
Data Protection Act Policies: Minimum Set for Compliance

Most Jamaican organisations now understand the Jamaica Data Protection Act (DPA) is not just about “being careful” with personal data. Regulators, customers, and business partners increasingly expect you to prove you can manage personal data safely and consistently. That proof is largely built on a practical set of written policies and procedures that match how your organisation actually operates.
This guide outlines a minimum set of Data Protection Act policies most organisations should have in place to demonstrate compliance, reduce operational risk, and avoid scramble-mode when a rights request or incident arrives.
What “policies” mean in a DPA compliance context
People often use “policy” to mean any privacy document. For compliance, it helps to separate three categories:
Policies: management intent and rules (what the organisation requires and why). Example: Data Protection Policy, Retention Policy.
Procedures / playbooks: step-by-step instructions (how staff execute the policy). Example: Rights Request Procedure, Breach Response Procedure.
Notices and forms: outward-facing transparency and internal records. Example: Privacy Notice, consent language, request forms.
The DPA is anchored in accountability, meaning you must implement appropriate measures and be able to demonstrate them. A well-structured policy pack is part of that evidence.
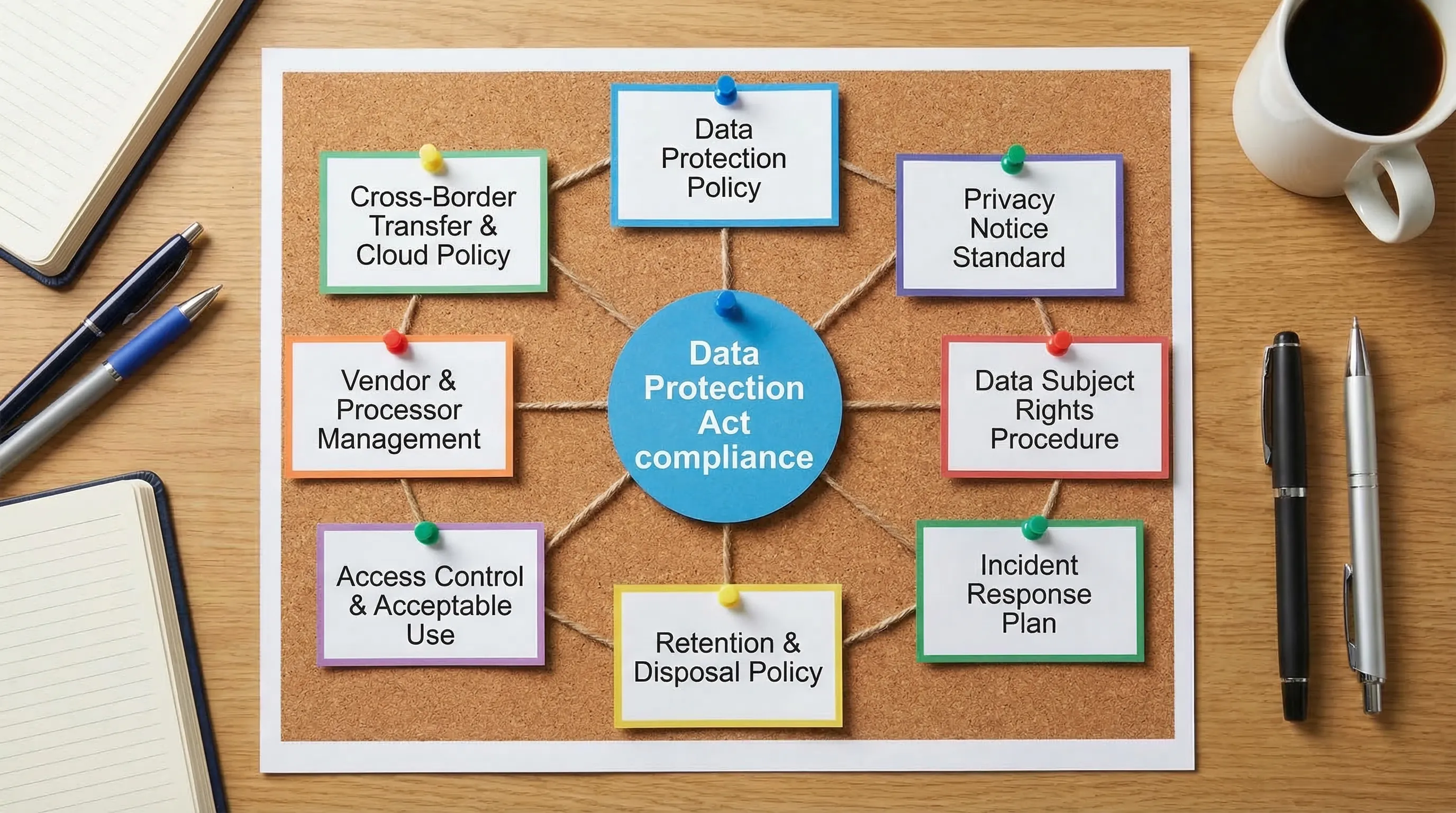
The minimum set: 8 policies (and the procedures that make them real)
There is no single “official” policy bundle that fits every sector, but most Jamaican organisations can treat the following as a baseline. If you only have the capacity to start with a minimum set, start here.
1) Data Protection Policy (the umbrella policy)
This is your top-level statement of how your organisation governs personal data. It should be approved by leadership and referenced by other policies.
Include, at minimum:
Scope (which entities, locations, systems, and staff it applies to)
Definitions and roles (controller/processor concepts, internal owners)
The principles you will follow (fairness, purpose limitation, minimisation, accuracy, storage limitation, security, accountability)
A high-level overview of how you meet key obligations (security safeguards, transparency, rights handling, vendor controls, breach handling)
Consequences for non-compliance (disciplinary approach aligned with HR policies)
Review cadence and version control
Common gap: a policy that is copied from another jurisdiction and does not match Jamaica operations, vendors, or data flows.
2) Privacy Notice Standard (external transparency rules)
Your privacy notice is often the first document customers, employees, patients, students, or citizens will look for. Many organisations have a notice, but lack an internal standard that ensures every collection point provides consistent information.
Instead of treating this as “one webpage,” create a privacy notice standard that governs:
When notices must be shown (web forms, paper forms, call scripts, mobile apps, CCTV signage, HR onboarding)
What content must be included (what you collect, why, who you share with, retention approach, rights, contact channel)
How you handle special categories, especially health-related data, which is sensitive and requires extra care
Practical tip: maintain a simple register of collection points and the notice version used at each point.
3) Data Subject Rights Request Procedure
Sooner or later, someone will request access, correction, or other rights related to their personal data. Your risk is not only legal, it is operational: requests often arrive through customer service, social media inboxes, HR, or front desk staff.
A workable rights procedure should specify:
Intake channels (email address, form, physical locations) and staff responsibilities
Identity verification steps that are proportionate (strong enough to prevent disclosure to the wrong person)
Search plan (systems and departments to check, including third parties)
Response workflow (approval steps, redaction rules, response templates)
Exceptions and escalation triggers (legal privilege, ongoing investigations, mixed data about multiple people)
Logging requirements (date received, deadline tracking, outcome, and evidence retained)
Evidence to keep: a rights request log, response templates, and training records for staff who handle requests.
4) Personal Data Breach and Incident Response Plan
Data incidents are not always “hackers.” Misaddressed emails, lost devices, exposed spreadsheets, and misconfigured cloud storage are common causes of personal data exposure.
Your incident response plan should define:
What counts as a personal data incident (including near misses)
How to report internally (a single channel, with after-hours coverage if needed)
First-hour actions (containment, access revocation, forensic preservation)
Risk assessment approach (what data, how many affected, potential harm)
Notification decision-making, including documentation even if you decide not to notify
Communications control (who can speak externally, how messages are approved)
Post-incident corrective actions and lessons learned
For recognised guidance on incident handling structure, many organisations map their playbooks to established frameworks such as the NIST Computer Security Incident Handling Guide (SP 800-61).
5) Records Retention and Secure Disposal Policy
Storage limitation is one of the most frequently overlooked principles. Many organisations can explain why they collect data, but cannot justify why they still have it five or ten years later.
Your retention policy should cover:
A retention schedule by record type (customer files, HR records, vendor files, access logs, CCTV footage, complaints)
Legal and regulatory retention drivers (sector rules, contractual obligations)
Disposal methods (secure shredding, wiping standards, media destruction)
Litigation hold process (pausing deletion when disputes or investigations arise)
Backup considerations (how deletion works for backups and archives)
Practical tip: start with your highest-risk and highest-volume record types, then expand.
6) Access Control and Acceptable Use Policy
The DPA requires appropriate security safeguards, but “security” must translate into clear staff rules and enforceable controls.
This policy typically combines two related areas:
Access control rules: least privilege, joiner-mover-leaver process, password and MFA requirements, privileged access oversight
Acceptable use rules: handling of customer data, use of personal email, removable media, printing, screen privacy, device storage
Common gap: access is granted for convenience and never reviewed. Add a simple access review requirement (quarterly for high-risk systems is a good starting point).
7) Vendor and Processor Management Policy
If third parties handle personal data for you (payroll providers, cloud platforms, marketing agencies, security companies, medical labs, courier services), your compliance depends on their controls as well.
This policy should define:
Vendor categorisation (which vendors are “data processors” and which are independent controllers)
Minimum due diligence checks before onboarding (security posture, breach history, subprocessor use)
Contract requirements (confidentiality, security measures, breach reporting timelines, audit rights, deletion/return on exit)
Ongoing monitoring approach (annual reassessment for higher-risk vendors)
This is especially important for businesses with international supply chains. For example, an organisation launching a brand and working with a full-service apparel development and manufacturing partner still needs to assess whether any personal data is exchanged (customer order data, shipping details, employee data for factory access, or marketing databases) and ensure contracts and transfer safeguards match the risk.
8) Cross-Border Transfer and Cloud Use Policy
Many Jamaican organisations rely on cloud services where data may be stored or accessed outside Jamaica. Cross-border transfers are often invisible to business teams because they happen through standard SaaS setups.
This policy should include:
Rules for selecting cloud tools (security minimums, data residency considerations where relevant)
Required assessment before enabling a new system that stores personal data
Rules for international sharing (including with group companies, vendors, and consultants)
Documentation requirements for transfer risk decisions and vendor assurances
Practical tip: keep a simple register of systems that store personal data and note where the vendor is based, where data may be processed, and who has admin access.
How to prioritise if you cannot do all eight at once
If you are building from zero, prioritise based on likely risk and frequency of use:
First wave (high frequency): Data Protection Policy, Privacy Notice Standard, Rights Request Procedure
Second wave (high impact): Incident Response Plan, Vendor Management Policy
Third wave (risk reduction over time): Retention & Disposal, Access Control & Acceptable Use, Cross-Border & Cloud Policy
The key is to avoid a “paper compliance” pack that sits in a folder. Start with what you can operationalise quickly, then mature it.
What regulators and auditors will look for (your evidence pack)
Written policies matter, but evidence of implementation matters more. Build a lightweight “privacy evidence pack” alongside your policies:
Policy approval records (board/management sign-off, dates, version history)
Training logs (who was trained, when, and on what)
Rights request log and sample response packs (redacted)
Incident log, including near misses and lessons learned
Vendor due diligence records and signed agreements
Retention schedule and proof of disposal activities (where applicable)
Periodic reviews (access reviews, vendor reassessments, policy reviews)
For a practical benchmark on accountability-style documentation, the UK regulator’s materials on accountability are a useful reference point even outside the UK, because they explain what “being able to demonstrate” looks like in practice. See the ICO’s accountability framework.
Policy drafting pitfalls that create compliance risk
Copying templates without operational ownership
A policy that no one owns will not be followed. Every document should have:
A named owner (role, not a person’s name if roles change often)
Clear “who does what” responsibilities
A realistic review period
Writing policies that contradict your actual practices
If your retention policy says “we delete after 12 months” but your CRM retains data indefinitely, your policy becomes evidence against you.
Treating privacy as only an IT issue
IT enables controls, but privacy decisions are often made in operations, HR, marketing, sales, and customer service. Your policy set should reflect that shared accountability.
A practical implementation approach for Jamaican organisations
A workable way to implement the minimum policy set without overwhelming teams is:
Map your personal data reality first
Do a simple data inventory: what you collect, where it lives, who can access it, who you share it with, and why. This prevents policies from becoming theoretical.
If you want a broader operational refresher first, PLMC has resources that cover the fundamentals and readiness steps, such as “Data Protection Basics: What Jamaican Firms Must Know” on the PLMC site.
Draft policies in plain language, then add procedures where needed
Aim for policies staff can actually follow. Where a workflow is required (rights handling, incidents, vendor onboarding), build a short procedure and templates.
Train by role, not by generic slides
Front desk and customer service need intake scripts. HR needs employee-data handling rules. IT needs access and incident tasks. Procurement needs vendor checklists.
Test with tabletop exercises
Run one rights request drill and one incident drill. The value is immediate: you will discover gaps in contact lists, permissions, and decision-making.
Where PLMC can help
If you need to implement Data Protection Act policies quickly, PLMC supports Jamaican organisations with data protection implementation, staff training, risk assessments, and GRC integration. A practical engagement often focuses on producing a usable policy pack, aligning it to your data flows, and leaving you with an evidence-ready operating model rather than only templates.
For organisations unsure where to start, a short scoping discussion can clarify what you truly need for your size, sector, and risk profile.
