
Data Protection Training Courses: What to Teach by Role

Most organisations do not fail data protection because they do not have a policy. They fail because day to day work does not match the policy.
That is why data protection training courses work best when they are role-based. A receptionist, a payroll clerk, a system administrator, and a director do not face the same privacy risks, and they do not need the same depth of instruction. In Jamaica, where the Data Protection Act sets expectations around fair processing, security, accountability, and rights handling, role-based training also makes it easier to demonstrate compliance with credible evidence.
Below is a practical way to structure what to teach by role, including topics, exercises, and what “proof of training” should look like.
Start with the outcome: what should each role be able to do?
Before you build a slide deck, define measurable outcomes per role. Good outcomes describe actions, not awareness.
Examples of outcomes:
A customer service agent can correctly verify identity before discussing an account.
HR can explain what belongs in an employee file, and what does not.
Marketing can run a campaign without repurposing data in a way that conflicts with the original purpose.
IT can classify a security event and trigger the internal incident process.
Executives can ask for the right metrics and approve risk treatment.
Once outcomes are clear, your training course becomes easier to scope, assess, and refresh.
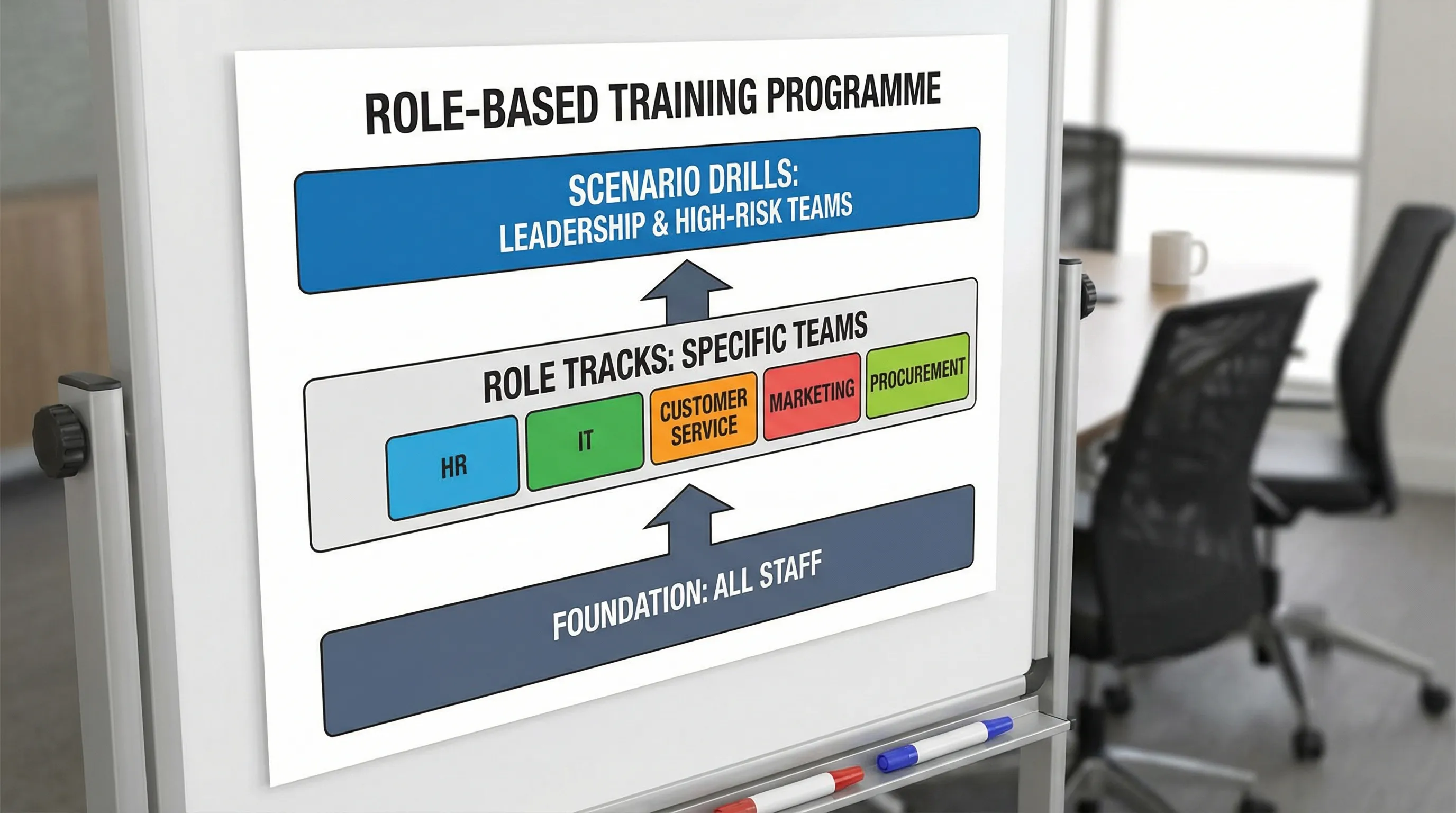
A simple training architecture that works in Jamaican organisations
Most organisations need three layers, delivered on a predictable cadence.
1) Foundation training (everyone)
This is baseline literacy. It should be short enough to finish and memorable enough to change behaviour.
2) Role tracks (by function)
These sessions go deeper into the specific ways each team collects, uses, discloses, stores, and deletes personal data.
3) Scenario drills (management and high risk teams)
These are tabletop exercises for incidents, rights requests, vendor failures, and “pressure moments” (for example, an urgent executive request for employee data).
A practical cadence for many organisations is:
Onboarding: foundation within the first 2 weeks.
Annual refresher: foundation for all staff.
Role track refreshers: every 12 to 18 months, or sooner after major process changes.
Drills: at least annually for incidents and rights requests.
The foundation module: what every employee should learn
Foundation training should be consistent across the company and anchored in your own processes (who to contact, how to report, what systems are approved).
Core topics to include:
Personal data basics (in plain language)
Cover what personal data is in your context, and what makes data sensitive or higher risk (for example, ID numbers, financial information, health data, biometrics, children’s data).
The “why it matters” that staff actually feels
Make consequences real:
Harm to individuals (identity fraud, embarrassment, unfair treatment).
Operational disruption (investigations, downtime, customer churn).
Legal and contractual impact (regulatory attention, partner audits).
Avoid fear tactics, but show what a mistake looks like in your environment.
Everyday privacy rules
Teach specific behaviours your staff can apply immediately:
Verify identity before disclosure.
Use approved channels for sharing data.
Keep data to the minimum needed for the task.
Do not forward work files to personal email or WhatsApp.
Lock screens and protect paper records.
Report suspected incidents quickly.
Recognising and reporting a privacy incident
People should know that incidents are not only “hacks”. Include examples like:
Sending a spreadsheet to the wrong recipient.
Losing a laptop or USB drive.
Posting personal data in a group chat.
Giving information over the phone to an impersonator.
Tie this to your internal escalation path, including who receives the report and what information is needed.
Rights requests: what staff must do (and must not do)
Most staff do not have to fulfil a rights request, but they must recognise one and route it correctly. Provide wording examples such as:
“Can you tell me what information you have on me?”
“Delete my account.”
“Stop using my number.”
Teach staff not to argue, delay, or disclose data before identity checks are completed.
What to teach by role (with practical scope)
The goal is to teach each team how the Data Protection Act principles show up in their workflows. The table below gives a clean way to plan your course catalogue.
Role / audience | What they do with personal data | What to teach (minimum) | Best assessment method |
Board, CEO, executives | Approve strategy, accept risk, set culture | Accountability, governance expectations, risk appetite, reporting dashboards, resourcing, incident decision making | Short executive briefing plus tabletop exercise |
People managers | Collect performance, attendance, discipline info | Data minimisation, sharing boundaries, retention basics, “need to know” access, handling complaints and employee rights | Scenario based discussion |
HR and payroll | Process high volumes of sensitive employee data | Lawful and fair processing in employment, file hygiene, ID handling, reference checks, medical info handling, vendor oversight (payroll, benefits), access logging | Case studies, file review checklist |
Customer service / front office / call centre | Disclose account and identity information daily | Identity verification scripts, secure authentication, handling third party callers, secure notes, dealing with pressure, escalation of rights requests | Role play plus short quiz |
Marketing and sales | Use contact data for outreach and campaigns | Purpose limitation, transparency and notices, preference management, lead lists, data sharing rules, working with agencies, measuring without over-collecting | Campaign review exercise |
IT and cyber security | Implement access controls, logging, backup, monitoring | Privacy by design basics, access management, encryption, vulnerability management, secure configuration, incident handling coordination, vendor access, data disposal | Technical checklist and incident drill |
Procurement and vendor owners | Engage processors and cloud vendors | Due diligence questions, contract clauses, sub-processors, cross-border considerations, ongoing monitoring, offboarding vendors and returning data | Vendor assessment workshop |
Legal, compliance, risk | Interpret obligations, manage investigations | Records of processing, DPIA style risk assessment, complaint response, breach evaluation, audits, policy control | Practical walkthrough of templates |
Records management / admin | Store and destroy paper and digital records | Retention schedules, secure storage, destruction methods, scanning controls, archiving discipline | Spot check and process audit |
Use this table as a training matrix. It becomes evidence for audits, partner questionnaires, and internal accountability.
Executive and board training: governance, metrics, and decision rights
Leadership training is not a longer version of staff training. It should focus on governance decisions leaders must make.
Teach executives:
What accountability looks like in practice
Cover the minimum governance elements leaders should sponsor:
Clear ownership for privacy (who is responsible for what).
Approval of policies that actually match operations.
Budget for controls and training.
Oversight of high risk processing (for example, biometrics, large scale profiling, children’s data).
The metrics leaders should demand
Many organisations report activity, not risk. Good board level indicators include:
Volume and age of open rights requests.
Number of incidents by type (mis-send, lost device, unauthorised access).
Vendor risk status (high risk vendors with overdue reviews).
Completion rates for training by role.
Results of breach and rights request drills.
Incident decision making
Leaders should know their role in:
Approving communications.
Deciding when to engage counsel, insurers, forensic support, and PR.
Ensuring fast containment and a credible post-incident improvement plan.
People managers: prevent “informal” disclosures
Managers often leak personal data unintentionally, especially over messaging apps, shared drives, and quick hallway conversations.
Teach managers:
What “need to know” means for staff data.
How to share team updates without exposing unnecessary personal details.
How to respond when another manager asks for information they are not entitled to.
How to document performance and disciplinary issues without including irrelevant personal information.
A good exercise is a “manager request” scenario: one manager asks for employee health details to “help with scheduling”. Participants must decide what can be shared, what cannot, and what approvals are required.
HR and payroll: treat the employee file like a controlled system
HR teams need deeper training because they process high risk data under tight timelines.
Include these topics:
Collection and file hygiene
What to collect at hiring, and what not to collect.
Handling IDs and proof of address, including secure copying and storage.
Separating medical and accommodation documentation from general HR files where appropriate.
Transparency and internal notices
Employees should understand how their data is used. Training should equip HR to:
Explain internal notices in clear language.
Respond consistently to employee questions.
Payroll, benefits, and third parties
Many HR risks are vendor risks. HR should learn how to:
Confirm the vendor’s role (processor or independent controller) and responsibilities.
Verify secure file transfer methods.
Ensure termination and offboarding includes access removal and data return or deletion.
Responding to employee rights requests
HR should know the internal workflow, the identity verification steps, and how to avoid over-disclosure (for example, when records contain information about other employees).
Customer service and reception: identity verification under pressure
Front line teams experience the highest volume of real-time disclosure decisions. Training must be practical and scripted.
Teach:
A consistent verification method
What identifiers staff may ask for.
What staff must not ask for (especially if it creates new risk).
How to handle third party callers (spouses, “co-workers”, “someone from the bank”).
Safe channels and safe notes
Where customer data can be recorded.
How to avoid writing sensitive information in free-text notes.
When to pause a conversation and escalate.
“Pressure moment” scenarios
Run role play exercises:
An angry customer demands information quickly.
A caller claims to be the customer but fails verification.
A senior employee asks the front desk to print a list of visitors that includes phone numbers.
Marketing and sales: purpose limitation and trust by design
Marketing teams often create risk through repurposing data, buying lists, or using new tools without governance.
Teach:
Purpose and transparency
Use data only in ways people would reasonably expect based on your notices and relationship.
Keep privacy notices aligned to actual practices.
Consent and preferences (where relevant)
Even where consent is not the only lawful route, preference management is a trust requirement. Marketing should learn:
How to document opt-outs and honour them across systems.
How to avoid creating “shadow lists” that bypass controls.
Working with agencies and platforms
What information can be shared with an agency.
How to approve ad platform integrations.
How to minimise data in analytics.
A useful exercise is a campaign review: teams bring a real campaign concept and check it against a privacy checklist before launch.
IT and security: privacy controls are security controls plus accountability
IT training should bridge cyber security and privacy governance.
Teach:
Access control as a privacy control
Role-based access and least privilege.
Joiner, mover, leaver processes.
Logging and monitoring for inappropriate access.
Secure configuration and data protection
Encryption in transit and at rest where appropriate.
Patch management and vulnerability scanning.
Backups and restoration testing.
Where helpful, you can align training with recognised guidance like the NIST Privacy Framework and ISO/IEC 27001 concepts, adapted to your organisation’s scale.
Incident response integration
IT should understand how privacy incident handling intersects with:
Legal and compliance assessment.
Communications.
Evidence preservation.
Make this real with a tabletop drill that begins as a security alert and evolves into a data disclosure risk.
Procurement and vendor owners: contracts are not a control by themselves
Many organisations sign strong contracts but do not operationalise them. Vendor owners need training that produces repeatable due diligence.
Teach:
Vendor due diligence questions
What data is processed, where, and by whom.
Whether sub-processors are used.
Security measures and breach notification expectations.
Data return and deletion at end of service.
Ongoing monitoring
Vendor management is not “once and done”. Teach how to:
Reassess high risk vendors regularly.
Track evidence (SOC reports where applicable, security attestations, penetration testing summaries, policy updates).
Offboarding
Include a checklist for exit: remove accounts, reclaim devices, confirm data return or destruction, and revoke API keys.
Legal, compliance, and risk: make privacy operational, not theoretical
This role must translate the law into daily processes and evidence.
Teach:
How to maintain records of processing activities in a way that stays current.
How to run a risk assessment for new initiatives (a DPIA style approach), focusing on proportional controls.
How to design and test the rights request workflow.
How to assess incidents and coordinate a consistent response.
This is also the group that should validate training content annually as processes and guidance evolve.
Records and administration: paper is still personal data
Jamaican organisations often operate in hybrid environments with both paper and digital records.
Teach:
Secure storage for paper files (controlled access, sign-out logs where needed).
Secure printing practices and “print release” habits.
Approved shredding and disposal processes.
Retention schedules and what triggers destruction.
A simple but effective exercise is a walk-through audit: staff identify common paper risk points (unattended trays, open cabinets, files on desks overnight) and agree corrective actions.
How to build training that stands up to audits and investigations
Training should produce evidence. If you cannot show who was trained, on what, and when, you will struggle to demonstrate accountability.
Maintain a training evidence pack
Include:
A training matrix by role.
Attendance records or LMS completion logs.
Course outlines and version history.
Quiz results and pass marks.
Signed acknowledgements for key policies (where appropriate).
Records of drills, including lessons learned and corrective actions.
Test behaviour, not memory
A short quiz can confirm understanding, but scenario assessments confirm application. For high risk roles, prioritise:
Role play.
Tabletop exercises.
Spot checks (for example, sample rights request handling, sample vendor files, sample access reviews).
Measure improvement
Choose two or three metrics that reflect reduced risk, for example:
Fewer mis-sent emails containing attachments.
Faster internal reporting of incidents.
Lower volume of overdue rights requests.
Common mistakes to avoid when designing data protection training courses
Treating training as a one time event
Privacy programmes degrade when training is only annual. Use short refreshers after incidents, process changes, or new systems.
Delivering generic content with no local workflow
Staff need to hear:
Which forms they must use.
Which inbox receives rights requests.
Which tools are approved.
Who can authorise disclosure.
Generic content can be a foundation, but role tracks must map to your real processes.
Ignoring contractors and temporary staff
If they handle personal data, they need onboarding training and clear rules on tools, devices, and disclosure.
Training without executive sponsorship
When leadership does not attend its own session, staff assume privacy is optional. A visible leadership commitment increases completion rates and reporting confidence.
Choosing the right training provider in Jamaica
When evaluating a provider for data protection training courses, look for:
Demonstrated understanding of Jamaican regulatory expectations and business realities.
Ability to tailor role tracks (not just deliver one general presentation).
Practical exercises and templates you can reuse.
Clear deliverables you can retain as evidence (outlines, attendance, assessments).
If you are building or upgrading your organisation’s privacy training programme, Privacy & Legal Management Consultants Ltd. (PLMC) provides data protection implementation support, training sessions, and GRC-aligned advisory in Jamaica. If you want help scoping role-based content, mapping training to your internal processes, or designing scenario drills, you can start with a free consultation.

