
Company Data Protection Policy: Minimum Clauses for Compliance

A written policy is one of the fastest ways to move from “we care about privacy” to “we can prove compliance”. For Jamaican organisations, a company data protection policy also helps turn the Data Protection Act, 2020 into practical rules staff can follow, and auditors, partners, and regulators can verify.
This guide walks through the minimum clauses your company data protection policy should include to support compliance, reduce incidents, and create consistent handling of personal data across departments. (This article is general information, not legal advice.)
What a company data protection policy is (and what it is not)
A company data protection policy is an internal governance document. It sets the rules employees and contractors must follow when they collect, use, store, share, and delete personal data.
It is not the same as:
A privacy notice (external-facing transparency statement to customers, employees, website visitors, and others).
A retention schedule (detailed timelines per record type, usually maintained as a separate register).
An incident response plan (often a separate playbook, referenced by the policy).
A strong policy connects these documents and makes ownership clear.
Who the policy should cover
Your policy should apply to:
Employees (permanent and temporary)
Contractors and consultants
Interns
Anyone processing personal data on the organisation’s systems or under its authority
It should also cover all formats of personal data, including paper files, emails, cloud tools, messaging apps used for work, CCTV footage, call recordings, and exported spreadsheets.
Minimum clauses for a compliant company data protection policy
Below are the clauses most organisations need as a baseline to align with the Data Protection Act and good-practice privacy governance.
1) Purpose, scope, and policy objectives
State why the policy exists and what it is designed to achieve.
Include:
The policy’s purpose (compliance, protection, trust, risk reduction)
The scope (business units, locations, systems, subsidiaries)
A clear statement that breaches of the policy may lead to disciplinary action
Practical tip: Put the scope in plain language. If your HR team thinks it is “an IT policy”, adoption will fail.
2) Definitions (personal data, sensitive data, processing)
Define key terms in language staff can understand, including:
Personal data
Sensitive categories (for example health data, biometrics, children’s data where applicable)
Processing activities (collecting, storing, sharing, deleting)
This prevents common confusion such as “it’s just a name and phone number” (still personal data) or “it’s only internal HR data” (still covered).
3) Governance and accountability (who owns what)
This clause is the backbone of enforcement.
Include:
The executive owner (often a senior leader responsible for oversight)
The privacy lead or Data Protection Officer function (if appointed)
Department responsibilities (HR, Marketing, IT, Operations)
Escalation paths for issues and incidents
Board reporting expectations (at least annually, often quarterly for higher-risk organisations)
Minimum language to include: who approves exceptions, who signs off vendor contracts that include personal data processing, and who has final authority during a breach.
4) Data protection principles and lawful processing rules
Your policy should translate legal principles into operating rules, such as:
Only collect what you need (data minimisation)
Use data only for defined purposes (purpose limitation)
Keep data accurate and up to date where required
Secure data appropriately
Keep data only as long as needed (storage limitation)
Where relevant to your operations, your policy should also require teams to document the lawful basis for key processing activities and to avoid collecting “just in case” data.
Helpful reference for principle-based governance: The UK Information Commissioner’s Office (ICO) publishes widely-used guidance on data protection principles, which many Caribbean organisations use as a practical benchmark even when operating under local law: ICO guidance.
5) Data inventory and record-keeping requirement
A policy should require a maintained data inventory (sometimes called a record of processing activities), because you cannot protect what you cannot identify.
Minimum requirements to state:
Each department must document what personal data it collects and why
Where it is stored (systems, paper files, cloud services)
Who it is shared with (vendors, partners, regulators)
Retention periods or retention triggers
This clause is especially important for audits, partner due diligence, and incident response.
6) Transparency: privacy notices and fair collection
Your policy should require:
A privacy notice (or notices) appropriate to each audience (customers, employees, website users)
Approved scripts or statements for frontline collection (forms, call scripts, reception desks)
Controls around “secondary use” (using data for a new purpose without proper review)
Practical tip: Make one team responsible for maintaining privacy notices (and change control), otherwise updates become inconsistent.
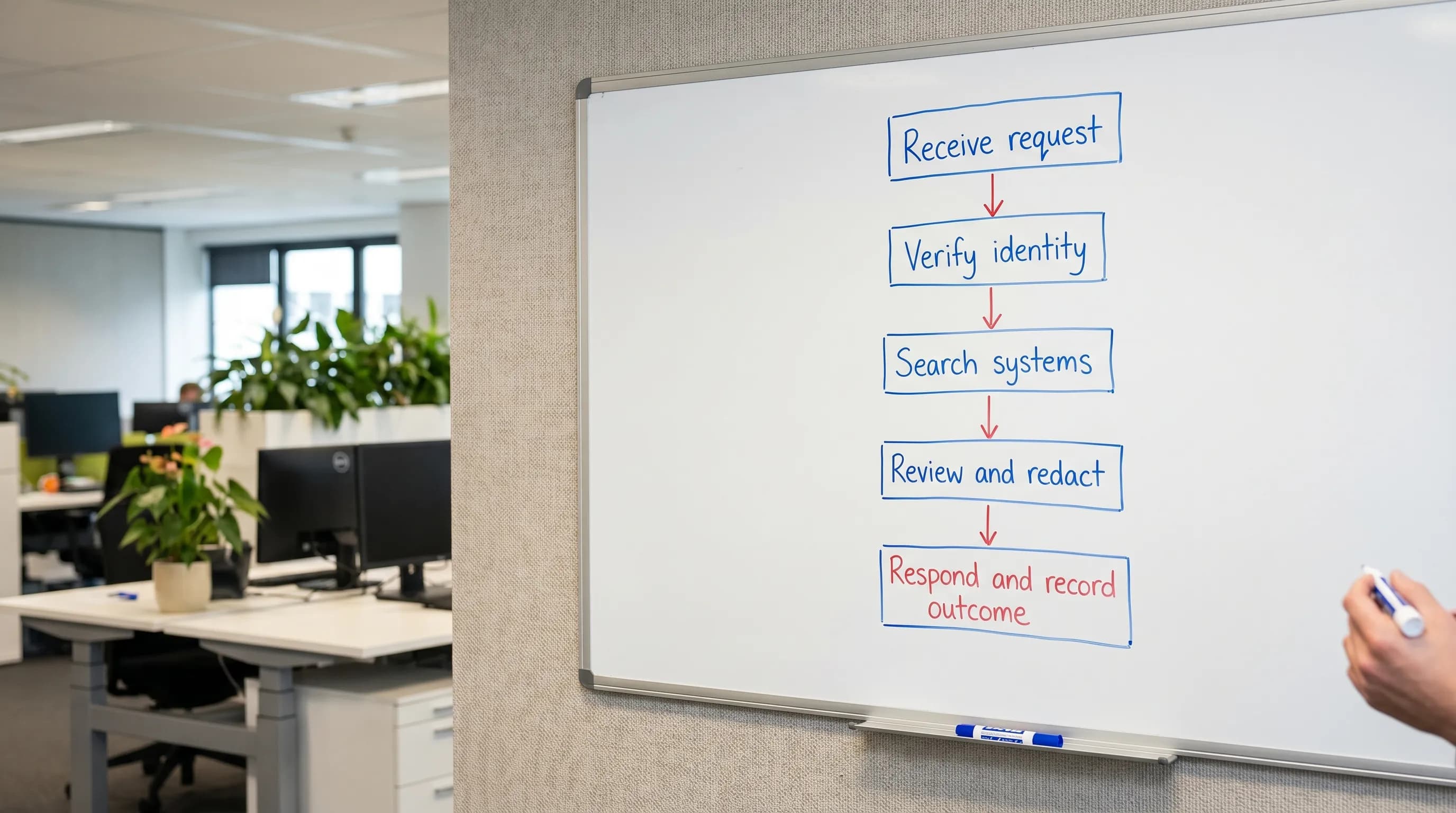
7) Individual rights handling (requests and timelines)
Most compliance failures become visible through rights requests, because they test your organisation end-to-end.
Your policy should include:
Which requests you accept (access, correction, objection, deletion where applicable)
Where requests can be submitted (email address, form, physical location)
Identity verification rules
Internal routing and ownership (who searches which systems)
Response governance (who reviews, who signs off)
If you already have a process, the policy should reference it and make compliance mandatory.
8) Data security baseline controls (technical and organisational)
A strong policy does not try to be a full cybersecurity standard, but it must set minimum expectations.
Include requirements for:
Access control (least privilege, role-based access)
Password and MFA expectations
Approved storage locations (no personal USB drives, no unapproved cloud sharing)
Encryption expectations where feasible (especially for laptops and backups)
Secure disposal for paper and hardware
Remote work and BYOD rules (including what happens if a device is lost)
Where you have an information security policy, cross-reference it and clarify which one takes precedence if there is a conflict.
9) Retention and secure disposal
This clause is often missing, and it creates long-term risk.
Minimum requirements:
A retention schedule must exist (even if it is simple at first)
Data must be deleted or anonymised when no longer needed
Legal holds must be respected (for litigation, investigations, regulatory matters)
Secure destruction methods for paper and electronic records must be defined
Practical tip: If you cannot confidently delete, start by enforcing retention on one high-volume dataset (for example, applicant CVs, visitor logs, or customer support tickets).
10) Third-party and processor management (contracts and due diligence)
If vendors handle personal data, your policy should require controls before onboarding and throughout the relationship.
Minimum clause elements:
Vendor risk screening for privacy and security
A requirement for written terms covering confidentiality, security measures, use limitations, breach reporting, and sub-processing
Rules for sharing data with auditors, regulators, or affiliates
Termination requirements (return or destruction of data)
This is critical for common Jamaican business realities such as outsourced payroll, cloud email, customer management tools, and payment processors.
11) Cross-border transfers and cloud use
Many organisations store or access data using platforms hosted outside Jamaica.
Your policy should set out:
The approval process for new cloud tools that process personal data
Required assessments for cross-border transfers
Minimum contractual and security expectations
If you already use major platforms, document them and ensure your procurement process prevents “shadow IT” from creating unmanaged transfers.
12) Personal data breach and incident management
Your policy must require immediate reporting and define what counts as an incident.
Include:
Examples of reportable events (misdirected email, lost laptop, compromised account, wrong recipient on WhatsApp, exposed database)
Mandatory internal reporting channels (and how quickly staff must report)
The incident response owner (and backups)
Documentation requirements (what happened, impact, remediation)

13) Training and awareness (role-based, not one-size-fits-all)
A minimum clause should require:
Induction training for all staff
Annual refreshers
Role-based training for high-risk functions (HR, IT, Customer Service, Marketing, Compliance)
Records of attendance and completion
Training is also one of the easiest ways to demonstrate accountability during an investigation or partner review.
14) Monitoring, audit, and continuous improvement
A compliant policy should not be “set and forget”.
Include:
How compliance is monitored (spot checks, audits, risk assessments)
How issues are recorded and tracked to closure
Review frequency (at least annually, or after major changes such as new systems or incidents)
15) Enforcement, exceptions, and disciplinary measures
This clause makes the policy real.
Include:
Consequences of non-compliance
A documented exception process (who can approve an exception, for how long, with what safeguards)
A requirement to document and review exceptions
Minimum clause checklist table (policy content you can validate quickly)
Use this table as a quick internal review: if any item is missing, your policy is likely too thin to support compliance.
Clause | Why it matters | What evidence supports it |
Purpose and scope | Prevents “this doesn’t apply to my team” | Published policy, staff acknowledgement |
Definitions | Reduces misunderstanding and under-reporting | Policy glossary, examples |
Governance and accountability | Enables decision-making and escalation | Org chart, role descriptions, reporting line |
Principles and lawful processing | Prevents excessive collection and misuse | Data inventory, lawful basis notes |
Data inventory requirement | Enables risk management and rights handling | Data map, system register |
Transparency | Supports fair collection and trust | Privacy notices, form statements |
Rights handling | Avoids missed deadlines and incomplete searches | DSAR log, procedures, templates |
Security baseline | Reduces incidents and limits harm | Access control records, policies, training |
Retention and disposal | Reduces long-term exposure | Retention schedule, destruction logs |
Vendor management | Controls outsourcing risk | Due diligence files, DPAs in contracts |
Cross-border and cloud | Prevents unmanaged transfers | Tool approval records, transfer assessments |
Incident management | Improves response speed and documentation | Incident register, post-incident reviews |
Training | Builds a defensible compliance posture | Training records, materials |
Monitoring and review | Keeps policy aligned with reality | Audit reports, management reviews |
Enforcement and exceptions | Ensures consistency | Exception register, disciplinary framework |
Common mistakes that weaken a data protection policy
A policy can exist on paper and still fail in practice. Watch for these common gaps:
The policy repeats legal language but gives no operational direction, so teams do not know what to do differently.
No ownership is assigned (for example, “IT handles privacy”), so decisions stall.
No linkage to vendor onboarding, so third-party risk grows silently.
No retention rules, so data accumulates indefinitely.
No requirement to log requests and incidents, so you cannot demonstrate accountability.
Frequently Asked Questions
Do we need a company data protection policy if we already have a privacy notice? Yes. A privacy notice tells people what you do. A company data protection policy tells staff what they must do internally to keep processing lawful, secure, and consistent.
Can a small business use a shorter data protection policy? Yes, but the same minimum clauses still apply. SMEs can simplify language and reduce appendices, but should keep governance, security, retention, vendor controls, and incident reporting.
Is a data protection policy the same as an information security policy? No. Security focuses on protecting information assets. Data protection focuses on lawful and fair processing of personal data, including rights handling, transparency, and retention. They should align.
What is the most important clause to add first? Governance and accountability, incident reporting, and retention are often the fastest to improve real-world outcomes, because they change behaviour and reduce unmanaged risk.
Need help drafting or upgrading your company data protection policy?
Privacy & Legal Management Consultants Ltd. (PLMC) supports Jamaican organisations with data protection implementation, training, and GRC-aligned compliance programmes. If you want a policy that is not just compliant on paper, but workable for your teams, you can request a consultation via Privacy & Legal Management Consultants Ltd..
