and whether controls are followed.
“Privacy is legal’s job, protection is IT’s job”
Privacy and protection split across teams, but accountability cannot. The practical solution is shared governance: clear roles, evidence of decisions, and consistent controls across departments.
How the two work together under Jamaica’s Data Protection Act
If you are building (or repairing) a programme, it helps to map your work into two streams that join under accountability.
Build the privacy foundation (the “should we” layer)
Focus on defining, documenting, and communicating lawful and fair processing:
Know what personal data you collect, and why
Identify and document your purpose(s)
Create or update privacy notices so people are informed
Put a process in place to handle individual rights requests
Train staff so they understand expectations and limits
For deeper context on rights and principles, see PLMC’s guide: Data Privacy in Jamaica: Key Principles and Rights.
Implement protection controls (the “how do we keep it safe” layer)
This is where operational and technical safeguards reduce the likelihood and impact of incidents:
Access control (least privilege, joiner-mover-leaver discipline)
Secure configuration and patching, especially for internet-facing systems
Encryption, backups, and recovery testing
Retention and secure disposal
Vendor governance and contracts
Incident response planning and simulations
A practical way to align both privacy and protection work is to use a recognised structure such as the NIST Privacy Framework, alongside your security framework of choice. The key is making sure privacy requirements are implemented in operations, not only written down.
What “good” looks like: evidence you can show
In real audits, investigations, or customer due diligence, you may be asked to demonstrate not just what you believe, but what you can prove. A balanced approach is to maintain evidence from both sides.
Evidence area | Privacy-aligned artefacts | Protection-aligned artefacts |
Transparency | Current privacy notices, internal staff notices, purpose statements | Records showing notices are linked in apps, forms, and onboarding workflows |
Data inventory | Processing register, data mapping outputs, system list with purposes | Data flow diagrams, asset inventory, access lists, security classifications |
Rights handling | Request intake process, timelines, decision logs | Identity verification steps, secure delivery method, access logging |
Vendor management | Due diligence questions tied to processing purpose | Security requirements, contractual clauses, SOC/ISO evidence where applicable |
Breach readiness | Internal escalation rules, communications playbooks | Incident response plan, tabletop exercises, detection and containment logs |
PLMC has a useful operational companion piece if you want to turn this into a working plan: Privacy and Data Protection: A Practical Checklist.
A quick self-check: are you dealing with a privacy problem, a protection problem, or both?
Use these signals to triage issues quickly in meetings.
It is mainly a privacy issue when the concern is about purpose, fairness, or transparency, for example “We want to reuse customer data for a new product” or “We never told staff we were collecting this information”.
It is mainly a protection issue when the concern is about exposure, unauthorised access, or weak controls, for example “Too many people can see payroll files” or “We cannot tell who downloaded the report”.
It is both when a change introduces new use and new risk, for example launching a new app feature, onboarding a new vendor, or starting cross-border processing.

Why this distinction matters for Jamaican organisations right now
In 2026, many local organisations are moving from “awareness” to “operational proof” on compliance. The fastest route to progress is making sure your programme covers both halves:
Privacy decisions are documented and communicated (so processing is justified).
Protection controls are implemented and tested (so information is actually safeguarded).
If you need a time-structured implementation approach, PLMC’s Data Protection Jamaica: Compliance Roadmap for 2026 is designed to help teams sequence deliverables and build evidence.
Turning understanding into action
Once you can clearly explain the difference between data privacy and data protection, your next step is to align people, process, and technology around it. That usually means:
Assigning ownership across legal/compliance, IT/security, HR, and operations
Agreeing on what “minimum necessary data” looks like in each workflow
Updating notices and internal guidance so staff can act consistently
Implementing and testing controls, not just writing policies
If your organisation would benefit from help scoping gaps, documenting decisions, training teams, or implementing a data protection programme aligned to Jamaica’s Data Protection Act, Privacy & Legal Management Consultants Ltd. (PLMC) provides data protection implementation, training sessions, risk assessment support, and consultations. You can explore PLMC’s resources and services at privacymgmt.org.
