
Data Protection Risk Assessment: Scope, Steps, and Evidence

A data protection programme becomes defensible when you can answer three questions at any time: What personal data do we hold, what could go wrong, and what proof do we have that we reduced the risk? That is exactly what a data protection risk assessment is for.
For Jamaican organisations working to meet the expectations of the Data Protection Act, a risk assessment is not just a “security exercise” and not just a document. Done well, it is a repeatable process that links your data map to your controls, your vendor oversight, your incident readiness, and the evidence you will need when customers, auditors, regulators, or your Board ask for assurance.
What a data protection risk assessment actually covers
A data protection risk assessment is a structured evaluation of risks to individuals’ rights and freedoms (privacy harms) that may arise from how your organisation collects, uses, shares, stores, and disposes of personal data.
It typically covers:
People: staff behaviour, access rights, segregation of duties, training, insider risk.
Process: how data is collected, approvals, retention and disposal, rights handling, breach response, vendor onboarding.
Technology: identity and access management, logging, endpoint security, backups, encryption, cloud configurations.
Third parties: processors, outsourced HR/payroll, marketing platforms, cloud providers, couriers, call centres.
Physical environment: offices, archives, paper records, device storage, visitor access, disposal methods.
A common mistake is to scope the assessment only to IT security. Under modern privacy expectations (and aligned with global good practice), you also assess misuse, over-collection, unlawful sharing, excessive retention, and weak governance.
Risk assessment vs DPIA (impact assessment): when you need which
Many organisations use “risk assessment” as a broad umbrella and reserve a deeper impact assessment (often called a DPIA in GDPR contexts) for higher-risk processing.
As a practical approach:
Use a baseline risk assessment for business-as-usual processing across the organisation.
Trigger a high-risk impact assessment when you introduce new technologies, new large-scale data uses, or sensitive data at scale.
High-risk triggers often include:
Sensitive data (health, biometrics, children’s data) processed at scale.
Systematic monitoring (CCTV analytics, call monitoring, tracking staff productivity).
Large datasets combined across systems (CRM + loyalty + behavioural analytics).
New cross-border transfers or new cloud hosting arrangements.
Even if your internal terminology differs, the core point is consistent: higher risk requires deeper analysis and stronger evidence.
Scope: how to define it without making it unmanageable
Scope determines whether your assessment is usable or ignored.
1) Choose the unit of assessment
You can scope by:
System (HRIS, CRM, core banking platform)
Process (recruitment, customer onboarding, debt collection)
Dataset (patient records, student records)
Business line/location (branch, call centre, clinic)
For most Jamaican organisations, a practical starting point is process-based scoping (because it naturally includes people, paper, vendors, and technology).
2) Set clear boundaries
Write down what is in and out:
In scope: personal data handling end-to-end (collection to disposal)
Out of scope (for this cycle): non-personal data, purely public information, legacy archives scheduled for later review
3) Identify the data “hot spots” early
A short pre-scan helps you prioritise where risk is highest. Typical hot spots:
HR files and medical benefits
Customer due diligence (especially in regulated sectors)
Marketing databases and messaging platforms
CCTV and visitor logs
Customer support recordings
Cross-border cloud services
Scope cheat sheet (quick matrix)
Area | Typical risk to individuals | Common organisational risk | Usual evidence to expect |
HR and payroll | identity theft, unfair decisions | employment disputes, reputational harm | access controls, retention schedule, staff confidentiality |
Customer onboarding | over-collection, unlawful sharing | complaints, enforcement, lost trust | privacy notice, lawful basis, data minimisation rules |
Marketing and analytics | profiling, unwanted contact | spam complaints, brand damage | consent/opt-out logs, suppression lists, vendor contracts |
Vendor processing | loss of control, onward transfers | breaches via third parties | due diligence records, DPAs, audit clauses |
Physical records | exposure, unauthorised access | regulatory findings, litigation | secure storage, disposal certificates, visitor controls |
Steps: a practical, repeatable method (that produces usable outputs)
You do not need a complex methodology to be credible. You need a consistent one.
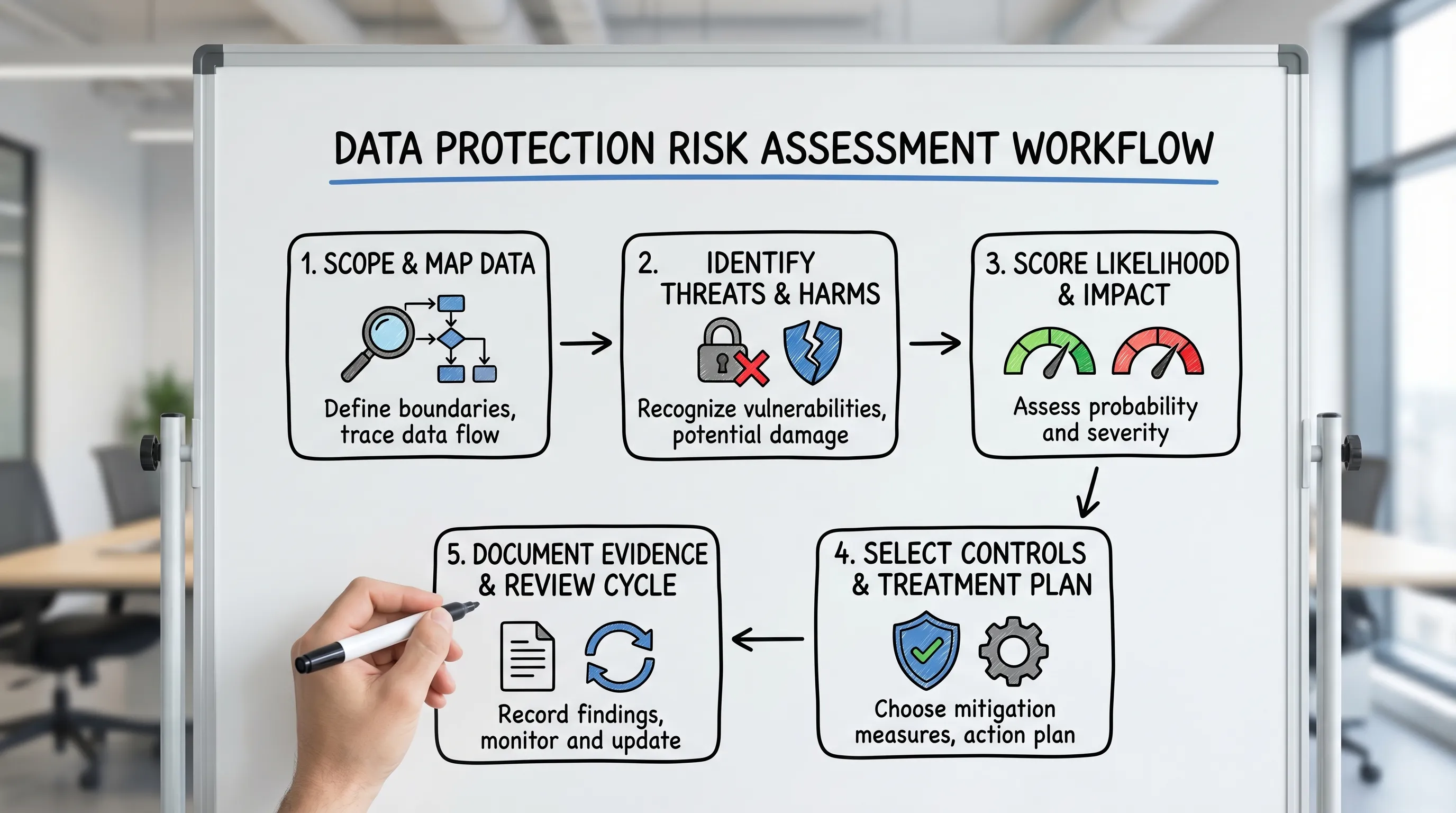
Step 1: Map the processing (so you are not guessing)
For each in-scope process, capture:
Purpose of processing (why you need the data)
Categories of individuals (employees, customers, students)
Categories of data (ID numbers, contact details, financial data, health data)
Sources (online forms, paper forms, third parties)
Where it is stored (on-premise, cloud, paper archives)
Who accesses it (roles, not names)
Disclosures (vendors, regulators, affiliates)
Retention and disposal
If you already have a data inventory, use it. If you do not, keep this mapping lightweight, but specific enough that someone else can follow it.
Step 2: Identify risks as “harms” to people, not only threats to systems
A helpful way to phrase risks is: “If X happens, the likely harm is Y.”
Examples:
If access to the HR folder is not role-restricted, employees could experience unauthorised disclosure of medical information.
If a vendor uses sub-processors without oversight, customers could lose control over where their data is transferred or stored.
If retention is undefined, former customers could be exposed to unnecessary long-term risk with no business need.
This framing aligns your assessment with privacy outcomes, not only technical controls.
Step 3: Score likelihood and impact (use a scale your leaders will understand)
Most organisations use a 3x3 or 5x5 risk matrix. What matters is consistency and clarity.
Impact should reflect both:
Impact to individuals (financial loss, distress, discrimination, identity theft)
Impact to the organisation (regulatory action, contractual claims, operational disruption)
A simple approach:
Score | Likelihood (example) | Impact (example) |
1 | Unlikely within 2 years | Low harm, limited data, easy remediation |
2 | Possible within 12-24 months | Moderate harm, some sensitive data |
3 | Likely within 6-12 months | Serious harm, sensitive data or large scale |
4 | Very likely or already occurring | Severe harm, high volume, hard to contain |
5 | Near certainty | Catastrophic harm, systemic issues |
Do not over-engineer. Your goal is prioritisation.
Step 4: Evaluate existing controls (and identify gaps)
Controls usually fall into three buckets:
Governance controls: policies, approvals, ownership, audits, training, records.
Operational controls: procedures, checklists, quality assurance, exception handling.
Technical controls: access control, logging, encryption, backups, endpoint security.
A useful output is the difference between:
Inherent risk (before controls)
Residual risk (after controls)
This is where decision-makers can accept risk, reduce it, transfer it (for example via contracts/insurance), or stop the activity.
Step 5: Create a risk treatment plan with owners and dates
Your treatment plan should be measurable:
Action (what will change)
Owner (role or named person)
Due date
Evidence (what will prove it is done)
Residual risk target (what “good” looks like)
This prevents risk assessments from becoming reports that do not change anything.
Step 6: Sign-off, review cadence, and change triggers
A risk assessment is a living control. Set:
Review frequency (commonly every 12 months, and sooner for high-risk areas)
Change triggers (new vendor, new system, new data category, new cross-border transfer, major incident)
Sign-off authority (senior management, risk committee, or Board depending on severity)
Evidence: what to keep so you can prove compliance
If an auditor, client, or regulator asks “How do you know you are compliant?”, you need more than verbal assurance. You need an evidence pack.
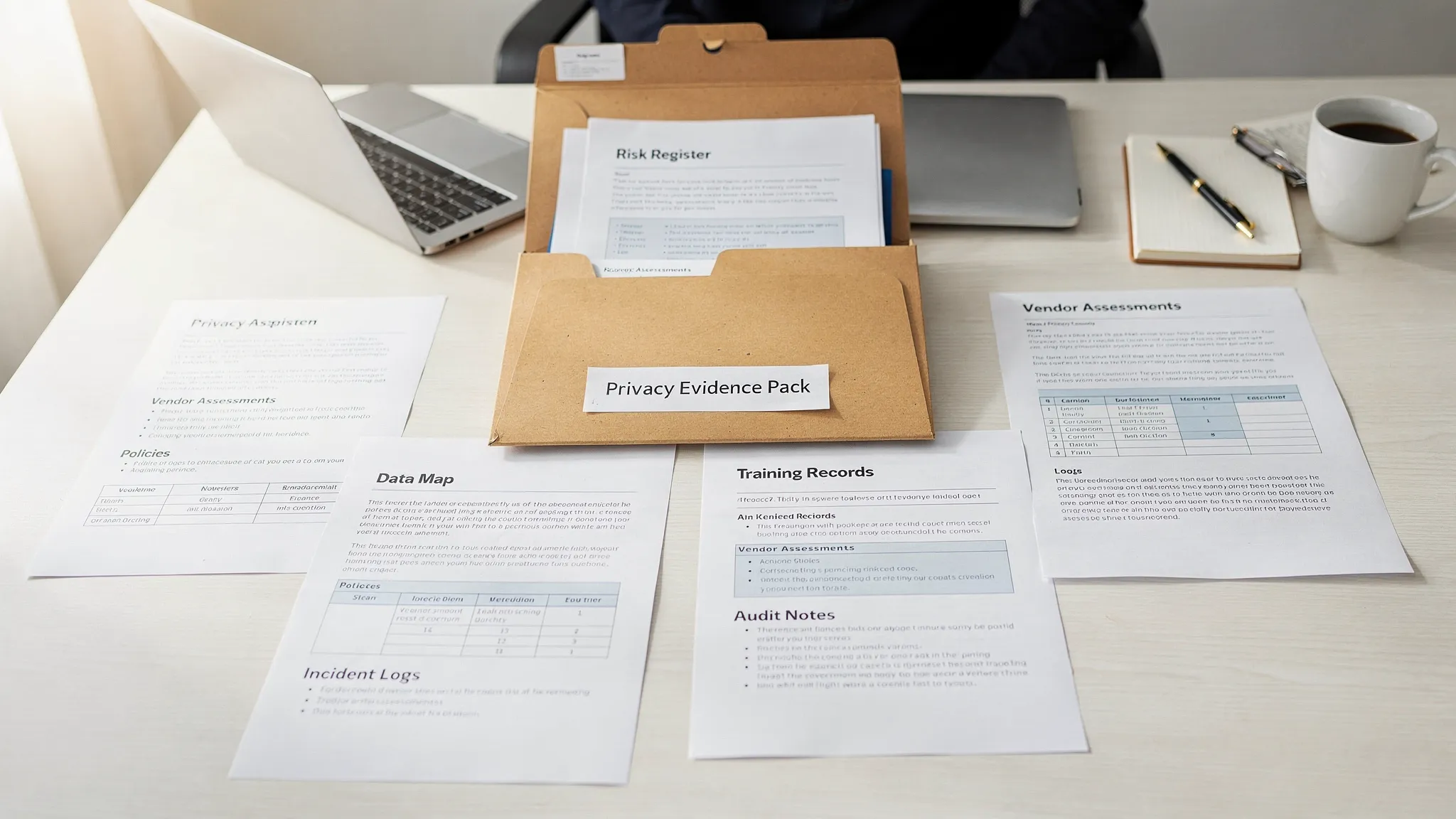
The “minimum viable” evidence pack
These items usually give the strongest coverage with the least duplication:
Evidence item | What it proves | Good practice detail |
Data inventory / processing register | you know what data you hold and why | includes purpose, sharing, retention, security controls |
Risk assessment report (per scope) | you assessed harms and prioritised them | includes inherent vs residual risk and sign-off |
Risk register (tracking) | you are managing risk over time | includes owners, dates, status, residual risk |
Privacy notices | transparency to individuals | version control and review dates |
Rights request procedure + logs | you can respond to individuals | includes timelines, identity verification, outcomes |
Vendor due diligence + contracts | third-party risk is controlled | includes security checks and data processing clauses |
Retention schedule + disposal records | data is not kept forever | includes secure disposal certificates where applicable |
Incident response plan + incident log | readiness and accountability | includes post-incident reviews and lessons learned |
Training records | awareness and role competence | attendance, content, role-based modules |
Evidence quality tips (what reviewers look for)
Traceability: Can you trace a control back to a specific risk?
Versioning: Do documents show dates, owners, and approval?
Consistency: Does the retention schedule match what teams actually do?
Sampling: Can you show a few real examples (a vendor assessment, a closed rights request, a completed access review)?
Common risk areas in Jamaican organisations (and what “good” looks like)
Vendor and outsourcing risk
If a processor has a breach, you will still be expected to show you selected and monitored them responsibly.
Strong indicators include:
A standard vendor due diligence checklist for privacy and security
A contract template that covers confidentiality, breach notification, sub-processing, and return or deletion at end of service
Periodic reviews for critical vendors (not every vendor needs the same depth)
Cross-border transfers and cloud services
Many Jamaican organisations use cloud services hosted abroad. The risk assessment should document:
Where data is stored and accessed from
Who can access it (roles, admin privileges)
What safeguards exist (contractual terms, security controls, access logging)
Physical records and storage
Paper files remain a major exposure point, especially where records are stored offsite or moved between locations.
If you use external physical storage for archives or records during renovations, expansions, or consolidation projects, treat it like any other control: document security requirements (locks, access logs, environmental risks, transport chain of custody). Some organisations even use secure containerised storage as part of facilities planning. If you are exploring this option in the US for operational projects, see buy shipping containers online for examples of container specifications and delivery logistics, then ensure your own security and access controls meet your risk appetite.
Over-collection and “just in case” data
A common privacy gap is collecting more than needed because “it might be useful later.” Your risk assessment should challenge:
Whether each data field is necessary for the stated purpose
Whether optional fields are clearly marked
Whether you have a deletion/retention rule that prevents indefinite storage
Deliverables you should expect at the end of the assessment
A strong data protection risk assessment normally produces:
A defined scope statement (what you assessed, boundaries, assumptions)
Process maps or data flow summaries (even if simple)
A risk register with scoring, inherent and residual risk
A treatment plan with owners, dates, and evidence requirements
Management sign-off and review schedule
If you do not get a treatment plan, you did not get a risk assessment. You got a report.
How this fits into a broader compliance programme
Risk assessment is most effective when it is integrated into your governance and operating rhythm. If you are building your programme for 2026 execution, connect your assessment outputs to:
Your quarterly implementation plan and assurance cycle (see PLMC’s Data Protection Jamaica: Compliance Roadmap for 2026)
Your baseline controls checklist (useful alongside a risk lens), such as PLMC’s Privacy and Data Protection: A Practical Checklist
The difference is simple: checklists confirm coverage, risk assessments justify priority and depth.
Frequently Asked Questions
What is the scope of a data protection risk assessment? A good scope covers the end-to-end handling of personal data for the selected processes or systems, including people, technology, vendors, physical records, retention, and disclosures.
How often should we perform a data protection risk assessment? Commonly annually for key processing areas, and immediately when major changes occur (new system, new vendor, new sensitive data use, cross-border transfer change, or a significant incident).
What evidence should we keep after a risk assessment? Keep your scope statement, data flows, risk register (with inherent and residual risk), treatment plan, sign-offs, and proof of completed actions (policies, access reviews, vendor checks, training logs, incident logs).
Is a privacy risk assessment the same as a cyber security assessment? Not exactly. Cyber security assessments focus on confidentiality, integrity, and availability of systems. Privacy risk assessments also examine lawful use, over-collection, transparency, retention, sharing, and harms to individuals.
What is the most common reason risk assessments fail? They fail when they are not connected to ownership and deadlines. Without a treatment plan, status tracking, and leadership sign-off, the assessment does not change behaviour or reduce risk.
Get support with a defensible data protection risk assessment
If you want a risk assessment that stands up to scrutiny and produces a clear treatment plan, PLMC can help you scope the work, assess risks against your real processing activities, and assemble an evidence pack aligned with the Data Protection Act.
Explore PLMC’s resources at Privacy & Legal Management Consultants Ltd. or book a free consultation to discuss your organisation’s scope, timelines, and priorities.
