
Data Privacy Act 2020: Myths vs Facts

Misinformation about Jamaica’s Data Protection Act, 2020 is one of the biggest hidden risks in otherwise well-run organisations. A single myth can lead to the wrong policy, the wrong contract clause, the wrong “quick fix” from a vendor, or the wrong response when an individual asks, “What data do you have on me?”
This article separates common myths vs facts in plain language, so leadership teams, HR, IT, marketing, finance, and operations can align on what the Act is really asking for in day-to-day practice.
Why Data Protection Act myths spread so easily
Most organisations do not set out to “get privacy wrong”. Myths usually come from a few predictable places:
GDPR bleed-over: People hear GDPR terms online and assume the exact same rules apply locally. There is overlap in concepts, but local legal requirements still need to be mapped to your operations in Jamaica.
Security-first thinking: Cyber security is essential, but privacy compliance is broader than firewalls and antivirus.
Policy theatre: A privacy policy looks official, so teams assume it equals compliance.
Vendor marketing: Tools can help, but tools rarely solve governance, accountability, and decision-making.
If your organisation has already started implementation work, PLMC’s resources on a practical path to compliance may be helpful for context: Data Protection Jamaica: Compliance Roadmap for 2026 and Privacy and Data Protection: A Practical Checklist.
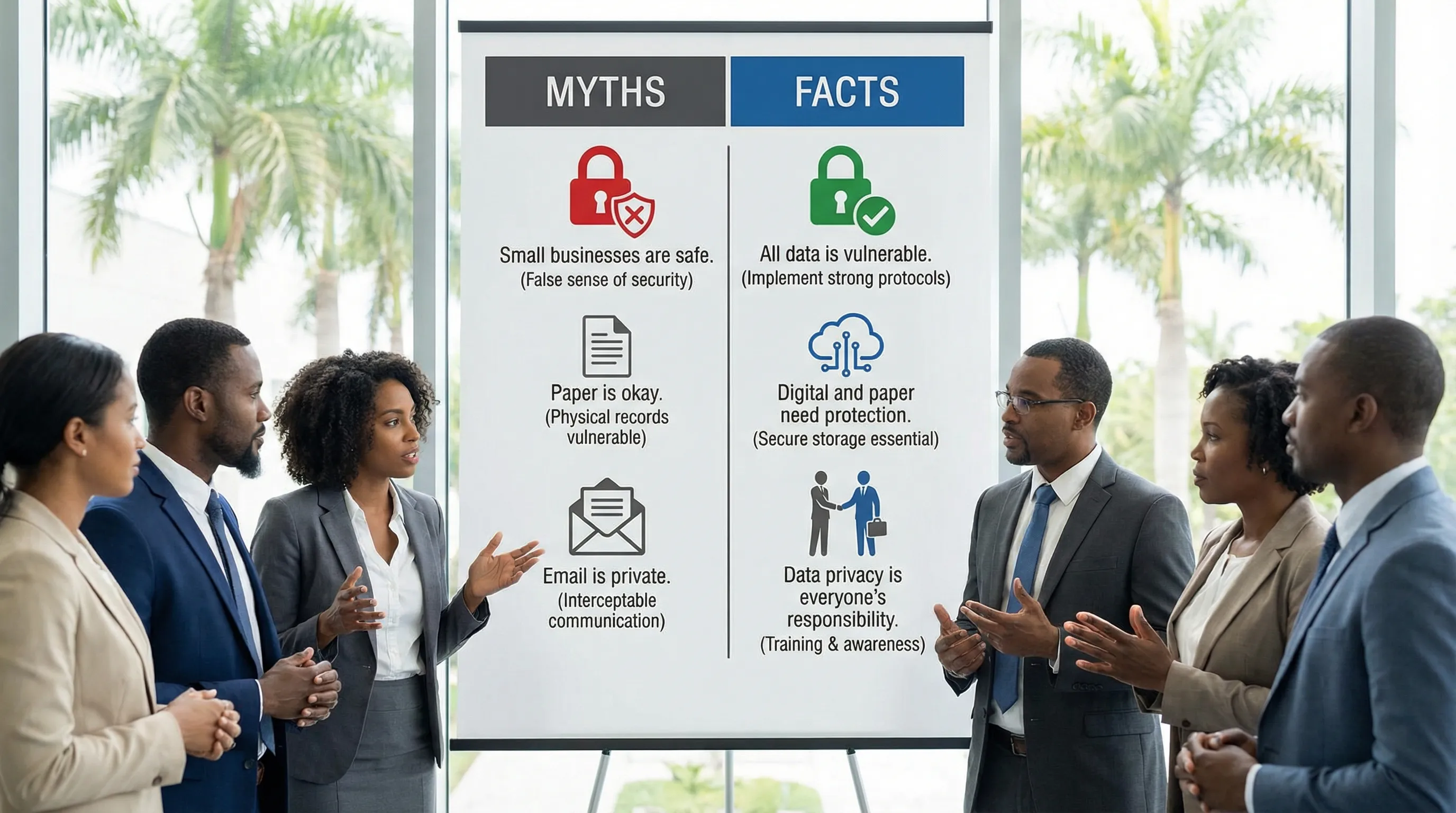
Data Privacy Act 2020: myths vs facts (quick reference)
Myth | Fact (what to do instead) |
“Consent is always required to use personal data.” | Consent is one possible basis, but not the only one. Focus on fair, lawful processing and clear communication. |
“Small businesses are exempt.” | Size does not remove risk. If you handle personal data, you need sensible controls that match your scale. |
“Privacy is an IT issue.” | Privacy is cross-functional: HR, marketing, finance, customer service, and procurement all make privacy-impacting decisions. |
“If data is publicly available, we can use it however we want.” | Public availability does not erase privacy obligations. Use must still be fair, relevant, and transparent. |
“A privacy policy on the website means we are compliant.” | Policies help, but compliance is evidenced by how you operate: inventories, access control, retention, training, and response workflows. |
“We can share customer data internally without limits.” | “Need to know” still matters. Internal sharing should align to purpose, access roles, and minimal use. |
“Cloud services are automatically non-compliant because data leaves Jamaica.” | Cross-border processing is not automatically prohibited, but it must be managed and governed (including vendor due diligence and transfer safeguards). |
“A breach only counts if we were hacked.” | Mis-sent emails, lost devices, unauthorised access, and accidental disclosures can also be incidents that need assessment and response. |
“Individuals can demand deletion of any data at any time.” | Individuals have rights, but organisations may have lawful reasons to retain certain records (for example, regulatory, contractual, or dispute-related). |
“One annual training session is enough.” | Training works best when role-based and ongoing, with reinforcement during onboarding and process changes. |
Myth 1: “Consent is always required”
Consent is often treated as the “safe” option, but over-relying on consent can backfire. If you ask for consent when you do not actually need it, you create a fragile process: when consent is withdrawn, teams panic, systems cannot adapt, and service delivery is disrupted.
What to do instead
Start by documenting:
What data you collect (and where it comes from)
Why you use it (purpose)
Who you share it with (internal and external)
How long you keep it (retention)
What control you rely on (your lawful condition or justification for processing)
A good privacy notice and a clear internal record of purposes often reduce the urge to “consent-wash” routine processing.
Myth 2: “Small businesses are exempt from the Data Protection Act”
In practice, some of the most sensitive datasets in Jamaica sit in smaller organisations: clinics, professional services firms, schools, retailers, and growing online businesses.
The reality is that privacy expectations scale with complexity, but the fundamentals remain the same. Even a small operation should be able to answer basic questions quickly:
What personal data do we hold?
Who can access it?
What happens when someone asks for access or correction?
What happens if an employee emails the wrong attachment to the wrong person?
If you do not have those answers, “small” can become “high risk” very quickly.
Myth 3: “Privacy is just cyber security”
Cyber security protects systems, but privacy governs use.
A strong security programme can still fail privacy tests if:
HR collects more information than needed “just in case”
Marketing reuses contact lists for new campaigns without checking expectations and purpose
Customer service shares account details without verifying identity
Procurement signs vendor contracts without data protection clauses and oversight
What to do instead
Treat privacy as governance plus operations. It needs decisions, ownership, and routine checks, not only technical controls.
Myth 4: “A privacy policy on our website means we’re compliant”
A policy is not evidence of implementation. Audits, complaints, and incidents usually test what you do, not what your PDF says.
Operational proof tends to look like:
A maintained data inventory (systems, datasets, owners)
A working process for individual requests (access, correction, objection, deletion where applicable)
Role-based access and joiner-mover-leaver controls
Vendor due diligence and contract clauses
Incident handling playbooks and decision logs
Retention and disposal routines
If you want a step-by-step view of operational controls, PLMC’s Practical Checklist is designed exactly for that.
Myth 5: “If it’s public, we can use it freely”
Teams often assume that information taken from social media, public directories, or public records can be copied, aggregated, and repurposed without restriction.
The fact is that public availability does not automatically make processing fair or aligned with people’s expectations. The key questions become:
Would the individual reasonably expect this use?
Is the use relevant to a clear purpose?
Are you being transparent about what you are doing?
Are you minimising what you collect and retain?
This is especially important for list-building, background screening, and community or customer profiling.
Myth 6: “We can share customer or employee data internally without limits”
Internal misuse is one of the most common real-world privacy problems because it is often normalised as “helping out”.
A practical standard is “need to know” access. Even inside the same organisation:
Finance should not automatically see full HR files
Front-line teams should not automatically see full ID documents if verification can be recorded without storing copies
Managers should not receive sensitive information in group chats where it is not necessary
Internal sharing should be tied to purpose and role, and supported by access controls and clear guidance.
Myth 7: “Cloud services are automatically non-compliant”
Cloud is not inherently incompatible with data protection. The risk is unmanaged cloud usage, shadow IT, and weak vendor governance.
What to do instead
When evaluating cloud tools (HR platforms, CRM, payroll, email marketing, file storage), focus on:
What personal data will be stored and processed
Where processing may occur (including support access)
Security measures and access logging
Sub-processors (who else may touch the data)
Contract terms (confidentiality, breach support, deletion/return of data)
Your internal configuration (permissions, sharing links, retention)
If your organisation is asking “Are we facing GDPR in Jamaica?”, reframe it. The better question is, “Are we managing cross-border processing and vendor controls in a way that meets our local legal obligations and our customers’ expectations?”
Myth 8: “A breach only counts if we were hacked”
Many incidents start with everyday mistakes:
Email sent to the wrong recipient
Attachment includes additional records accidentally
Lost laptop or USB drive
Ex-employee accounts left active
Customer information discussed where it can be overheard
What to do instead
Build a simple incident workflow that helps your team:
Recognise an incident quickly
Contain it (stop further disclosure)
Assess impact (what data, whose data, how sensitive)
Decide next steps (including whether notifications are required)
Document actions and lessons learned
PLMC’s earlier discussion of sensitive health information is a useful reminder that privacy is not theoretical. In many environments, health information is among the most sensitive data you can handle: COVID-19 results are protected by the Data Protection Act.
For additional background on incident response concepts, the NIST Computer Security Incident Handling Guide (SP 800-61) is a widely cited reference.
Myth 9: “Individuals can demand deletion of any data at any time”
Individuals’ rights matter, but organisations also have legitimate needs to retain specific records, such as payroll records, AML documentation, contractual records, or records required to manage disputes.
The real compliance task is not “delete everything on request”. It is:
Confirm identity and scope of the request
Identify where the data sits (systems, email, paper files)
Apply the right action (provide access, correct, restrict, delete where applicable)
Document what you did and why
Ensure retention schedules and legal holds are managed consistently
When retention is not defined, teams usually keep data forever, which increases breach impact and makes rights requests harder.
Myth 10: “One annual privacy training is enough”
Training is often treated as a compliance checkbox. But most incidents happen because staff are unsure in the moment.
What works better is role-based training tied to real tasks:
HR: recruitment data, medical notes, employee files, reference checks
Marketing: mailing lists, consent and preferences, profiling, third-party platforms
Customer service: identity verification, call handling, account changes
Finance and AML: due diligence records, data sharing, retention
IT: access management, logging, incident response, secure configuration
Reinforce training during onboarding, system rollouts, and policy changes. Short refreshers usually outperform a once-a-year lecture.
A “reality check” table: what regulators and stakeholders look for
If you want to replace myths with measurable action, align on evidence your organisation can actually produce.
Area | What “good” looks like in practice | Evidence you can keep |
Accountability | Clear owners for privacy decisions | Roles and responsibilities, meeting notes, decision logs |
Data visibility | You know what you hold and where | Data inventory, data flow maps |
Transparency | People can understand your processing | Privacy notices, internal scripts, collection statements |
Individual rights | Requests are handled consistently | Request log, templates, response timelines |
Vendor governance | Third parties are controlled | Due diligence records, contracts, assessments |
Security and access | Access is role-based and reviewed | Access reviews, joiner-mover-leaver records |
Retention | You keep data only as long as needed | Retention schedule, disposal records |
Incident readiness | You can respond under pressure | Incident plan, tabletop exercises, post-incident reviews |
How to use “myths vs facts” internally (without starting a blame game)
Privacy programmes fail when they feel like gotcha. They succeed when teams see privacy as a way to reduce rework, reduce incidents, and protect trust.
A practical approach is to run a short internal session where each department answers:
What personal data do we touch weekly?
What is the most likely mistake we could make?
What is one control we can implement this quarter?
From there, prioritise changes that reduce risk quickly, like tightening access, cleaning up shared drives, aligning retention, and standardising vendor reviews.
When you should get help
If your organisation is unsure whether its current processes match the Data Protection Act, myths are often the first warning sign. The second is when teams give inconsistent answers to basic questions about purpose, retention, sharing, and rights handling.
PLMC supports Jamaican organisations with data protection implementation, training, and broader governance, risk, and compliance integration. If you want to sanity-check where you are today and what to do next, you can request a consultation via Privacy & Legal Management Consultants Ltd. or start by aligning your internal plan to the Compliance Roadmap for 2026.
