
Data Protection Cyber Security: Controls That Reduce Real Risk

Most data protection failures are not caused by a missing policy, they are caused by a predictable set of cyber security weaknesses: stolen passwords, unpatched systems, misconfigured cloud storage, weak vendor access, and slow incident response.
If you are responsible for compliance in Jamaica, the practical question behind “data protection cyber security” is simple:
Which controls reduce real risk, quickly, and leave evidence you can defend?
This guide focuses on the controls that consistently prevent breaches, limit blast radius, and support compliance with the spirit of Jamaica’s Data Protection Act (protecting personal data through appropriate security and accountability).
Data protection cyber security: why “privacy” controls must be technical
Data protection obligations are often documented in governance language (policies, notices, contracts). But most personal data is lost through operational failures that cyber security controls are designed to stop.
A useful way to align teams is to treat privacy risk as an outcome of cyber risk:
Confidentiality failures (unauthorised access) lead to data exposure.
Integrity failures (unauthorised changes) corrupt customer and financial records.
Availability failures (ransomware, outages) can force unsafe workarounds, reduce service quality, and increase breach likelihood.
Frameworks like the NIST Cybersecurity Framework 2.0 and CIS Critical Security Controls v8 are useful here because they translate risk into clear, testable practices.
Start with a risk-based control strategy (so you do not “checkbox” your budget)
Before you buy tools or write more documents, make three decisions:
1) Define the data that would hurt you most if exposed
For most Jamaican organisations, the highest-risk categories typically include:
Customer ID information (TRN, passport number, driver’s licence)
Financial data (account numbers, card-related data)
Employee records (medical, disciplinary, payroll)
Sensitive categories (health, biometrics, children’s data)
This is not about perfect data mapping on day one, it is about identifying where strong controls must be non-negotiable.
2) Identify your most likely attack paths
Across many industries, the same entry points show up repeatedly:
Phishing leading to credential theft
Compromised remote access (VPN, RDP, admin portals)
Unpatched internet-facing systems
Excessive privileges and shared accounts
Third-party access (IT support, payroll vendors, cloud platforms)
3) Choose a control baseline you can evidence
Pick a baseline that auditors, insurers, and executives understand, then tailor it:
CIS Controls v8 for pragmatic, prioritised controls
NIST CSF for governance and program structure
ISO/IEC 27001 for formal information security management and assurance
You do not need certification to benefit from the discipline of these standards.
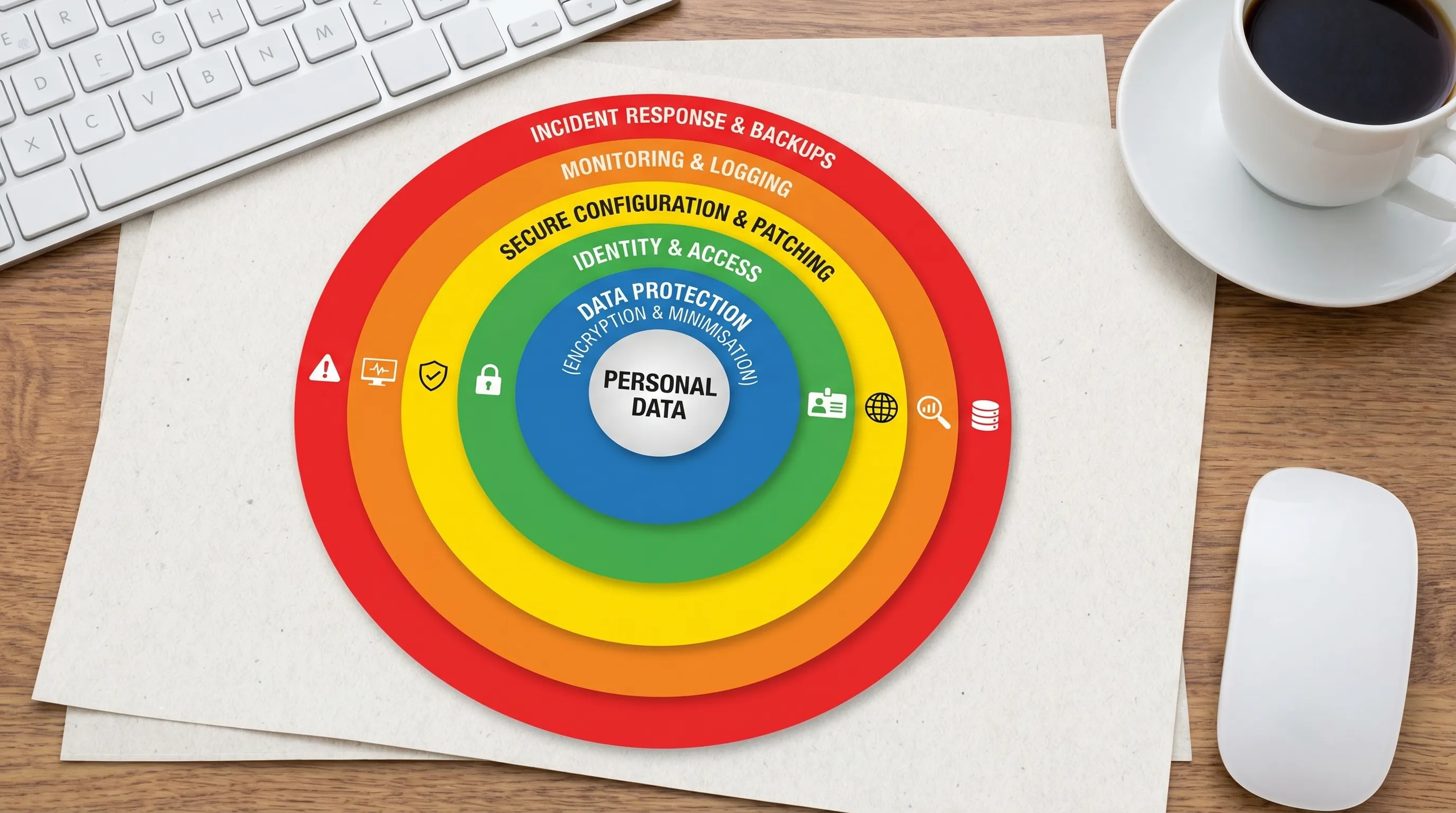
Controls that reduce real risk (and how to prove they exist)
Below are the controls that most directly reduce personal data breach likelihood and impact. They also tend to produce clear evidence for management, clients, and regulators.
1) Strong identity and access management (IAM) with MFA everywhere
If an attacker can log in as a user, they can usually reach personal data.
Prioritise:
Multi-factor authentication (MFA) on email, cloud apps, remote access, and admin accounts
No shared accounts, especially for administrators and service desks
Least privilege (users only access what they need)
Joiner-mover-leaver process (fast removal of access when someone leaves)
Evidence to keep:
MFA enforcement screenshots or configuration exports
List of admin accounts and proof of MFA
Access review records (monthly or quarterly)
Reference: Microsoft has repeatedly stated MFA can block the vast majority of account compromise attempts when properly implemented (see Microsoft Security guidance).
2) Patch management and secure configuration (reduce “known exploit” breaches)
Unpatched systems and default configurations are still a major driver of breaches and ransomware.
Prioritise:
A defined patch SLA (for example: critical patches within days, not months)
Asset inventory (you cannot patch what you cannot see)
Secure configuration baselines for endpoints and servers
Removal of unsupported operating systems and unneeded services
Evidence to keep:
Patch compliance reports (by device and severity)
A record of exceptions (and why they are accepted)
Baseline configuration standards
3) Email and phishing controls (because phishing is still a top initial vector)
Email is the front door for many incidents.
Prioritise:
Advanced phishing protection (or at minimum strong filtering)
DMARC, SPF, DKIM for your domain to reduce spoofing
Disable legacy authentication in cloud email where possible
User reporting mechanism (a “report phishing” button) plus response playbook
Evidence to keep:
DMARC policy records and reports
Secure email gateway settings
Phishing simulation and training logs (if used)
Industry reference: the Verizon Data Breach Investigations Report continues to highlight the role of human-driven attack patterns such as phishing and credential abuse.
4) Backups that are recoverable (not just “we have backups”)
For data protection, availability matters. Ransomware often becomes a privacy incident when organisations cannot restore cleanly and resort to insecure workarounds.
Prioritise:
3-2-1 backup approach (multiple copies, different media, one offsite)
Immutable or offline backups (resistant to ransomware)
Regular restore tests (prove you can recover)
Defined RPO/RTO targets aligned to business impact
Evidence to keep:
Restore test results and screenshots
Backup job success rates
Written recovery procedures
Guidance: see CISA ransomware resources for practical resilience measures.
5) Logging and monitoring focused on “detection you can act on”
Many organisations collect logs but cannot answer basic questions during an incident: who accessed what, from where, and when?
Prioritise:
Centralised logging for identity systems, endpoints, servers, and key applications
Alerts for high-risk events (new admin creation, impossible travel, mass downloads)
Time synchronisation (accurate timestamps matter in investigations)
A clear escalation process (who responds, within what timeframe)
Evidence to keep:
Log source list and retention settings
Sample alerts and ticket records showing investigation
Incident response metrics (time to detect, time to contain)
6) Data minimisation and retention (a privacy control that also reduces breach impact)
Keeping less personal data, for less time, reduces exposure. This is one of the most underrated “security” controls because it reduces the amount of data an attacker can steal.
Prioritise:
Retention schedules linked to business and legal needs
Secure disposal processes for paper and digital records
Data classification (so teams know what needs stronger protection)
Evidence to keep:
Approved retention schedule
Disposal logs (especially for high-risk records)
Data classification standard and sample labels
For a broader organisational checklist, you can cross-reference PLMC’s practical guide: Privacy and Data Protection: A Practical Checklist.
7) Vendor and third-party access controls (especially outsourced IT)
In Jamaica, many organisations rely on managed service providers, payroll vendors, and cloud platforms. Vendor access can become your highest-risk pathway.
Prioritise:
Contracts with security requirements (access controls, breach notification, sub-processors)
MFA and least privilege for vendor accounts
Separate vendor admin accounts (no shared credentials)
Periodic review and removal of stale vendor access
Evidence to keep:
Vendor risk assessments and due diligence notes
Contract clauses or security addenda
Access review logs for vendor accounts
8) Incident response that is rehearsed (not just written)
A fast response is a breach impact control.
Prioritise:
A practical incident response plan with named roles
Tabletop exercises (for example: ransomware, email compromise, lost laptop)
A decision tree for notification, legal, and communications
Forensics-ready steps (preserve logs, images, and evidence)
Evidence to keep:
Exercise agenda, attendees, and lessons learned
Updated playbooks after each exercise
Incident register
A quick “control to risk” map you can use with leadership
Control area | What it prevents or reduces | Typical proof an auditor or client will accept |
MFA and least privilege | Account takeover, unauthorised access | MFA enforcement settings, access reviews |
Patch management | Exploitation of known vulnerabilities | Patch reports, exception register |
Email security + DMARC | Phishing success, spoofed emails | DMARC records, mail security configurations |
Tested backups | Ransomware impact, extended outages | Restore test records, backup logs |
Centralised logging | Undetected breaches, weak investigations | Log retention settings, alert tickets |
Retention and minimisation | Excess exposure and breach scope | Retention schedule, disposal evidence |
Vendor access governance | Third-party breach pathways | Due diligence, contract clauses, access logs |
Incident response exercises | Slow containment and confusion | Tabletop minutes, updated playbooks |
A practical 30-60-90 day plan (focused on risk reduction, not paperwork)
This is a common approach for organisations that need measurable improvement within one quarter.
Timeline | Focus | Deliverables that show real progress |
Days 1-30 | Stop easy account compromise | MFA enforced on email and remote access, admin accounts reviewed, shared accounts removed |
Days 31-60 | Reduce “known exploit” and ransomware risk | Patch SLAs active, asset inventory baseline, backup restore test completed |
Days 61-90 | Improve detection and response | Central logging for key systems, priority alerts configured, incident tabletop completed |
If you are also building full compliance capability in 2026, PLMC’s broader implementation roadmap can help you sequence governance alongside controls: Data Protection Jamaica: Compliance Roadmap for 2026.
Common mistakes that look compliant but do not reduce risk
“We bought a tool” without changing access and process
A new security platform will not help if admin accounts are shared, MFA is optional, and alerts are ignored.
Policies that are not enforceable
If a policy says “encrypt laptops” but encryption is not technically enforced, the organisation is exposed.
Backups that are never tested
The only backup that matters is one you can restore within the required timeframe.
Vendor risk treated as procurement paperwork
Third parties often have persistent access. If you cannot see and control that access, you cannot manage the risk.
When to get outside help (and what to ask for)
You typically need support when:
You cannot clearly evidence controls (even if you think they exist)
You have complex vendor ecosystems or outsourced IT
You have had a near miss (phishing, suspicious logins, ransomware attempt)
You need privacy, legal, and technical teams aligned under one plan
A good engagement should produce outcomes like a prioritised control backlog, implementation support, role-based training, and an evidence pack you can maintain.
Frequently Asked Questions
What is the difference between data protection and cyber security? Data protection focuses on lawful, fair handling of personal data and the rights of individuals. Cyber security is the set of technical and operational controls that protect systems and data from unauthorised access, loss, or disruption. In practice, strong cyber security is essential to meeting data protection obligations.
Which control should we implement first to reduce breach risk? Enforce MFA on email, cloud applications, and remote access, then review privileged accounts. Credential theft is one of the fastest ways attackers reach personal data.
Do small businesses in Jamaica need the same controls as large organisations? The risk is often similar (phishing, ransomware, vendor access), but the implementation can be scaled. Focus first on MFA, patching, tested backups, and basic logging, then expand.
How do we prove our cyber security controls for compliance or client due diligence? Keep evidence such as configuration exports, access review records, patch and backup reports, incident tabletop notes, and vendor due diligence files. Evidence should be repeatable and tied to named owners.
Does data minimisation really help cyber security? Yes. Keeping less personal data, and deleting it on schedule, reduces the amount of data exposed in an incident and lowers the cost and complexity of response.
Reduce risk with a control plan you can defend
If you want to move from “we have policies” to controls that actually reduce risk, PLMC can help you prioritise, implement, and evidence a data protection cyber security programme aligned to your operations in Jamaica.
Explore PLMC’s services and request a free consultation at Privacy & Legal Management Consultants Ltd..
