
AML Compliance Jamaica: Policies, Training, Reporting

Strong anti-money laundering (AML) controls are not only a regulatory requirement in Jamaica, they are also a commercial necessity. Weak AML programmes can lead to regulatory action, disrupted banking relationships, increased fraud exposure, and lasting reputational damage. For many Jamaican organisations, the practical question is not “Do we need AML?” but “Do we have the right policies, training, and reporting to prove we manage AML/CFT risk day to day?”
This guide focuses on what an audit-ready AML programme looks like in Jamaica, with practical steps you can implement across governance, staff capability, and suspicious activity reporting.

What “AML compliance” means in Jamaica (in plain terms)
AML compliance is the set of controls your organisation uses to prevent, detect, and report money laundering and terrorist financing (often referred to as AML/CFT). In Jamaica, AML/CFT obligations typically arise under national AML laws and related guidance, and are overseen by sector regulators.
Even if your organisation is not a financial institution, you may still fall within AML obligations depending on your activities (for example, certain cash-intensive or professional service models). The consistent theme across regulators is a risk-based approach, meaning your controls should match your real exposure to AML/CFT risk, not just what is written in a policy.
For international alignment, Jamaican regulators and many group compliance teams anchor to the FATF Recommendations, which set the global baseline for AML/CFT programmes.
The three pillars: policies, training, reporting
A useful way to structure AML compliance is around three pillars:
Policies and governance: What you require, who owns it, and what evidence you keep.
Training and competence: Whether staff can actually apply the policy under pressure.
Reporting and escalation: How you identify unusual activity, document decisions, and file reports appropriately.
If one pillar is weak, the programme is fragile. For example, strong policies without training become “shelfware,” and good training without reporting processes creates hesitation and inconsistency.
Pillar 1: AML policies that regulators and auditors can test
An AML policy should not be a generic template. It should describe your organisation’s actual controls, decision points, and accountability. In practice, your “AML documentation set” often includes:
Governance and accountability
Your programme should clearly assign ownership. Common elements include:
Board and senior management oversight (how AML risk is reviewed and challenged)
A named compliance lead (often an MLRO or equivalent, depending on your sector)
Defined roles for front-line staff, operations, compliance, and internal audit
A documented approach to issue management (tracking, remediation, retesting)
If your organisation is regulated, ensure your governance aligns with sector guidance (for example, the Bank of Jamaica for certain financial services, or the Financial Services Commission for other financial sectors).
Enterprise-wide AML risk assessment (EWRA)
A strong AML programme starts with a risk assessment that is specific to Jamaica and specific to your business model. It typically covers:
Customer risk (types of customers, legal persons, beneficial ownership complexity)
Product and service risk (cash exposure, speed of movement, cross-border features)
Channel risk (online onboarding, agents, third parties)
Geographic risk (domestic and cross-border exposure)
Your risk assessment should drive your controls. If your EWRA says you are exposed to higher-risk onboarding or cash activity, your CDD/EDD steps and monitoring should visibly reflect that.
Customer due diligence (CDD) and enhanced due diligence (EDD)
Your policies should explain:
What information you collect at onboarding (KYC)
How you verify identity (and what verification is acceptable)
How you identify and verify beneficial owners (where applicable)
When EDD is required (and what extra steps you take)
How you manage politically exposed persons (PEPs), higher-risk customers, or unusual structures
Avoid writing policies that promise controls you do not have (for example, “real-time automated monitoring”) if your operations are manual. It is better to document a practical manual control that you consistently apply and evidence.
Sanctions and terrorist financing controls
While AML and sanctions are not identical, most compliance programmes address them together operationally. At minimum, document:
When screening occurs (onboarding and ongoing)
What you screen (names, beneficial owners, connected parties)
What happens on a potential match (pause, escalate, decision, documentation)
Recordkeeping for screening outcomes
Recordkeeping and audit trail
In an examination, “If it isn’t documented, it didn’t happen” is a common standard. Your policy suite should specify:
What records you keep (KYC, beneficial ownership, monitoring alerts, case notes)
Where you keep them and who can access them
Retention rules aligned to legal and regulatory expectations
Independent testing and assurance
Most mature AML programmes include periodic independent testing (internal audit, external review, or other independent function). The goal is to verify:
Policy is implemented in practice
Files contain required evidence
Monitoring and escalation work end to end
Training is completed and effective
To make AML policy requirements easier to operationalise, use a simple evidence-driven structure like the table below.
AML area | What the policy should clearly state | Evidence an auditor will look for |
Governance | Who owns AML, escalation paths, board reporting cadence | Org chart, board minutes/pack, KRIs, issue logs |
Risk assessment | How risk is assessed and refreshed | EWRA document, methodology, review dates |
CDD and EDD | Required KYC, verification, EDD triggers and steps | KYC files, EDD memos, approvals, supporting documents |
Screening | What is screened, when, and how matches are handled | Screening logs, match decisions, case notes |
Monitoring | What is monitored and who reviews | Monitoring rules (or manual checks), alert logs, case outcomes |
Reporting | Internal escalation and external reporting process | STR decision logs, filing records, confidentiality controls |
Training | Who is trained, how often, how competence is checked | Training attendance, assessments, onboarding completion |
Pillar 2: AML training that changes behaviour (not just attendance)
In Jamaica, many organisations treat AML training as a once-a-year presentation. That is rarely enough. Effective AML training is role-based, practical, and verified.
What good AML training covers
At minimum, training should help staff answer:
What is suspicious activity in our specific business model?
What are the internal steps when something looks unusual?
What should we document, and how do we avoid “tipping off”?
What are common red flags we actually see in Jamaica (cash intensity, third-party payment patterns, unusual urgency, inconsistent source of funds narratives)?
Where possible, include realistic scenarios drawn from your own operations (anonymised). Staff tend to remember scenarios far better than definitions.
Role-based training matrix (simple and defensible)
Audience | Training goal | Typical approach |
Board and senior leadership | Understand AML risk exposure, approvals, oversight expectations | Short briefings tied to risk and metrics |
Front-line and onboarding staff | Spot red flags, perform CDD correctly, escalate consistently | Scenario-based sessions with checklists |
Operations and payments teams | Identify unusual patterns, document decisions | Practical walkthroughs of cases |
Compliance/MLRO function | Case management quality, reporting standards, trend analysis | Deep dives, typologies, quality assurance |
Third parties (agents, contractors) | Apply your minimum standards and escalation requirements | Contractual training + attestations |
Training records matter
Keep training records in a way you can produce quickly during an examination. Include:
Attendance or completion logs
Training materials and dates
Knowledge checks (even simple quizzes)
Remediation steps for non-completion
A regulator or auditor will often ask for evidence that training is effective, not only that it occurred.
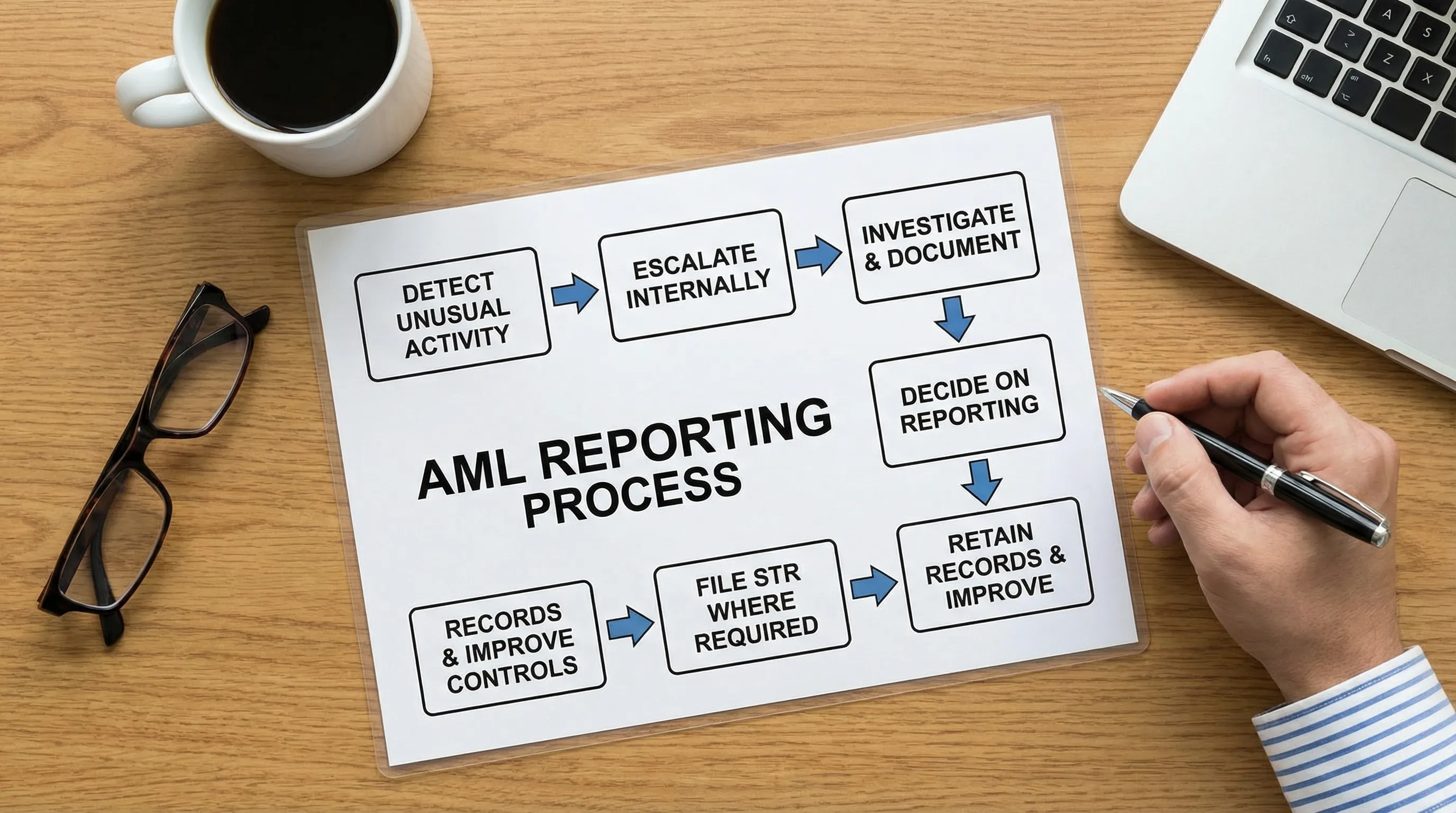
Pillar 3: Reporting and escalation (how suspicious activity becomes an STR)
Most AML failures happen in the “middle” of the process. Staff notice something unusual, but the organisation does not consistently document, escalate, decide, and report.
Build a clear internal escalation process
Your internal process should answer:
Who receives escalation (name the role, not just “Compliance”)
How staff escalate (email, case tool, form, hotline)
What information is required (customer details, transactions, narrative, documents)
Target turnaround expectations for triage and decisioning
How you document decisions, including “no report” decisions
This process should be tested. A tabletop exercise once or twice a year often reveals gaps quickly.
External reporting (STRs and related obligations)
Where suspicion reaches the legal threshold, organisations file suspicious transaction reports (STRs) with the appropriate Jamaican authority. In practice, compliance teams typically reference guidance and channels from Jamaica’s competent authority and sector regulator.
For general information on reporting and financial investigations in Jamaica, organisations commonly consult the Financial Investigations Division (FID) and their sector regulator. (Confirm your reporting obligations and process for your specific sector and licensing status.)
Protect confidentiality and avoid tipping off
Your AML policy and training should specifically address:
Who may know about an STR decision
How case files are secured
How staff communicate with customers during reviews (neutral language)
“Tipping off” risk is operational, not theoretical. A single careless comment can compromise an investigation.
Practical red flags to include in your playbooks
Your red flag library should be tailored to your services. Common examples that often warrant a closer look include:
Customer reluctance to provide consistent identification or beneficial ownership details
Transactions inconsistent with stated business activity or customer profile
Repeated third-party payments with unclear rationale
Unusual urgency, pressure, or attempts to bypass standard checks
Structured activity (for example, repeated transactions that appear designed to avoid internal thresholds)
Red flags do not automatically equal money laundering. The goal is to trigger review and documentation, not to accuse customers.
Common AML compliance gaps seen in practice
Across many Jamaican organisations, recurring weaknesses tend to fall into a few patterns:
Policies exist, but operations do not match
Templates are common, especially for fast-growing organisations. The risk is that policies describe controls you cannot evidence. Regulators and auditors test what you do, not what you say.
Risk assessments are outdated or too generic
An EWRA done once and never refreshed quickly becomes irrelevant, especially if you expand products, add channels, take on higher-risk customers, or change third-party relationships.
Beneficial ownership is inconsistent
Higher-risk legal persons, layered ownership, or informal structures often expose gaps. If your team cannot explain who ultimately owns or controls the customer and how you verified it, your CDD will be seen as weak.
STR decisioning is undocumented
Many teams escalate “suspicions,” but do not maintain a defensible case file showing investigation steps, rationale, and approvals.
Training is not role-based
One generic slide deck rarely addresses what front-line staff actually face, or what decision-makers must approve.
A quick AML self-check for Jamaica (audit readiness)
Use this as a practical internal sense-check. If multiple items are “not yet,” prioritise those areas in your compliance plan.
We have a documented AML risk assessment tailored to our products, customers, channels, and geographies.
Our CDD and EDD steps are clear, implemented, and evidenced in files.
We consistently identify and verify beneficial ownership where required.
Staff understand red flags for our business and know how to escalate.
We maintain a documented internal investigation and STR decision log.
Training is role-based, tracked, and includes knowledge checks.
We test the programme periodically (file reviews, independent testing, tabletop exercises).
Senior leadership receives AML metrics and can demonstrate oversight.
How PLMC can support AML compliance in Jamaica
Privacy & Legal Management Consultants Ltd. (PLMC) supports Jamaican organisations with practical Governance, Risk, and Compliance implementation, including AML programme support that fits your sector and operating reality.
Depending on your needs, support may include:
Designing or updating AML policies and procedures to match your actual operations
Building a defensible AML risk assessment methodology and refresh cycle
Delivering role-based AML training for front-line staff, leadership, and compliance teams
Strengthening reporting workflows, case documentation, and audit readiness
Integrating AML with wider corporate governance, cyber security, and data protection practices
If you want to sanity-check your current programme, you can start with a free consultation via PLMC.
Frequently Asked Questions
Who needs AML compliance in Jamaica? Any organisation with AML/CFT obligations based on its sector, licensing status, or activities should maintain an AML programme. If you are unsure, confirm your position with your regulator or qualified compliance support.
What is the difference between AML policy and AML procedures? A policy sets the rules and governance expectations (what must happen and who is accountable). Procedures explain the step-by-step process teams follow (how it happens in practice).
How often should AML training be done? Many organisations use a mix: onboarding training for new staff, regular refreshers, and targeted sessions when roles change or risks increase. The key is role relevance and evidence of completion and understanding.
What should we document when we decide not to file an STR? Keep a clear investigation record that shows the alert, what was reviewed, what information was considered, who approved the decision, and the rationale for closing the case.
How does AML reporting work in practice? Staff escalate internally, compliance reviews and documents the case, and the organisation files an STR where required through the appropriate Jamaican reporting channel. Always align the workflow to your regulator’s expectations.
How does AML intersect with data protection? AML requires collecting and retaining certain information, while data protection requires you to process personal data fairly, securely, and transparently. A good programme aligns both so you can evidence compliance without over-collecting or mishandling data.
Build an AML programme you can prove, not just describe
If your AML documentation, training, and reporting process are not producing reliable evidence, you are exposed during examinations, audits, and banking due diligence. PLMC can help you strengthen AML controls in a way that is practical for Jamaican operations and aligned with governance best practice.
Contact PLMC for a free consultation: https://www.privacymgmt.org/
