
Privacy Management: How to Build a Program That Sticks

A privacy policy on the website is easy to publish. A privacy management program that actually changes day to day behaviour is harder, and it is what Jamaica’s Data Protection Act ultimately demands: not just intentions, but consistent, provable control over how personal data is collected, used, shared, stored, and disposed of.
If you want a program that sticks, treat privacy like a management system, not a project. That means clear ownership, repeatable workflows, training that matches real roles, measurable controls, and regular assurance. This article breaks down a practical approach you can run in a Jamaican organisation without creating a “privacy team of one” that burns out.
What “privacy management” means in practice
Privacy management is the operating discipline that keeps your organisation aligned with privacy principles over time, even as systems, vendors, staff, and products change.
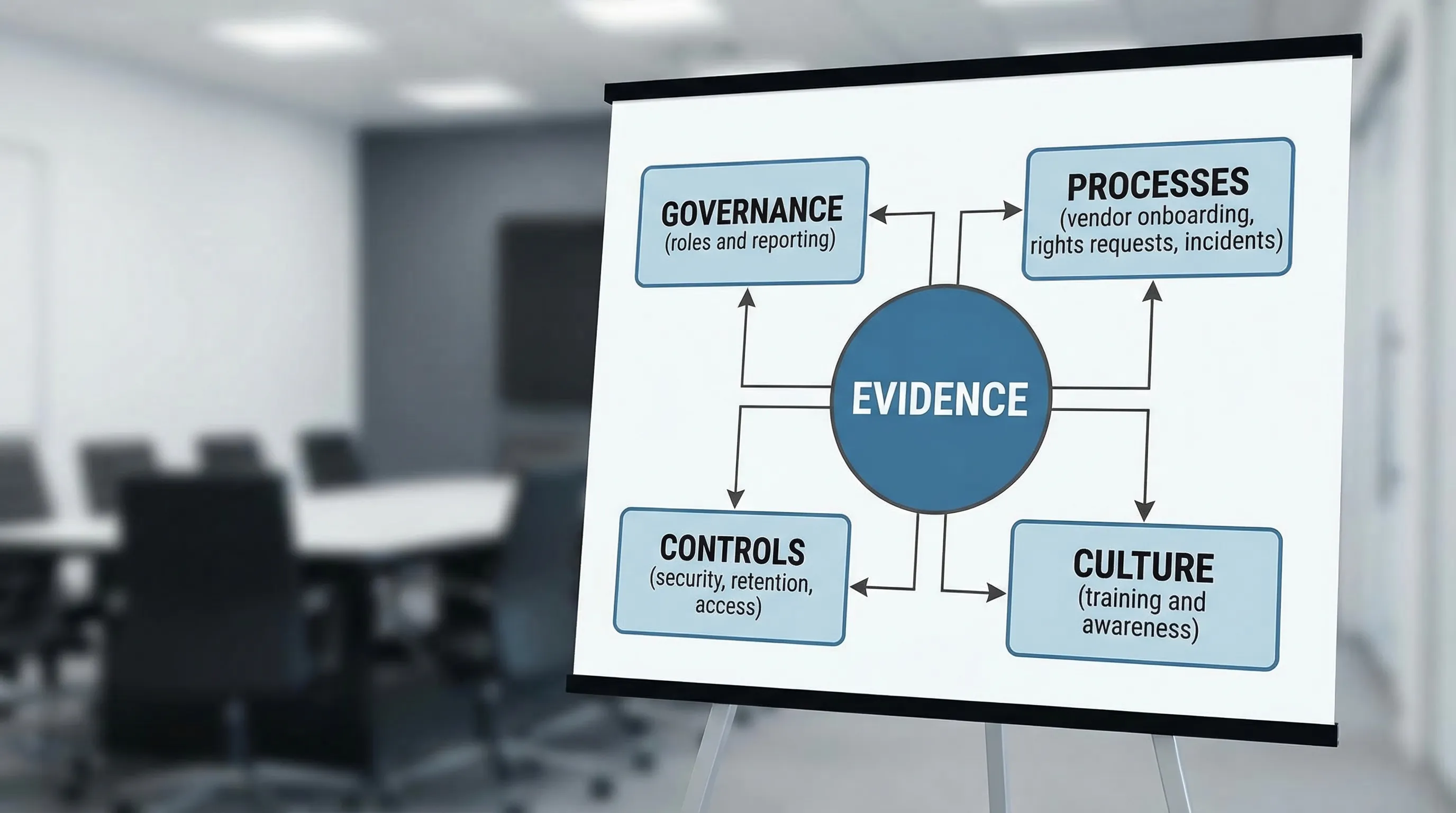
A program that sticks has three characteristics:
It is owned (executive sponsorship, defined responsibilities, and decision rights).
It is embedded (privacy is built into procurement, HR, IT change, marketing, and incident response, not handled as a last minute review).
It is evidenced (you can show what you do, when you did it, and how you know it works).
In other words, compliance is the outcome. Management is the mechanism.
Start with outcomes and scope (so the program doesn’t sprawl)
Before writing new policies or buying tools, define the outcomes you will manage to. In Jamaica, that typically includes:
Meeting the organisation’s obligations under the Data Protection Act (lawful processing, transparency, security, retention, rights handling, vendor oversight, and breach readiness).
Reducing operational risk (privacy incidents, complaints, reputational harm, and contract failures).
Improving trust with customers, citizens, patients, students, or employees.
Then set scope with precision:
Entities and locations: one company vs group, Jamaica only vs multi-country operations.
Data domains: customer, HR, vendor contacts, CCTV, marketing lists, health information, minors’ data.
Systems and channels: core apps, spreadsheets, WhatsApp usage, paper files, call recordings.
A good scope statement prevents the classic failure mode where privacy becomes “everything everywhere”, and therefore gets done nowhere.
Build a privacy operating model (people first, documents second)
Most privacy programs fail because responsibilities are vague. “IT handles it” is not a control. Neither is “Legal will review.”
Instead, define an operating model with named roles and clear handoffs.
Minimum roles that make a program stick
You do not need a large department, but you do need coverage:
Board and senior leadership: approve risk appetite, receive reporting, unblock resourcing.
Executive sponsor: ensures privacy is prioritised across departments.
Privacy lead / DPO function (formal title may vary): owns the program, coordinates responses, maintains the control framework.
Information security lead: aligns security controls, incident response, access management, and logging.
HR: ensures employee data processing, onboarding, exits, and training discipline.
Procurement / vendor management: manages due diligence, contract clauses, and supplier reviews.
Business owners: own processing activities and make decisions on lawful basis, retention, and data sharing.
A simple RACI keeps decision making fast
Use a RACI matrix for recurring activities so everyone knows who is Responsible, Accountable, Consulted, and Informed. Keep it short and tied to real workflows.
Privacy activity | Accountable (A) | Responsible (R) | Consulted (C) | Informed (I) |
Approve privacy risk appetite and program objectives | CEO / Board sponsor | Privacy lead | InfoSec, Legal, Risk | Leadership team |
Maintain record of processing and data inventory updates | Privacy lead | Business process owners | IT, HR, Procurement | Internal audit |
Vendor onboarding and contract privacy clauses | Head of Procurement | Vendor manager | Privacy lead, InfoSec, Legal | Business owner |
Data subject requests workflow | Privacy lead | Service desk / assigned team | HR, IT, Legal | Executive sponsor |
Incident response and breach assessment | InfoSec lead | IR team | Privacy lead, Legal, Comms | CEO / Board sponsor |
This table is not meant to be “perfect.” It is meant to stop confusion when the first urgent request or incident arrives.
Make privacy part of how work flows (the stickiness lever)
If privacy only lives in a policy binder, it will be forgotten. The program becomes durable when privacy checks happen at the same moments the business already makes decisions.
Here are high impact embed points.
1) Change management and projects (privacy by design)
Any time the organisation introduces a new system, form, camera, tracking tool, AI feature, vendor, or data sharing arrangement, privacy risk changes.
Add lightweight privacy steps into your project lifecycle:
A short intake (what data, whose data, why, where stored, who has access, who it is shared with).
A trigger for a DPIA-style assessment when risk is higher (sensitive data, large scale monitoring, new technology, children’s data, cross-border transfers).
A “go live” gate that verifies minimum controls (notice updates, retention, access roles, logging, vendor terms).
If you already have a change advisory board (CAB) or ITIL-style process, add privacy as a standing checkpoint rather than an email at the end.
2) Procurement and vendor onboarding
Vendor risk is where privacy programs quietly break. A supplier’s breach becomes your incident, and poor contracts make remediation difficult.
Embed privacy into procurement by standardising:
A vendor questionnaire that matches risk (short for low risk vendors, deeper for processors hosting personal data).
Contract clauses covering confidentiality, sub-processors, breach notification, deletion/return, audit rights, and cross-border transfers.
A go/no-go rule for vendors that cannot meet minimum security and privacy expectations.
This also applies to services that process sensitive HR and health information. For example, if your organisation uses online platforms to arrange employee benefits abroad, treat that as a vendor processing sensitive data. If you have staff in the UAE and need a way to compare and purchase cover efficiently, use a reputable platform and still do your diligence, for instance compare and buy health insurance online in the UAE with clear internal rules on what employee data is shared, who can access it, and how long it is retained.
3) HR lifecycle (privacy where employees feel it most)
Employee data is often widely accessible and poorly retained. Your HR workflows should include:
Standard access profiles (who can see what, and why).
Controlled sharing (especially for medical notes, disciplinary matters, and background checks).
Defined retention and disposal practices for files, emails, and paper records.
Exit procedures that remove access and secure handover of laptops, phones, and paper files.
4) Marketing and customer communications
Marketing teams move fast, and that is where consent, transparency, and data minimisation are often strained.
Make “privacy safe marketing” easier by providing:
Approved templates for notices and sign-up language.
A list hygiene process (source tracking, suppression lists, opt-out handling).
Simple rules for using third party audiences, pixels, and tracking.
Build “living” data visibility (so the inventory stays current)
Most organisations can build a data inventory once. The hard part is keeping it accurate.
To make it stick, connect your inventory to events that force updates:
New vendor onboarding.
New system or major feature release.
New form or data collection channel.
Department restructure or new business line.
Incident or complaint.
Also assign clear ownership at the process level. The privacy lead maintains the framework, but each department owns the accuracy of its processing information.
If you want an external structure for documentation, the NIST Privacy Framework is a practical reference for organising activities (Identify, Govern, Control, Communicate, Protect) without turning the program into a purely legal exercise.
Turn policies into procedures (and procedures into habits)
Policies state intent. Procedures drive action. Habits drive consistency.
A program that sticks typically has a small set of procedures that are actually used, such as:
Rights request handling (intake, identity verification, triage, response, extensions, logging).
Incident response privacy steps (assessment, containment, notification decisions, documentation).
Vendor due diligence and contract review.
Retention and disposal process (including legal holds).
Access reviews for key systems.
Keep procedures short, and test them in the real world. If a rights request arrives today, could your team respond consistently without improvising?
Training that changes behaviour (role-based, measurable, repeated)
Annual training alone rarely sticks, especially if it is generic. Effective privacy awareness looks more like an ongoing safety program.
What to train (by role)
Aim for role-based training rather than one slide deck for everyone:
All staff: recognising personal data, phishing hygiene, clean desk, secure sharing, reporting incidents.
HR and people managers: sensitive employee data, retention, sharing rules, access controls.
Customer-facing teams: identity verification, handling recordings, complaints, rights requests.
IT and developers: access management, logging, encryption, privacy by design checks.
Procurement: processor vs controller thinking, vendor red flags, contract essentials.
How to know training is working
Measure it with simple indicators:
Completion rates by department and role.
Spot checks (can staff identify what is sensitive data, and where to report a suspected incident?).
Reduction in recurring errors (misdirected emails, uncontrolled spreadsheets, unauthorised sharing).

Metrics and reporting (what you track is what you improve)
Privacy management becomes credible when leadership can see performance trends, not just hear reassurance.
Use a balanced set of operational and risk indicators. Keep them stable for at least two quarters so you can trend.
Metric area | Example metric | What it tells you |
Rights requests | Average time to acknowledge and close | Whether the workflow is working under real demand |
Vendor governance | Percentage of high risk vendors with completed reviews | Whether supplier risk is controlled |
Incidents | Number of privacy incidents by type and root cause | Where behaviour and controls are failing |
Training | Completion and spot-check pass rate by function | Whether awareness is reaching the right roles |
Data hygiene | Percentage of systems with defined retention rules | Whether data is being kept longer than necessary |
Report a small dashboard monthly to management, and provide a deeper quarterly report to the board sponsor.
Assurance: test the program before it is tested for you
A program that sticks includes regular assurance activities, not only after a complaint.
Practical options:
Tabletop exercises: run a breach simulation with IT, privacy, legal, and communications.
Rights request drills: test your identity verification and response process.
Access reviews: confirm that “least privilege” is real for high risk systems.
Vendor checks: verify that a key supplier’s controls and sub-processors still match what you agreed.
If your organisation has internal audit, align on what evidence they need and when they will review privacy controls.
Integrate privacy with GRC and cyber security (so it survives budget season)
Privacy initiatives are more resilient when they are connected to enterprise risk management, cyber security, and compliance reporting.
That integration usually includes:
Mapping privacy risks into the enterprise risk register.
Aligning privacy controls with security controls (for example, access management, logging, encryption, endpoint protection, secure configuration).
Coordinating incident response so privacy assessment is part of the core security playbook.
Where relevant, organisations also look to management system standards for structure. ISO/IEC 27701 (a privacy extension to ISO/IEC 27001) can be helpful as a reference model, especially for organisations with mature information security practices.
A realistic implementation rhythm (90 days to traction, 12 months to maturity)
Programs stick when they deliver visible progress quickly, then institutionalise the work.
A practical rhythm looks like:
First 30 to 90 days: stabilise and prioritise
Focus on what reduces risk quickly:
Confirm sponsor, roles, and escalation routes.
Establish the minimum workflows (rights requests, incidents, vendor onboarding).
Identify and fix your top three data risk areas (often uncontrolled spreadsheets, weak vendor terms, over-retention).
Months 3 to 6: embed into business operations
Add privacy checks into projects and procurement.
Roll out role-based training.
Produce your first management dashboard.
Months 6 to 12: assure and improve
Run exercises and targeted audits.
Improve documentation quality and evidence.
Mature metrics, and adjust controls based on incident trends.
The key is to avoid waiting for the “perfect” inventory or the “final” policy pack. Stickiness comes from usage, not from volume.
Common reasons privacy programs fail (and how to prevent them)
A few patterns show up repeatedly:
The privacy lead owns everything: fix it with distributed ownership and a clear RACI.
Too many documents, too few workflows: fix it by prioritising procedures that teams actually run.
No measurement: fix it with a small, stable set of KPIs and quarterly reporting.
Training is generic: fix it with role-based sessions tied to real incidents and real systems.
Vendor risk is ignored: fix it by making privacy due diligence a procurement default, not an exception.
How PLMC can help
If you want privacy management that sticks, outside support is most valuable where it accelerates execution and strengthens evidence. Privacy & Legal Management Consultants Ltd. (PLMC) supports Jamaican organisations with data protection implementation, GRC integration, cyber security services, risk assessment tools, and training, including practical sessions tailored to your teams.
If you are building or reworking your privacy program for 2026, a short scoping call can help you identify the highest impact embed points, confirm your operating model, and set a realistic implementation plan. Learn more at Privacy & Legal Management Consultants Ltd..
