
Privacy Governance: Board Oversight and Operating Model

Privacy compliance rarely fails because an organisation lacks a policy. It fails because the policy has no owner, no budget, no decision rights, and no consistent reporting. That is a governance problem.
For Jamaican organisations working toward (or strengthening) compliance with the Data Protection Act, privacy governance is the mechanism that turns legal requirements into operational control. It clarifies who decides, who implements, who monitors, and what evidence is produced when management, auditors, business partners, or regulators ask, “Show me how you know personal data is handled properly.”
This article explains what effective privacy governance looks like at board level, then provides a practical operating model you can adapt to your size and risk profile.
What “privacy governance” actually means (beyond policies)
Privacy governance is the set of structures and routines that make privacy management repeatable:
Oversight (board and executive accountability, risk appetite, escalation)
Decision rights (who approves new processing, vendors, cross-border transfers, retention)
Operating rhythm (committees, reporting cadence, exception handling)
Assurance (testing, internal audit, metrics, evidence)
If you are aligning to recognised practices, the governance concept maps well to the “Identify-Govern-Protect-Control-Communicate” style lifecycle used in frameworks such as the NIST Privacy Framework (useful even outside the US because it is operational and risk-based).
In practical terms, privacy governance should ensure:
Personal data is inventoried and assigned to accountable owners.
High-risk processing triggers impact assessments and approvals.
Third parties are onboarded through vendor due diligence and contract controls.
Individuals’ rights requests and incidents are handled through tested workflows.
Management can prove compliance using evidence, not assurances.
Board oversight: what directors should own and what they should ask
Privacy is now a core enterprise risk topic, particularly where personal data is central to revenue (financial services, telecoms, tourism, e-commerce, health, HR-intensive operations). The board does not run the programme day to day, but it must ensure the programme is designed, resourced, and monitored.
Key board responsibilities in a privacy programme
1) Set risk appetite and tolerance for data use
Management needs clear boundaries. For example, what level of residual risk is acceptable for:
New customer analytics initiatives
Cross-border processing and cloud services
Outsourced call centres or marketing agencies
Biometric access controls or CCTV expansion
2) Assign executive accountability and ensure capability
A privacy lead (often a DPO-equivalent, privacy officer, or privacy counsel) can coordinate, but accountability for lawful processing sits with the organisation. The board should ensure there is an empowered executive sponsor (for example, COO, CFO, or General Counsel) and that privacy has access to information security, procurement, HR, and operations.
3) Approve the operating model and “gates” that stop bad decisions early
Boards should expect to see privacy built into:
Project intake and change management
Procurement and vendor onboarding
Incident response
Training and disciplinary processes
4) Demand management information that shows control effectiveness
A board pack that only reports training completion is not a privacy governance pack. Directors need a view of:
Where personal data sits and who owns it
What high-risk processing is happening
Whether controls are working (rights requests, retention, security events)
5) Ensure incident readiness and escalation
Privacy incidents are governance events. The board should approve escalation thresholds and require periodic exercises (tabletops) that test decision-making, not just technical containment.
Board-level questions that reveal whether governance is real
Board question | What a good answer looks like | Red flag answer |
“Which business units have the highest privacy risk this quarter, and why?” | Ranked risk view backed by processing inventory, incident trends, third-party exposure | “We have policies, so risk is low.” |
“How do we approve new uses of customer data?” | Defined intake process, risk tiering, impact assessments for high-risk items | “Teams decide case by case.” |
“Do we know where sensitive data is stored and who can access it?” | Systems list, access control model, periodic access reviews with evidence | “IT handles that.” |
“Which vendors process personal data, and what changed since last quarter?” | Vendor register, due diligence status, contract controls, issues and remediation | “Procurement has the contracts.” |
“How do we prove compliance?” | Evidence plan (records, logs, approvals, training records, test results) | “We have not been audited.” |
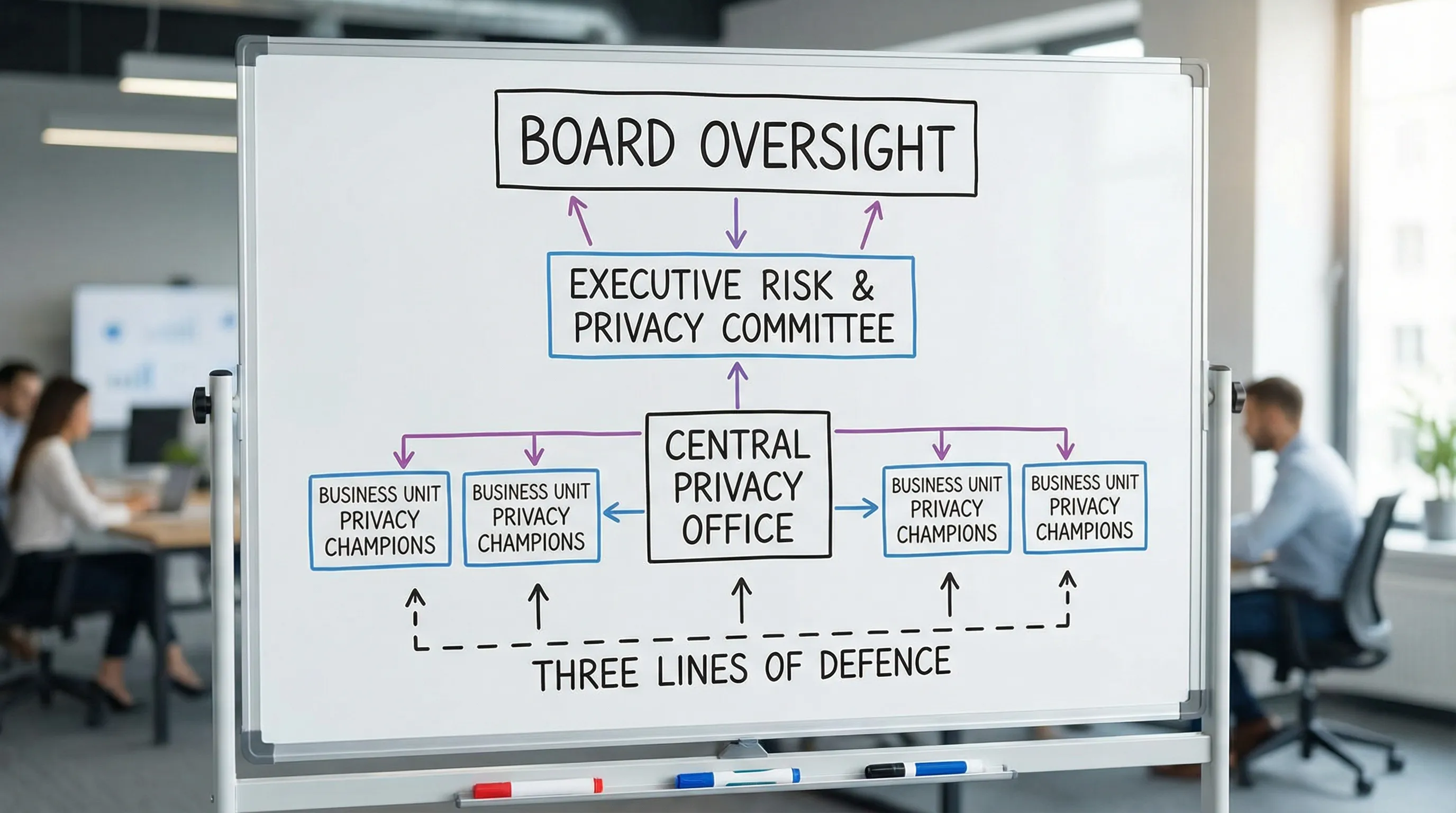
Choosing an operating model: centralised, federated, or hybrid
An operating model defines how privacy work is distributed across the organisation. There is no single best choice. The right model depends on size, complexity, and how frequently the organisation changes systems and processes.
Common models
Model | Best for | Strengths | Watch-outs |
Centralised (privacy team does most work) | Smaller organisations, simpler operations | Consistent decisions, easier to standardise | Can become a bottleneck, weak ownership in business units |
Federated (privacy champions in units) | Large or diversified groups | Scales well, strong local ownership | Inconsistent decisions unless standards and QA are strong |
Hybrid (central standards + local execution) | Most mid-size to large organisations | Balance of consistency and speed | Needs clear decision rights and reporting cadence |
A hybrid model is often the most realistic for Jamaican organisations with lean teams: a central privacy function sets standards, runs assurance, and supports high-risk initiatives, while business units own day-to-day compliance for their processes.
Define roles and decision rights (so privacy does not become “everyone and no one”)
A strong privacy governance design separates accountability (who is answerable) from responsibility (who does the work). The aim is not bureaucracy, it is repeatability.
Roles you should define explicitly
Board / Board committee: Approves risk appetite, receives reporting, oversees serious incidents.
Executive sponsor: Owns delivery, resolves conflicts between privacy, growth, and operations.
Privacy lead (DPO-equivalent): Provides expert advice, designs the programme, monitors compliance, coordinates impact assessments and rights workflows.
Information security: Implements technical and organisational measures, supports breach management.
Legal / Compliance: Aligns privacy with broader obligations (contracting, disputes, AML, sector regulations).
Procurement / Vendor management: Ensures due diligence, contract terms, and ongoing monitoring.
Business process owners: Own specific processing activities (customer onboarding, HR, marketing).
Data owners / system owners: Own systems, access control decisions, data quality, and retention implementation.
A practical RACI for common privacy activities
Activity | Board | Exec sponsor | Privacy lead | InfoSec | Procurement | Business owner |
Approve privacy strategy and annual plan | A | R | C | C | C | C |
Maintain records of processing (inventory) | I | A | R | C | C | R |
Risk-tiering new initiatives (low/med/high) | I | A | R | C | C | R |
Privacy impact assessments for high-risk processing | I | A | R | C | C | R |
Vendor due diligence for data processing vendors | I | A | C | C | R | C |
Rights request workflow (access, correction, deletion) | I | A | R | C | I | R |
Incident response and notification decisioning | I (escalation) | A | R | R | I | C |
Retention schedule implementation and evidence | I | A | C | C | I | R |
Legend: R = Responsible, A = Accountable, C = Consulted, I = Informed.
This matrix is intentionally simple. The goal is clarity, not paperwork.
Build the privacy governance “rhythm”: committees, reporting, and escalation
Good governance is not a once-a-year policy refresh. It is a management routine.
Committees that work (and what they should decide)
A common pattern is:
Executive Privacy Committee (monthly or quarterly): approves high-risk initiatives, reviews incidents, resolves resourcing conflicts.
Operational Privacy Working Group (bi-weekly or monthly): tracks deliverables, manages the inventory, monitors rights requests and vendor actions.
If your organisation already has a Risk Committee, you can embed privacy there, but only if privacy has agenda space and measurable reporting.
What should be in a board-ready privacy dashboard
Below is a sample structure. Targets and thresholds should be set to match your risk appetite and capacity.
Dashboard area | Example measures | Why it matters |
Data visibility | % of business units with up-to-date processing inventory; systems onboarded to data map | You cannot govern what you cannot see |
Rights readiness | # of rights requests received/closed; average days to close; backlog | Demonstrates operational capability and accountability |
Vendor risk | # of processors with completed due diligence; # of overdue contract updates; critical vendor issues | Third parties are a common failure point |
Security and incidents | # of privacy incidents; time to triage; lessons learned closed | Measures resilience, not just compliance |
Change governance | # of high-risk initiatives assessed; % completing impact assessment before go-live | Prevents “privacy after launch” |
Training effectiveness | role-based completion, but also phishing or scenario results where relevant | Tracks behavioural change, not only attendance |
Embed privacy into operations: the “control gates” that prevent rework
A mature privacy operating model is integrated into the business lifecycle. Instead of chasing teams after they deploy a new tool or launch a campaign, you create gates that route decisions to the right reviewers.
The most effective integration points
Project and change intake: A short privacy screening at the start of every change, with escalation to an impact assessment for high-risk work.
Procurement and contracting: Vendor onboarding should require a privacy and security review before purchase orders are raised or integrations begin.
Marketing and communications: Consent, transparency, and suppression list management must be treated as controlled processes, with approvals and evidence.
HR and workplace management: Joiner, mover, leaver processes should enforce least privilege access, retention rules, and secure disposal.
IT and SDLC: Privacy requirements should be present in requirements, design review, testing, and release gates.
A simple set of control gates many organisations adopt:
Gate 1: Privacy screening in project intake
Gate 2: Data classification and access model confirmed
Gate 3: Vendor review completed (where applicable)
Gate 4: Notice/consent content reviewed (where applicable)
Gate 5: Retention and deletion method defined before go-live
Vendor governance: where many privacy programmes break
Even organisations with good internal discipline can be exposed by weak third-party controls. Vendors may include payroll processors, CRM platforms, call centres, marketing agencies, cloud providers, and logistics partners.
Vendor privacy governance should cover:
Due diligence (what data, where processed, security posture, subcontractors)
Contract terms (processing instructions, confidentiality, security measures, breach notice timelines, audits)
Ongoing monitoring (periodic reviews, incident reporting, performance issues)
This matters even in seemingly non-technical partnerships. For example, a Jamaican retailer or reseller that sources inventory internationally may share customer contact and delivery details with a wholesale liquidation distributor such as American Bulk Pallets to coordinate fulfilment. That data sharing can be perfectly legitimate, but it still needs governance: confirm roles (controller/processor), define processing instructions, and ensure the contract and operational process match what you tell customers.
Assurance: proving the programme works (three lines of defence)
Privacy governance becomes credible when it includes independent checking.
A practical three-lines approach:
First line (business and operations): execute controls, maintain records, follow procedures.
Second line (privacy and compliance): define standards, monitor, advise, challenge, report.
Third line (internal audit or independent review): test design and operating effectiveness.
Assurance does not need to be heavy. What matters is consistency and evidence. Examples of high-value assurance activities:
Quarterly sampling of rights requests for completeness and timeliness
Review of a subset of high-risk vendors for contract clauses and due diligence evidence
Access review testing for a critical system (who has access, why, and whether it is still needed)
Retention and deletion testing for a priority dataset

Common privacy governance failures (and how to correct them)
“Privacy sits with Legal, so we are covered”
Legal input is essential, but privacy is operational. Fix this by assigning business owners to processing activities and making them report status, not just receive advice.
“We have a DPO or privacy lead, so they own compliance”
A privacy lead coordinates, but cannot own every process and system. Fix this with RACI, privacy champions, and change gates.
“Training is our main control”
Training supports behaviour, but it is not a control system. Fix this by adding measurable controls: inventory, approvals, access reviews, retention evidence, vendor governance, incident exercises.
“We only talk about privacy after an incident”
That is reactive governance. Fix this with a monthly operational working group and quarterly executive reporting, even when nothing has gone wrong.
Turning this into an operating model your organisation can run
If you want a fast path to implementation, treat privacy governance as a build-out of a few concrete artefacts:
Privacy strategy and annual plan (approved by an executive sponsor)
Processing inventory with named owners
Risk-tiering and impact assessment workflow for new initiatives
Vendor register and onboarding workflow
Rights request workflow and evidence pack
Incident response playbook integrated with security
Board-ready dashboard with 8 to 12 meaningful measures
For deeper implementation guidance aligned to Jamaica’s Data Protection Act timelines and audit expectations, you may also find these PLMC resources helpful:
If you want support designing or operationalising your privacy governance model, Privacy & Legal Management Consultants Ltd. (PLMC) provides data protection implementation, training, risk assessment tools, and a free consultation to help you move from intent to evidence-based compliance.
