
Data Privacy Data Protection: A Simple Guide for SMEs

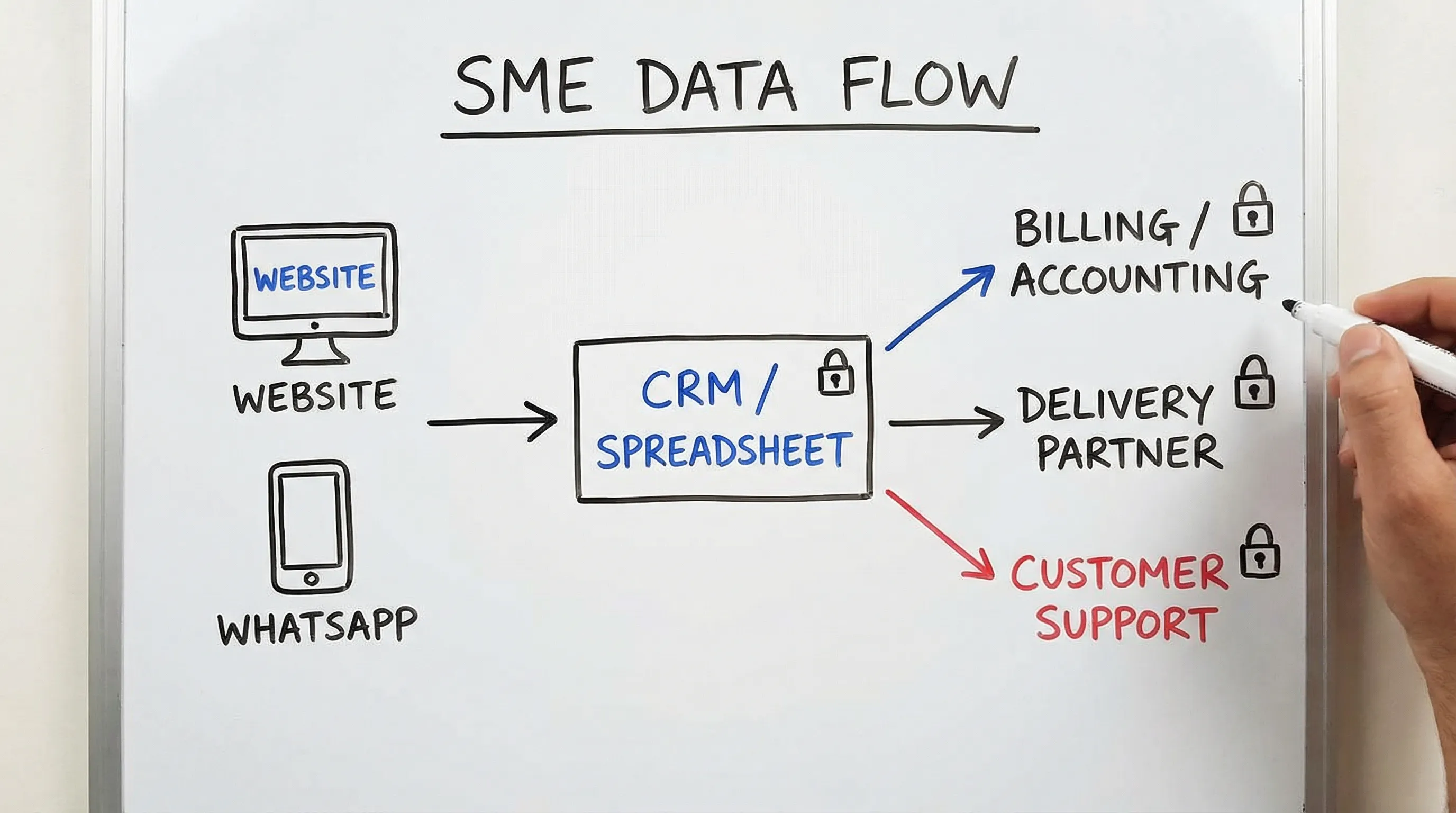
Most SMEs in Jamaica do not set out to “process personal data”. You simply take customer orders, pay staff, send invoices, manage deliveries, run loyalty programmes, or answer WhatsApp enquiries. But the moment you record a name, phone number, TRN, address, IP address, camera footage, or employee medical note, you are handling personal data and that creates privacy obligations.
This guide breaks down data privacy and data protection in plain language, with practical steps you can implement without a large legal or IT team.
Data privacy vs data protection (simple definitions)
People often use these terms interchangeably, but for an SME it helps to separate them:
Data privacy is about rules and trust. It covers how and why you collect personal information, what you tell people about it, and whether you respect their choices and rights.
Data protection is about safeguards. It covers the practical controls that keep personal information secure, accurate, and only available to people who should have it.
A useful shortcut is:
If the question is “Should we be collecting or sharing this at all?” you are in privacy.
If the question is “How do we keep it safe and prevent leaks?” you are in protection.
Why data privacy and data protection matter for Jamaican SMEs
SMEs typically feel privacy compliance is “for big companies”, until one of these happens:
A customer complains that you used their number for marketing without consent. An employee requests a copy of their personnel file. A laptop goes missing. A staff member clicks a phishing link. A vendor mishandles your customer list. A new corporate client asks you to complete a privacy questionnaire before onboarding.
Strong privacy and protection practices reduce three very real risks:
Commercial risk: Many contracts now require proof of security controls, vendor oversight, and breach readiness.
Operational risk: Incidents cause downtime, reputational damage, and expensive clean-up, even if no regulator contacts you.
Legal and governance risk: Jamaica’s Data Protection Act sets expectations around lawful processing, security safeguards, and accountability. If you want a deeper legal breakdown, see PLMC’s guide: Jamaica Data Protection Act Explained for Businesses.
The 5 questions every SME should answer first
Before you write a policy or buy a tool, get clarity on these basics. They drive everything else.
1) What personal data do we have?
Think beyond customer contact details. SMEs commonly hold:
Customer data (names, phone numbers, addresses, emails, delivery notes, complaint logs)
Employee data (TRN, NIS details, bank details, performance notes)
CCTV footage
Website and app data (analytics identifiers, contact forms)
Supplier and contractor data
2) Where is it stored?
Usually it is spread across:
Email inboxes, filing cabinets, WhatsApp chats, spreadsheets, POS systems, accounting software, HR folders, cloud drives, and personal devices.
3) Who can access it?
“Everyone has the password” is common in small teams and is one of the easiest problems to fix.
4) Why do we need it?
If you cannot clearly explain the purpose, you are likely collecting too much or keeping it too long.
5) Who do we share it with?
Think couriers, payment providers, payroll processors, cloud platforms, marketing agencies, IT support, and outsourced call centres. Vendor handling is one of the fastest-growing risk areas for SMEs.
A practical “starter map” you can create in one hour
You do not need an enterprise data mapping exercise to start. Create a one-page starter map with three columns:
System or location, What personal data is there, Who uses it.
For example:
System or location | Example personal data | Who uses it |
WhatsApp Business | Names, numbers, addresses, order details | Sales, customer service |
Accounting software | Names, invoice details, sometimes TRN | Accounts |
CCTV DVR | Footage of customers and staff | Manager, security contractor |
Staff files (digital or paper) | TRN, bank info, NIS, disciplinary notes | HR, management |
Once this exists, most decisions become easier: you can identify your highest-risk locations (shared spreadsheets, personal email use, unlocked filing cabinets) and fix them first.
The SME privacy and protection basics that actually move the needle
There are many “privacy programme” checklists, but SMEs need actions that reduce risk quickly and create evidence of responsible governance.
Collect less, and your compliance gets easier
Data minimisation is not just a legal principle, it is a cost-saving strategy. Every extra field you collect is another thing you must secure, retain, and potentially disclose later.
Practical examples:
If you run a delivery business, you may need an address and phone number, but you probably do not need a customer’s date of birth. If you are collecting TRNs, be clear about the legal or operational reason and ensure you are protecting that field properly.
Tell people what you are doing (in normal language)
Most SMEs do not need complex privacy wording. They need a simple notice that answers:
What you collect, why you collect it, who you share it with, how long you keep it, and how someone can contact you about their information.
Where to place it:
Your website contact forms, job application pages, customer intake forms, and any place you request sensitive information.
Control access with role-based decisions, not “trust”
Small teams rely on trust, but privacy requires boundaries. Start with:
Separate user accounts (no shared logins where possible), strong passwords, and multi-factor authentication on email and cloud storage. Remove access promptly when someone changes role or leaves.
For security control guidance, the NIST Cybersecurity Framework is a widely used reference, even for smaller organisations.
Secure the everyday tools SMEs actually use
For many Jamaican SMEs, your biggest risk surface is not a data centre. It is:
Email, cloud drives, mobile devices, and messaging apps.
Your priority controls should include:
Device screen locks, encrypted storage where available, up-to-date software, and phishing awareness. If you use Wi‑Fi at the office, secure the router, change default credentials, and separate staff and guest networks.
If you handle web applications, keep an eye on common web risks described by OWASP. You do not have to implement everything at once, but you should know what “normal” attacks look like.
Manage vendors like they are part of your business
If a third party can access your customer list, payroll file, CCTV system, or email platform, you need a minimum standard for:
Contracts, confidentiality, security safeguards, and how they notify you if something goes wrong.
This is especially important when data may be stored or accessed outside Jamaica (for example, cloud hosting or overseas support teams). You do not need to ban international services, but you do need to understand the risk and document the decision.
Keep data only as long as you need it
One of the simplest risk reducers is deleting what you no longer need. A retention approach can start small:
Define basic timeframes for customer inquiries, inactive customer accounts, employee records, and CCTV footage. Then assign an owner who checks quarterly that deletion actually happens.
Be ready for two requests: “Show me my data” and “Something went wrong”
Even SMEs should be able to respond if:
A customer asks what data you have about them, or requests a correction, or an employee requests access to their file.
Separately, you need a basic incident plan. Not a binder. A one-page playbook with:
Who to call internally, how to contain the issue, how to preserve evidence, and how to decide whether notifications are needed.
The minimum “privacy pack” an SME should keep
Think of this as your proof that you are acting responsibly. It also speeds up customer questionnaires and procurement checks.
Document or record | What it does | SME-friendly version |
Starter data map | Shows what you have and where | One page, updated quarterly |
Privacy notice | Builds transparency and trust | Plain language, one page |
Access list | Shows who has access to what | Simple table, reviewed monthly |
Vendor list | Identifies third-party risk | List of vendors with what they access |
Retention rules | Reduces “keep everything forever” | Short rules per data type |
Incident log | Creates evidence and lessons learned | Date, what happened, actions taken |
Training record | Shows awareness efforts | Attendance list and topics |
If you want a more detailed operational checklist, use it as a next step rather than your starting point: Privacy and Data Protection: A Practical Checklist.
Common SME privacy mistakes (and quick fixes)
Mistake 1: Using personal WhatsApp and personal email for business records
This creates uncontrolled copies of personal data and makes it hard to respond to requests or incidents.
Quick fix: Move to WhatsApp Business and a dedicated business email domain, define what must be transferred into your main system (CRM, order sheet, ticketing tool), and set rules for deleting old chats.
Mistake 2: Shared passwords and “everyone is admin”
Shared access kills accountability and makes incident response harder.
Quick fix: Separate accounts, least-privilege access, and MFA on your highest-risk systems first (email, cloud drive, accounting).
Mistake 3: Collecting sensitive data without safeguards
Health details, ID numbers, TRNs, and employee information need extra care.
Quick fix: Restrict access, encrypt where possible, and stop collecting fields that are not essential.
Mistake 4: No vendor oversight
Many breaches and privacy issues start with a supplier.
Quick fix: Keep a vendor register and require basic assurances (confidentiality, security measures, incident notification timelines).
A realistic implementation plan for a small team
If you only do one thing this week, create your starter data map and lock down your email and cloud storage.
Over the next 30 days, aim to:
Write a plain-language privacy notice, build your vendor list, decide simple retention timeframes, and run a short staff awareness session focused on phishing and handling customer information.
If you want a structured, time-bound approach that aligns with 2026 planning, PLMC has a roadmap you can adapt: Data Protection Jamaica: Compliance Roadmap for 2026.
When to bring in help
You can start small internally, but consider professional support if you:
Are handling sensitive data at scale (health, financial, children’s information), experienced a security incident, are onboarding enterprise clients, are expanding internationally, or need to build a defensible compliance programme with evidence.
PLMC supports organisations in Jamaica with data protection implementation, privacy awareness training, risk assessments, cyber security services, and broader GRC integration. If you are not sure where to begin, a focused conversation can help you prioritise.
Frequently Asked Questions
What is personal data for a small business in Jamaica? Personal data is information that can identify a person directly or indirectly, such as a name, phone number, address, email, employee file, CCTV footage, or an online identifier tied to a person.
What is the difference between data privacy and data protection? Data privacy is about lawful, fair, and transparent use of personal data (the “why” and “rules”). Data protection is about safeguards like access control, encryption, and secure processes (the “how”).
Do SMEs really need a privacy notice? Yes. Even a simple notice builds trust and helps meet transparency expectations. It should explain what you collect, why, who you share it with, and how people can contact you.
What are the quickest security wins for protecting customer data? Enable multi-factor authentication on email and cloud tools, remove shared logins, restrict access by role, update devices, and train staff to spot phishing.
How long should we keep customer and employee records? Keep records only as long as there is a clear business or legal reason. Start with basic rules by category (accounts, HR, CCTV) and review them quarterly.
What should we do if we suspect a data breach? Contain it quickly (secure accounts, isolate devices), preserve evidence, document what happened, and get advice on notification obligations and communications. Having a one-page incident playbook in advance makes a major difference.
Get practical support for your SME privacy programme
If you want to move from “we should do something about privacy” to a clear, prioritised plan, PLMC can help you build a right-sized programme that fits your operations, budget, and risk.
Explore resources at Privacy & Legal Management Consultants Ltd. or review your starting point with PLMC’s detailed guidance on the Jamaica Data Protection Act.
