
Data Privacy and Governance: Build Accountability That Works

Accountability is the difference between a privacy programme that looks good on paper and one that actually survives audits, customer complaints, vendor incidents, and board scrutiny. In Jamaica, where the Data Protection Act has pushed organisations to formalise how they handle personal data, “we have a policy” is no longer the same as “we are in control”. Data privacy and governance is about building a repeatable operating model: clear decision rights, assigned owners, evidence you can produce quickly, and metrics that show privacy is being managed like any other business risk.
This article explains what “accountability that works” looks like in practice, and how to build it into day to day operations without turning privacy into a paperwork exercise.
What accountability really means in data privacy and governance
Accountability is often misunderstood as a single role (for example, “the DPO handles privacy”) or a set of documents. In reality, accountability is a governance outcome:
The organisation can explain what personal data it uses, why it uses it, where it flows, and who can access it.
The organisation can demonstrate that controls exist and are working (training completion, access reviews, vendor due diligence, retention enforcement, incident handling).
The organisation can prove ownership (who approves new processing, who accepts risk, who remediates gaps, who reports to leadership).
Regulators and customers do not experience your privacy policy. They experience how you respond when something goes wrong: a rights request, an incident, a vendor failure, or an employee mistake.
For reference, accountability is also a widely recognised expectation in mature privacy regimes and guidance. The UK Information Commissioner’s Office maintains detailed accountability and governance guidance that is helpful even outside the UK because it focuses on operational proof, not just policy statements: ICO accountability and governance guidance.
Why privacy governance fails (even in well intentioned organisations)
Most accountability failures come down to governance gaps, not bad intentions. Common patterns we see across organisations include:
“Privacy lives in one department”
Privacy touches HR, marketing, customer service, IT, procurement, legal, compliance, and frontline operations. If only one team “owns” it, the organisation becomes dependent on informal favours and last minute reviews.
Decisions are not linked to risk ownership
Teams may identify risks (for example, storing ID copies too long, using personal email for work files, sharing spreadsheets externally), but nobody is empowered to accept the risk formally or fund remediation.
Evidence is scattered, stale, or missing
Even where good work is happening, organisations struggle to evidence it. Training logs are incomplete, vendor assessments are inconsistent, and data inventories are outdated after system changes.
Security and privacy are treated as separate worlds
Cyber security controls are essential, but privacy governance also covers legality, purpose limitation, minimisation, retention, fairness, and individual rights. When teams only think “security”, they miss key privacy risks.
The core building blocks of accountability that works
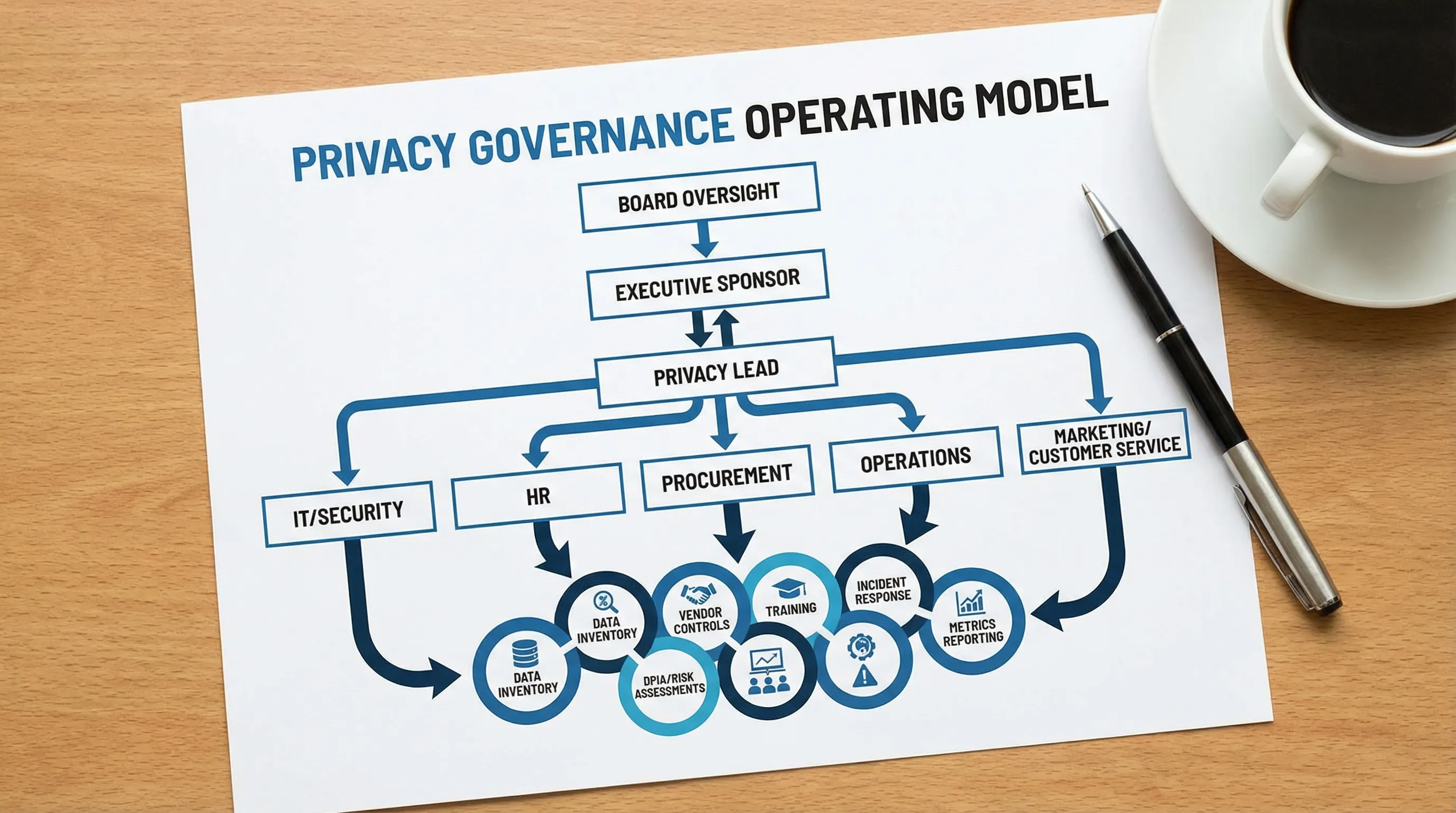
Think of privacy accountability as an operating model, similar to financial controls or AML governance. The goal is consistency and proof.
1) Clear roles, with clear decision rights
Define who does what, who approves what, and who is accountable when trade offs appear (for example, speed to launch versus stronger consent controls).
A practical approach is to assign:
Executive sponsor (often C-suite): ensures priority, budget, and cross functional support.
Privacy lead (could be DPO or privacy officer where applicable): coordinates the programme, sets standards, monitors performance.
Data owners (business leaders): accountable for data use in their functions.
IT and security: implements technical controls, monitors threats, supports incident response.
HR and learning: embeds training and employee lifecycle controls.
Procurement and vendor management: ensures supplier due diligence and contracts.
Internal audit or assurance (where present): independently tests effectiveness.
You do not need a large team. You need named owners, a cadence, and the authority to make decisions.
2) A governance forum that meets and makes decisions
Accountability improves when privacy has a regular forum that is empowered to:
approve high risk processing and projects
prioritise remediation items
review incidents and lessons learned
track metrics and overdue actions
Depending on your size, this can be a privacy committee or a standing agenda item in an existing governance body (for example, risk committee, IT steering committee, compliance committee). The important part is that privacy is not handled only by ad hoc emails.
3) Standard artefacts that are owned, versioned, and reviewed
Privacy governance becomes manageable when it is built around a small set of “always on” artefacts. These artefacts should have owners and review dates, and they should generate evidence.
Accountability artefact | What it’s for | Typical owner | What “good evidence” looks like |
Data inventory and data flow map | Knowing what personal data exists, where it goes, and why | Privacy lead with data owners | Updated entries after system or process changes, not just annually |
Privacy risk assessment / DPIA process | Identifying and treating privacy risks before go live | Privacy lead with project owners | Completed assessments for new systems, marketing campaigns, and vendor changes |
Privacy notice(s) and internal standards | Transparency and consistent handling rules | Privacy lead, legal/compliance | Version history, approval records, alignment with actual practices |
Retention and disposal rules | Preventing “keep everything forever” behaviour | Data owners with records management | Retention schedule, disposal logs, periodic checks |
Vendor due diligence and contract controls | Managing processor and supplier privacy risk | Procurement/vendor management | Completed assessments, signed data clauses, ongoing monitoring |
Rights request workflow | Responding consistently to access, correction, objection, deletion where applicable | Privacy lead with customer service/HR | Intake log, triage steps, response templates, evidence of deadlines |
Incident response playbook (privacy plus security) | Faster, consistent response to breaches and near misses | IT/security with privacy lead | Tabletop exercise records, incident logs, post incident reviews |
Training and awareness programme | Reducing human error, building culture | HR/learning with privacy lead | Role based training completion and refresher cadence |
This structure keeps governance focused: fewer documents, more operational proof.
Metrics that prove accountability (and help leadership invest)
Boards and executives respond to trends and indicators. Metrics also reveal whether privacy is improving or simply producing documents.
Good privacy governance metrics are:
actionable (you can do something with them)
traceable (they come from logs, systems, or auditable records)
linked to risk (they measure exposure, not just activity)
Metric | What it tells you | Common data source |
% of systems/processes covered by a current data inventory | Whether the organisation knows its footprint | Data inventory register, IT asset list |
# of high risk initiatives reviewed before launch | Whether privacy is embedded in change | Project intake records, DPIA log |
Rights request cycle time and backlog | Whether individual rights can be handled under pressure | Ticketing system, intake register |
Vendor due diligence completion rate for critical suppliers | Whether supplier risk is being managed consistently | Procurement records, contract repository |
Incidents and near misses by cause | Whether you are learning and reducing repeat events | Incident register, helpdesk, SOC logs |
Training completion by role | Whether high risk roles are covered | LMS reports, HR records |
Avoid vanity metrics (for example, “number of policies”). Policies matter, but they do not prove control.
If you want a structured way to align metrics to a recognised framework, the NIST Privacy Framework is a useful reference for building privacy outcomes that can be measured and reported alongside cyber and enterprise risk.
Integrating privacy governance into wider GRC (so it actually sticks)
Privacy works best when it is not treated as a separate programme that competes with everything else.
Align privacy risk with enterprise risk language
If your organisation already tracks risk (operational, financial, cyber, compliance), map privacy risks into the same approach:
define impact and likelihood consistently
use the same risk acceptance and escalation thresholds
link remediation to owners, dates, and budget
This makes privacy comparable, which makes it governable.
Use “privacy by design” as a change control standard
Instead of relying on last minute reviews, build privacy requirements into existing processes:
project intake and approval
software procurement
vendor onboarding
marketing campaign sign off
HR onboarding and offboarding
That is what accountability looks like in practice: privacy becomes part of how work gets approved.
Connect privacy and cyber security without merging them
Your cyber security programme should feed privacy governance (for example, access controls, monitoring, incident response). At the same time, privacy governance must cover non security obligations (for example, transparency, minimisation, retention, lawful basis documentation).
A practical bridge is to align controls to standards that recognise both domains. ISO/IEC 27701 extends ISO/IEC 27001 into privacy information management and is often used to formalise privacy governance within an information security management system: ISO/IEC 27701 overview.
Vendor accountability: where many programmes are exposed
In many organisations, the biggest privacy risk sits outside the organisation’s walls: hosted software providers, payroll services, marketing platforms, and outsourced processing.
To make vendor governance work, focus on consistency:
classify suppliers by risk (for example, access to ID data, financial data, health data, children’s data)
require minimum controls and contract clauses before onboarding
keep vendor assessments reusable (do not restart from scratch each year)
create an offboarding checklist (data return, deletion confirmation, access removal)
If you can answer, quickly and confidently, “Which vendors process our personal data and which of them are highest risk?” you are already ahead of many organisations.
Building an “accountability pack” you can produce on demand
One of the most useful ways to test privacy governance is to imagine you have 48 hours to respond to a regulator query, a major client questionnaire, or a board request.
An accountability pack is a curated set of evidence that you can pull together quickly, typically including:
a current data inventory summary
your governance structure (roles and committee terms of reference)
risk assessment outputs for recent high risk projects
vendor risk overview for critical suppliers
incident response process and exercise results
training programme coverage and completion
a small set of metrics and trends
This is where many programmes either succeed or collapse. A well run programme can produce evidence with confidence because it is generated by operations, not assembled at the last minute.
Getting started: a practical approach for Jamaican organisations
If your organisation is still maturing its programme, the fastest wins usually come from tightening accountability mechanisms, not writing more policies.
Focus on:
naming owners for the key artefacts and processes (inventory, risks, vendors, rights, incidents)
setting a monthly governance cadence with decision rights
building a minimal evidence trail (logs, approvals, version control)
training by role, especially teams that handle high volumes of personal data
For teams that need a broader baseline of requirements, PLMC’s guides may help you align privacy operations to the Jamaican context:
When to bring in support
Some organisations can design a basic governance model internally, but struggle with consistency, evidence, and cross functional adoption. External support is often most valuable when you need to:
run an independent assessment of current privacy governance and gaps
build practical templates and workflows that match how your teams actually work
deliver targeted training (for leadership, frontline teams, IT/security, HR, procurement)
integrate privacy governance with broader GRC and cyber security activities
Privacy & Legal Management Consultants Ltd. supports organisations in Jamaica with data protection implementation, governance and compliance integration, training, and risk assessment tools. If you want to strengthen data privacy and governance with an accountability model that leadership can measure and defend, you can start with a conversation via the PLMC website.
