
Implementation of Data Privacy Act: Step-by-Step Roadmap

Most Jamaican organisations do not struggle with understanding the Data Protection Act, they struggle with implementation. Turning legal requirements into day-to-day processes, controls, evidence, and accountability is where projects stall.
This step-by-step roadmap is designed for the implementation of data privacy act obligations in real operations. It focuses on the practical deliverables you need, who should own them, and what “good” looks like when you must demonstrate compliance.
If you need a refresher on principles and rights first, see PLMC’s guide to Data Privacy in Jamaica: Key Principles and Rights.
What “implementation” means (beyond writing policies)
Implementation is the point where privacy becomes measurable and repeatable. You are not just drafting documents, you are building a small management system that can answer:
What personal data do we hold, where is it, and why?
What is our lawful basis for each processing activity?
How do we handle access, correction, objection, and deletion requests consistently?
How do we prevent incidents and respond if one happens?
What evidence can we produce to show controls are working?
A practical way to think about it is: decisions (governance) + knowledge (data mapping) + controls (process and security) + proof (records and testing).
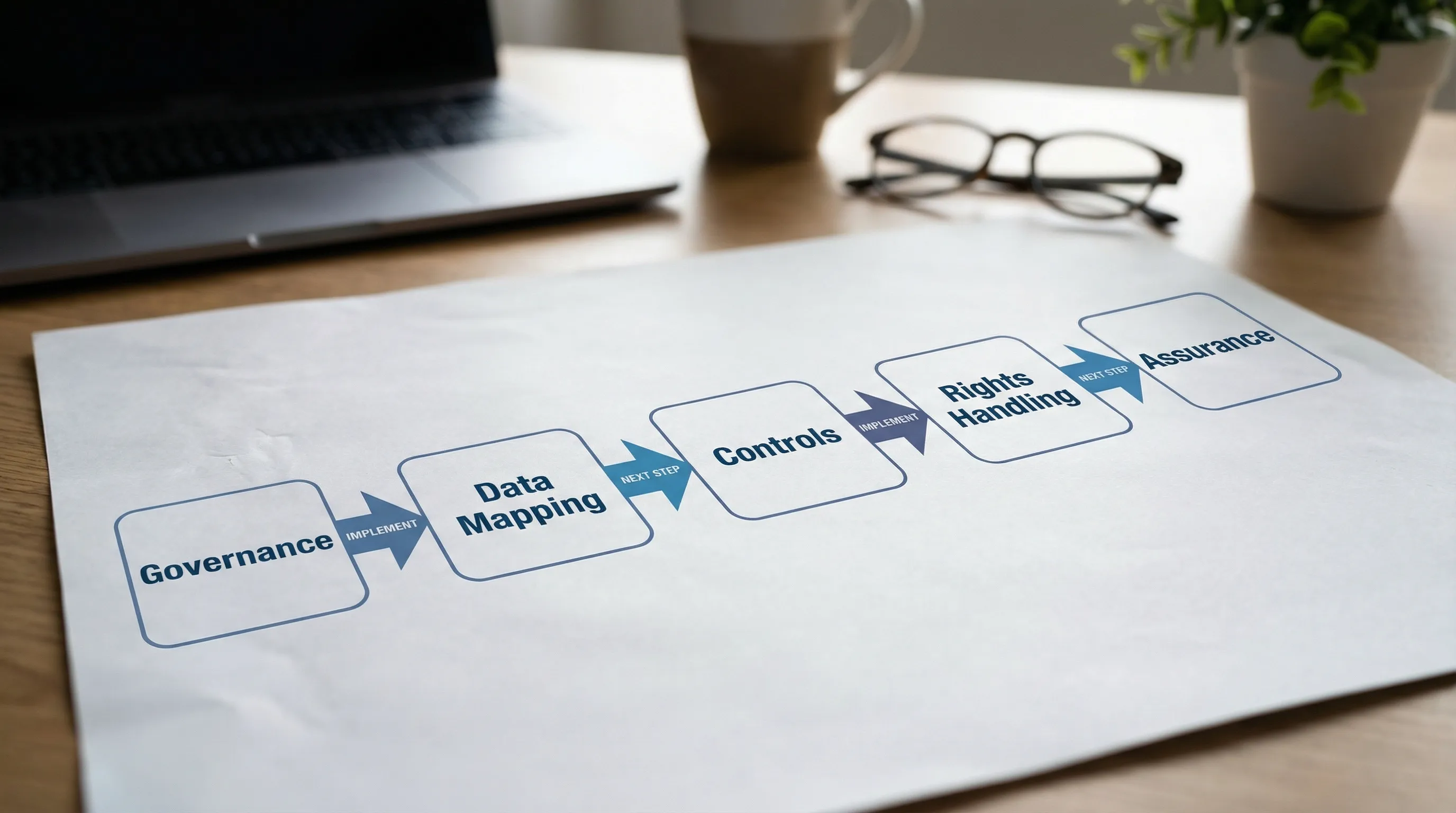
Roadmap at a glance (phases, outputs, owners)
The steps below can be executed in parallel, but sequencing matters. Most organisations move fastest when they deliver an initial “baseline” in 6 to 12 weeks, then harden and expand over the next quarter.
Phase | Primary goal | Key outputs (minimum viable) | Typical owner(s) |
1. Mobilise | Set mandate and accountability | Privacy programme charter, roles, scope, plan | CEO/MD, Board sponsor, Compliance, Legal |
2. Discover | Find and document personal data use | Data inventory, system list, vendor list, high-risk areas | Privacy lead, IT, HR, Operations |
3. Design | Decide lawful basis and rules | Privacy notices outline, retention approach, DPIA triage | Legal/Compliance, Business owners |
4. Build | Implement processes and controls | Rights request workflow, breach workflow, vendor controls | IT/Security, HR, Procurement |
5. Embed | Train, communicate, operationalise | Training completion records, updated forms, scripts | HR, Privacy lead, Managers |
6. Assure | Prove it works and improve | Internal review, evidence pack, corrective actions | Internal audit, Risk, Privacy lead |
Phase 1: Mobilise (mandate, scope, and roles)
A privacy programme fails most often because ownership is unclear. Start by creating a clear mandate and a small, empowered team.
1) Confirm your scope and “who you are” in the data chain
Document where the organisation acts as a controller, a processor, or both. This affects your contract terms, notices, and operational duties.
Practical output: a one-page scope statement that includes business units, locations, brands, and key systems (HR, CRM, payroll, CCTV, customer support).
2) Appoint a privacy lead and define decision-making
Even if you do not have a full-time Data Protection Officer role, you need a named person accountable for coordinating implementation and reporting.
Practical output: a RACI-style assignment of who is Responsible, Accountable, Consulted, and Informed for each workstream (HR data, customer data, marketing, IT/security, procurement).
3) Set implementation objectives that can be evidenced
Avoid goals like “be compliant.” Choose goals like:
“We can fulfil a data subject request end-to-end within an agreed internal service level.”
“We maintain an approved data inventory covering all business units.”
“All high-risk processing activities are assessed using a consistent DPIA method.”
Practical output: a privacy programme plan with milestones, plus a simple evidence register (what documents and logs you will keep).
For background on compliance expectations, you can review the Data Protection Act, 2020 (Jamaica) via official government sources.
Phase 2: Discover (data inventory that is actually usable)
A data inventory is not an academic spreadsheet. It is the foundation for notices, retention, vendor control, security, and rights handling.
4) Build a “processing inventory” by business activity, not by department
Start with real activities, for example onboarding employees, payroll, customer onboarding, online sales, credit checks, loyalty programmes, CCTV, guest Wi-Fi, marketing campaigns, complaints handling.
For each activity, capture:
Categories of data (personal, sensitive where applicable)
Purpose(s)
Source (direct from individual, third party, internal)
Where stored (systems, paper files, cloud platforms)
Who can access
Who it is shared with (including processors)
Retention (current practice, not ideal state)
Practical output: a processing inventory that can be filtered by system, vendor, and risk level.
5) Identify high-risk processing early
You want to surface risk before you design controls. Typical high-risk areas include:
Large-scale monitoring (including CCTV or tracking)
Handling sensitive categories of data
Processing involving children
Automated decision-making affecting individuals
Cross-border transfers or heavy reliance on cloud vendors
Practical output: a short “risk register” listing high-risk activities and what must be assessed first.
Phase 3: Design (lawful basis, transparency, retention)
This phase translates your inventory into decisions that can be applied consistently.
6) Confirm lawful basis and document it
Implementation requires a documented rationale for why each activity is lawful. In practice, teams often “assume consent” when the stronger basis is contractual necessity, legal obligation, or legitimate interests (depending on the context).
Practical output: a lawful basis column in your processing inventory, plus short notes that justify the choice.
Tip: align this documentation with internationally recognised privacy governance approaches, such as the NIST Privacy Framework and ISO-style management system thinking. This helps with auditability even when your organisation is not formally certified.
7) Create or update privacy notices with real inputs from operations
Privacy notices often fail because they are written without the inventory. Use your data map to ensure notices reflect:
What you collect
Why you collect it
Who you share it with (by category)
How long you keep it (or how you determine retention)
How individuals can exercise their rights
Practical output: updated external notices (customers, website users) and internal notices (employees, contractors).
8) Define retention rules that match business and legal realities
Retention is one of the quickest ways to reduce risk, because keeping data “just in case” increases breach exposure and complicates rights requests.
Practical output: a retention schedule (even if initial) that covers priority record types such as:
Employee and applicant records
Customer account and transaction records
Marketing lists and consent records (where used)
CCTV footage
Support tickets and complaint files
Keep it practical: define retention triggers (for example, end of employment, account closure, last transaction, claim resolution) and disposal methods.
Phase 4: Build (rights handling, vendor controls, security, incident readiness)
This is where implementation becomes operational. You are building repeatable workflows and controls.
9) Implement a data subject rights workflow
A rights process should not live in one person’s inbox. Build a workflow that captures requests, verifies identity appropriately, assigns tasks to system owners, and logs outcomes.
Practical output: a rights request procedure with templates (acknowledgement, ID verification, extension or refusal where allowed, response pack). Also keep a request log.
Design choices that prevent chaos:
One intake channel (email address or web form), with an internal triage backup
Clear ownership per system (HR system owner, CRM owner, payroll owner)
Standard search steps (what fields to search, where exports are stored)
10) Fix vendor and processor management (contracts plus checks)
Many Jamaican organisations rely on payroll providers, cloud email, HR platforms, CRMs, security companies, and marketing tools. Implementation requires that procurement and vendor management be privacy-aware.
Practical output: a vendor register that flags who processes personal data, the type of data involved, where it is hosted, and what contract terms apply.
Minimum controls to implement:
Contract clauses covering confidentiality, security, breach notification, and use limitations
A basic vendor due diligence checklist (security measures, access controls, subcontractors)
Offboarding process (data return or deletion when the relationship ends)
11) Implement security controls that match your data risks
The Act expects appropriate safeguards, and regulators and customers will judge you on what was reasonable given your risk profile.
Practical output: a short security control baseline for systems processing personal data (access control, MFA where feasible, encryption, backups, patching, logging, least privilege, secure disposal).
Where cyber security maturity is developing, prioritise:
Admin access control and MFA for email and core systems
Laptop and mobile device protections (passwords, encryption, remote wipe)
Centralised joiner, mover, leaver controls
Backup testing and ransomware readiness
12) Build an incident and breach response playbook
You do not want your first breach plan to be written during an incident. Implementation means defining roles, escalation, evidence preservation, communications, and decision-making.
Practical output: an incident response procedure aligned with your privacy obligations, plus a breach assessment template that helps decide when to notify affected individuals or authorities (as applicable).
Good practice references include the ISO/IEC 27001 family of controls for information security governance.
Phase 5: Embed (training, culture, and “privacy by design”)
Even strong policies fail if staff are unaware, rushed, or not supported by processes.
13) Run role-based privacy training (not one-size-fits-all)
Implementation training works best when it mirrors real tasks:
HR: recruitment, employee records, disciplinary files, reference checks
Customer service: identity verification, call recordings, complaint files
Marketing: mailing lists, consent preferences, third-party campaigns
IT: access requests, log review, vendor onboarding, secure disposal
Practical output: training attendance records, short quizzes or acknowledgements, and updated onboarding materials.
PLMC provides training sessions tailored to organisational roles, and can support awareness programmes designed for Jamaican workplaces.
14) Introduce a simple DPIA (impact assessment) trigger process
A DPIA does not need to be bureaucratic. The goal is to catch risky initiatives early, for example new apps, new data sharing, expanded CCTV coverage, biometrics, or new marketing profiling.
Practical output: a “DPIA required?” triage form that projects must complete before go-live, plus a DPIA template for high-risk cases.
15) Update forms, scripts, and customer touchpoints
If your notice says one thing but frontline scripts say another, that is where complaints begin. Align the reality of data collection with what you publish.
Practical output: updated customer onboarding forms, HR forms, website forms, call scripts, and consent language (where used).
Phase 6: Assure (evidence, testing, and continuous improvement)
Compliance is not just doing the work, it is being able to show it.
16) Build your “privacy evidence pack”
An evidence pack is a structured set of documents and logs that you can produce for leadership, auditors, or regulators.
Control area | Evidence examples you should be able to produce |
Governance | Charter, role appointments, meeting minutes, risk register |
Transparency | Published notices, internal notices, change log |
Inventory | Processing inventory, system list, data flow notes |
Rights | Request log, response templates, completed request records |
Vendors | Vendor register, due diligence records, signed agreements |
Security | Access reviews, MFA policy, incident procedure, training records |
Retention | Retention schedule, disposal records, archived data controls |
Assurance | Internal review results, corrective actions, follow-up checks |
17) Test what you built (tabletop and sampling)
Two simple tests dramatically improve readiness:
A rights request simulation (pick a real customer record, run the workflow end-to-end)
An incident tabletop exercise (simulate a lost laptop or compromised account and test escalation)
Practical output: test notes, gaps identified, and assigned corrective actions.
18) Operationalise reporting to leadership
Privacy implementation is a risk topic. Leadership should see a simple quarterly view of:
Rights requests volume and outcomes
Incidents and near misses
Vendor risks and onboarding status
Training completion
High-risk projects assessed
Practical output: a short privacy dashboard or report (even if it starts as a single page).
Common implementation pitfalls (and how to avoid them)
Many programmes slow down for predictable reasons:
Treating privacy as a legal-only project. Implementation needs IT, HR, operations, and procurement. Legal guidance is necessary, but not sufficient.
Building the inventory too late. If you draft notices and rights workflows before you map data, you will rework everything.
Over-engineering templates. Start with minimum viable procedures that staff can follow, then improve.
Ignoring vendors. If your processors are uncontrolled, your risk profile stays high even if internal processes improve.
No evidence discipline. If you cannot show meeting minutes, logs, and approvals, you will struggle to demonstrate accountability.
If you want an implementation-focused checklist to complement this roadmap, PLMC also offers a Privacy and Data Protection: Practical Checklist.
Frequently Asked Questions
How long does implementation of data privacy act requirements usually take? A baseline programme is often achievable in 6 to 12 weeks if leadership assigns owners and you prioritise high-risk processing. Full maturity (testing, continuous improvement, vendor uplift) typically takes longer and should be treated as an ongoing programme.
Do small businesses in Jamaica need the same level of documentation as large organisations? The principles are the same, but the scale should be proportional. Small businesses can implement a lean inventory, simple notices, a basic rights workflow, and essential security controls, then expand as operations grow.
What is the first document we should produce for implementation? A short privacy programme charter (scope, roles, timeline) is a strong first step because it unlocks decision-making and resourcing. Immediately after that, start the data inventory.
How do we handle cross-border cloud services during implementation? Start by documenting where data is hosted and which vendors process it, then put contractual controls and due diligence in place. Treat cross-border transfers as a specific risk area to be assessed and documented.
What if we do not have a dedicated privacy officer? Assign a privacy lead with authority to coordinate across departments, and set clear escalation to leadership. Many organisations use a part-time role initially, supported by training and external consulting.
Need help turning the roadmap into an implementation plan?
PLMC supports Jamaican organisations with practical Data Protection Act implementation, including data mapping, programme governance, staff training, cyber security alignment, and GRC integration. If you want to accelerate progress, reduce rework, and build an evidence-ready programme, you can request a free consultation to discuss your current state and next steps.
