
Data Security and Data Privacy: How to Separate Duties

Many organisations treat “privacy” and “security” as the same workstream until something goes wrong: a vendor is onboarded without the right clauses, a shared drive is exposed, or a staff member answers a rights request from the wrong inbox. In Jamaica, where the Data Protection Act requires practical accountability, a simple way to reduce risk is to separate duties between data security and data privacy, while keeping both teams aligned.
This article explains what each discipline is responsible for, where they overlap, and how to assign clear ownership across IT, Legal, HR, Compliance, and business units without creating gaps.
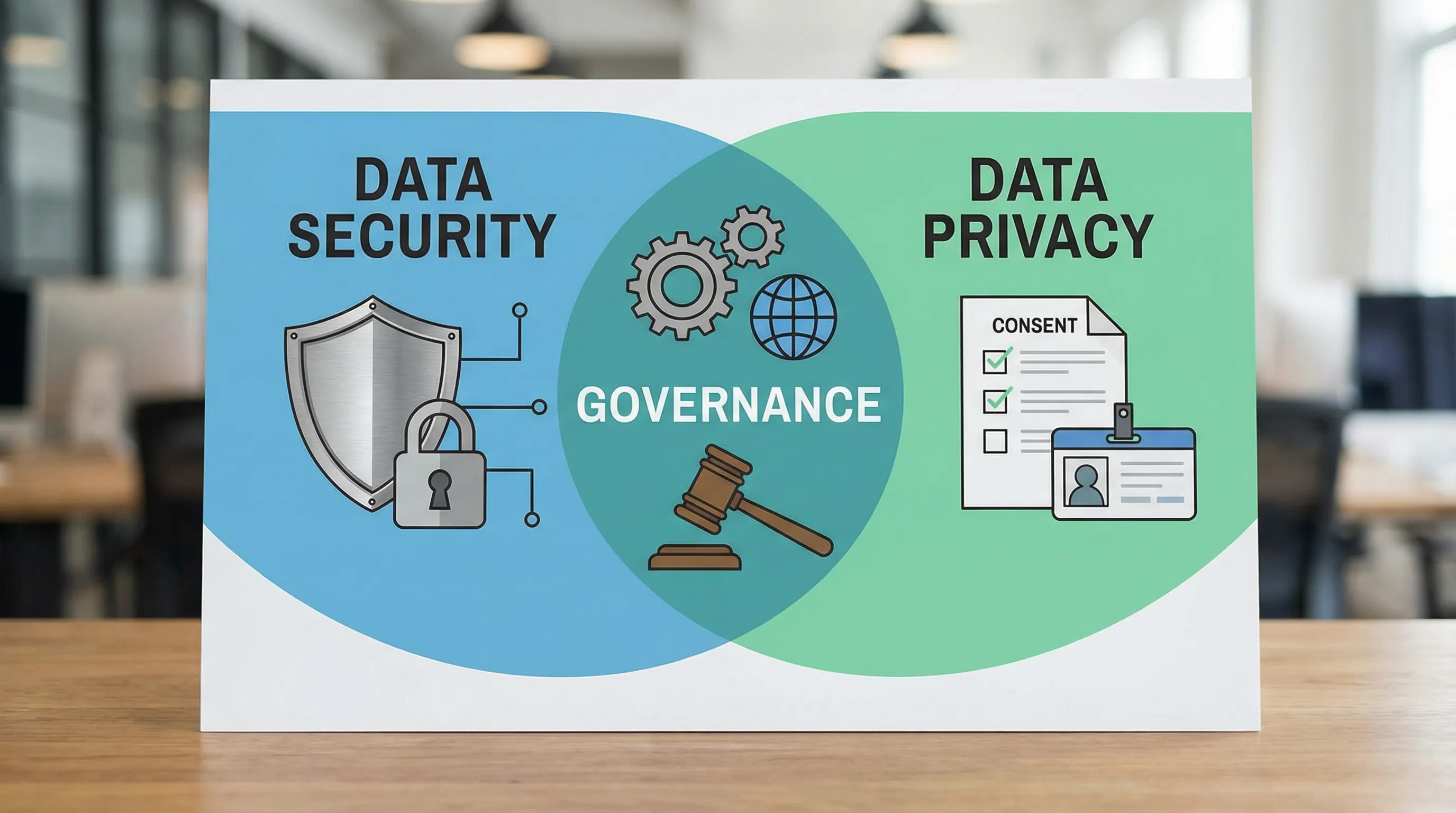
Data security vs data privacy (the shortest useful definition)
Data security is about protecting data from unauthorised access, alteration, loss, or disruption. It focuses on confidentiality, integrity, and availability.
Data privacy is about using personal data in a lawful, fair, and transparent way, for specific purposes, and respecting people’s rights. It focuses on appropriate processing and governance.
A helpful way to remember the difference:
Security asks: “How do we protect data?”
Privacy asks: “Should we collect this, can we use it this way, and what do we owe the individual?”
In practice, you need both. Strong security cannot “legalise” an unfair or excessive use of personal data, and a good privacy notice cannot compensate for weak security controls.
Why separating duties matters (and what “separation” actually means)
Separating duties does not mean building silos. It means assigning decision rights and accountability so that:
No single person can approve risky processing, implement it, and mark it compliant.
Privacy decisions (purpose, lawful basis, retention, sharing) are reviewed independently from delivery pressures.
Security decisions (controls, access, monitoring, incident response) are reviewed independently from the team that runs the system day to day.
This mirrors long-standing governance principles used in finance, audits, and cyber risk management. It also supports evidence-based compliance, which is increasingly important as Jamaican organisations mature their privacy programmes.
What belongs to data security (typical responsibilities)
Data security is usually led by IT, a Security Officer, or an outsourced security provider. The scope is broader than personal data, it covers company data of all types.
Security responsibilities commonly include:
Identity and access management (accounts, MFA, role-based access)
Secure configuration, patching, vulnerability management
Network security and endpoint protection
Encryption and key management decisions (implementation and operations)
Logging, monitoring, alerting, and security testing
Backup, disaster recovery, and resilience
Incident response operations (containment, eradication, recovery)
Framework references many organisations use include NIST Cybersecurity Framework (CSF) and ISO/IEC 27001 (information security management).
What belongs to data privacy (typical responsibilities)
Data privacy is usually led by a Data Protection Officer (DPO) or privacy lead, supported by Legal, Compliance, HR, and business owners.
Privacy responsibilities commonly include:
Data mapping and records of processing (what data, where it goes, why)
Privacy notices and transparency obligations
Defining purposes, lawful bases, and rules for sensitive data
Data minimisation and retention rules (including disposal requirements)
Rights request handling (access, correction, objection, deletion where applicable)
Vendor and data sharing governance from a privacy standpoint (due diligence, contract clauses)
Privacy impact assessments (often called DPIAs) for higher-risk processing
Privacy training and awareness
If you want a Jamaica-focused foundation before you redesign duties, see PLMC’s guides on data privacy principles and rights and the practical privacy checklist.
The overlap: where most confusion (and risk) happens
The danger zone is the overlap where privacy needs security controls, and security decisions affect privacy outcomes.
Common overlap areas include:
Access control (security implements it, privacy defines “who should access what”)
Data retention (privacy sets rules, security ensures deletion is actually enforced across systems and backups where feasible)
Vendor management (privacy focuses on terms and purpose limitations, security focuses on technical safeguards)
Breach response (security investigates and contains, privacy assesses reporting obligations and communications)
When these are not separated properly, organisations often end up with “checkbox compliance” (policies without controls) or “security-only compliance” (controls without lawful processing discipline).
A practical separation of duties model (who owns what)
The goal is clarity. The table below shows a pragmatic way to separate duties without slowing the business.
Activity | Data privacy owner (accountable) | Data security owner (accountable) | Notes (how they work together) |
Approve new use of personal data (purpose, lawful basis, minimisation) | Privacy Lead / DPO, Legal/Compliance | Consulted | Security input helps assess risk, but privacy owns the “should we” decision. |
Define access rules for personal data | Privacy Lead + Business Owner | IT/Security | Privacy defines roles and least privilege intent, security enforces via RBAC, MFA, reviews. |
Vendor onboarding (personal data processing) | Privacy Lead + Procurement/Legal | Security | Privacy reviews processing terms, security reviews technical controls and assurance evidence. |
Retention schedule and disposal rules | Privacy Lead + Records/Business Owner | IT/Security | Privacy sets “how long,” security ensures systems can purge and restrict. |
Security testing and monitoring | Consulted | Security | Privacy is consulted when tests involve production personal data and when findings affect privacy risk. |
Incident response (technical) | Consulted | Security | Security leads containment and forensics. |
Incident response (legal/privacy) | Privacy Lead + Legal/Compliance | Consulted | Privacy leads assessment of impact to individuals, notifications, and remediation obligations. |
Training | Privacy Lead (privacy training) | Security (security training) | Coordinate content so staff hear one message, not competing rules. |
If you are a smaller organisation, one person may hold multiple hats, but you can still separate duties by using independent review. For example, the system administrator should not be the only approver for access to sensitive HR files.
How to implement separation of duties in 6 steps
1) Write down your “minimum viable” governance roles
Start with roles you already have, not ideal future hires. Most Jamaican organisations can map ownership across:
Business owner (Head of Department or process owner)
IT/Security lead (internal or outsourced)
Privacy lead (DPO function, Legal, Compliance, or a designated manager)
HR (employee data)
Procurement (vendors)
Make the role definitions short and operational. The outcome should be: “If X happens, who decides?”
2) Create one workflow for new processing, not five informal approvals
A common failure pattern is a project team launching a new tool, then asking privacy to “sign off” at the end. Separation of duties works best when privacy and security are both embedded early.
At a minimum, require a documented checkpoint before go-live:
Privacy checkpoint: purpose, lawful basis, notice updates, retention, vendor terms, rights handling impact
Security checkpoint: access model, configuration baseline, encryption approach, logging, backup, incident response fit
This does not need to be bureaucratic. A one-page intake form plus a short review meeting can prevent months of remediation.
3) Split “can do” from “should do” decisions
This is where many teams accidentally collapse privacy into security.
Security answers: “Can we restrict access, monitor, and protect the data in this system?”
Privacy answers: “Should we collect this data at all, and can we use it for this purpose?”
You want independent challenge. For example, marketing may be able to store national ID numbers in a CRM, but privacy should challenge whether it is necessary.
4) Separate administration from approval for access to sensitive data
For high-risk datasets (HR, payroll, health information, financial profiles, student records), implement a two-person rule:
One person administers accounts and groups (IT)
A different role approves access based on job need (business owner or privacy lead, depending on context)
Log approvals so you can evidence why access was granted.
5) Build an incident workflow that assigns privacy and security tasks clearly
During an incident, speed matters, but so does coordination. Your playbook should separate duties like this:
Security: detect, contain, preserve evidence, identify affected systems and data types
Privacy/Legal: assess risk to individuals, decide notification steps, manage regulator and stakeholder communications, document decisions
To make this real, run a tabletop exercise at least annually that includes both tracks. PLMC’s 2026 compliance roadmap includes practical assurance activities like simulations and metrics.
6) Measure both programmes with different metrics
If privacy and security share one set of metrics, one usually dominates.
Security metrics: patch timelines, MFA coverage, critical vulnerabilities, backup restore testing, monitoring coverage
Privacy metrics: rights request turnaround, completion of privacy reviews for new projects, vendor contract coverage, training completion by role
These metrics help demonstrate accountability, and they keep each function focused on its outcomes.
Example: separating duties in a real-world scenario
Consider a mid-sized Jamaican company implementing a new cloud HR system.
Security might focus on MFA, role-based access, encryption, and logging. Privacy should focus on whether the system collects only what is needed, whether retention aligns to policy, how employee notices are updated, whether the vendor contract limits processing, and how employee access or correction requests will be handled.
If the same person “approves” everything, the project can move quickly, but risk hides. Separation of duties introduces a healthy pause: privacy challenges data fields and retention, security challenges configuration and monitoring, and the business owner confirms the operational need.
Common mistakes to avoid
One of the biggest mistakes is assuming the DPO or privacy lead “owns security.” Under most operating models, they do not. They may require appropriate security, but they are not responsible for configuring firewalls or deploying endpoint tools.
Another common mistake is treating security as purely technical. Access decisions, retention enforcement, and vendor risk decisions have governance components that require business and privacy input.
Finally, avoid publishing policies that your systems cannot support. If your retention policy promises deletion after a short period, but backups and archives keep data indefinitely, you have a mismatch that will surface during audits or incidents.

Frequently Asked Questions
Is data privacy the same as confidentiality? No. Confidentiality is a security concept (preventing unauthorised disclosure). Privacy is broader and includes lawful purpose, transparency, minimisation, retention, and individuals’ rights.
Who should own breach notification decisions in Jamaica? Typically Legal/Compliance and the privacy lead should own notification decisions, informed by security’s investigation findings. Security should own containment and technical remediation.
Can one person be both the privacy and security owner in a small organisation? Sometimes, yes, but you should still separate duties through independent review. For example, require a second approver for access to sensitive data or vendor onboarding.
What is the simplest way to start separating duties? Start with a RACI-style table for three processes: new projects, vendor onboarding, and incident response. Then implement a two-person approval rule for access to sensitive datasets.
How does separation of duties help with the Data Protection Act? It supports accountability by showing who is responsible for lawful processing decisions (privacy) and who is responsible for protective controls (security), with evidence of review and oversight.
Need help designing a clean privacy and security operating model?
Privacy & Legal Management Consultants Ltd. (PLMC) supports organisations in Jamaica with data protection implementation, cyber security services, training, and GRC integration. If you want a practical separation-of-duties model tailored to your size and sector, you can request a consultation via privacymgmt.org and align your privacy governance with real security controls.
