
Privacy and Compliance: How to Avoid Costly Mistakes

Privacy and compliance failures rarely start with bad intent. They usually start with a rushed project, a “quick” spreadsheet of customer data, an unchecked vendor contract, or a well-meaning employee emailing a file to the wrong person.
The costs add up fast, regulatory exposure, operational disruption, incident response spend, and reputational damage that can linger for years. Globally, the average cost of a data breach reached USD $4.88 million in IBM’s 2024 report, a reminder that even a single preventable lapse can become a board-level event for any organisation, not just large multinationals (IBM Cost of a Data Breach Report).
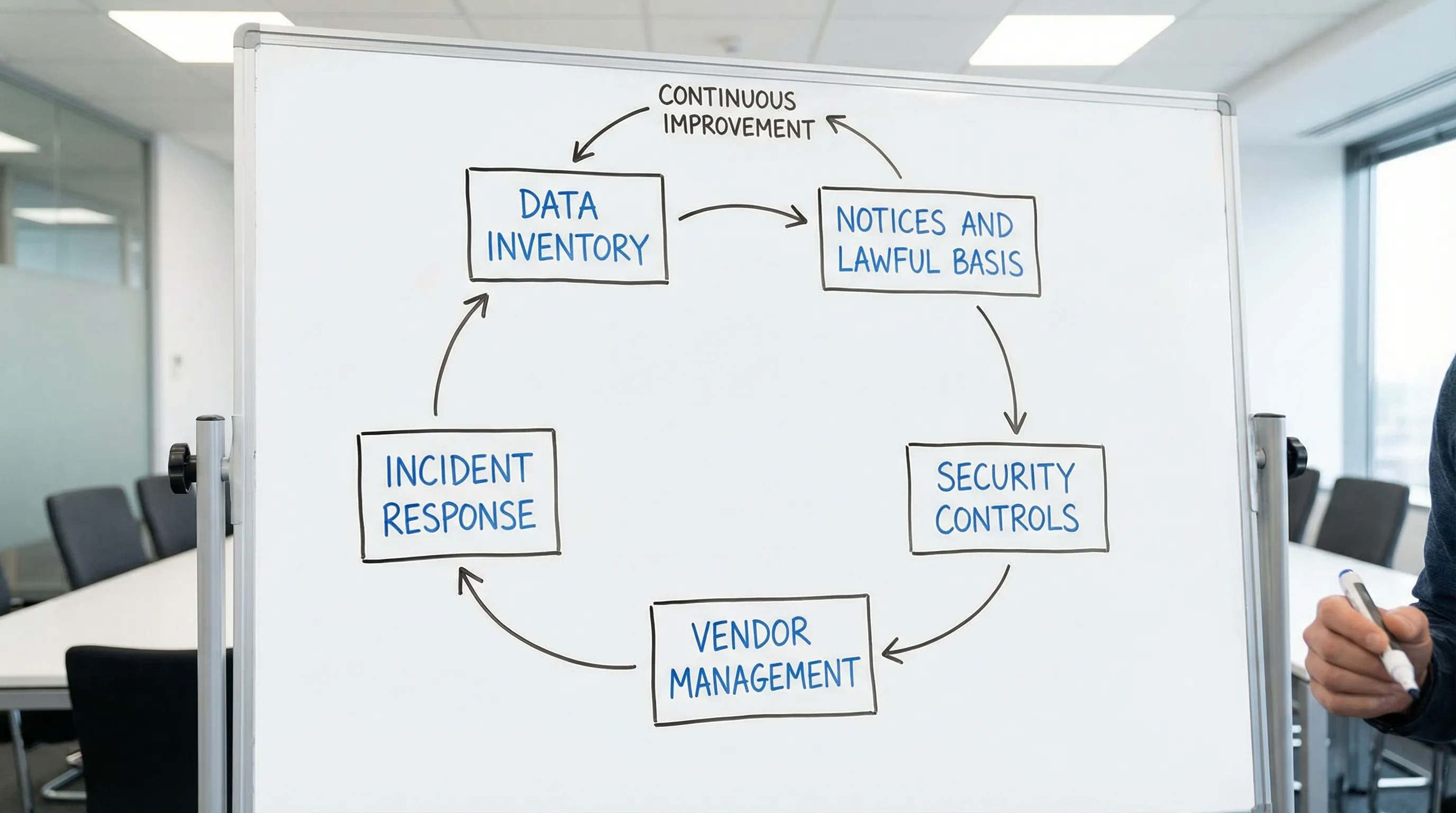
For Jamaican organisations aligning to the Data Protection Act, the goal is not to “write policies” and hope for the best. The goal is to build a workable, provable privacy and compliance operating model that stands up in real life.
What “costly mistakes” look like in practice
Most costly privacy and compliance problems fall into one of four buckets:
Uncontrolled personal data sprawl (too many copies, unknown locations, unclear owners).
Mismatched expectations (what you told people you would do vs what you actually do).
Weak third-party governance (vendors, cloud tools, payroll processors, marketing platforms).
Poor incident readiness (no clear plan, slow detection, inconsistent reporting).
The good news is that these failures are predictable. Better, they are preventable when you treat privacy like an operational risk and manage it the same way you manage finance, safety, or AML obligations.
The privacy and compliance mistakes that most often become expensive
Below are the mistakes that most often trigger enforcement risk, customer complaints, incident response costs, and executive time drains. Each one includes what to change so you can avoid repeating it.
Mistake 1: Treating privacy as a one-off project instead of ongoing governance
Many organisations rush to produce policies, a notice, and a training slide deck, then move on. But privacy compliance changes whenever the business changes, new systems, new vendors, new marketing campaigns, new data uses.
What to do instead: establish clear ownership and review rhythms.
Assign accountable owners for privacy governance (not just “everyone”).
Create a simple change trigger: new system, new vendor, new data collection point, or new use of data means a privacy review.
Report privacy risk and progress to leadership on a schedule (quarterly works for many organisations).
Mistake 2: Not knowing what personal data you have, where it lives, and why you keep it
You cannot protect what you cannot find. A common failure mode is having partial data inventories that ignore:
Shared drives and email inboxes
Portable storage and exported reports
CRM and marketing tools
HR files and contractor records
Customer support call logs and recordings
What to do instead: build a living data inventory that is usable, not perfect.
A practical inventory should capture: data category, purpose, lawful basis (where applicable), system/location, access roles, retention period, and key vendors.
Mistake 3: Copying privacy notices that do not match reality
Privacy notices are not marketing text. If your notice is generic, outdated, or borrowed from a different jurisdiction, it can create instant credibility and compliance problems.
What to do instead: align transparency to actual processing.
Map each collection point (web forms, onboarding, CCTV signage, call recordings, applications).
Ensure the notice reflects the real purposes, recipients, retention approach, and rights process.
Update notices when you introduce new tools or new uses of personal data.
Mistake 4: Using “consent” as the default legal basis for everything
Consent is often overused because it feels straightforward. In reality, consent has operational requirements: it must be informed, specific, and freely given, and people must be able to withdraw it.
What to do instead: choose a lawful basis you can support operationally.
If you rely on consent, build withdrawal and preference management into your process. If you rely on other bases (for example, contractual necessity or legal obligation in relevant contexts), document your reasoning and align it with how the business actually operates.
Mistake 5: Ignoring retention, then discovering you have years of data you cannot justify
Over-retention increases breach impact and complicates rights requests. It also increases your e-discovery and investigation workload during disputes.
What to do instead: define retention rules and make them executable.
Retention is not only a policy statement. It needs:
A retention schedule tied to business purpose and legal requirements
A disposal process (including secure deletion and destruction)
A review cadence for long-lived datasets (HR, customer history, CCTV)
Mistake 6: Weak access control and “everyone can see everything” permissions
One of the most common causes of internal incidents is excessive access, especially for shared mailboxes, spreadsheets, HR folders, and CRM exports.
What to do instead: implement least privilege and prove it.
Use role-based access, remove stale accounts, and log access to sensitive datasets. Align your controls with recognised guidance such as the NIST Cybersecurity Framework, which remains a useful reference for governance and security outcomes.
Mistake 7: Poor third-party and vendor management (including cloud services)
Vendors often touch the most sensitive information: payroll, background checks, benefits, call centres, marketing automation, SaaS CRMs, and IT support.
What to do instead: treat vendor risk as part of your privacy programme.
At minimum, ensure:
Contracts clearly define roles and responsibilities (controller/processor style responsibilities where relevant)
Security requirements are explicit (access control, incident notification expectations, sub-processor rules)
You keep a vendor register and review high-risk vendors periodically
Mistake 8: No tested process for access requests, correction, deletion, and complaints
It is easy to say “contact us for requests.” It is harder to actually deliver within timelines, verify identity, locate all the data, and respond consistently.
What to do instead: build a simple, repeatable request workflow.
Define an intake channel, identity verification rules, search steps (by system), review and approval, and response templates. Then test it with a dry run.
Mistake 9: Over-collecting sensitive data “just in case”
Organisations often collect copies of IDs, medical information, or detailed demographic data without a clear operational need. This increases risk and complicates security.
What to do instead: apply data minimisation at the point of collection.
Challenge every field in a form. If you cannot explain why you need it, how long you keep it, and who uses it, remove it or make it optional.
Mistake 10: Treating incidents as rare events instead of planned scenarios
Even with strong controls, incidents happen. What makes them costly is confusion: unclear roles, delayed escalation, inconsistent messaging, and missing evidence.
What to do instead: define and rehearse an incident response plan.
Use a short playbook: detect, contain, assess impact, decide notifications, remediate, and document lessons learned. Tabletop exercises are one of the highest ROI activities for privacy and compliance maturity.
A quick “risk to evidence” view (what auditors and stakeholders look for)
Privacy and compliance is easier to defend when you can show evidence, not only intent.
Common mistake | What it turns into | What you should be able to show | Practical evidence examples |
No clear ownership | Tasks fall through gaps | Assigned accountability | Role descriptions, committee terms, meeting notes |
No data inventory | Unknown exposure | Understanding of data flows | Data map, system register, vendor register |
Generic privacy notice | Complaints and mistrust | Transparency aligned to reality | Notices per channel, version history |
Excess access | Internal leak risk | Least privilege controls | Access reviews, IAM policies, logs |
Weak vendor controls | “Shadow processing” | Oversight of processors/vendors | Due diligence, contracts, assessments |
No retention execution | Over-retention | Consistent disposal | Retention schedule, deletion tickets |
No rights workflow | Missed deadlines | Repeatable process | Intake log, templates, search procedure |
Untested incident plan | Slow response | Readiness and learning | IR playbook, tabletop outputs, actions tracked |
Build guardrails that stop mistakes before they happen
A strong privacy and compliance programme is not just documentation. It is a set of operational guardrails that make the right action the easiest action.
1) Embed privacy into change management
Most risk arrives through change: a new HR platform, a new marketing campaign, a new customer onboarding flow, a new outsourcing partner.
Add a lightweight privacy checkpoint into:
Procurement (before signing)
IT change approvals (before go-live)
Marketing campaign launches (before sending)
HR process changes (before collecting new employee data)
2) Standardise assessments for higher-risk activities
Some activities consistently justify extra scrutiny: large-scale customer data, sensitive data, monitoring technologies, cross-border processing, and new analytics uses.
A consistent assessment template helps you avoid relying on memory or individual judgment. It also creates an audit trail that shows you took reasonable steps.
3) Train for behaviour, not awareness
“Privacy training” fails when it is generic and annual. People need role-based, scenario-based guidance that reflects how work is actually done.
Examples that change behaviour:
How to share files securely with vendors
How to verify identity before releasing information
How to handle misdirected emails and accidental disclosures
What to do when a customer asks to “delete everything”
PLMC provides training sessions and educational resources that can be tailored to these operational scenarios, so teams practice the decisions that prevent real-world incidents.
A special risk area in 2026: AI tools, automation, and “silent” data sharing
Many teams now use AI-enabled tools for drafting emails, summarising customer calls, analysing spreadsheets, or supporting HR and customer service workflows. The privacy and compliance risk is rarely the model itself. It is what happens to your data when it enters that tool.
Common costly mistakes here include:
Uploading personal data into tools that are not approved by the organisation
Not understanding where data is processed or stored
No clear contractual terms on data use, retention, and sub-processors
Deploying automated decision logic without documented reasoning and governance
How to reduce AI-related privacy risk:
Create an approved-tool list and a “do not upload” rule for certain data categories
Treat AI tools like any other vendor, due diligence, contractual protections, and access controls
Require a short assessment for AI use cases that touch personal or sensitive information
Provide targeted training so staff understand what is permitted and why
If your organisation is moving quickly with automation and wants an independent view of where AI creates privacy and compliance exposure, an external AI audits and training partner can help you identify high-risk data flows and prioritise controls without slowing down productivity.
Proving compliance: what to keep in your “evidence pack”
When a regulator, client, bank partner, or board asks “Are we compliant?”, the most credible answer is supported by a small set of current, organised artefacts.
An evidence pack should be easy to produce and maintain, and it should show what you do, not only what you intend.
Data inventory (and last review date)
Record of key policies and procedures (privacy, retention, incident response)
Training records (who completed what, when)
Vendor register and high-risk vendor reviews
Rights request log (even if volume is low)
Incident log and lessons learned (including near misses)
Management reporting (risk register items, actions, status)
When to get help (and how PLMC can support)
Some organisations can move quickly with internal leadership. Others benefit from external support when:
You have complex vendor chains or heavy outsourcing
You operate across borders or rely on cloud systems with regional processing
You are scaling quickly and personal data is spreading into more tools
You need to demonstrate compliance to clients, regulators, or partners with confidence
Privacy & Legal Management Consultants Ltd. supports Jamaican organisations with data protection implementation, GRC integration, cyber security services, risk assessment tools, and training, including free consultations to help you identify your highest-impact gaps first.
Costly mistakes in privacy and compliance are rarely mysterious. They are usually visible, measurable, and fixable, once you build the right guardrails and keep the evidence that proves they work.

